Surge in AI-driven selfie age verification as governments enhance online safety regulations
Published on: 2025-11-29
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Selfie-based age checks boom as govts push for online controls
1. BLUF (Bottom Line Up Front)
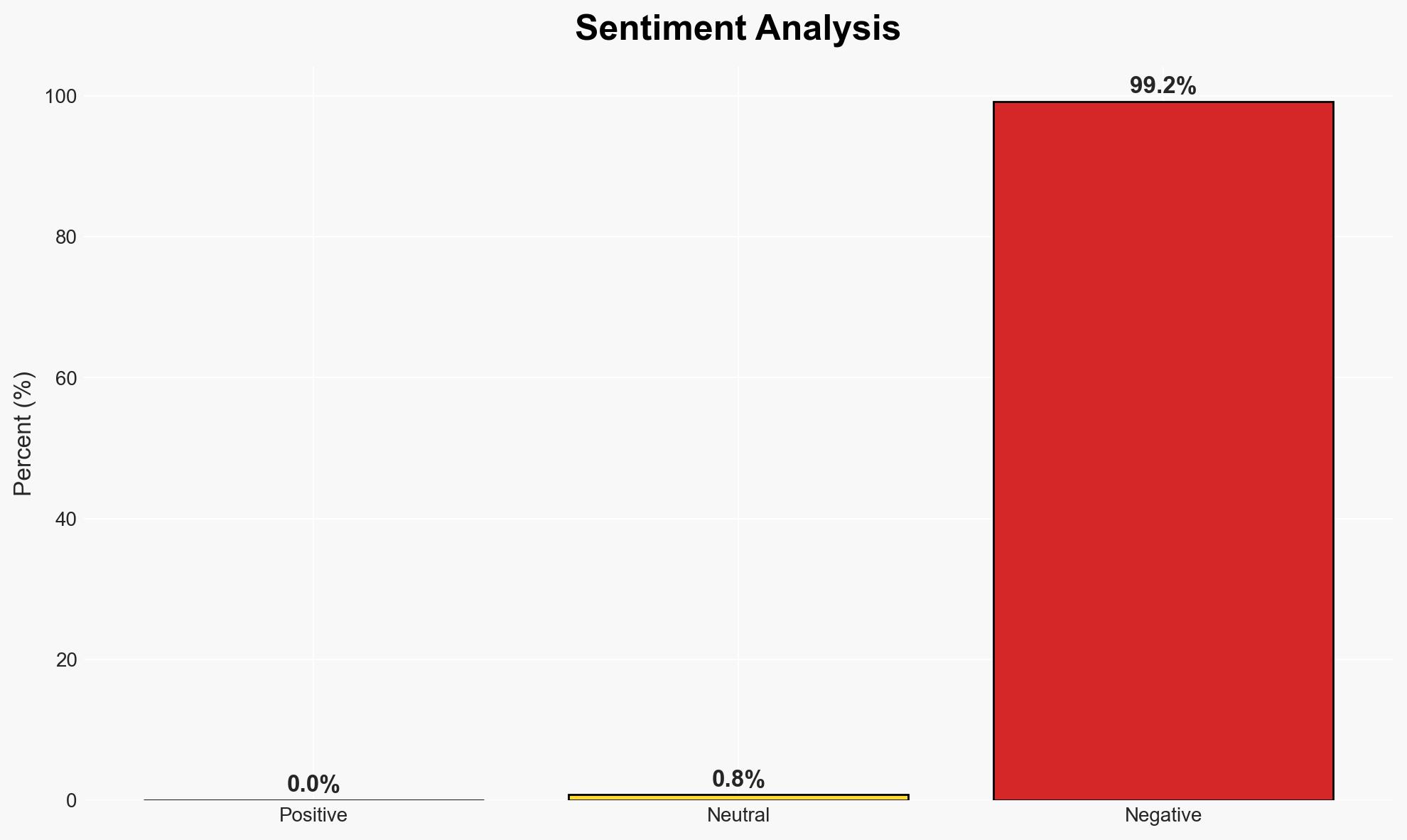
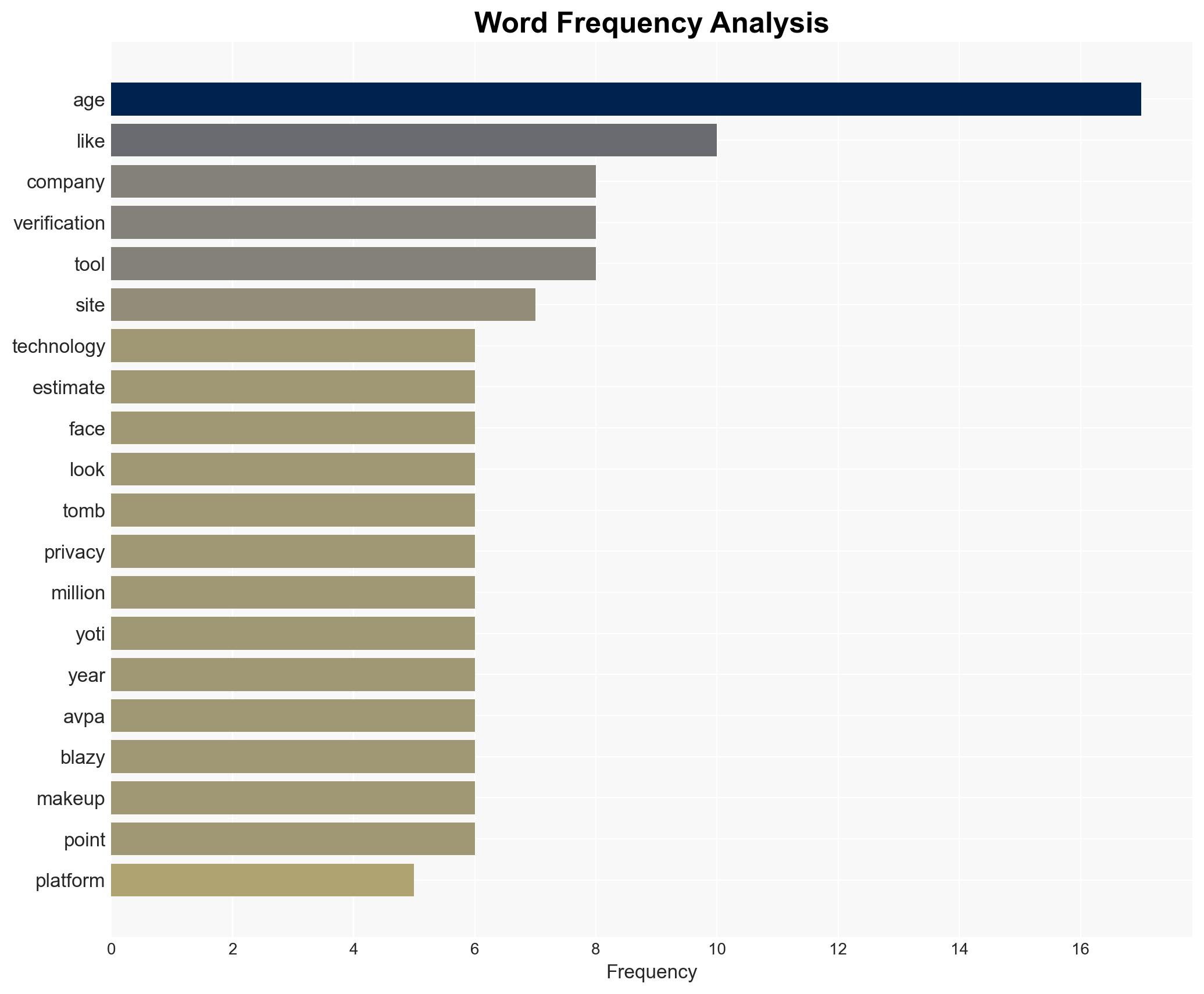
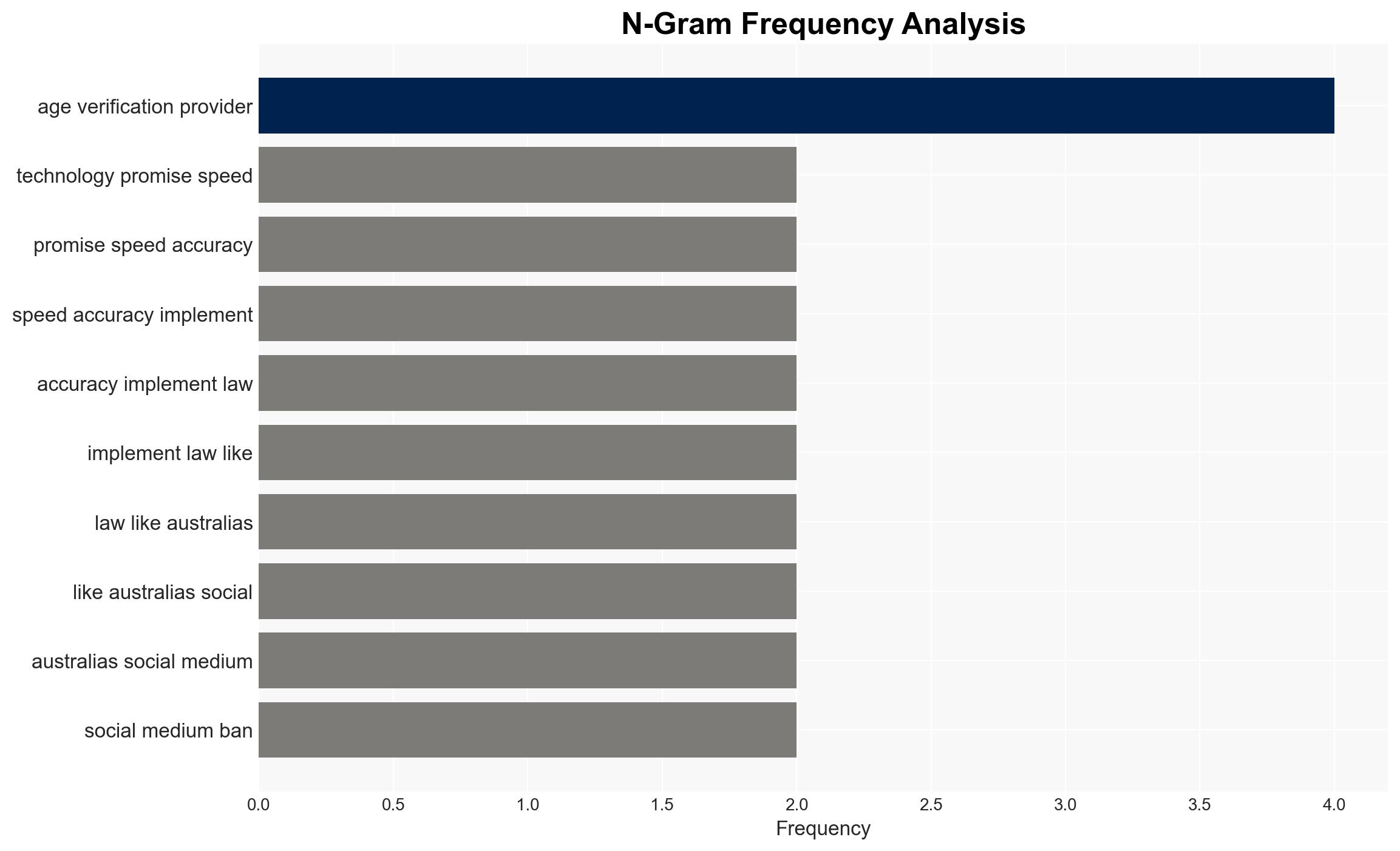
The adoption of AI-driven selfie-based age verification technologies is accelerating, driven by government regulations such as Australia’s social media age verification law. This trend is primarily affecting online platforms and users, with significant privacy and bias concerns. The most likely hypothesis is that these technologies will continue to expand, albeit with increasing scrutiny. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The expansion of selfie-based age verification technologies will continue unabated due to regulatory pressures and technological advancements. Supporting evidence includes the rapid adoption by major companies and the forecasted growth in the sector. However, uncertainties remain regarding privacy concerns and potential biases in the technology.
- Hypothesis B: The growth of selfie-based age verification technologies will face significant setbacks due to privacy issues, bias in AI algorithms, and potential public backlash. Supporting evidence includes expert concerns about privacy and bias, and the potential for regulatory pushback. Contradicting evidence is the current momentum and investment in these technologies.
- Assessment: Hypothesis A is currently better supported due to the strong regulatory drivers and commercial interest. Key indicators that could shift this judgment include significant legal challenges or public opposition to privacy intrusions.
3. Key Assumptions and Red Flags
- Assumptions: Governments will continue to enforce age verification laws; AI technologies will improve in accuracy and bias reduction; user acceptance will remain stable.
- Information Gaps: Detailed data on the accuracy of age verification across diverse demographics; comprehensive privacy impact assessments.
- Bias & Deception Risks: Potential cognitive bias in underestimating public resistance; source bias from industry stakeholders promoting technology benefits; manipulation risks from AI vendors overstating accuracy.
4. Implications and Strategic Risks
The proliferation of selfie-based age verification technologies could reshape online identity verification, with broad implications across sectors.
- Political / Geopolitical: Potential for international regulatory divergence, affecting cross-border digital services.
- Security / Counter-Terrorism: Enhanced verification could reduce underage access to restricted content, but may also create new vectors for identity fraud.
- Cyber / Information Space: Increased data collection heightens cybersecurity risks and the potential for data breaches.
- Economic / Social: Growth in the age verification sector could spur economic activity, but privacy concerns may lead to social pushback.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor regulatory developments and public sentiment; engage with privacy advocates to address concerns.
- Medium-Term Posture (1–12 months): Develop partnerships with AI ethics organizations; invest in improving algorithmic fairness and transparency.
- Scenario Outlook:
- Best: Widespread adoption with minimal privacy issues; triggers include successful privacy safeguards.
- Worst: Major privacy breaches leading to regulatory clampdowns; triggers include significant data leaks.
- Most-Likely: Continued growth with ongoing privacy debates; triggers include incremental regulatory adjustments.
6. Key Individuals and Entities
- Robin Tombs, CEO of Yoti
- Meta, TikTok, Sony (clients of age verification services)
- Iain Corby, Director of AVPA
- Olivier Blazy, Cybersecurity Professor, Polytechnique
7. Thematic Tags
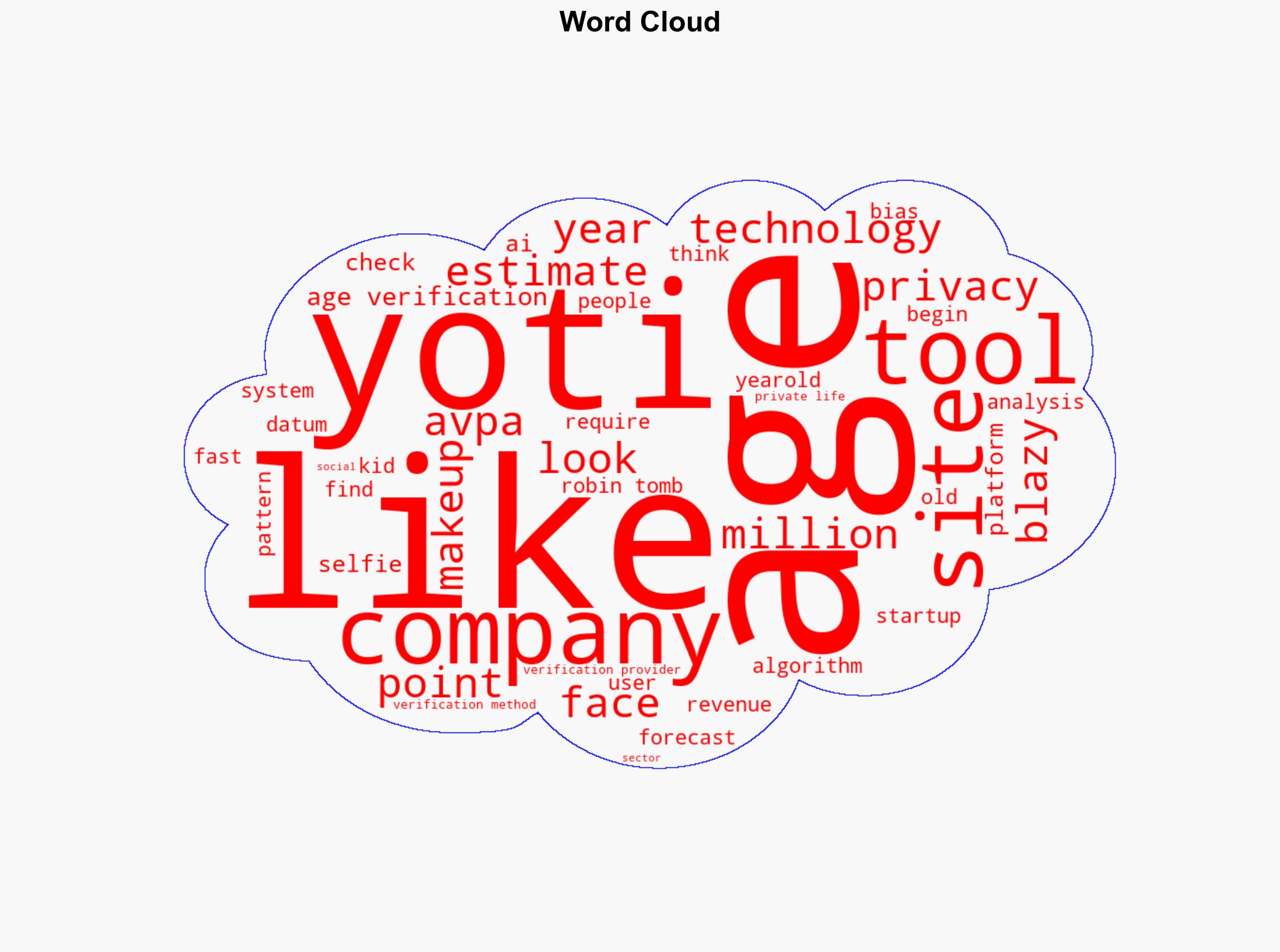
Cybersecurity, age verification, AI technology, privacy concerns, regulatory compliance, digital identity, online platforms
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Cognitive Bias Stress Test: Structured challenge to expose and correct biases.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us