Schneider Electric EcoStruxure Building Operation Workstation
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Schneider Electric EcoStruxure Building Operation Workstation
1. BLUF (Bottom Line Up Front)
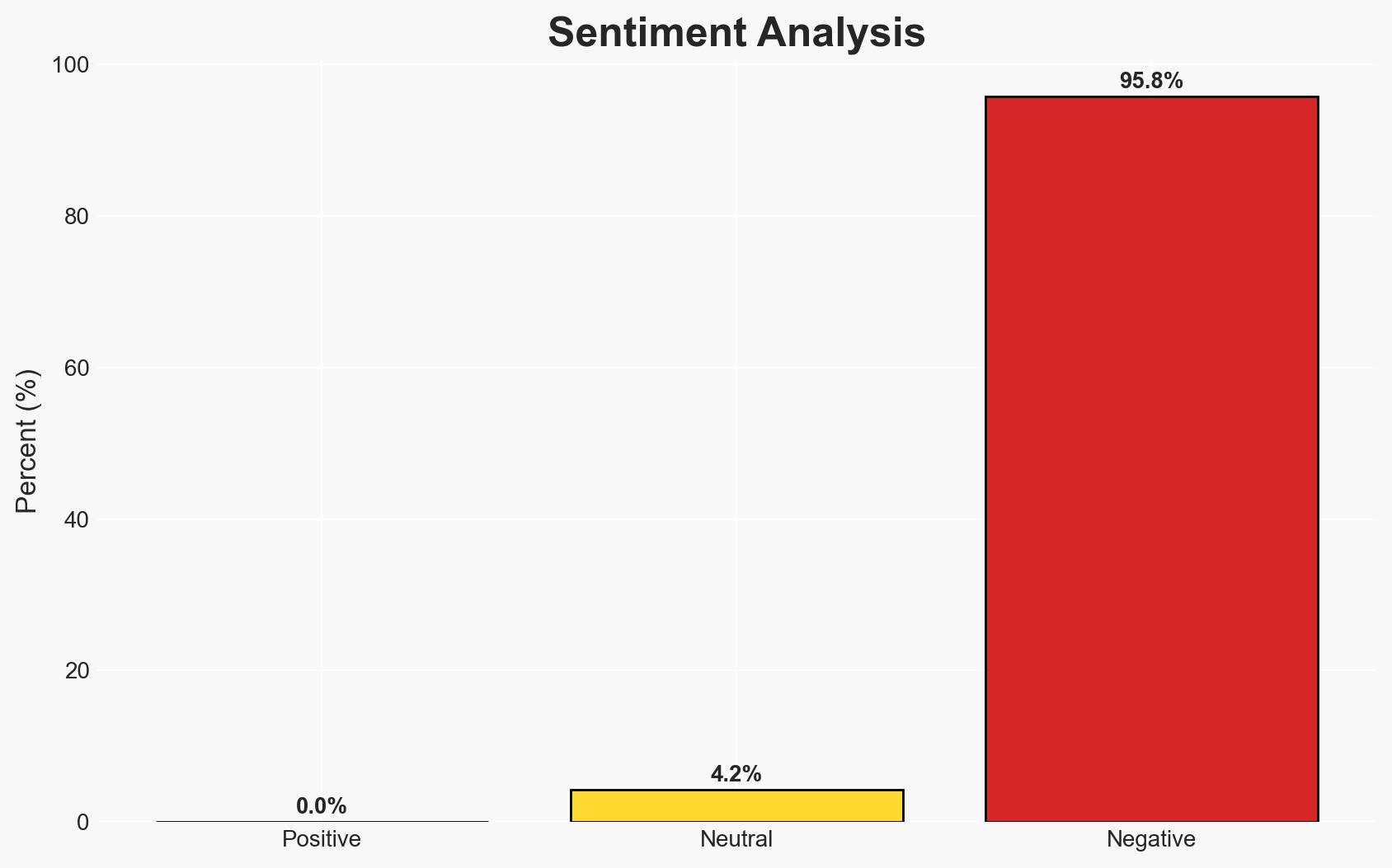
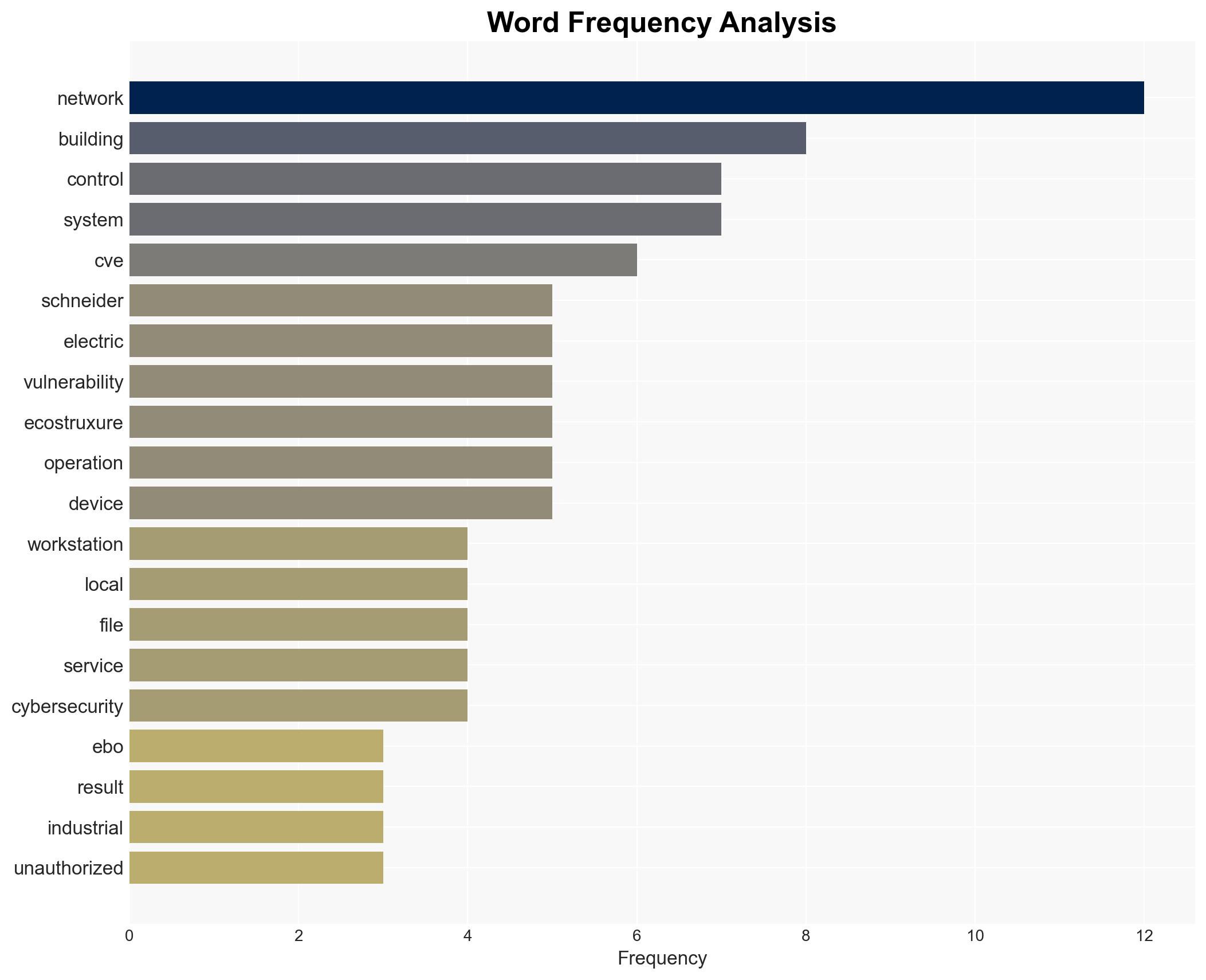
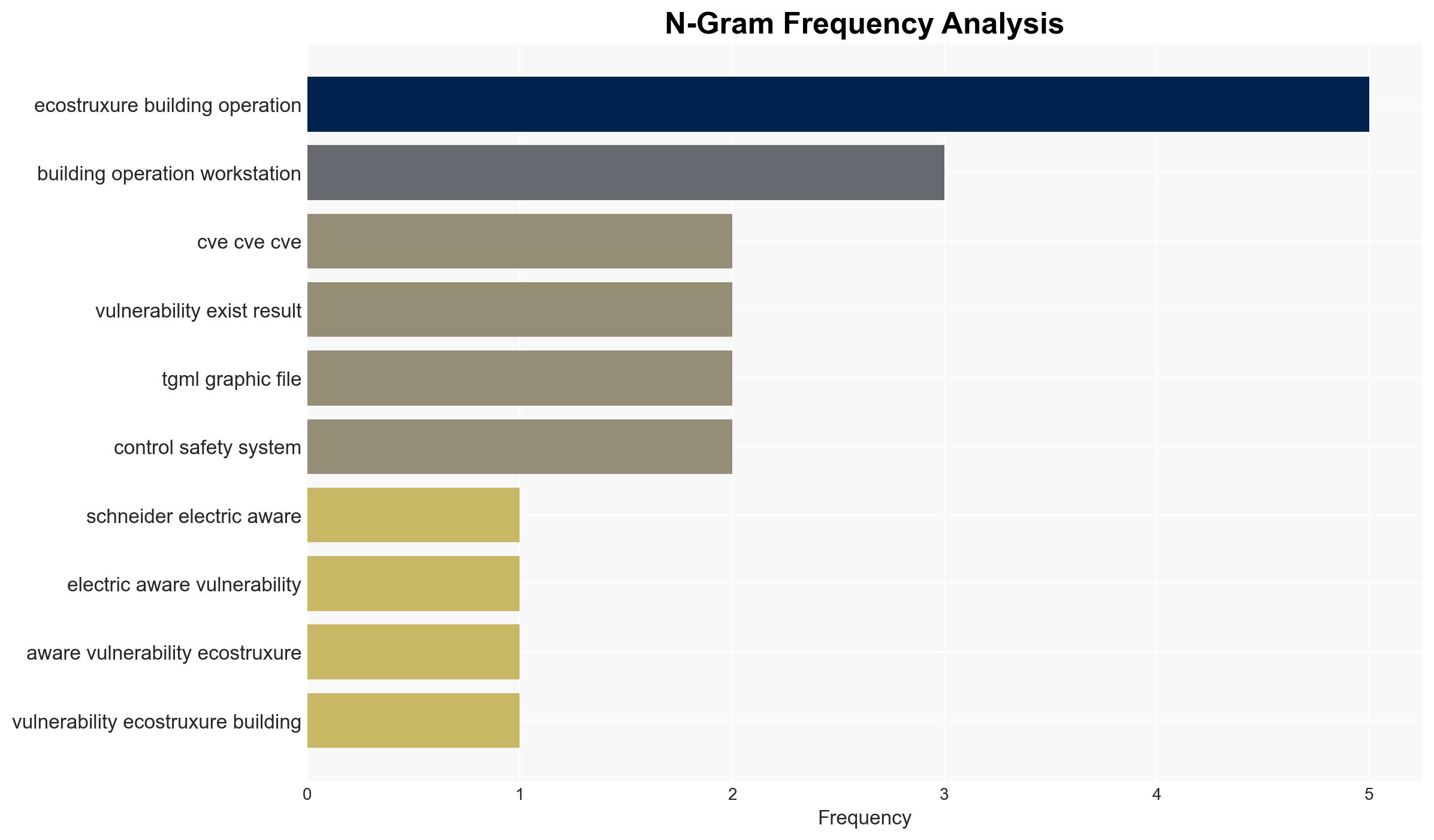
Schneider Electric’s EcoStruxure Building Operation Workstation and WebStation have identified vulnerabilities that could lead to unauthorized file access and denial of service. These vulnerabilities pose significant risks to critical infrastructure sectors globally. The most likely hypothesis is that these vulnerabilities could be exploited by cyber actors to disrupt operations, with moderate confidence in this assessment.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities in Schneider Electric’s systems are likely to be exploited by cybercriminals or state-sponsored actors to gain unauthorized access to sensitive data and disrupt operations. This is supported by the widespread deployment of these systems in critical infrastructure sectors and the nature of the vulnerabilities.
- Hypothesis B: The vulnerabilities will not be significantly exploited due to rapid patching and mitigation efforts by Schneider Electric and affected organizations. This hypothesis is less supported due to the potential delay in patch deployment across diverse global installations.
- Assessment: Hypothesis A is currently better supported given the critical nature of the sectors involved and the potential for significant disruption. Key indicators that could shift this judgment include the speed and effectiveness of patch deployment and any emerging reports of exploitation.
3. Key Assumptions and Red Flags
- Assumptions: Schneider Electric will provide timely patches; affected organizations will prioritize patch implementation; adversaries are aware of these vulnerabilities.
- Information Gaps: Details on the extent of current exploitation, specific adversary interest in these vulnerabilities, and the speed of patch deployment across sectors.
- Bias & Deception Risks: Potential underreporting of exploitation incidents; reliance on vendor-provided information which may downplay risks.
4. Implications and Strategic Risks
The vulnerabilities in Schneider Electric’s systems could lead to increased cyber threats against critical infrastructure, potentially impacting national security and economic stability.
- Political / Geopolitical: Potential for increased tensions if state-sponsored actors are implicated in exploiting these vulnerabilities.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks on critical infrastructure, necessitating increased security measures.
- Cyber / Information Space: Potential for widespread cyber incidents affecting multiple sectors, leading to increased scrutiny on cybersecurity practices.
- Economic / Social: Disruptions in critical services could lead to economic losses and public unrest if not promptly addressed.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply available patches, enhance monitoring for signs of exploitation, and review access controls.
- Medium-Term Posture (1–12 months): Develop resilience measures, conduct regular security audits, and strengthen partnerships for information sharing.
- Scenario Outlook:
- Best: Rapid patching mitigates risks with no significant exploitation.
- Worst: Widespread exploitation leads to major disruptions in critical sectors.
- Most-Likely: Some exploitation occurs, but effective mitigation limits impact.
6. Key Individuals and Entities
- Schneider Electric
- Critical Infrastructure Operators
- Cybersecurity Agencies
- Potential Adversaries (Cybercriminals, State-Sponsored Actors)
7. Thematic Tags
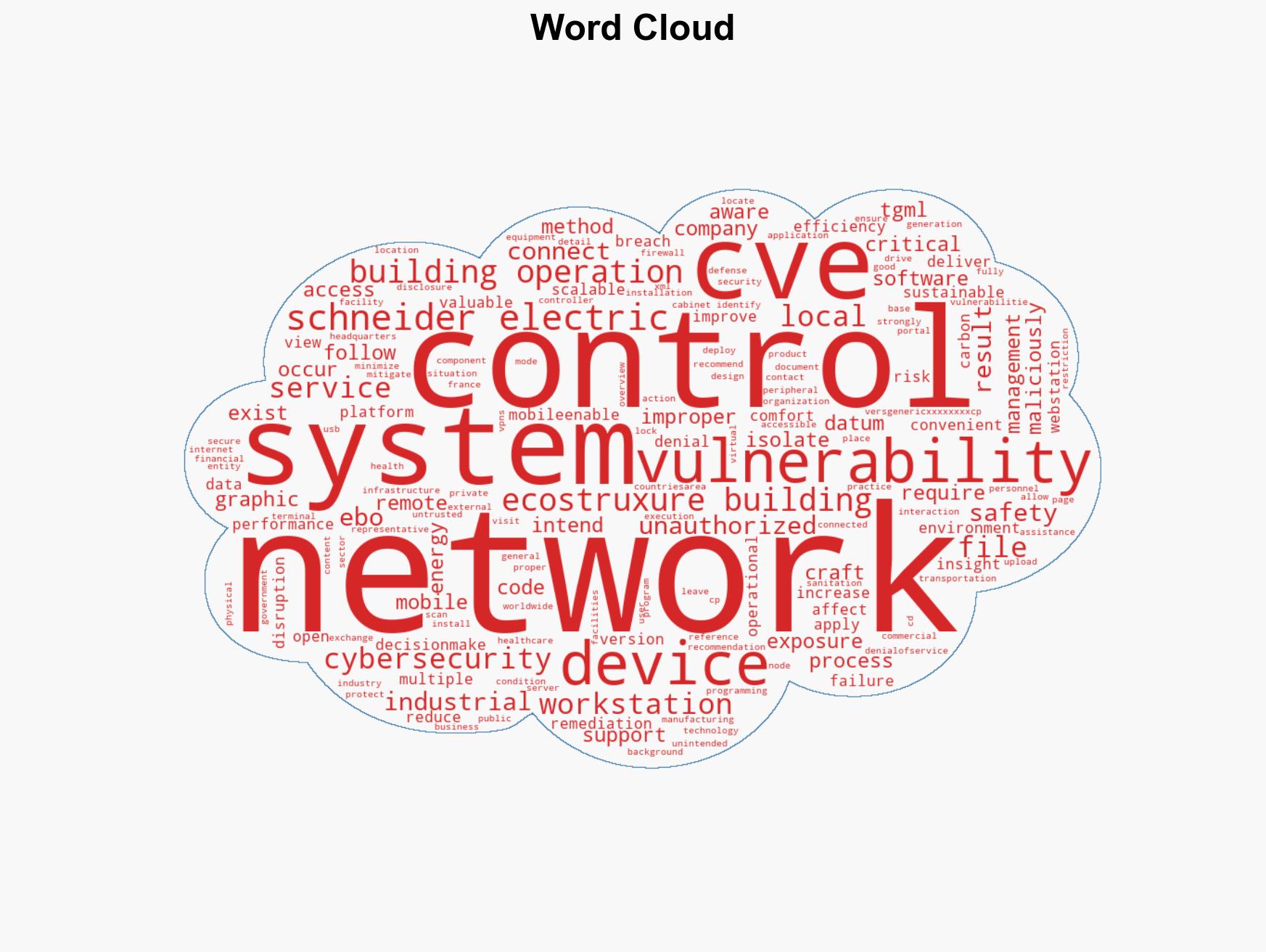
cybersecurity, critical infrastructure, vulnerability management, cyber threats, Schneider Electric, operational disruption, data breaches
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us