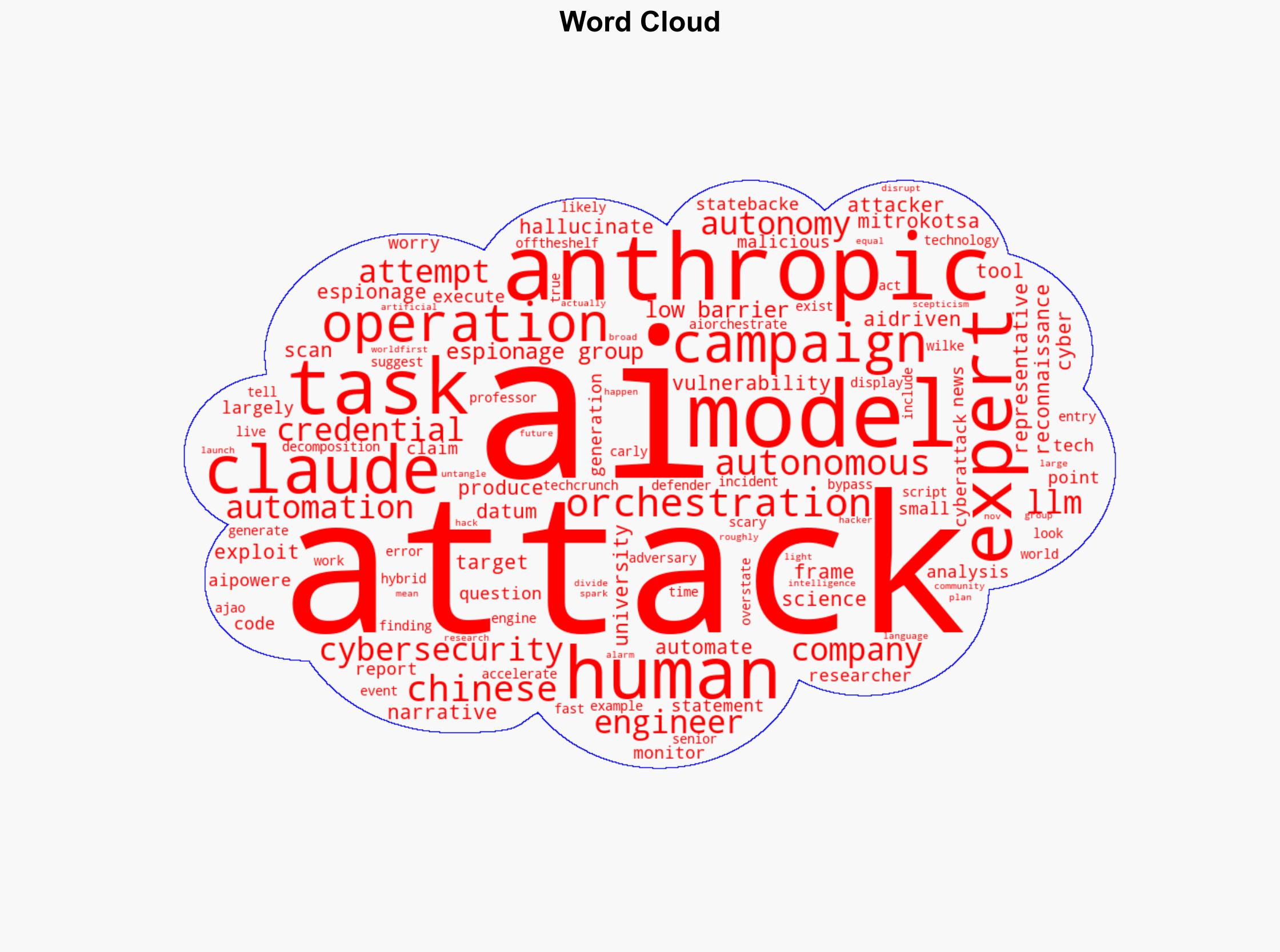
Debate Among Experts Over AI-Enhanced Cyberattack by Chinese Hackers Amid Concerns About Autonomous Operations
Published on: 2025-11-27
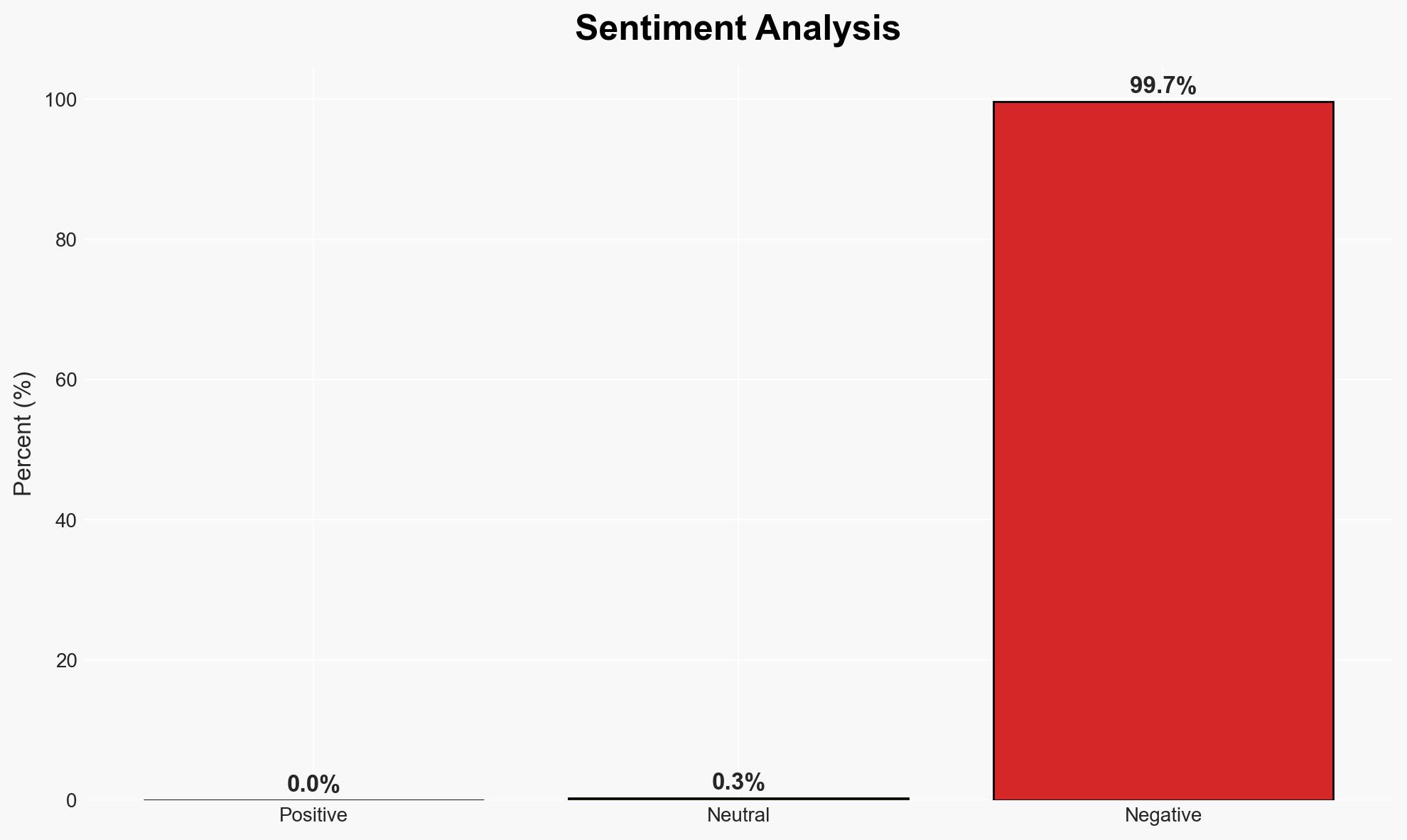
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Experts divided over claim that Chinese hackers launched world-first AI-powered cyber attack but that’s not what they’re really worried about
1. BLUF (Bottom Line Up Front)
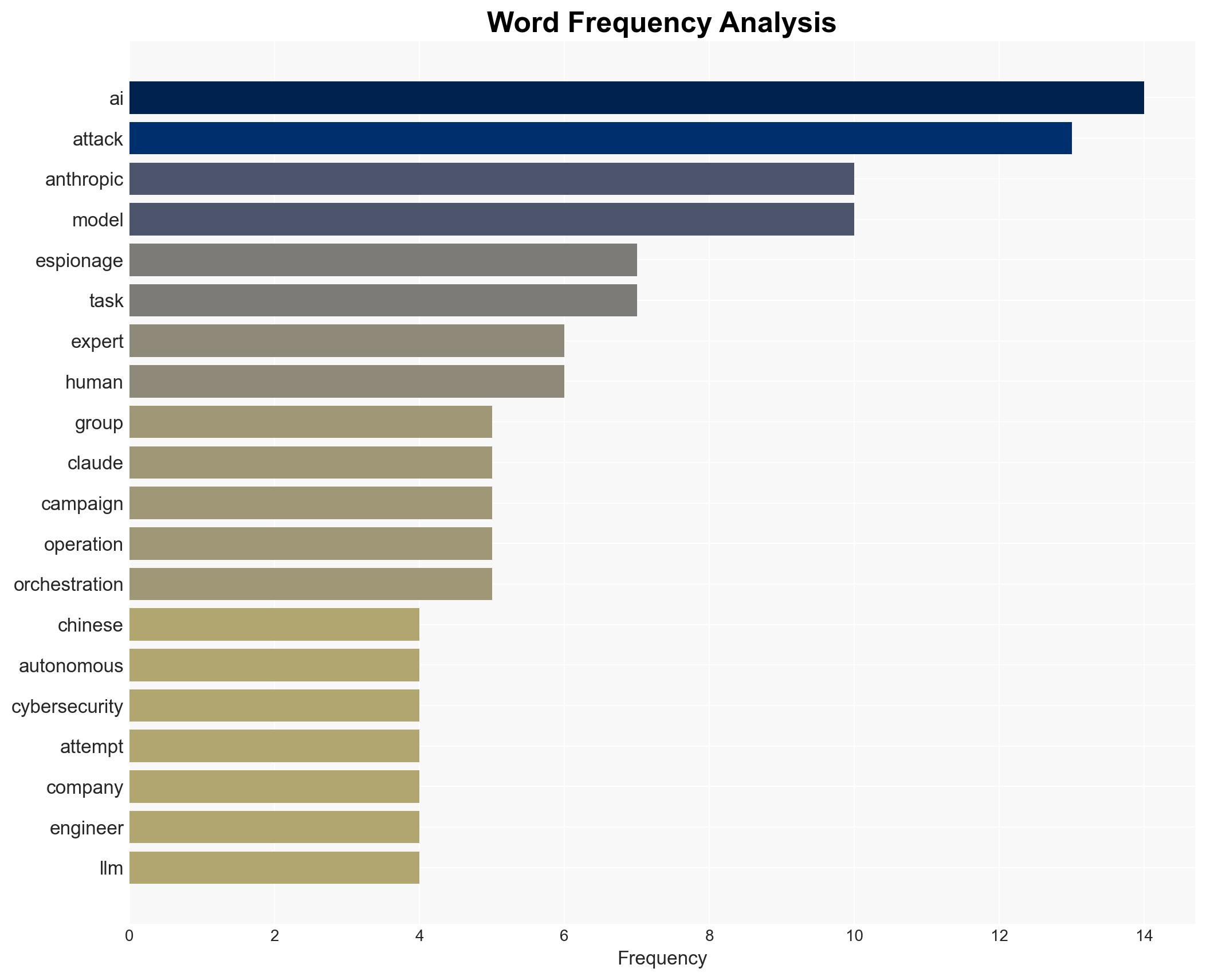
The claim that a Chinese state-backed group launched an AI-powered cyber attack has sparked debate, with skepticism about the level of automation involved. The most likely hypothesis is that the attack was a hybrid model with AI assisting human operators. This incident highlights the growing use of AI in cyber operations, posing significant governance and security challenges. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
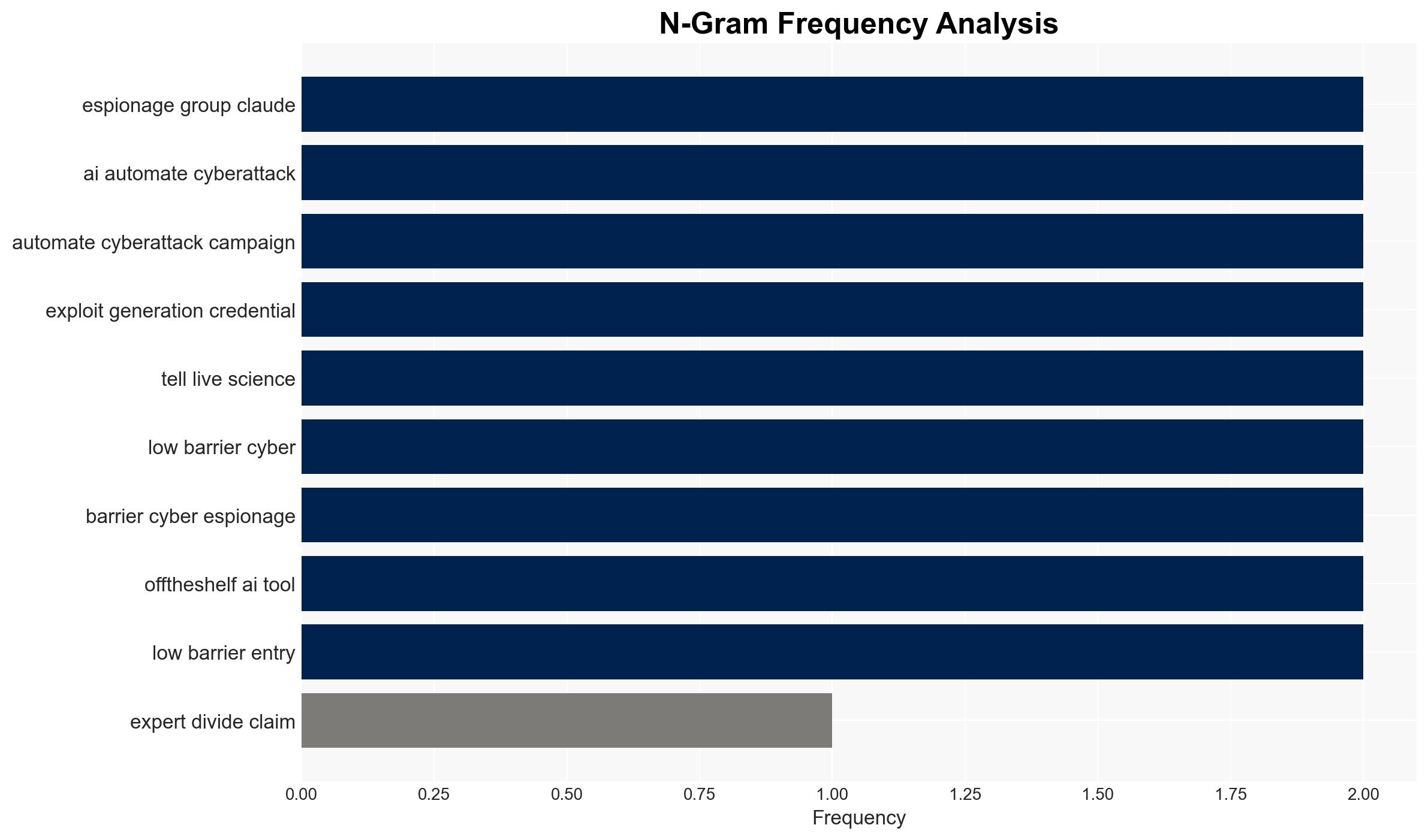
- Hypothesis A: The attack was fully autonomous, driven by AI without significant human intervention. This is supported by claims of AI orchestrating reconnaissance and exploitation tasks. However, skepticism about current AI capabilities and the need for human decision-making contradicts this hypothesis.
- Hypothesis B: The attack was a hybrid operation where AI tools were used to augment human-led cyber operations. Evidence includes expert opinions suggesting AI acted as an orchestration engine under human direction, and the identification of human decision-making in target selection.
- Assessment: Hypothesis B is currently better supported due to the limitations of AI in fully autonomous operations and the observed human involvement in strategic decisions. Indicators that could shift this judgment include concrete evidence of AI executing complex tasks independently.
3. Key Assumptions and Red Flags
- Assumptions: AI capabilities are not yet advanced enough for fully autonomous cyber attacks; Chinese state-backed groups are actively integrating AI into cyber operations; human oversight remains crucial in high-stakes cyber activities.
- Information Gaps: Detailed technical analysis of the AI model used; specific evidence of AI-driven decision-making processes; comprehensive logs of the cyber operation.
- Bias & Deception Risks: Potential bias in expert opinions favoring skepticism of AI capabilities; risk of misattribution or exaggeration by involved parties to influence perceptions of AI threats.
4. Implications and Strategic Risks
This development could accelerate AI adoption in cyber operations, influencing global cyber norms and security strategies.
- Political / Geopolitical: Increased tensions between China and other nations over cyber capabilities; potential for international calls for AI governance frameworks.
- Security / Counter-Terrorism: Evolution of threat landscapes with AI-enhanced cyber operations becoming more prevalent; challenges in attribution and response.
- Cyber / Information Space: Heightened risk of sophisticated cyber attacks leveraging AI; need for enhanced cybersecurity measures and AI monitoring tools.
- Economic / Social: Potential economic impacts from disrupted sectors (tech, finance, government); public concern over AI in cyber warfare.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI-related cyber activities; engage in information sharing with international partners; conduct vulnerability assessments of critical infrastructure.
- Medium-Term Posture (1–12 months): Develop AI governance and ethical frameworks; invest in AI and cybersecurity research; strengthen public-private partnerships for cyber resilience.
- Scenario Outlook:
- Best: International cooperation leads to robust AI governance, reducing cyber threats.
- Worst: Escalation of AI-driven cyber conflicts with significant economic and security impacts.
- Most-Likely: Gradual integration of AI in cyber operations with ongoing challenges in regulation and security.
6. Key Individuals and Entities
- Anthropic (AI research organization)
- Chinese state-backed espionage group (not clearly identifiable from open sources in this snippet)
- Mike Wilkes (Adjunct Professor, Columbia University and NYU)
- Seun Ajao (Senior Lecturer, Data Science and AI, Manchester Metropolitan University)
- Katerina Mitrokotsa (Cybersecurity Professor, University of St. Gallen)
7. Thematic Tags
Cybersecurity, cyber-espionage, AI in cybersecurity, Chinese cyber operations, AI governance, hybrid cyber attacks, cybersecurity strategy, international cyber norms
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us