CISA Alerts on Exploited RoundCube Vulnerabilities, Urges Federal Agencies to Implement Patches Promptly
Published on: 2026-02-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: CISA Recently patched RoundCube flaws now exploited in attacks
1. BLUF (Bottom Line Up Front)
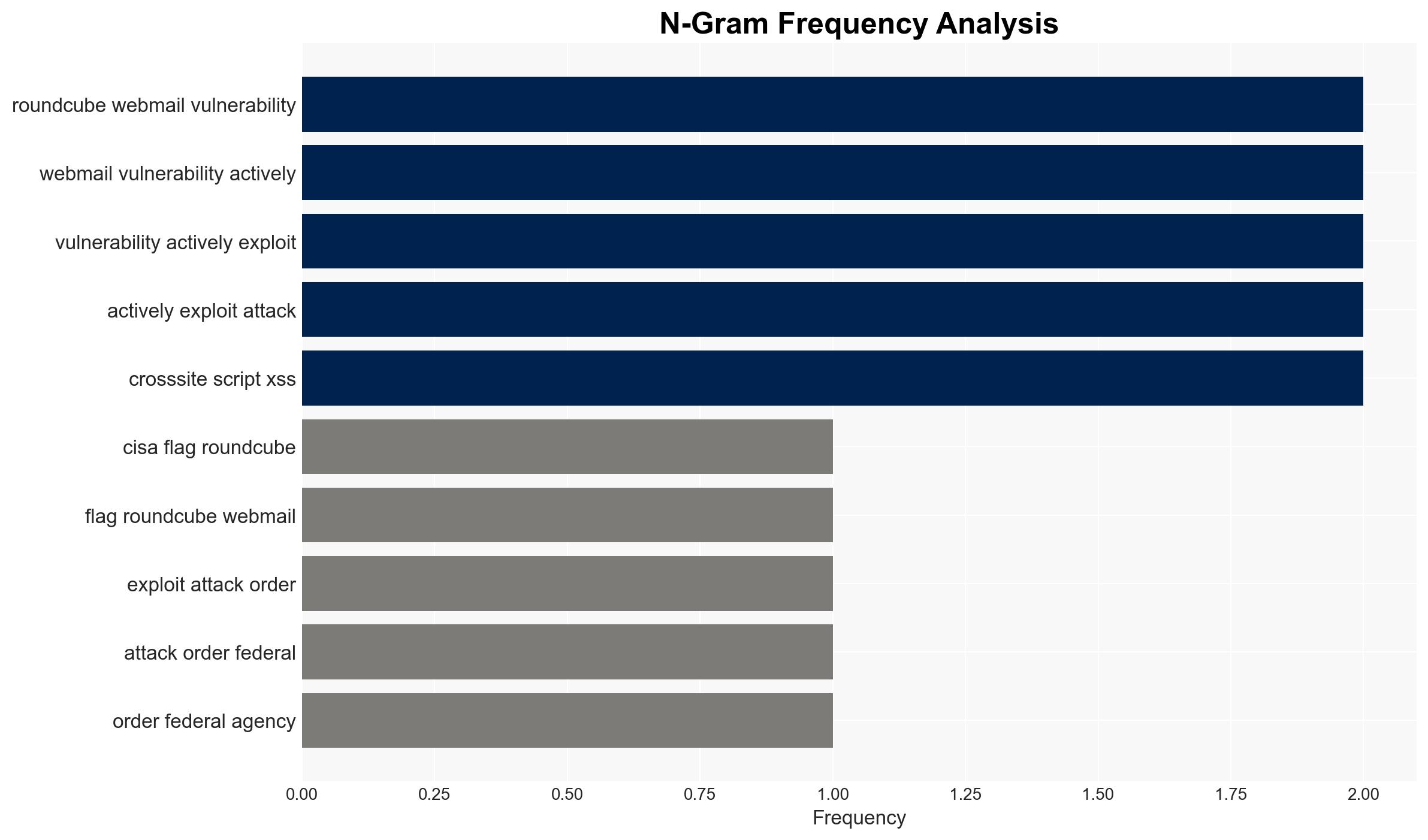
The exploitation of recently patched RoundCube vulnerabilities poses a significant threat to U.S. federal agencies and potentially other entities using the RoundCube Webmail. The vulnerabilities are being actively exploited, indicating a high risk of cyber intrusion. The most likely hypothesis is that state-sponsored actors are leveraging these vulnerabilities for espionage purposes. Overall confidence in this assessment is moderate due to limited information on the specific actors and methods of exploitation.
2. Competing Hypotheses
- Hypothesis A: State-sponsored actors are exploiting the RoundCube vulnerabilities to conduct espionage against U.S. federal agencies and allied entities. This is supported by past behavior of Russian groups targeting similar vulnerabilities and the strategic value of such information. However, specific attribution to a nation-state actor is currently lacking.
- Hypothesis B: Cybercriminal groups are exploiting these vulnerabilities primarily for financial gain, targeting entities with valuable data or resources. This hypothesis is less supported due to the lack of financial motivation typically associated with the exploitation of such vulnerabilities in government systems.
- Assessment: Hypothesis A is currently better supported due to the strategic nature of the targets and historical patterns of state-sponsored cyber activities. Indicators that could shift this judgment include evidence of financial transactions linked to the exploitation or identification of specific threat actor TTPs (Tactics, Techniques, and Procedures).
3. Key Assumptions and Red Flags
- Assumptions: The vulnerabilities are being exploited by actors with advanced capabilities; U.S. federal agencies are primary targets; the exploitation is part of a broader campaign.
- Information Gaps: Specific details on the nature and scope of the attacks; identification of the threat actors involved; the extent of the compromise across different sectors.
- Bias & Deception Risks: Potential bias in attributing attacks to state-sponsored actors without concrete evidence; risk of underestimating the involvement of non-state actors.
4. Implications and Strategic Risks
The exploitation of these vulnerabilities could lead to significant information breaches, affecting national security and diplomatic relations. Over time, this could escalate tensions between nation-states and increase the frequency of cyber operations targeting critical infrastructure.
- Political / Geopolitical: Increased tensions between the U.S. and adversarial states, potential for retaliatory cyber operations.
- Security / Counter-Terrorism: Enhanced threat environment for federal agencies, requiring increased cybersecurity measures.
- Cyber / Information Space: Potential for widespread information operations leveraging compromised data, increased cyber threat landscape.
- Economic / Social: Potential economic impact due to increased cybersecurity costs and loss of sensitive information affecting public trust.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Ensure all federal agencies comply with CISA’s directive to patch vulnerabilities; enhance monitoring for signs of exploitation; conduct threat intelligence sharing with allies.
- Medium-Term Posture (1–12 months): Develop resilience measures including regular security audits; strengthen partnerships with private sector cybersecurity firms; invest in capability development for rapid response.
- Scenario Outlook:
- Best: Rapid patching and mitigation efforts prevent significant breaches.
- Worst: Widespread exploitation leads to major data breaches and geopolitical tensions.
- Most-Likely: Continued exploitation by state-sponsored actors with limited immediate impact but potential long-term strategic consequences.
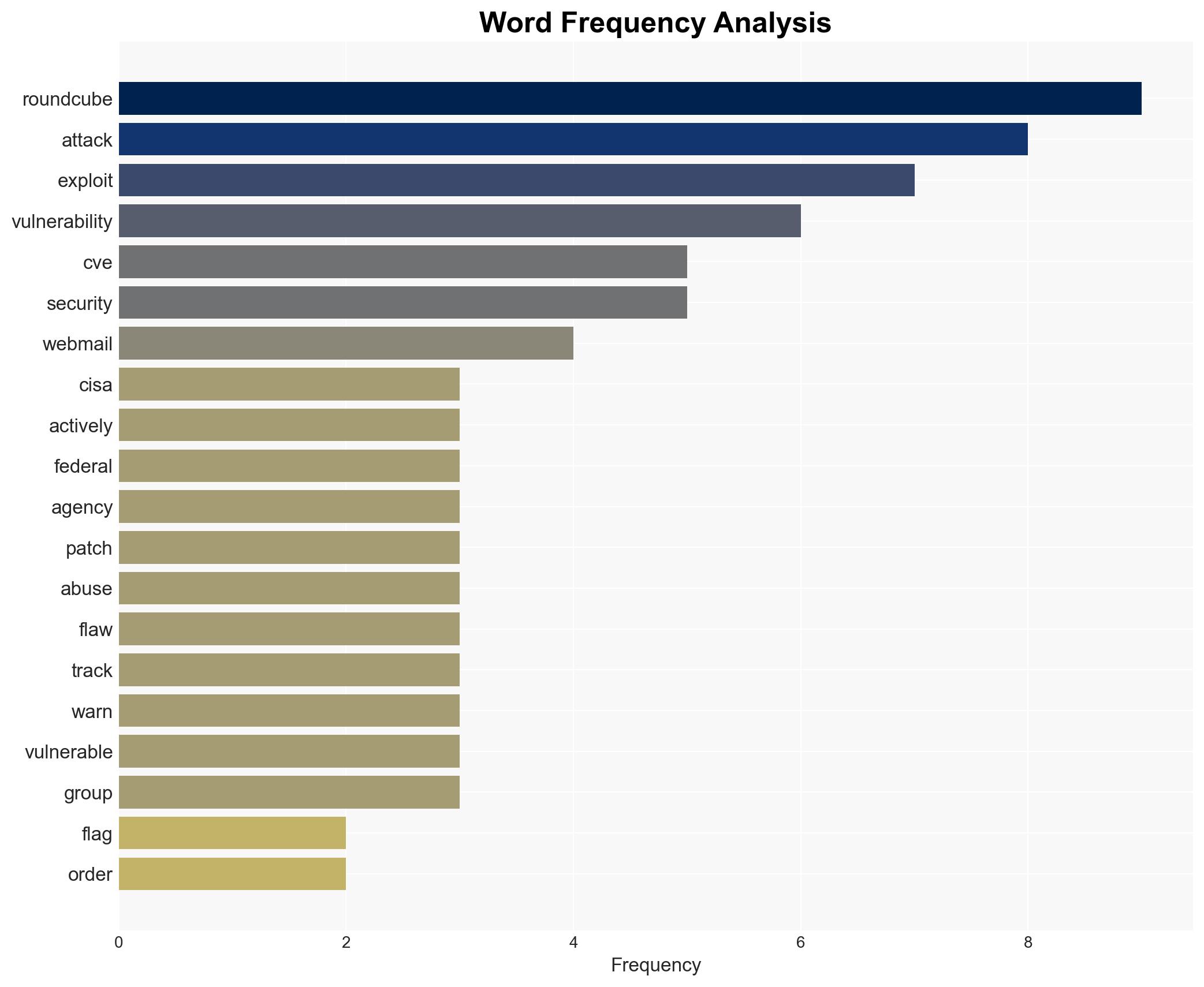
6. Key Individuals and Entities
- Roundcube Security Team
- CISA (Cybersecurity and Infrastructure Security Agency)
- Shadowserver Foundation
- Federal Civilian Executive Branch (FCEB) Agencies
- Russian APT28 Cyber-Espionage Group
- Winter Vivern (TA473) Russian Hacking Group
7. Thematic Tags
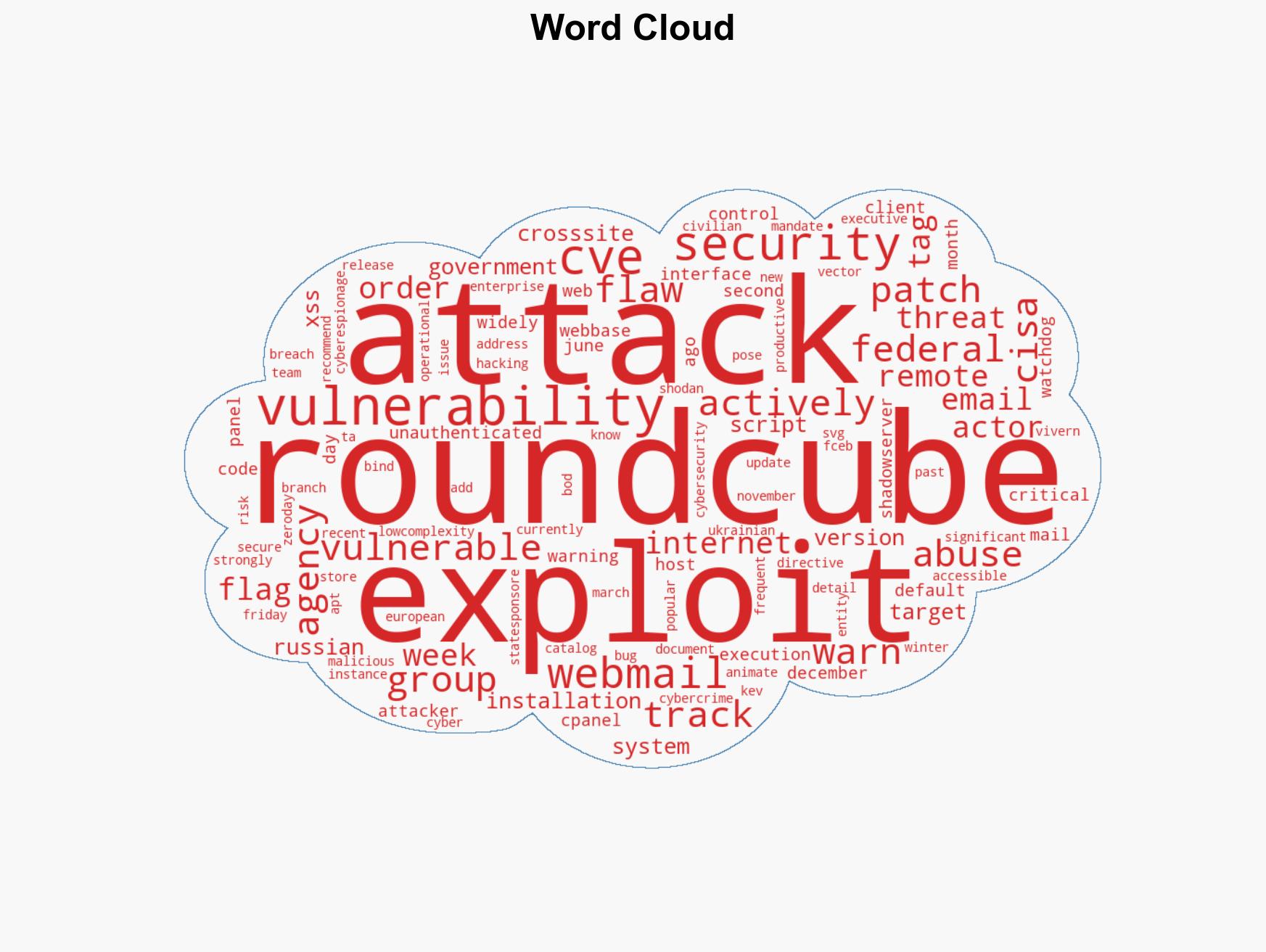
cybersecurity, state-sponsored actors, vulnerabilities, espionage, federal agencies, cyber operations, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us