Rising Threat of Kidnapping Gangs and Militants Poses Severe Security Challenges in Nigeria
Published on: 2025-11-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
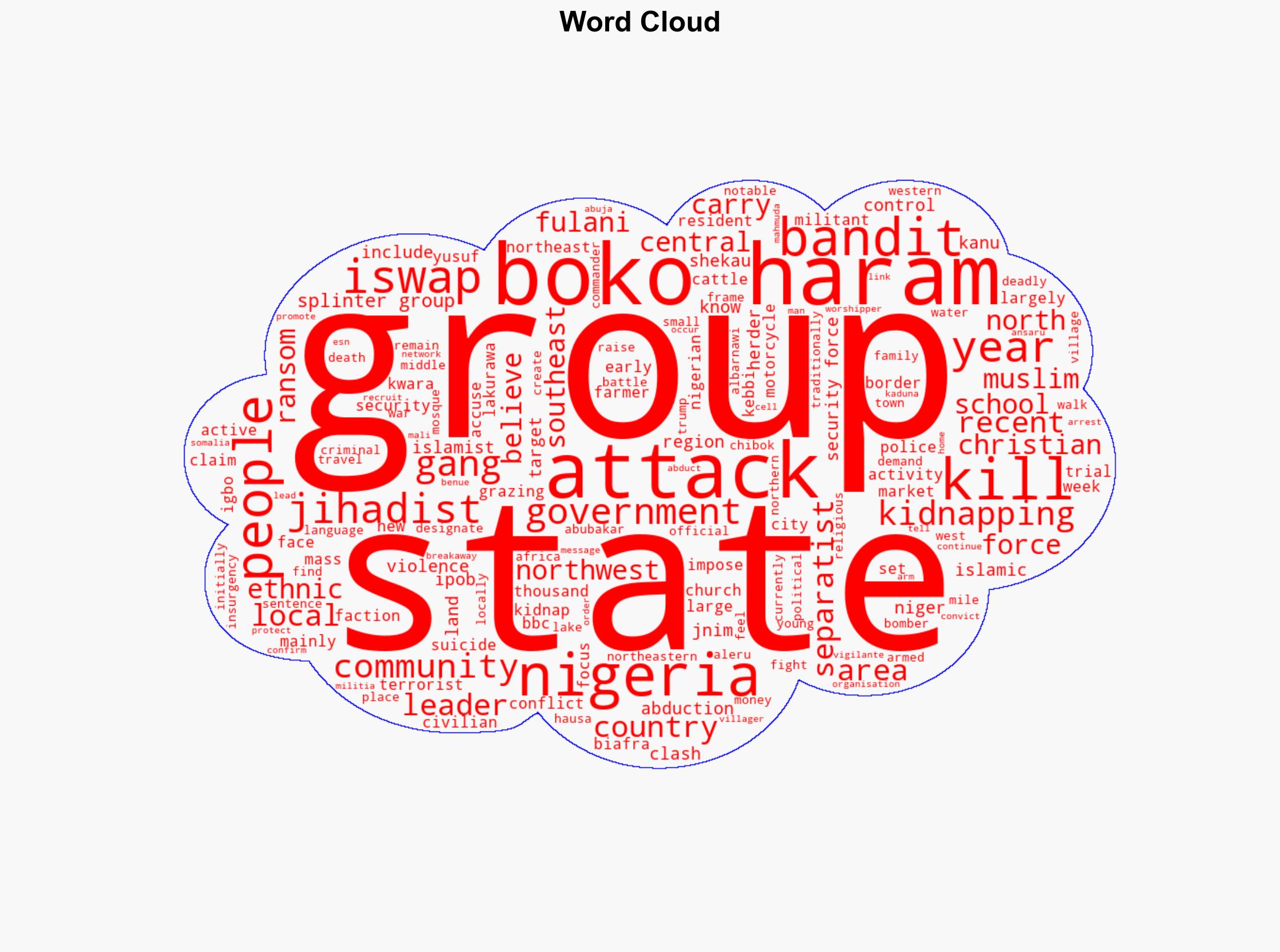
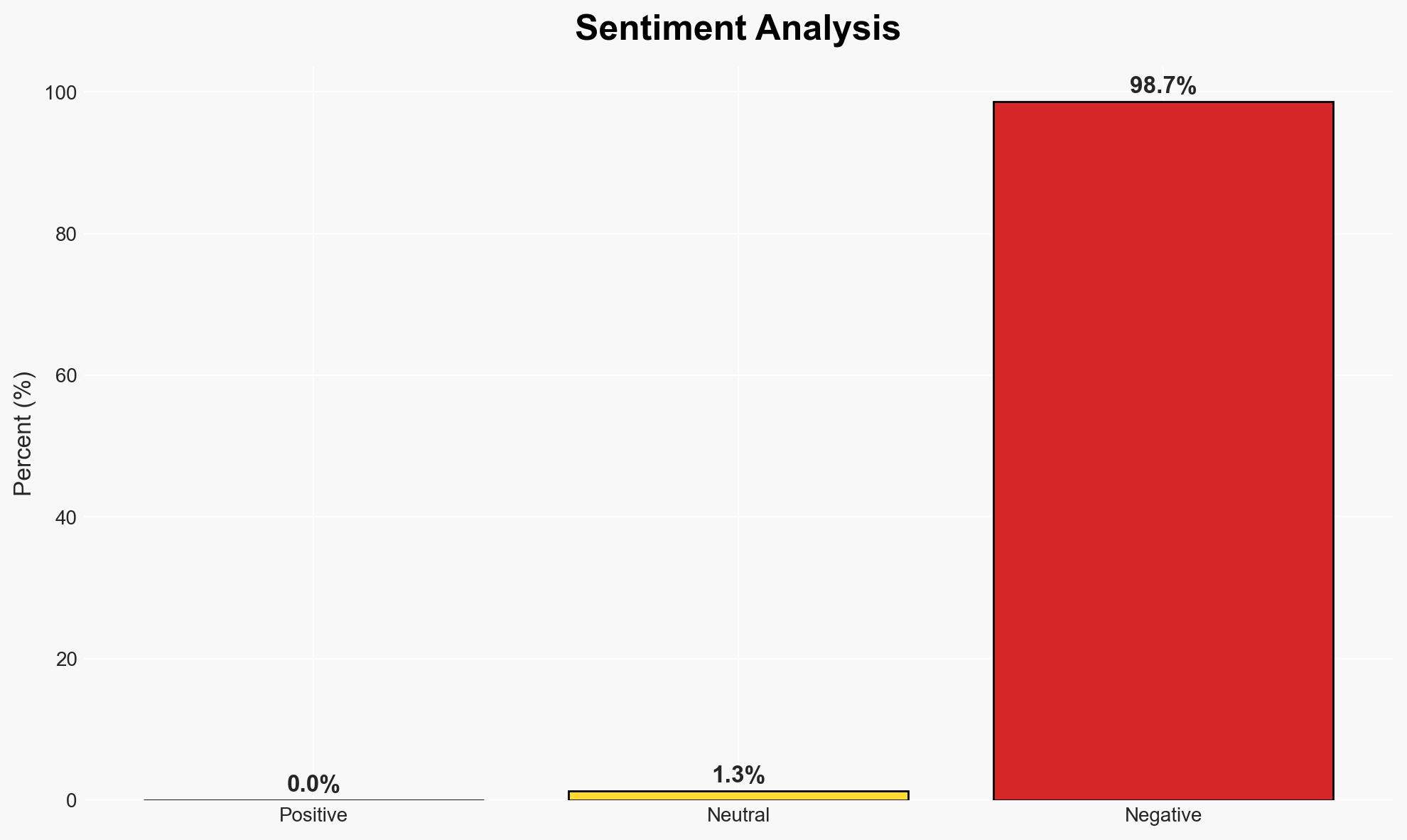
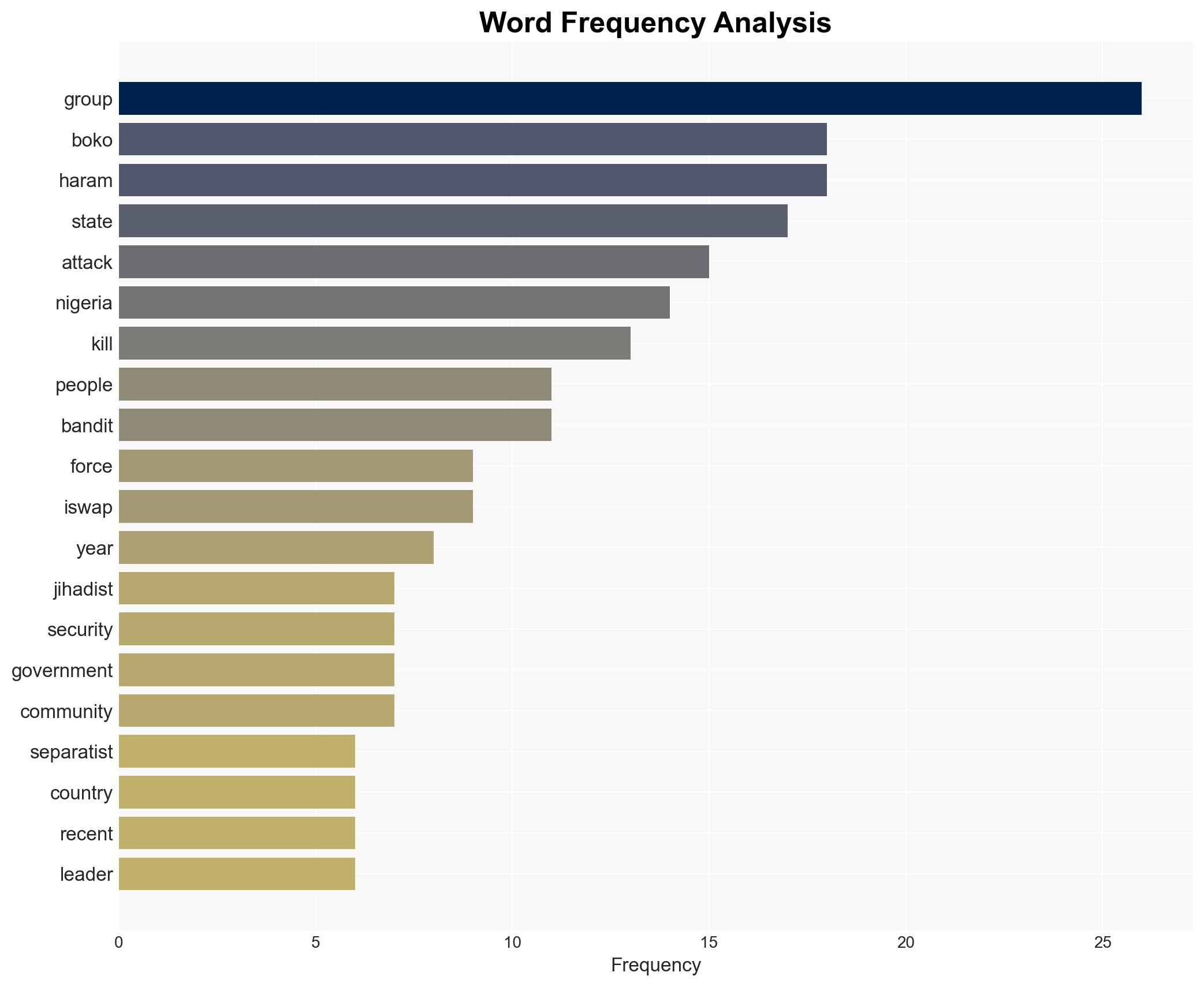
Intelligence Report: The kidnap gangs jihadists and separatists wreaking havoc in Nigeria
1. BLUF (Bottom Line Up Front)
Nigeria is experiencing significant security challenges due to the activities of kidnap gangs, jihadists, and separatists. The most likely hypothesis is that these groups are exploiting state weaknesses to pursue financial and ideological goals, affecting national stability and security. This assessment is made with moderate confidence due to the complexity and fluidity of the situation.
2. Competing Hypotheses
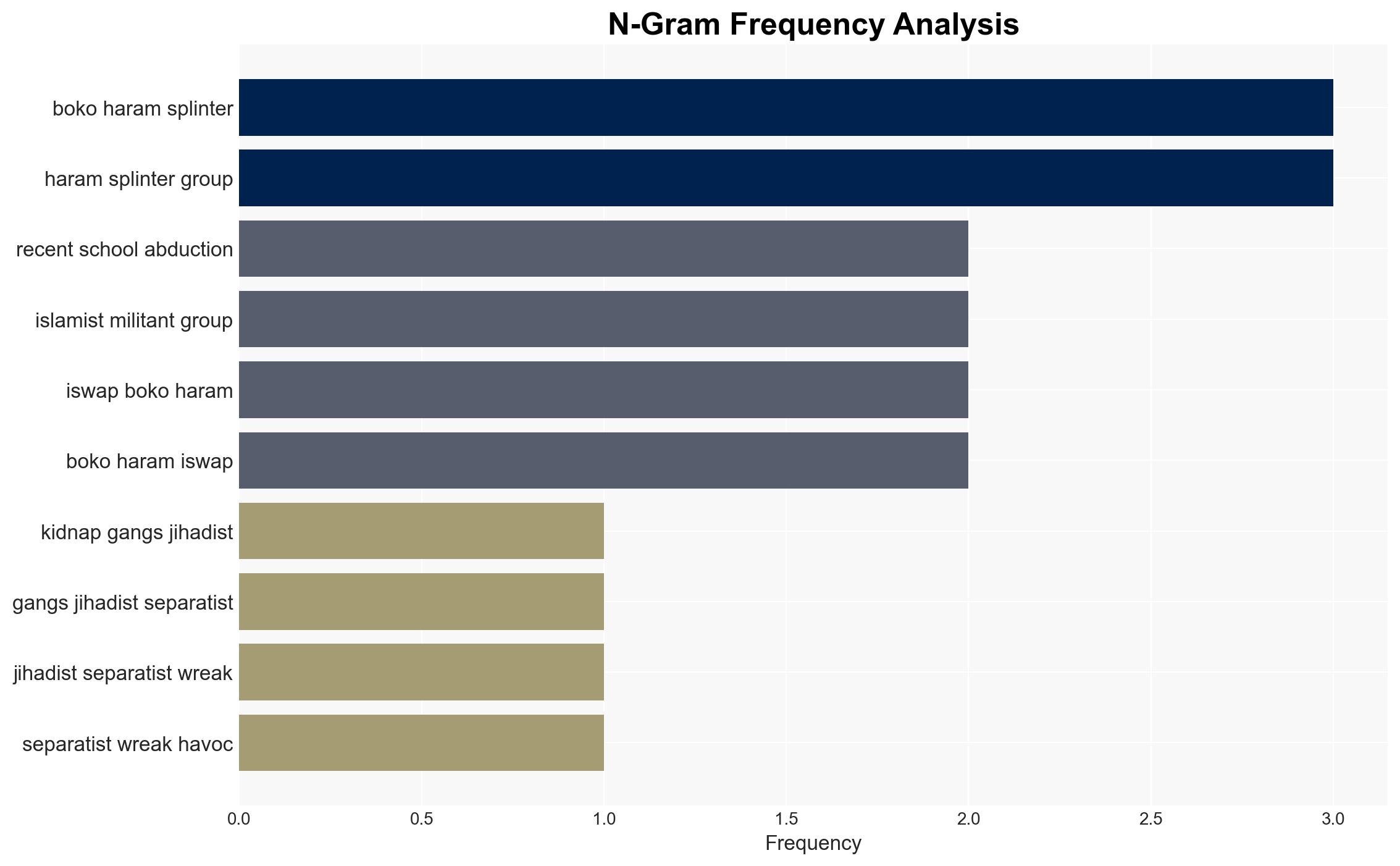
- Hypothesis A: The primary motivation of these groups is financial gain, with ideological and political goals being secondary. This is supported by the prevalence of kidnappings for ransom and the lack of centralized leadership among bandit groups. However, the involvement of jihadist factions suggests some ideological motivations.
- Hypothesis B: The groups are primarily driven by ideological and political objectives, using financial crimes as a means to fund their operations. This is supported by the historical context of jihadist groups like Boko Haram and ISWAP. Contradicting evidence includes the opportunistic nature of many kidnappings.
- Assessment: Hypothesis A is currently better supported due to the widespread and indiscriminate nature of kidnappings, indicating financial motivations. Key indicators that could shift this judgment include increased coordination among groups or a rise in ideologically motivated attacks.
3. Key Assumptions and Red Flags
- Assumptions: The Nigerian security forces remain overstretched; the groups lack unified leadership; financial incentives are a primary driver.
- Information Gaps: Detailed intelligence on the internal dynamics and leadership structures of these groups; the extent of foreign influence or support.
- Bias & Deception Risks: Potential bias in sources emphasizing religious or ethnic narratives; risk of deception from groups overstating ideological motives to gain legitimacy.
4. Implications and Strategic Risks
The ongoing instability could exacerbate regional tensions and undermine Nigeria’s economic and social fabric. The interplay between criminal, jihadist, and separatist activities may lead to further fragmentation and conflict.
- Political / Geopolitical: Potential for increased regional instability and international intervention if violence escalates.
- Security / Counter-Terrorism: Continued strain on security forces, potential for increased recruitment by extremist groups.
- Cyber / Information Space: Use of social media by groups for recruitment and propaganda, as seen with young bandits on TikTok.
- Economic / Social: Disruption of local economies, increased displacement, and social unrest.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance intelligence-sharing with regional partners, increase surveillance and monitoring of known hotspots.
- Medium-Term Posture (1–12 months): Strengthen local law enforcement capabilities, foster community resilience programs, and engage in dialogue with non-violent factions.
- Scenario Outlook:
- Best: Successful negotiation and disarmament of key groups, leading to reduced violence.
- Worst: Escalation of violence and territorial control by extremist factions.
- Most-Likely: Continued sporadic violence with occasional peaks, driven by financial incentives.
6. Key Individuals and Entities
- Ado Aleru (Bandit leader)
- Bello Turji (Bandit leader)
- Abubakar Shekau (Deceased Boko Haram leader)
- Abu Musab al-Barnawi (ISWAP leader)
- Not clearly identifiable from open sources in this snippet for other key figures.
7. Thematic Tags
Counter-Terrorism, kidnapping, insurgency, Nigeria security, jihadism, separatism, regional instability
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us