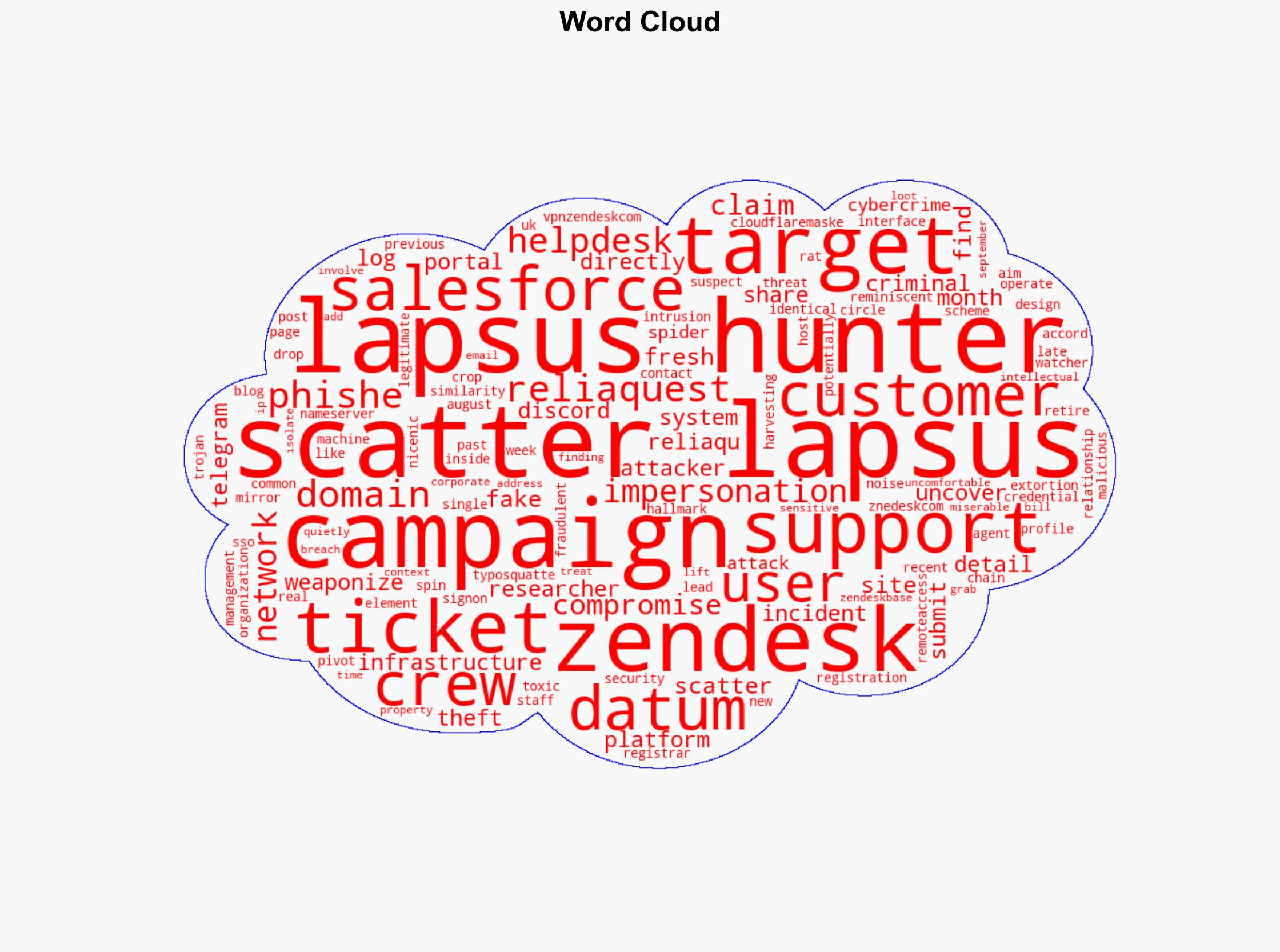
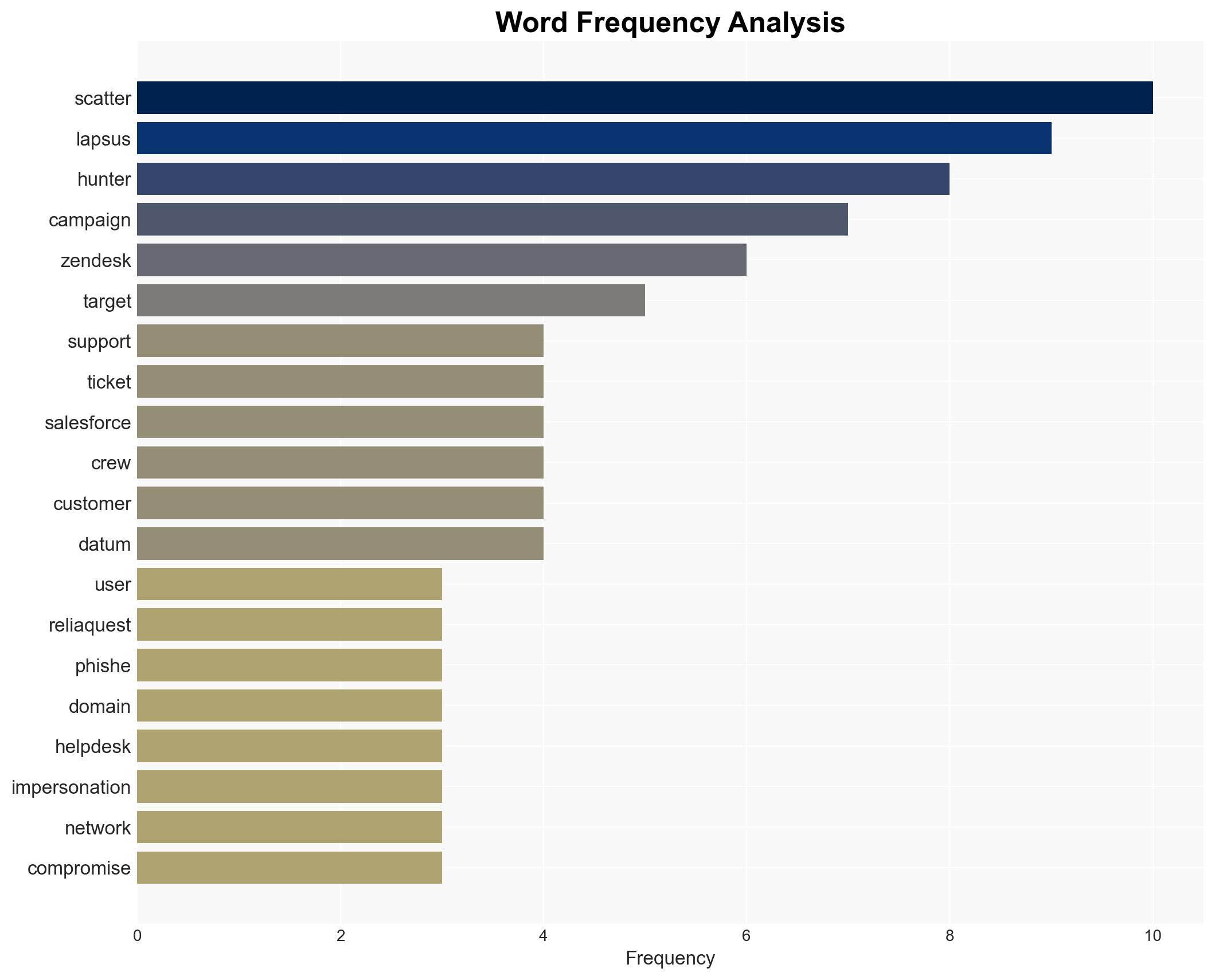
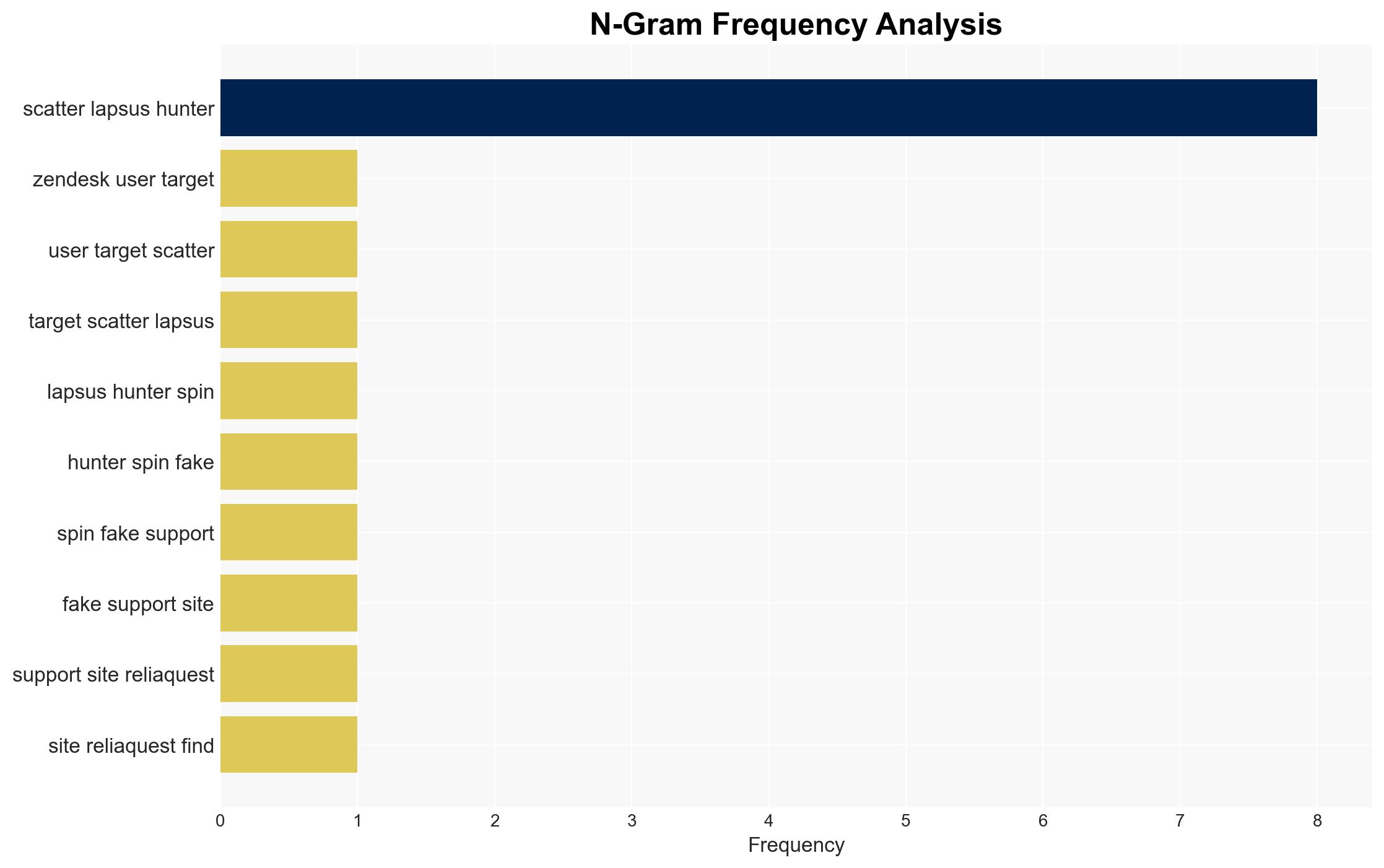
Scattered Lapsus Hunters Launch Phishing Campaign Targeting Zendesk Users with Fake Support Sites
Published on: 2025-11-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Zendesk users targeted as Scattered Lapsus Hunters spin up fake support sites
1. BLUF (Bottom Line Up Front)
The Scattered Lapsus Hunters group is actively targeting Zendesk users by creating fake support sites to harvest credentials and submit fraudulent tickets. This campaign poses a significant threat to organizations using Zendesk, potentially leading to data breaches and unauthorized network access. The most likely hypothesis is that this is part of a broader extortion campaign. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The Scattered Lapsus Hunters are conducting a targeted extortion campaign against Zendesk users, leveraging fake support sites to gain unauthorized access and extract sensitive information. This is supported by the creation of typosquatted domains and previous similar campaigns against other platforms.
- Hypothesis B: The activity is part of a larger, non-targeted phishing campaign aimed at multiple SaaS platforms, with Zendesk being one of many targets. This is contradicted by the specific focus on Zendesk-related infrastructure and the pattern of previous campaigns.
- Assessment: Hypothesis A is currently better supported due to the specific targeting of Zendesk infrastructure and the historical pattern of similar campaigns by the group. Indicators such as the emergence of new phishing domains and the use of typosquatting could shift this judgment if they begin to target a broader range of platforms.
3. Key Assumptions and Red Flags
- Assumptions: The Scattered Lapsus Hunters have the capability to exploit Zendesk vulnerabilities; the group’s primary motive is financial gain through extortion; the fake sites are effective in harvesting credentials.
- Information Gaps: The full extent of the compromise and the number of affected organizations remain unclear; the specific methods used to distribute phishing links are not detailed.
- Bias & Deception Risks: There is a risk of confirmation bias in interpreting the group’s activities as solely extortion-focused; potential deception by the group in misattributing attacks to other entities.
4. Implications and Strategic Risks
This development could lead to increased cyber threats against SaaS platforms, affecting organizational trust and data security. If successful, it may encourage similar campaigns by other threat actors.
- Political / Geopolitical: Potential for increased tensions between nations if state-sponsored elements are suspected.
- Security / Counter-Terrorism: Heightened alert for organizations using Zendesk and similar platforms; potential for increased security measures.
- Cyber / Information Space: Increased focus on phishing and credential harvesting tactics; potential for broader exploitation of SaaS vulnerabilities.
- Economic / Social: Possible financial losses for affected companies; erosion of trust in SaaS security could impact adoption rates.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor for new phishing domains; enhance user awareness training; implement multi-factor authentication for Zendesk access.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in advanced phishing detection technologies.
- Scenario Outlook:
- Best: The campaign is quickly mitigated with minimal impact, leading to improved security measures.
- Worst: Successful breaches result in significant data loss and financial damage, prompting regulatory scrutiny.
- Most-Likely: Continued attempts with varying success, leading to gradual improvements in organizational defenses.
6. Key Individuals and Entities
- Scattered Lapsus Hunters
- Zendesk
- ReliaQuest (as the reporting entity)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
Cybersecurity, phishing, extortion, SaaS platforms, credential harvesting, cybercrime, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us