Lazarus Group employs Medusa ransomware in attacks on US and Middle Eastern healthcare organizations
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: North Korea’s Lazarus Group targets healthcare orgs with Medusa ransomware
1. BLUF (Bottom Line Up Front)
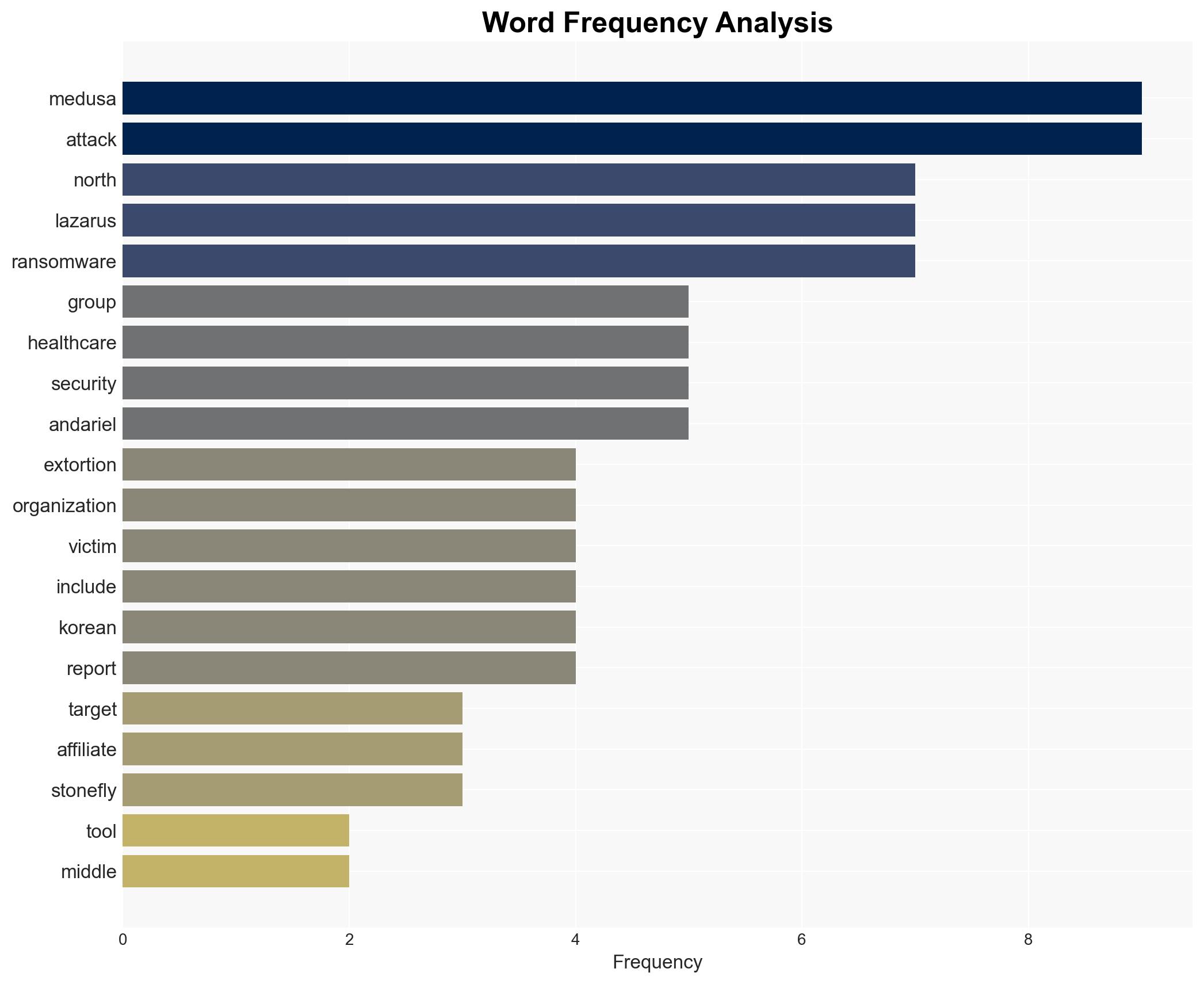
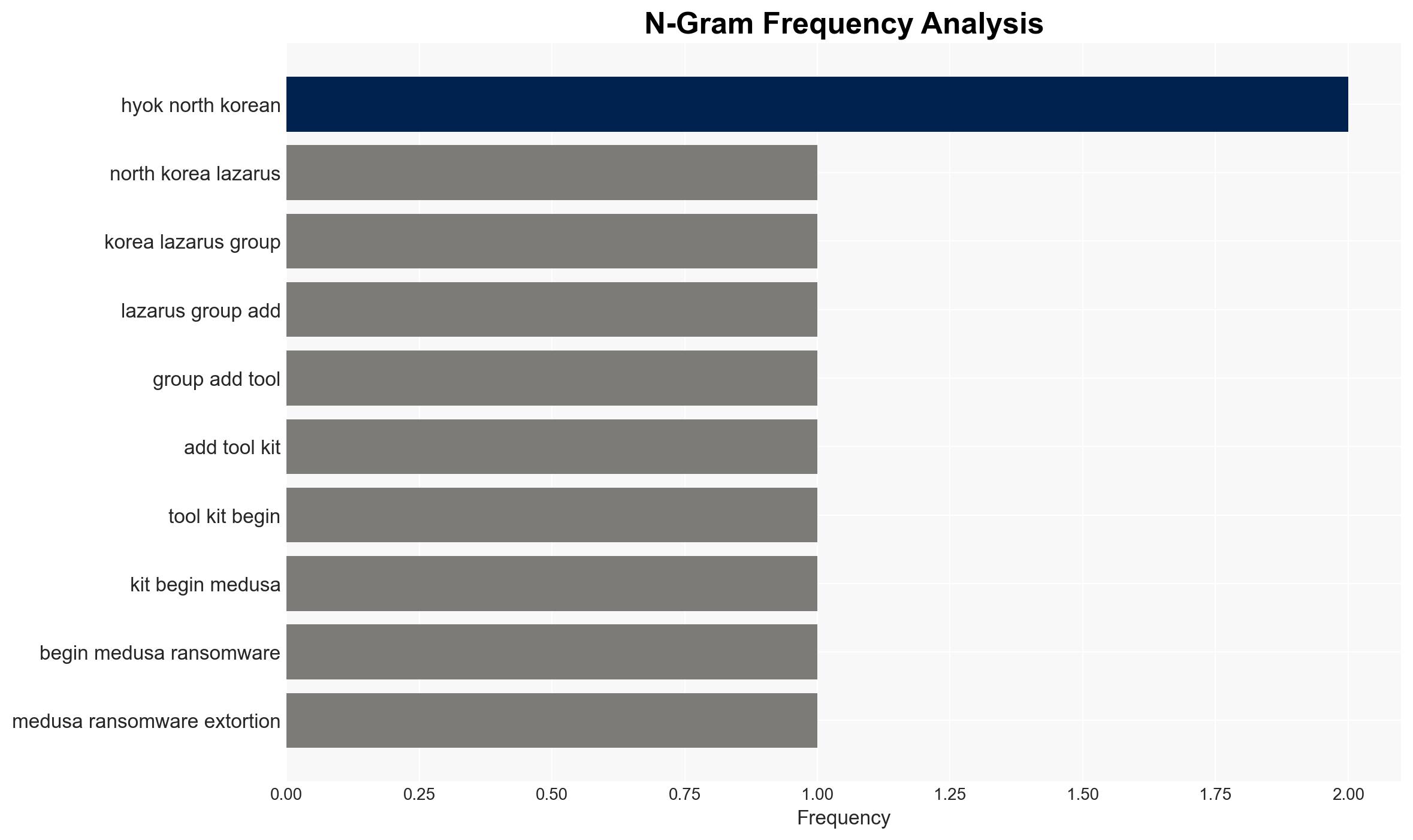
The Lazarus Group, a North Korean state-sponsored cyber entity, is reportedly using Medusa ransomware in extortion attacks targeting healthcare organizations. The group successfully compromised a Middle Eastern organization but failed against a US healthcare target. This activity suggests an expansion of Lazarus’ operational toolkit and targeting strategy, with moderate confidence in the attribution to Lazarus due to existing uncertainties about Medusa affiliate involvement.
2. Competing Hypotheses
- Hypothesis A: The Lazarus Group is directly responsible for the Medusa ransomware attacks on healthcare organizations. This is supported by the group’s history of using ransomware and the attribution by threat hunters. However, the involvement of Medusa affiliates introduces uncertainty.
- Hypothesis B: Medusa affiliates, independent of Lazarus, conducted the attacks, potentially with some coordination or overlap. The ransomware-as-a-service model supports this, but the specific targeting of healthcare aligns with Lazarus’ known objectives.
- Assessment: Hypothesis A is currently better supported due to Lazarus’ established pattern of cyber operations and the specific targeting of sectors aligned with North Korean interests. Confirmation of direct Lazarus involvement or further evidence of affiliate actions could shift this assessment.
3. Key Assumptions and Red Flags
- Assumptions: Lazarus Group retains operational control over its cyber activities; Medusa ransomware is being used strategically rather than opportunistically; North Korean cyber operations are state-directed.
- Information Gaps: Definitive attribution of the attacks to Lazarus versus Medusa affiliates; comprehensive understanding of Medusa’s affiliate network; specific motivations behind targeting healthcare.
- Bias & Deception Risks: Potential bias in attributing attacks to Lazarus due to their notoriety; risk of deception by Medusa affiliates or Lazarus to obscure true operational control.
4. Implications and Strategic Risks
The use of Medusa ransomware by Lazarus could indicate a shift towards more diversified and potentially more aggressive cyber tactics. This development might lead to increased tensions and further sanctions against North Korea.
- Political / Geopolitical: Potential for increased diplomatic friction between North Korea and affected nations, particularly the US and Middle Eastern countries.
- Security / Counter-Terrorism: Heightened threat environment for critical infrastructure sectors, necessitating improved defensive measures.
- Cyber / Information Space: Possible escalation in ransomware sophistication and deployment, impacting global cybersecurity norms.
- Economic / Social: Disruption to healthcare services could lead to public health risks and economic strain on affected organizations.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of ransomware activity in critical sectors; engage in information sharing with international partners; increase defensive posture for healthcare organizations.
- Medium-Term Posture (1–12 months): Develop resilience measures and incident response capabilities; strengthen partnerships with cybersecurity firms; explore diplomatic channels to address state-sponsored cyber threats.
- Scenario Outlook:
- Best: Improved international cooperation leads to disruption of ransomware networks.
- Worst: Escalation of ransomware attacks causes widespread disruption across critical sectors.
- Most-Likely: Continued sporadic ransomware incidents with gradual improvements in defensive measures.
6. Key Individuals and Entities
- Lazarus Group
- Andariel subgroup
- Spearwing cybercrime group
- Song Kum Hyok
- Rim Jong Hyok
- Not clearly identifiable from open sources in this snippet
7. Thematic Tags
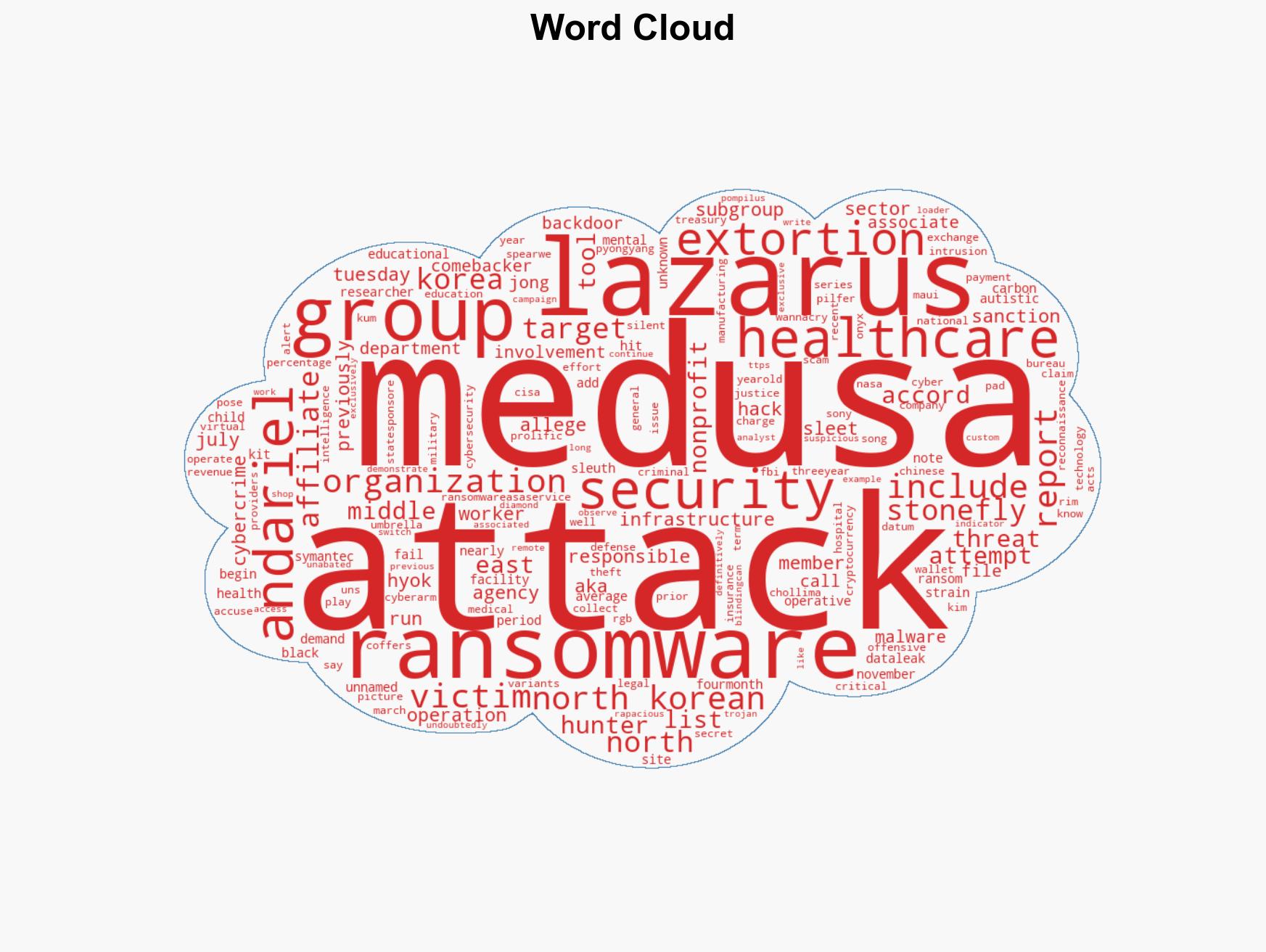
cybersecurity, ransomware, North Korea, Lazarus Group, healthcare sector, Medusa ransomware, state-sponsored cyber operations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us