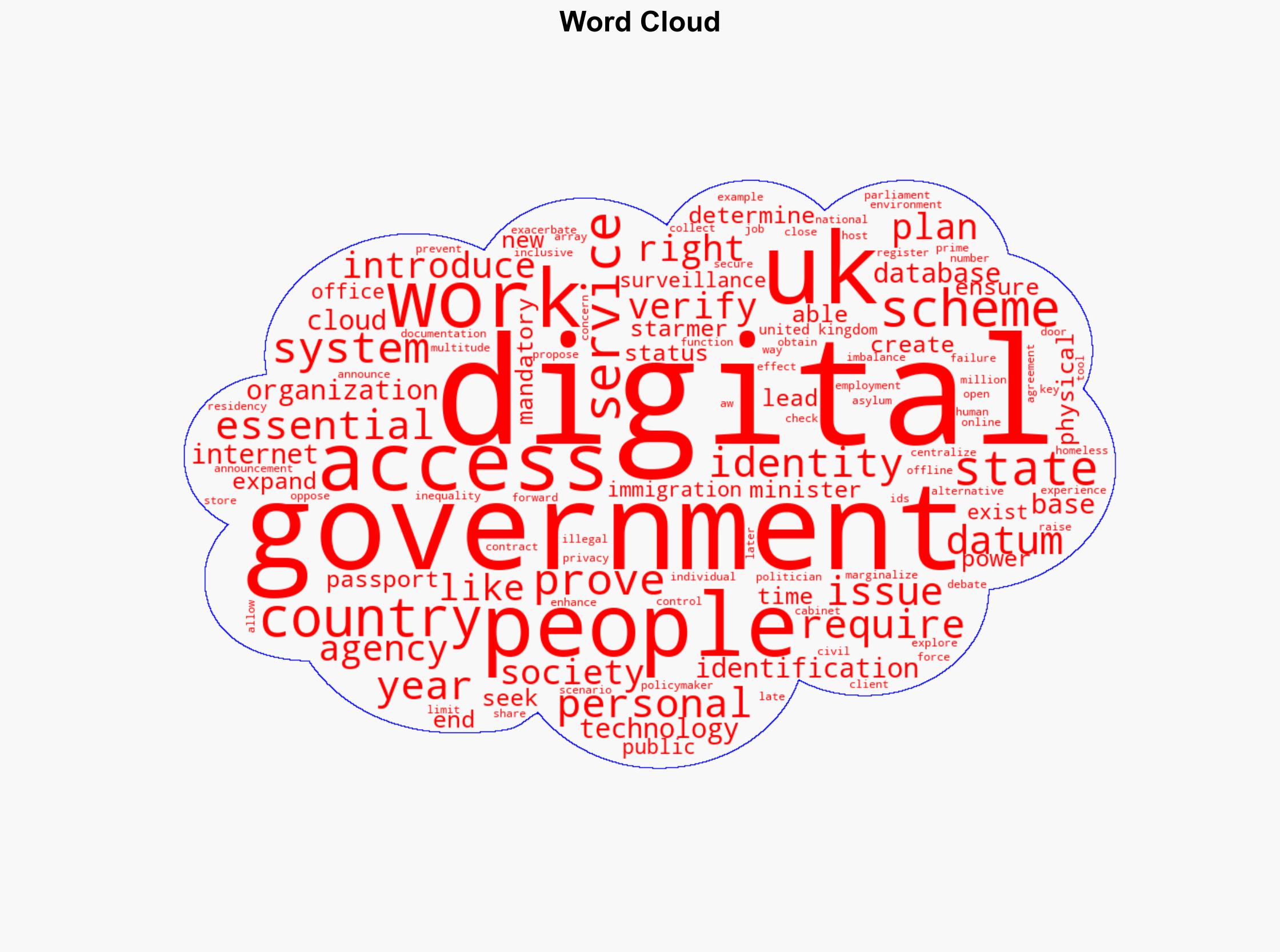
UK’s Digital ID Initiative Raises Concerns Over Privacy and State Control in Access to Essential Services
Published on: 2025-11-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The UK Has It Wrong on Digital ID Heres Why
1. BLUF (Bottom Line Up Front)
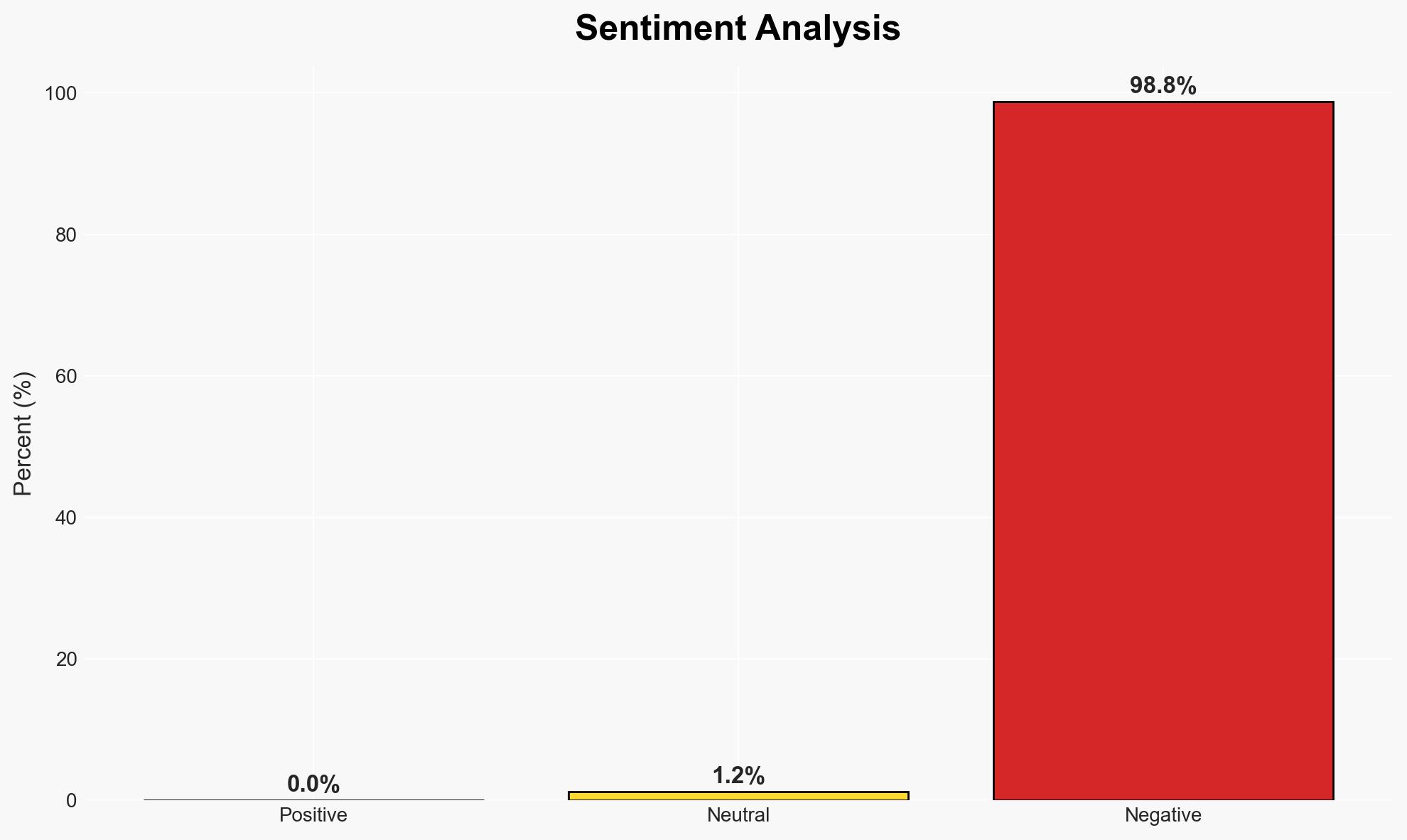
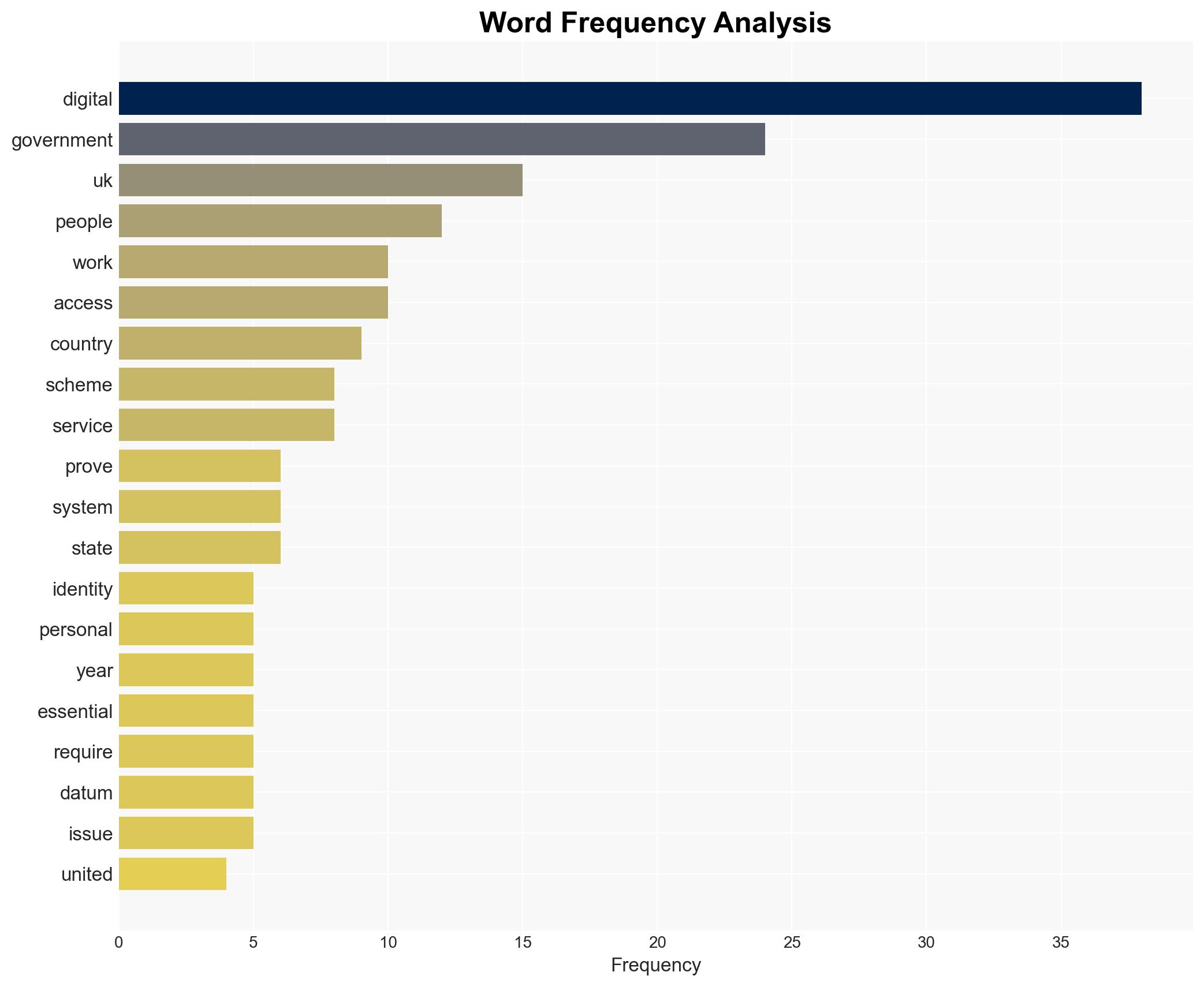
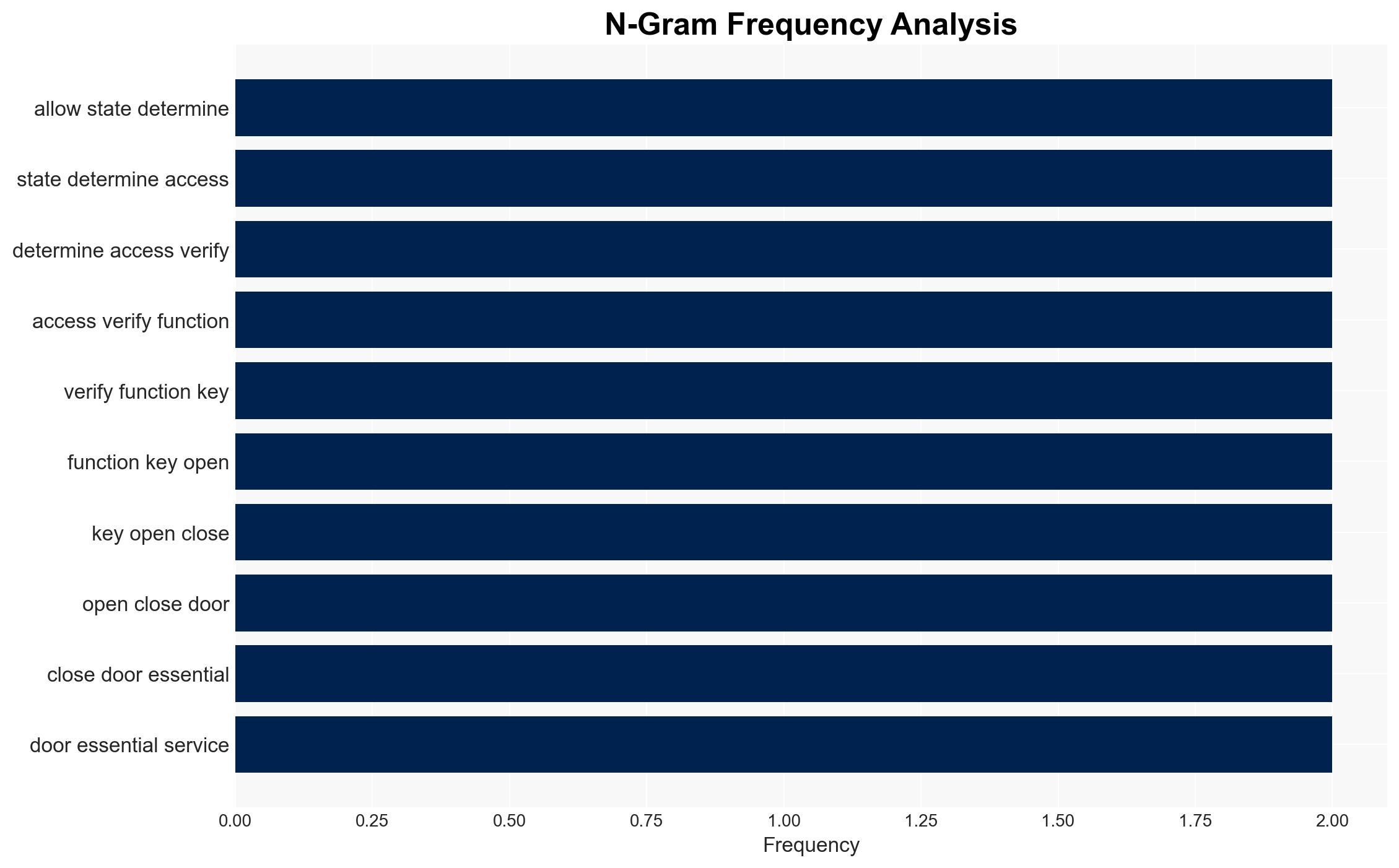
The UK government’s plan to introduce a digital ID scheme is likely to face significant challenges related to privacy, social inequality, and potential mission creep. The most likely hypothesis is that the scheme will exacerbate existing social divisions and face resistance from civil society. Overall confidence in this judgment is moderate, given the uncertainties surrounding implementation and public acceptance.
2. Competing Hypotheses
- Hypothesis A: The digital ID scheme will improve efficiency and security by streamlining identity verification processes. Supporting evidence includes the government’s claim that it will reduce administrative burdens and prevent fraud. Contradicting evidence includes concerns about privacy violations and potential misuse of data.
- Hypothesis B: The digital ID scheme will lead to increased surveillance and social inequality. Supporting evidence includes warnings from civil society organizations about mission creep and exclusion of marginalized groups. Contradicting evidence is the government’s assurance of inclusivity and privacy protection.
- Assessment: Hypothesis B is currently better supported due to historical precedents of surveillance expansion and the lack of clear safeguards against data misuse. Indicators that could shift this judgment include transparent implementation plans and robust privacy protections.
3. Key Assumptions and Red Flags
- Assumptions: The government will implement the digital ID scheme as currently proposed; public resistance will focus on privacy and inequality issues; technological infrastructure will support widespread adoption.
- Information Gaps: Details on data protection measures, the scope of data collection, and specific use cases for the digital ID are unclear.
- Bias & Deception Risks: Potential confirmation bias in government narratives emphasizing efficiency over privacy; risk of underestimating public opposition due to selective consultation processes.
4. Implications and Strategic Risks
The digital ID initiative could significantly influence the UK’s socio-political landscape, with potential long-term effects on civil liberties and public trust in government.
- Political / Geopolitical: Could strain government-civil society relations and impact the UK’s international reputation regarding privacy standards.
- Security / Counter-Terrorism: May enhance identity verification but also increase risks of data breaches and misuse by malicious actors.
- Cyber / Information Space: Raises concerns about data security and potential exploitation by cybercriminals.
- Economic / Social: Could widen social inequalities, particularly affecting those without access to digital infrastructure or those with uncertain residency status.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive risk assessment focusing on privacy and social impact; engage with civil society to address concerns.
- Medium-Term Posture (1–12 months): Develop robust data protection frameworks; establish oversight mechanisms to prevent misuse and ensure transparency.
- Scenario Outlook:
- Best: Successful implementation with strong privacy safeguards, enhancing efficiency without social backlash.
- Worst: Public backlash leading to policy reversal or significant social unrest.
- Most-Likely: Gradual implementation with ongoing public debate and adjustments to address privacy concerns.
6. Key Individuals and Entities
- Keir Starmer, UK Prime Minister
- UK Government
- Civil Society Organizations
- Not clearly identifiable from open sources in this snippet for additional individuals/entities.
7. Thematic Tags
Cybersecurity, digital identity, privacy, social inequality, government policy, surveillance, civil liberties
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us