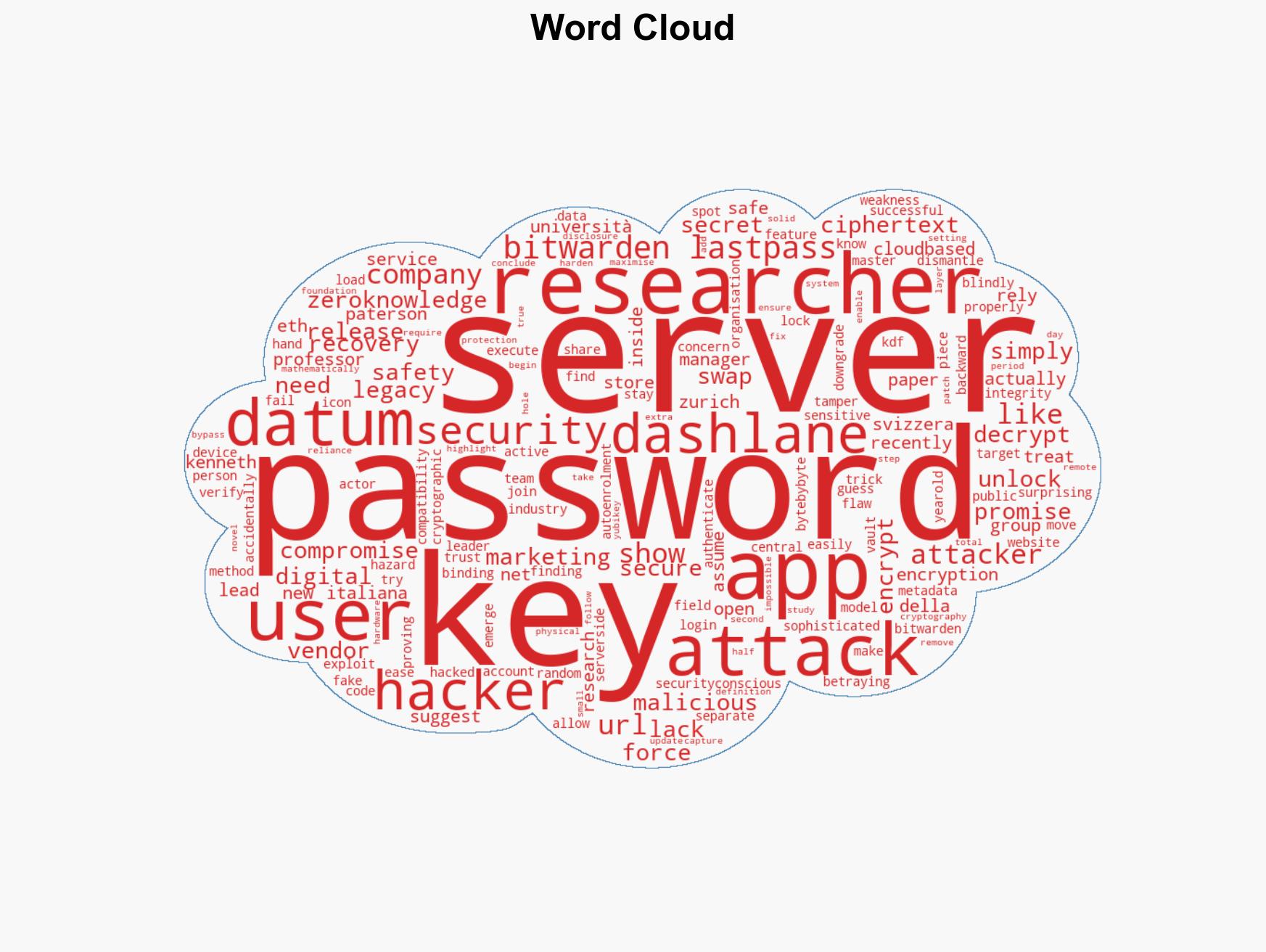
Study Reveals 27 Vulnerabilities in Leading Password Managers, Undermining Zero-Knowledge Encryption Claims
Published on: 2026-02-22
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Researchers Demonstrate 27 Attacks Against Major Password Managers
1. BLUF (Bottom Line Up Front)
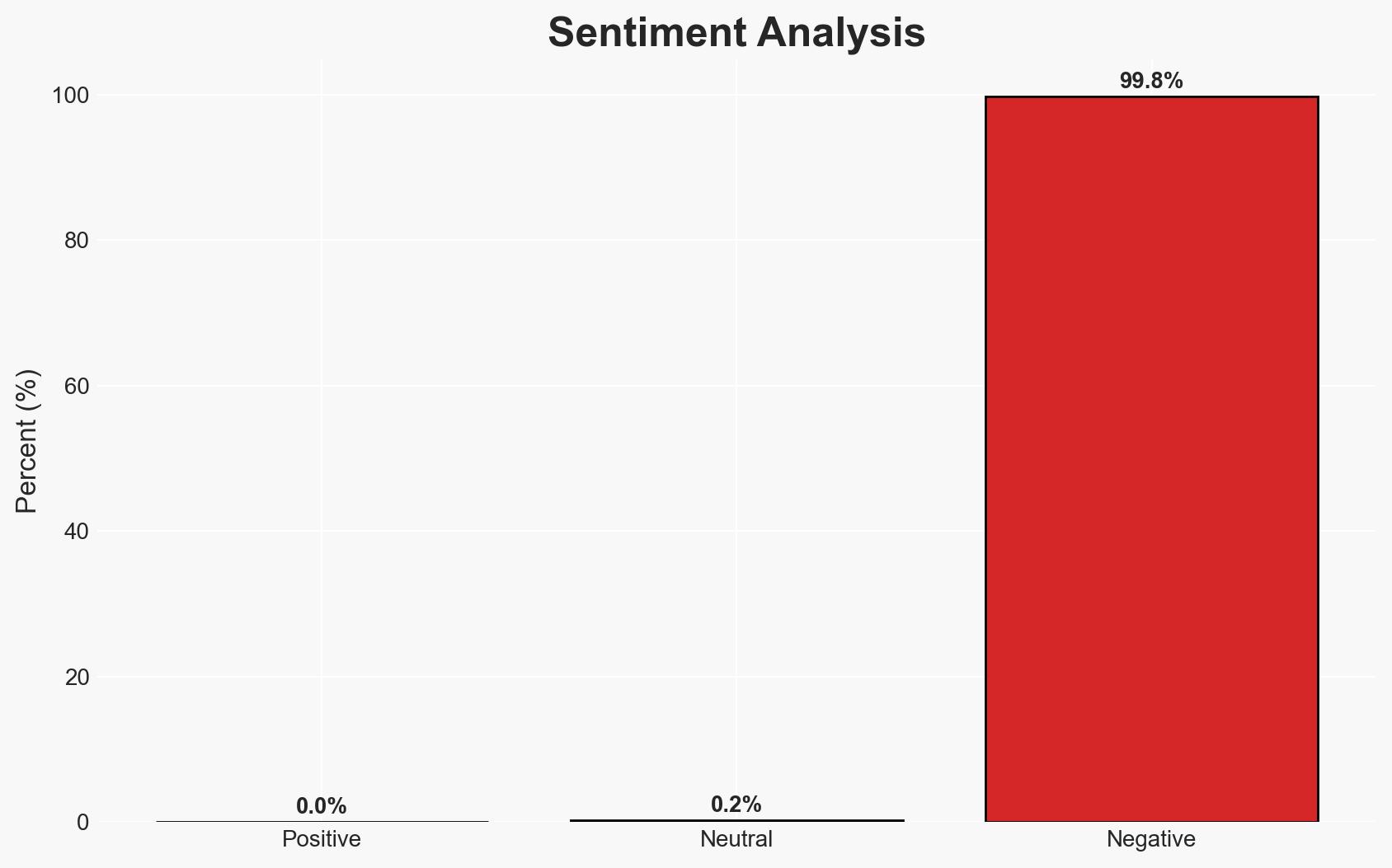
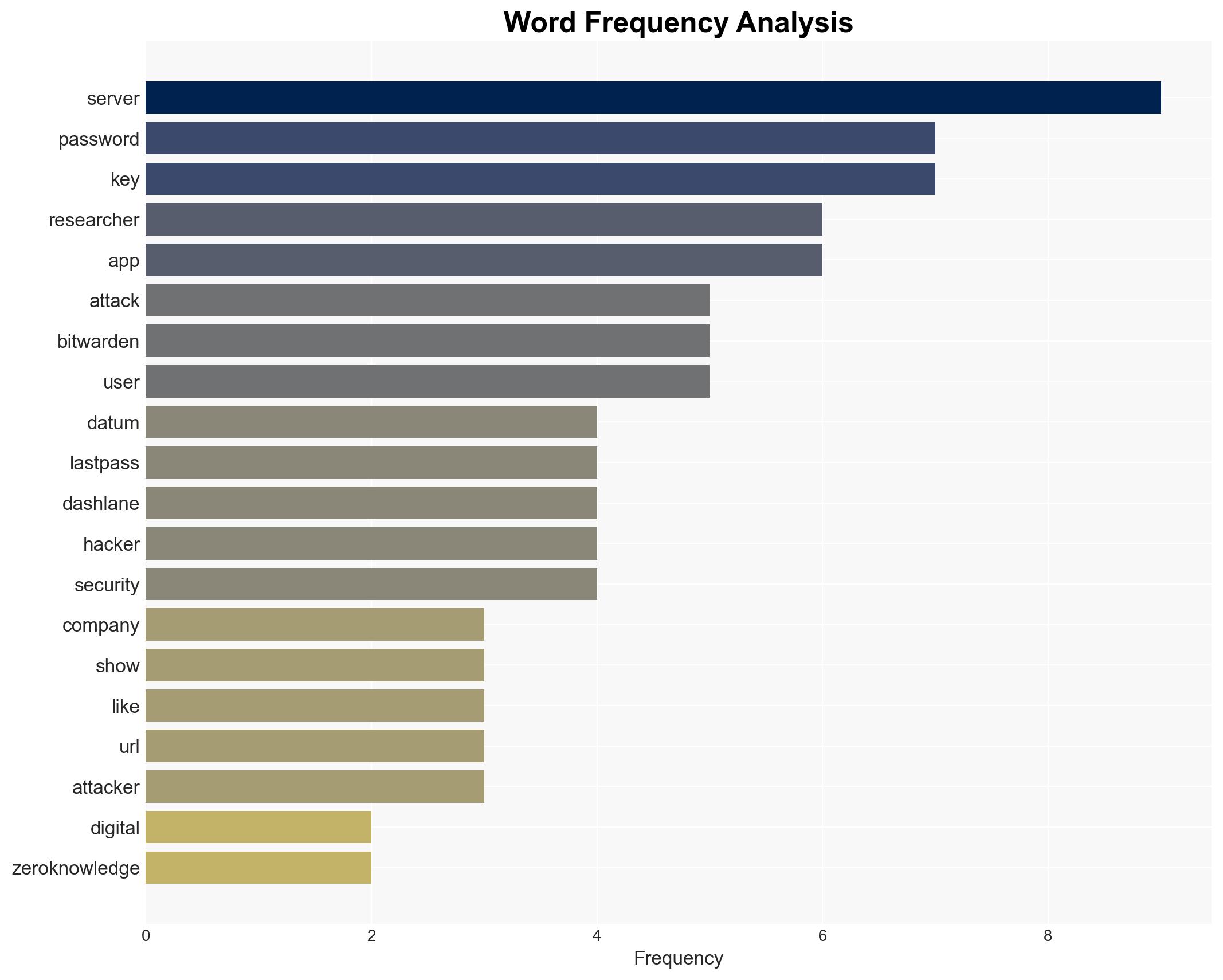
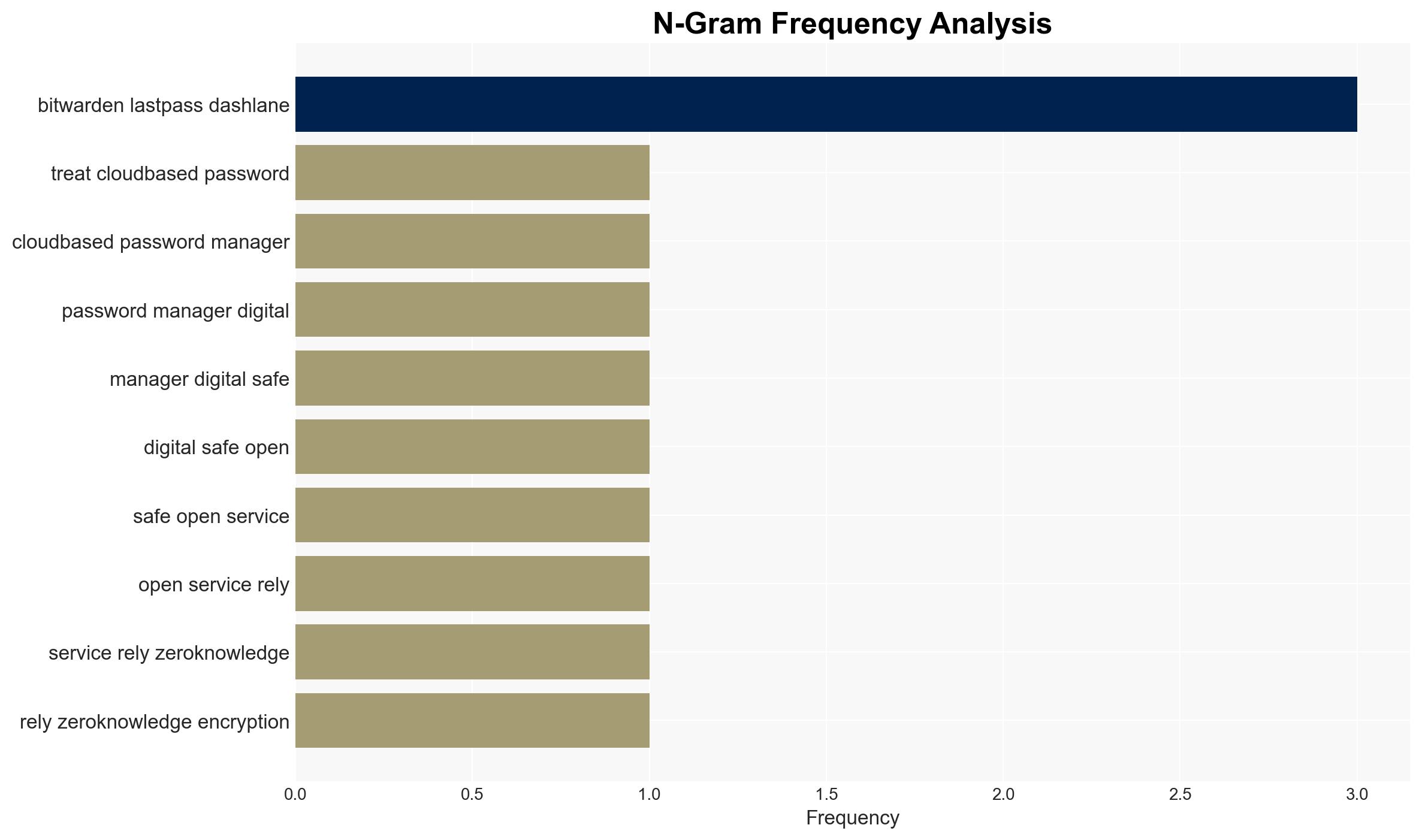
Recent research has revealed significant vulnerabilities in major password managers, undermining their security claims, particularly regarding Zero-Knowledge Encryption. The findings suggest that sophisticated attackers can exploit these weaknesses to access user data. The affected entities include Bitwarden, LastPass, and Dashlane, with 1Password showing relative resilience. Overall confidence in the assessment is moderate due to potential information gaps and evolving vendor responses.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities in password managers are systemic and indicative of fundamental flaws in their security architecture. Supporting evidence includes the successful execution of 27 attacks across multiple platforms, highlighting weaknesses in cryptographic binding and server authentication. Key uncertainties involve the extent to which these vulnerabilities can be mitigated by patches.
- Hypothesis B: The vulnerabilities are isolated incidents that can be effectively addressed through targeted patches and updates. This hypothesis is supported by the fact that vendors have begun releasing fixes, and 1Password’s architecture appears to mitigate these specific attacks. Contradicting evidence includes the pervasive nature of the vulnerabilities across different platforms.
- Assessment: Hypothesis A is currently better supported due to the widespread nature of the vulnerabilities and the fundamental issues in security architecture. Indicators that could shift this judgment include successful and comprehensive patch implementations by vendors and independent verification of their efficacy.
3. Key Assumptions and Red Flags
- Assumptions: Password managers will continue to be a primary tool for digital security; vendors are motivated to address vulnerabilities; attackers have the capability to exploit these weaknesses.
- Information Gaps: Detailed technical specifications of the patches and their effectiveness; potential undisclosed vulnerabilities; attacker capabilities and intentions.
- Bias & Deception Risks: Potential bias in vendor-reported patch effectiveness; researchers’ focus on specific vulnerabilities may overlook others; possible deception by attackers to exploit unpatched systems.
4. Implications and Strategic Risks
The exposure of these vulnerabilities could lead to increased scrutiny and regulatory pressure on password manager vendors. Over time, this may drive improvements in security standards or lead to shifts in user trust and behavior.
- Political / Geopolitical: Potential for regulatory actions or international standards development to address cybersecurity in consumer applications.
- Security / Counter-Terrorism: Increased risk of cyber-attacks leveraging these vulnerabilities, potentially impacting critical infrastructure if password managers are used in sensitive environments.
- Cyber / Information Space: Heightened awareness and potential shifts in cybersecurity practices; increased demand for alternative security solutions.
- Economic / Social: Possible economic impacts on affected companies due to loss of consumer trust; broader implications for digital security culture and practices.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor vendor patch releases and independent assessments; advise users to update software and consider additional security measures.
- Medium-Term Posture (1–12 months): Encourage development of industry-wide security standards; foster partnerships for shared threat intelligence and rapid response capabilities.
- Scenario Outlook: Best: Vendors successfully patch vulnerabilities, restoring user trust. Worst: Continued exploitation leads to significant data breaches. Most-Likely: Incremental improvements in security with ongoing challenges in user trust and regulatory scrutiny.
6. Key Individuals and Entities
- Professor Kenneth Paterson (Research Lead)
- Bitwarden (Password Manager Vendor)
- LastPass (Password Manager Vendor)
- Dashlane (Password Manager Vendor)
- 1Password (Password Manager Vendor)
- ETH Zurich (Research Institution)
- Università della Svizzera italiana (Research Institution)
7. Thematic Tags
cybersecurity, password management, zero-knowledge encryption, vulnerability assessment, digital security, data protection, cyber threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us