200 Million X User Records Released 28 Billion Twitter IDs Leaked – Forbes
Published on: 2025-04-01
Intelligence Report: 200 Million X User Records Released 28 Billion Twitter IDs Leaked – Forbes
1. BLUF (Bottom Line Up Front)
A significant data breach has occurred involving the release of 200 million user records and 28 billion Twitter IDs. The breach was facilitated by exploiting a vulnerability in the platform, leading to the unauthorized access and distribution of sensitive user data. Immediate actions are required to mitigate further risks and protect user privacy. Key recommendations include enhancing cybersecurity measures and conducting a thorough investigation to identify the breach’s full scope and prevent future incidents.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
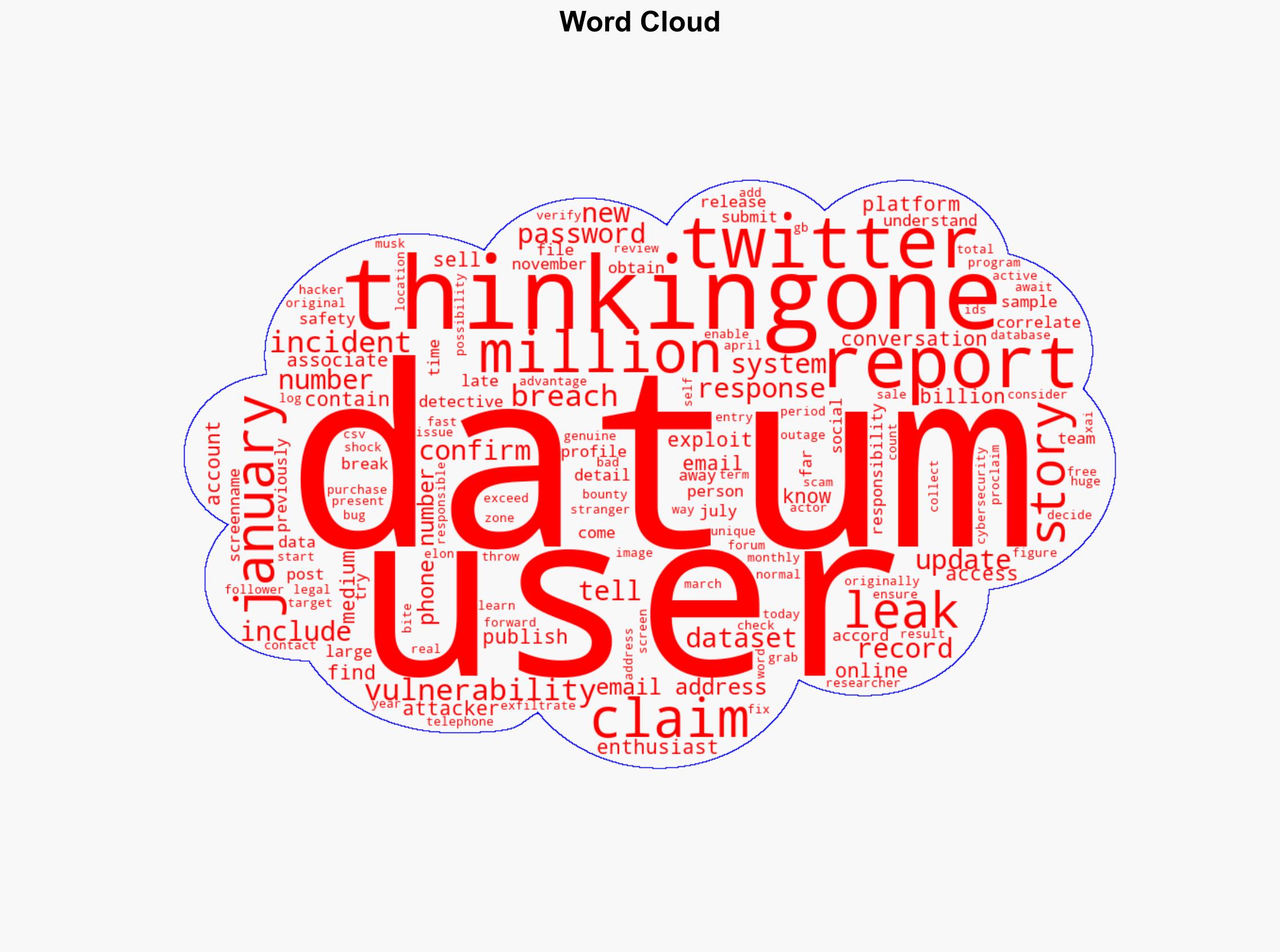
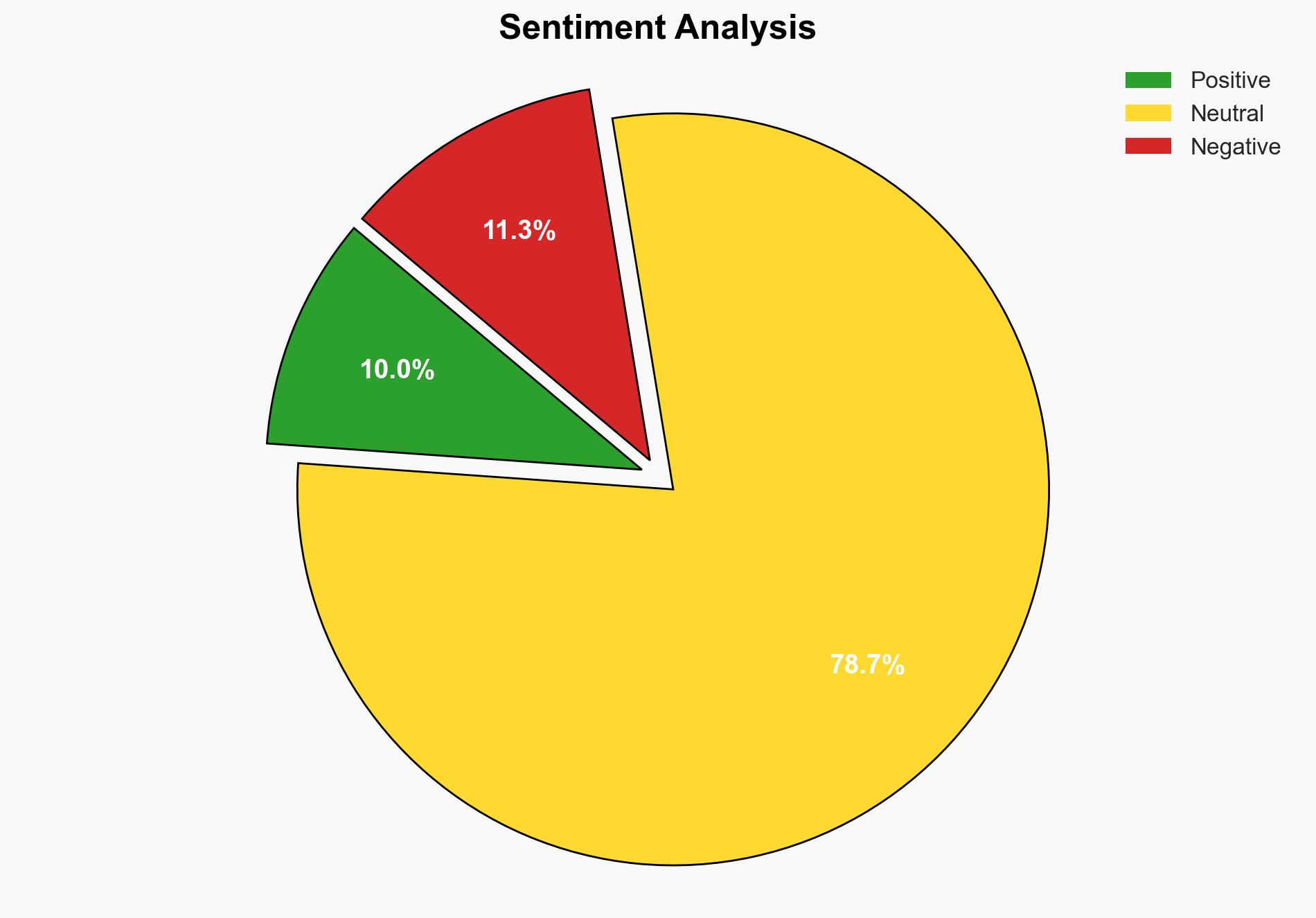
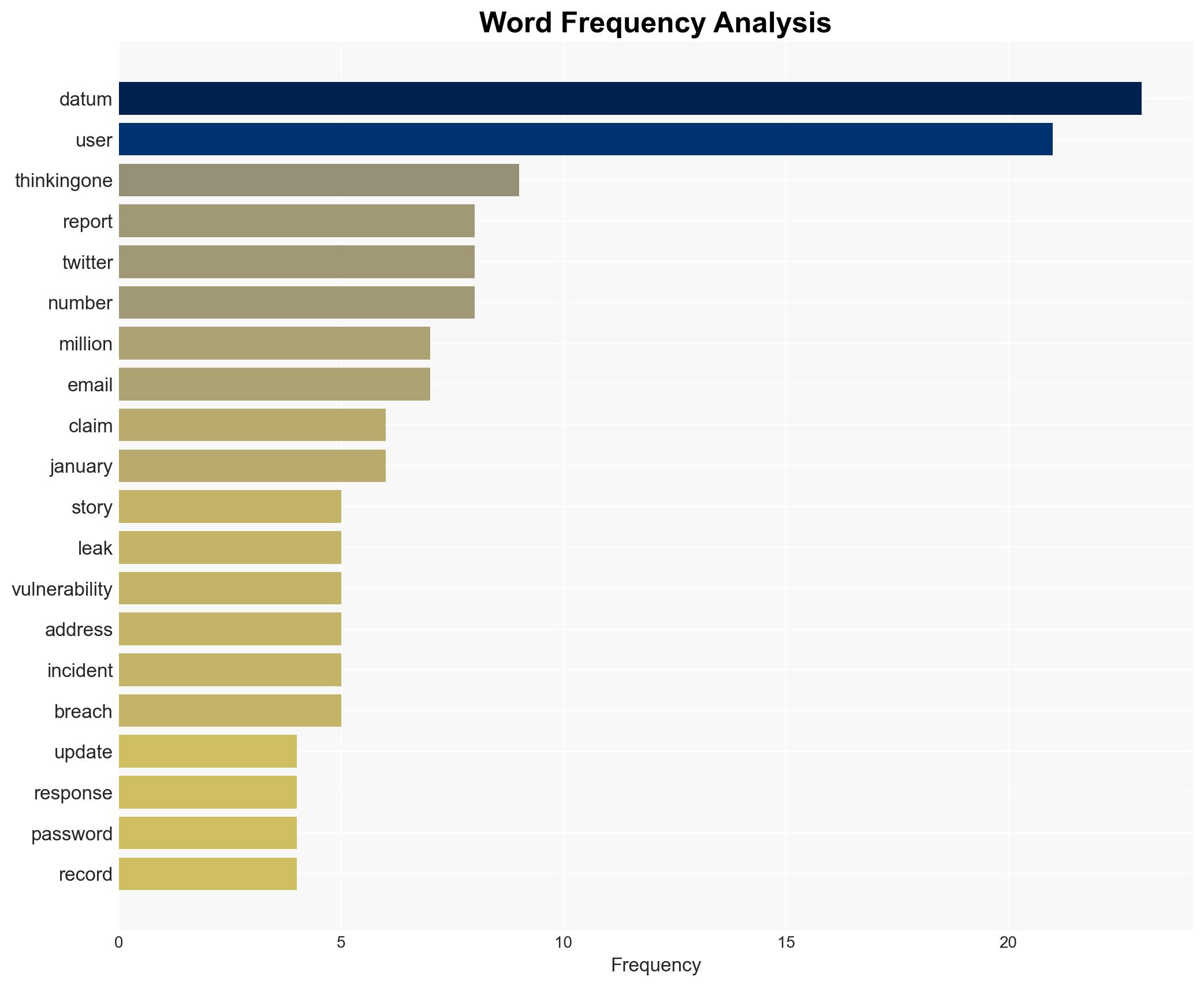
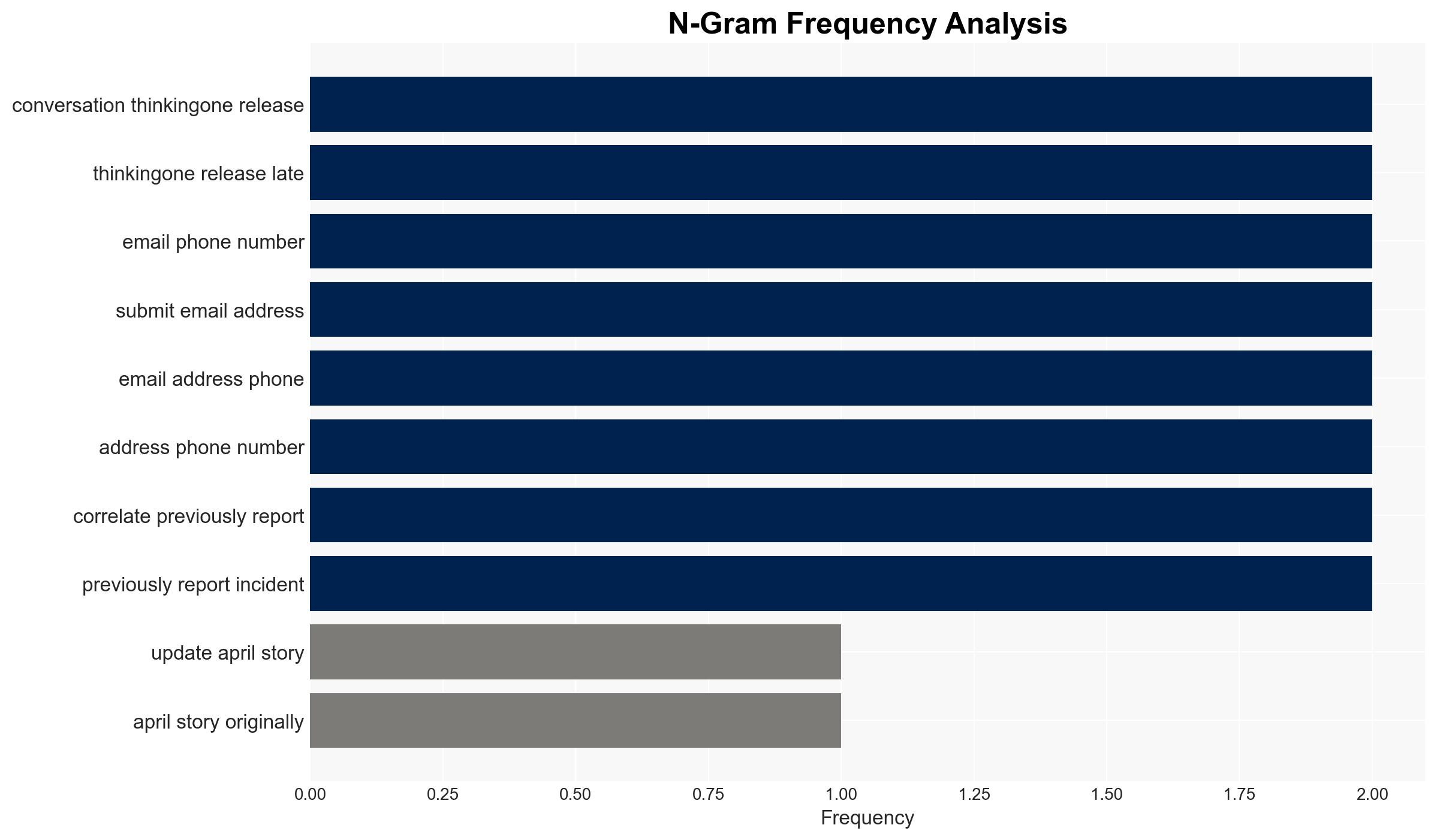
The breach was initially identified in January when a vulnerability was discovered through a bug bounty program. Despite efforts to address the issue, the data was later leaked by an individual known as thinkingone, who claimed to have accessed the data and released it for free. The dataset includes user IDs, names, locations, email addresses, follower counts, and other profile data. Verification by cybersecurity teams confirmed the authenticity of the data. The breach represents one of the largest in terms of user records, raising concerns about the platform’s security protocols and user data protection.
3. Implications and Strategic Risks
The breach poses significant risks to user privacy and platform integrity. The exposure of email addresses and phone numbers increases the likelihood of phishing attacks and identity theft. Additionally, the breach may undermine user trust in the platform, potentially impacting user engagement and revenue. From a national security perspective, the breach could be exploited by malicious actors to conduct targeted misinformation campaigns or other cyber operations.
4. Recommendations and Outlook
Recommendations:
- Enhance cybersecurity measures, including regular vulnerability assessments and penetration testing.
- Implement stricter data access controls and encryption protocols to safeguard user information.
- Conduct a comprehensive investigation to identify the breach’s root cause and prevent recurrence.
- Engage with users transparently about the breach and the steps being taken to protect their data.
Outlook:
In the best-case scenario, swift action to address the breach and improve security measures will restore user trust and prevent further data leaks. In the worst-case scenario, continued vulnerabilities could lead to additional breaches, damaging the platform’s reputation and financial standing. The most likely outcome involves a gradual recovery as security enhancements are implemented and user confidence is rebuilt over time.
5. Key Individuals and Entities
The report mentions Elon Musk in the context of platform ownership, and thinkingone as the individual claiming responsibility for the data release. These individuals are central to understanding the breach’s context and potential motivations.