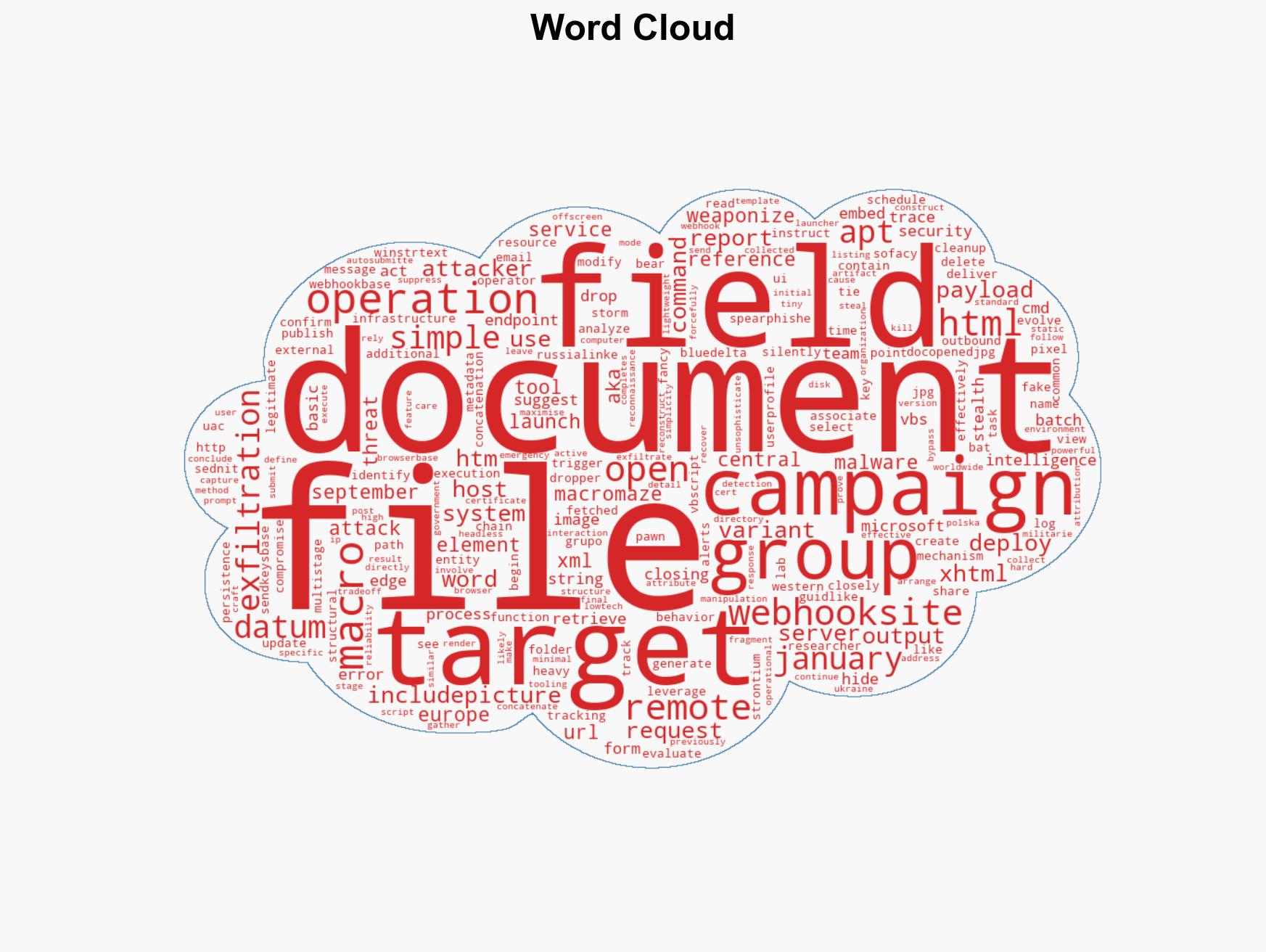
APT28’s Operation MacroMaze utilizes webhooks for stealthy data extraction in targeted cyber campaign
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Operation MacroMaze APT28 exploits webhooks for covert data exfiltration
1. BLUF (Bottom Line Up Front)
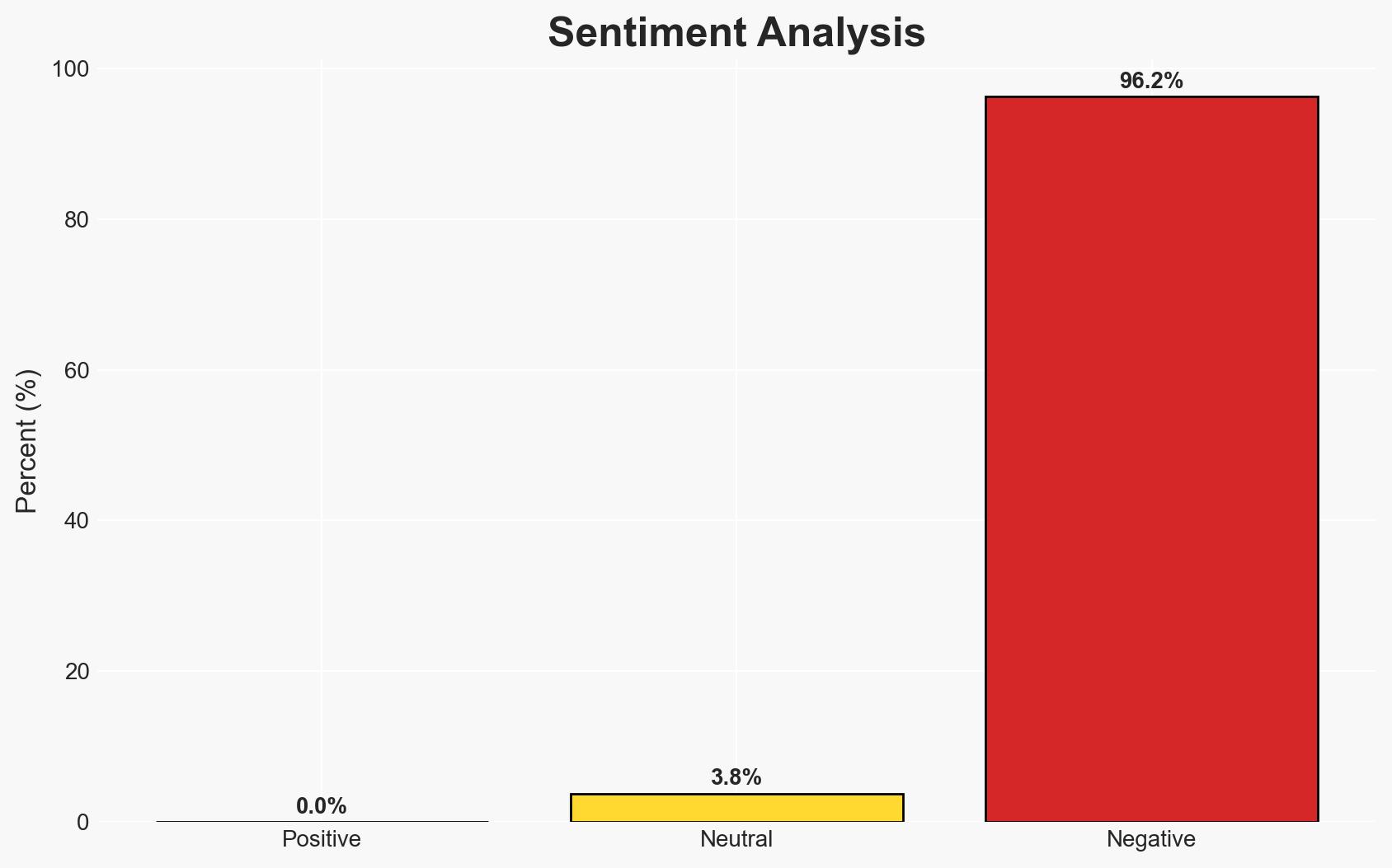
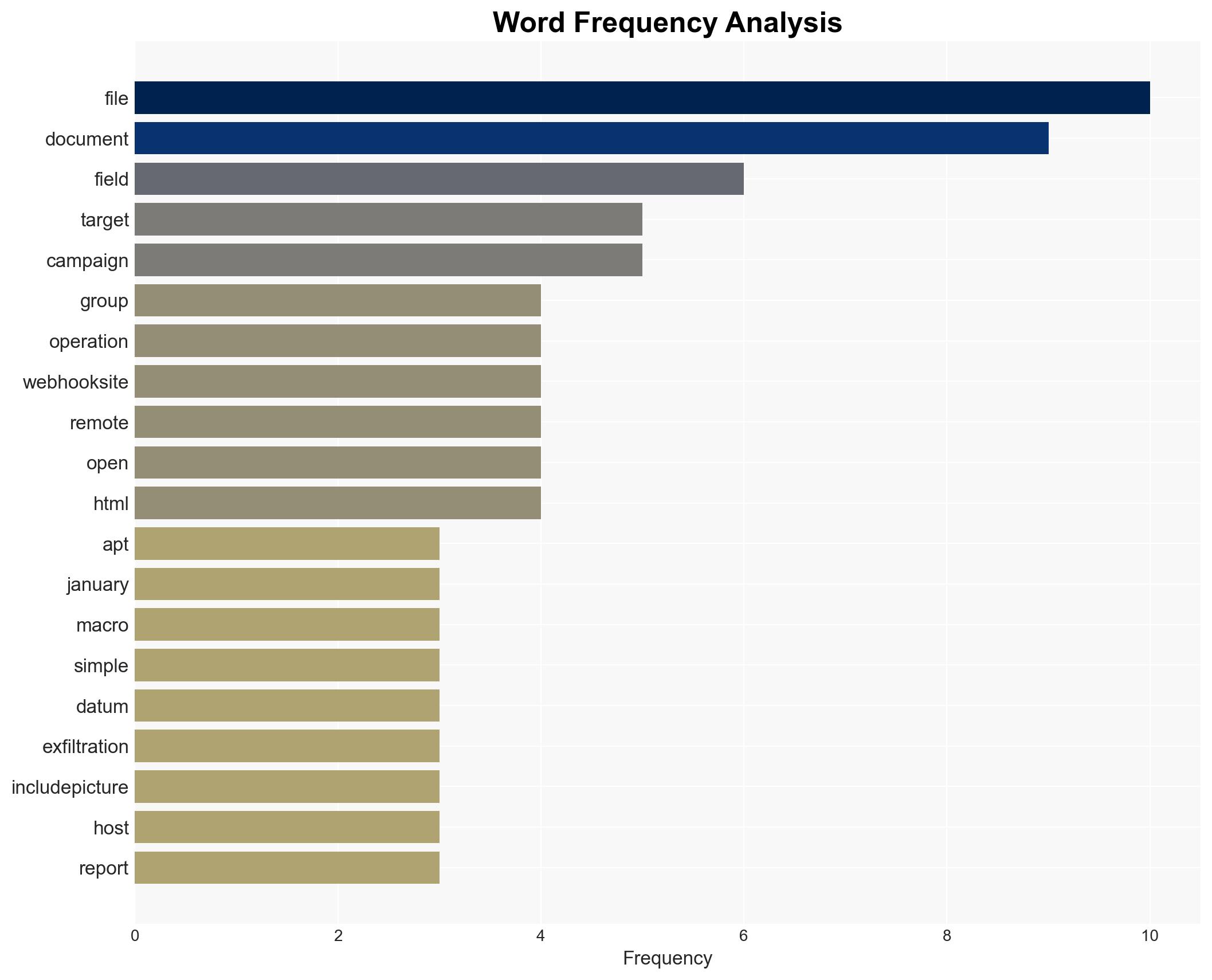
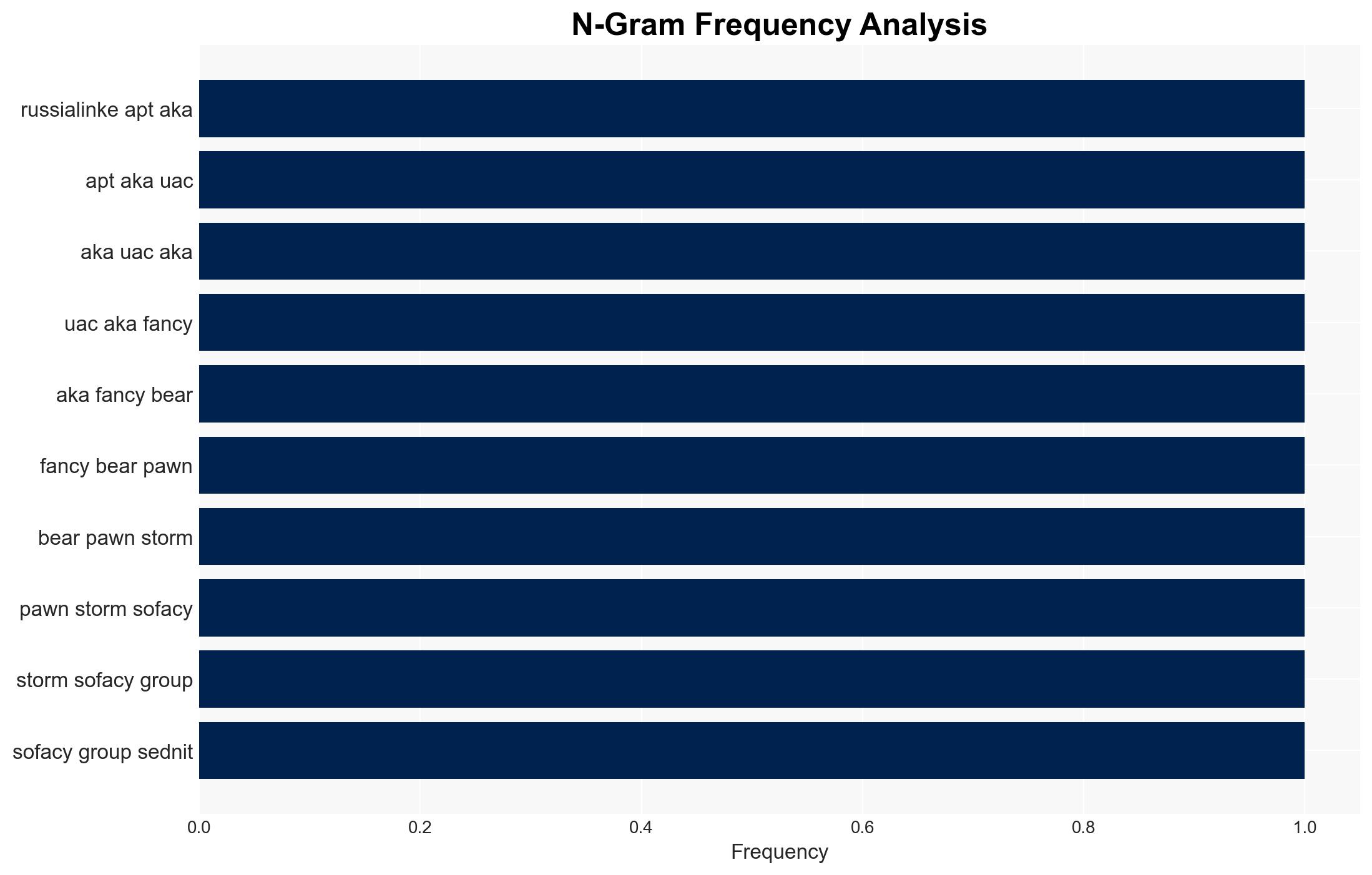
Operation MacroMaze, attributed to Russia-linked APT28, exploits webhook-based macro malware for data exfiltration targeting Western and Central Europe. The campaign leverages legitimate services and simple tools, indicating a strategic shift towards stealth and persistence. This assessment is made with moderate confidence due to the evolving nature of the tactics observed.
2. Competing Hypotheses
- Hypothesis A: APT28 is using Operation MacroMaze primarily for intelligence gathering on political and economic targets in Western and Central Europe. This is supported by the targeted nature of the spear-phishing emails and the use of sophisticated malware variants. However, the specific entities targeted remain unclear.
- Hypothesis B: The operation aims to disrupt or manipulate political processes in the region, using the gathered intelligence for strategic influence operations. While plausible, there is less direct evidence supporting this, as the primary focus appears to be on data exfiltration rather than immediate disruption.
- Assessment: Hypothesis A is currently better supported due to the technical focus on data exfiltration and the lack of immediate disruptive activities. Future indicators, such as shifts in target profiles or the emergence of related influence operations, could alter this assessment.
3. Key Assumptions and Red Flags
- Assumptions: APT28 remains aligned with Russian state interests; the campaign’s primary goal is intelligence collection; the use of webhooks is a deliberate choice for stealth.
- Information Gaps: Specific identities of targeted entities; full scope of data exfiltrated; potential secondary uses of the collected data.
- Bias & Deception Risks: Potential over-reliance on technical indicators without corroborating human intelligence; risk of misattribution due to shared tools and tactics among threat actors.
4. Implications and Strategic Risks
The development of Operation MacroMaze suggests a refinement in APT28’s operational tactics, with potential long-term impacts on regional security dynamics and cyber defense postures.
- Political / Geopolitical: Potential escalation in cyber tensions between Russia and affected European nations, possibly influencing diplomatic relations.
- Security / Counter-Terrorism: Increased threat to critical infrastructure and governmental entities, necessitating enhanced cybersecurity measures.
- Cyber / Information Space: Demonstrates evolving cyber capabilities and methodologies, potentially inspiring similar tactics by other state or non-state actors.
- Economic / Social: Potential economic impacts if sensitive commercial data is compromised, leading to market instability or loss of competitive advantage.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of spear-phishing activities; deploy advanced threat detection tools; conduct awareness training for potential targets.
- Medium-Term Posture (1–12 months): Strengthen international cyber cooperation; invest in cyber resilience and response capabilities; develop public-private partnerships for information sharing.
- Scenario Outlook: Best: Effective mitigation reduces impact; Worst: Data used for strategic manipulation; Most-Likely: Continued intelligence gathering with periodic adjustments in tactics.
6. Key Individuals and Entities
- APT28 (Fancy Bear, Pawn Storm, Sofacy Group, Sednit, BlueDelta, STRONTIUM)
- S2 Grupo’s LAB52 threat intelligence team
- Not clearly identifiable from open sources in this snippet for specific targeted entities.
7. Thematic Tags
cybersecurity, cyber-espionage, APT28, data exfiltration, spear-phishing, European security, Russia, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us