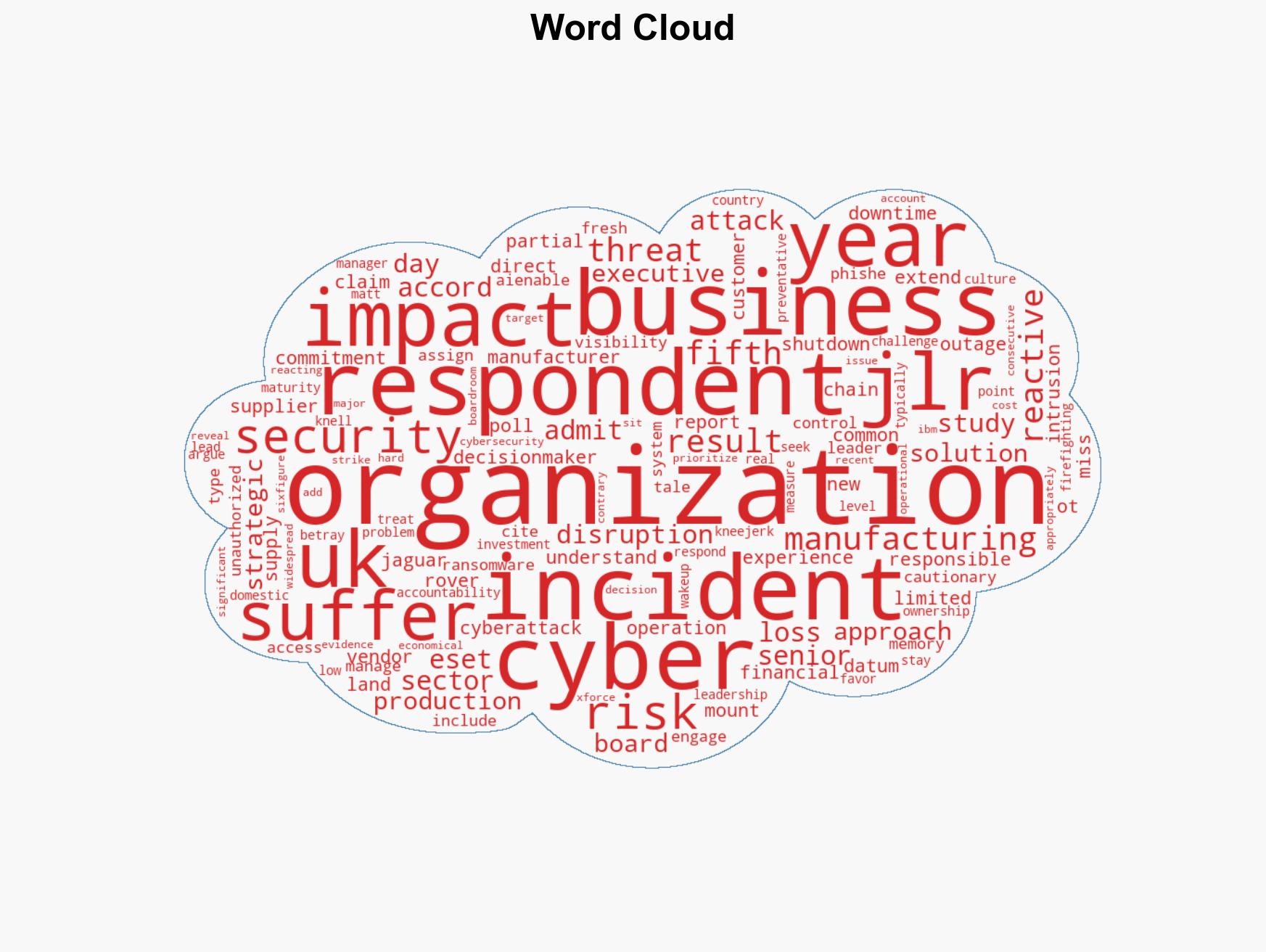
78% of UK Manufacturers Experience Significant Cyber Incidents in the Past Year, Reveals ESET Study
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Eight in 10 UK Manufacturers Hit by Cyber Incident in a Year
1. BLUF (Bottom Line Up Front)
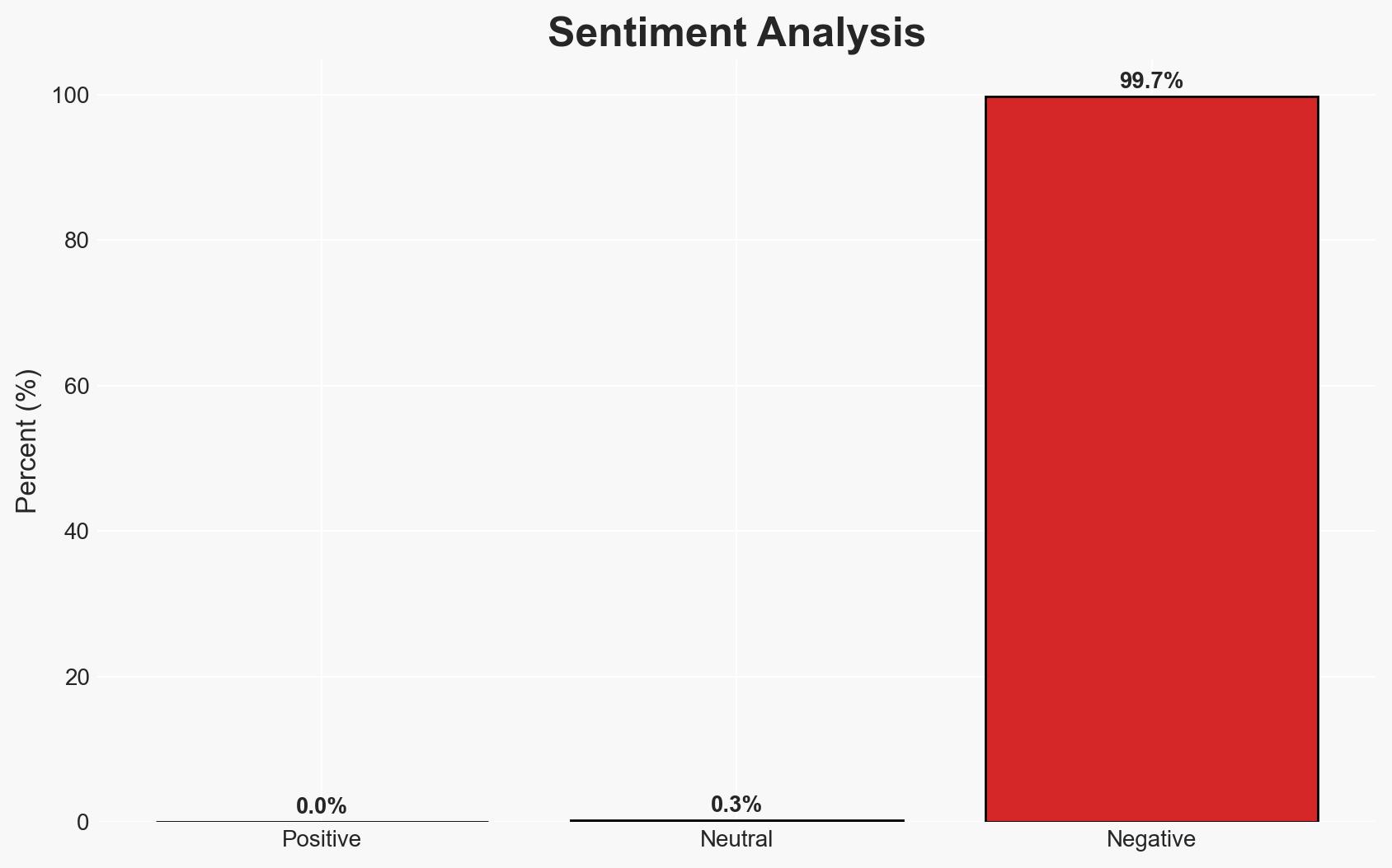
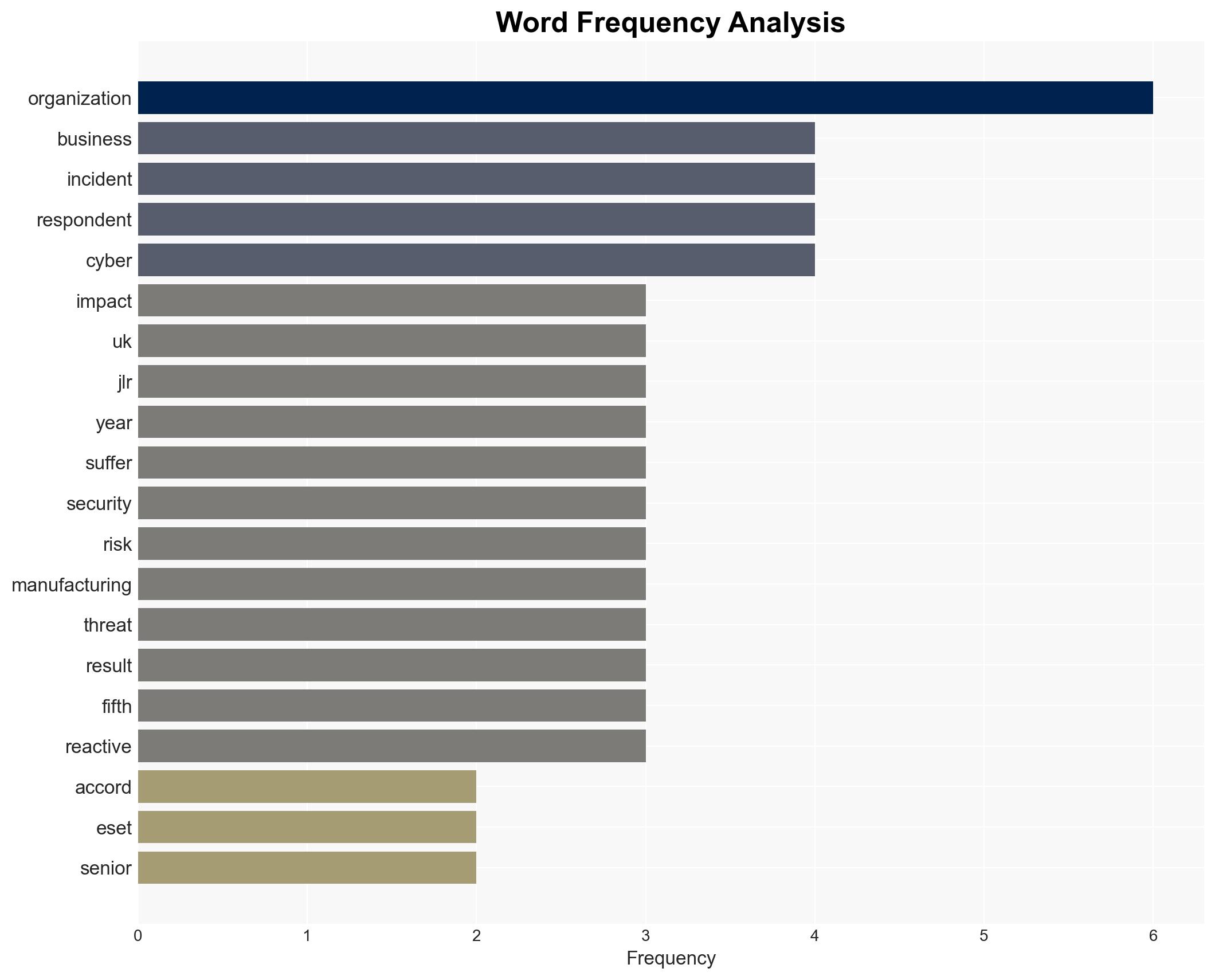
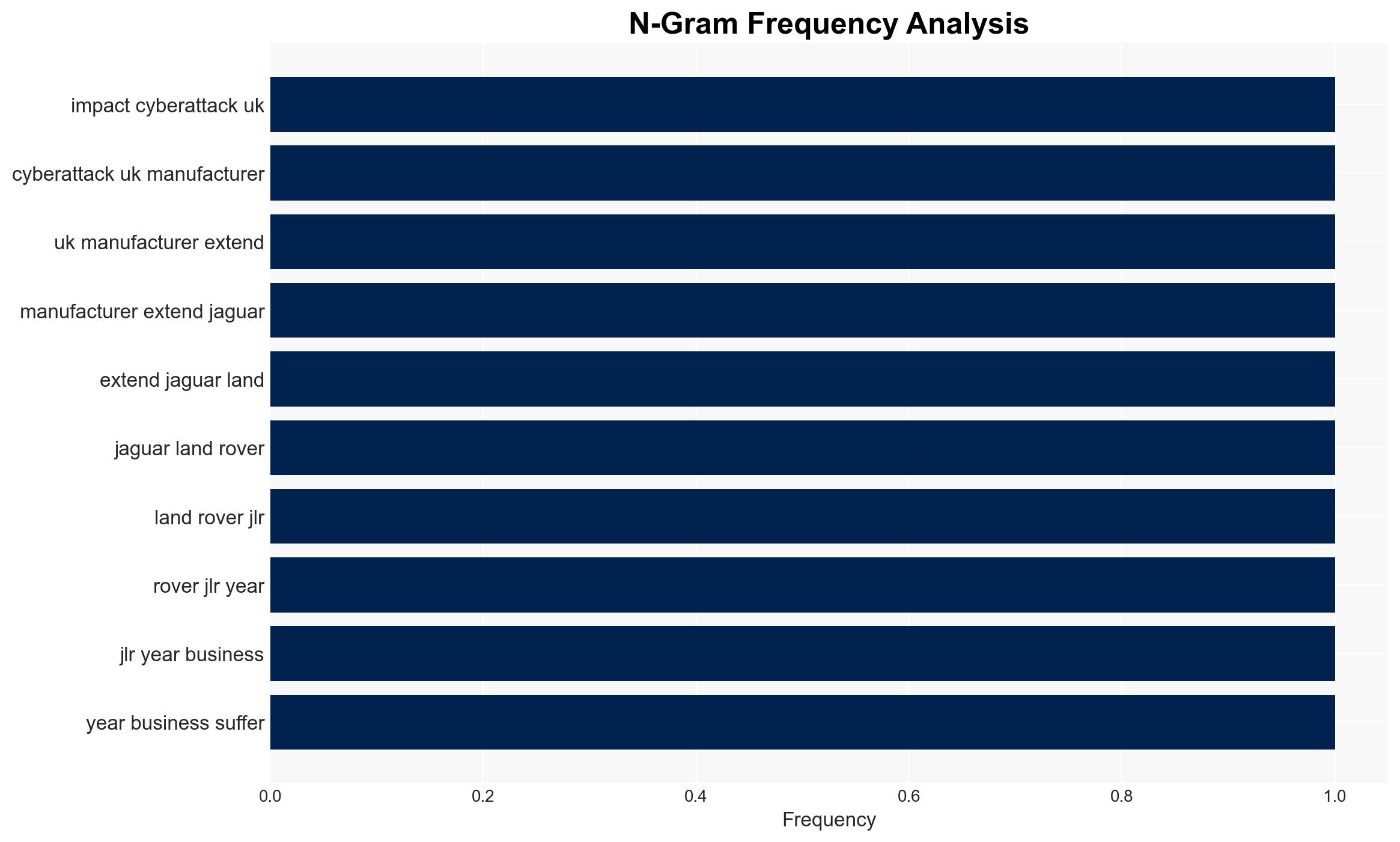
The UK manufacturing sector is experiencing significant cyber threats, with 78% of businesses reporting serious incidents in the past year. The sector’s vulnerability is exacerbated by a lack of strategic cyber risk management at the executive level. This situation poses substantial operational and financial risks, with moderate confidence in the assessment that current security practices are inadequate to address the evolving threat landscape.
2. Competing Hypotheses
- Hypothesis A: The high incidence of cyber-attacks is primarily due to inadequate cybersecurity practices and lack of strategic oversight by executive leadership. This is supported by evidence of low engagement from boards and a reactive approach to cybersecurity.
- Hypothesis B: The prevalence of cyber-attacks is driven by an increase in sophisticated threat actors targeting the manufacturing sector, independent of internal security practices. This is supported by the high percentage of AI-enabled attacks reported.
- Assessment: Hypothesis A is currently better supported due to the evidence of organizational immaturity in handling cyber risks and the lack of executive accountability. Indicators such as increased board engagement and strategic investment in cybersecurity could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Cybersecurity is not prioritized at the executive level; reactive measures are less effective than preventative strategies; AI-enabled attacks are a significant threat vector.
- Information Gaps: Specific details on the nature and origin of the cyber-attacks; comprehensive data on cybersecurity investments and strategies across the sector.
- Bias & Deception Risks: Potential bias in survey responses due to self-reporting; risk of underreporting incidents to avoid reputational damage; vendor bias from ESET’s involvement in the study.
4. Implications and Strategic Risks
The persistent cyber threats to UK manufacturers could lead to increased operational disruptions and financial losses, affecting national economic stability and supply chain integrity.
- Political / Geopolitical: Potential for increased regulatory scrutiny and policy interventions to bolster cybersecurity in critical sectors.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks being leveraged for industrial espionage or sabotage by hostile state or non-state actors.
- Cyber / Information Space: Escalation in the sophistication of cyber threats, including AI-enabled attacks, necessitating advanced defensive measures.
- Economic / Social: Financial losses and operational disruptions could lead to job losses and reduced competitiveness of UK manufacturers globally.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a sector-wide cybersecurity audit; enhance monitoring of cyber threats; engage executive leadership in cybersecurity strategy development.
- Medium-Term Posture (1–12 months): Develop sector-specific cybersecurity frameworks; invest in AI-driven threat detection and response capabilities; foster public-private partnerships for information sharing.
- Scenario Outlook:
- Best: Improved cybersecurity posture reduces incident rates, with executive leadership actively managing cyber risks.
- Worst: Continued reactive approaches lead to increased incidents and severe economic impacts.
- Most-Likely: Gradual improvement in cybersecurity practices with ongoing challenges from sophisticated threat actors.
6. Key Individuals and Entities
- Jaguar Land Rover (JLR)
- ESET (security vendor)
- Matt Knell (ESET UK country manager)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, manufacturing sector, AI-enabled attacks, executive leadership, supply chain disruption, economic impact, cyber risk management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us