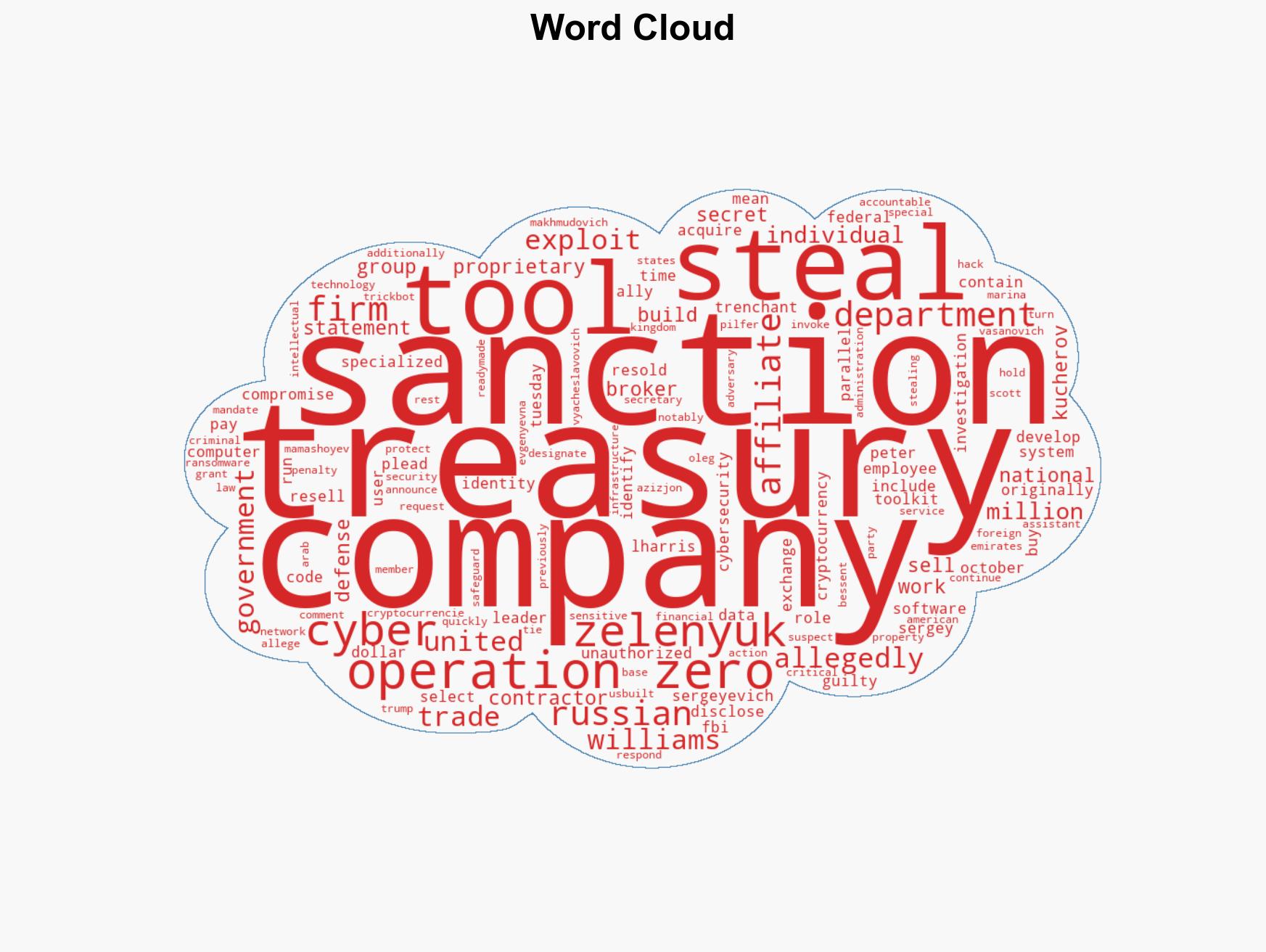
U.S. Treasury Targets Russian Operation Zero for Allegedly Reselling Stolen Cyber Tools
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Treasury sanctions Russian firm said to have stolen and sold US cyber tools
1. BLUF (Bottom Line Up Front)
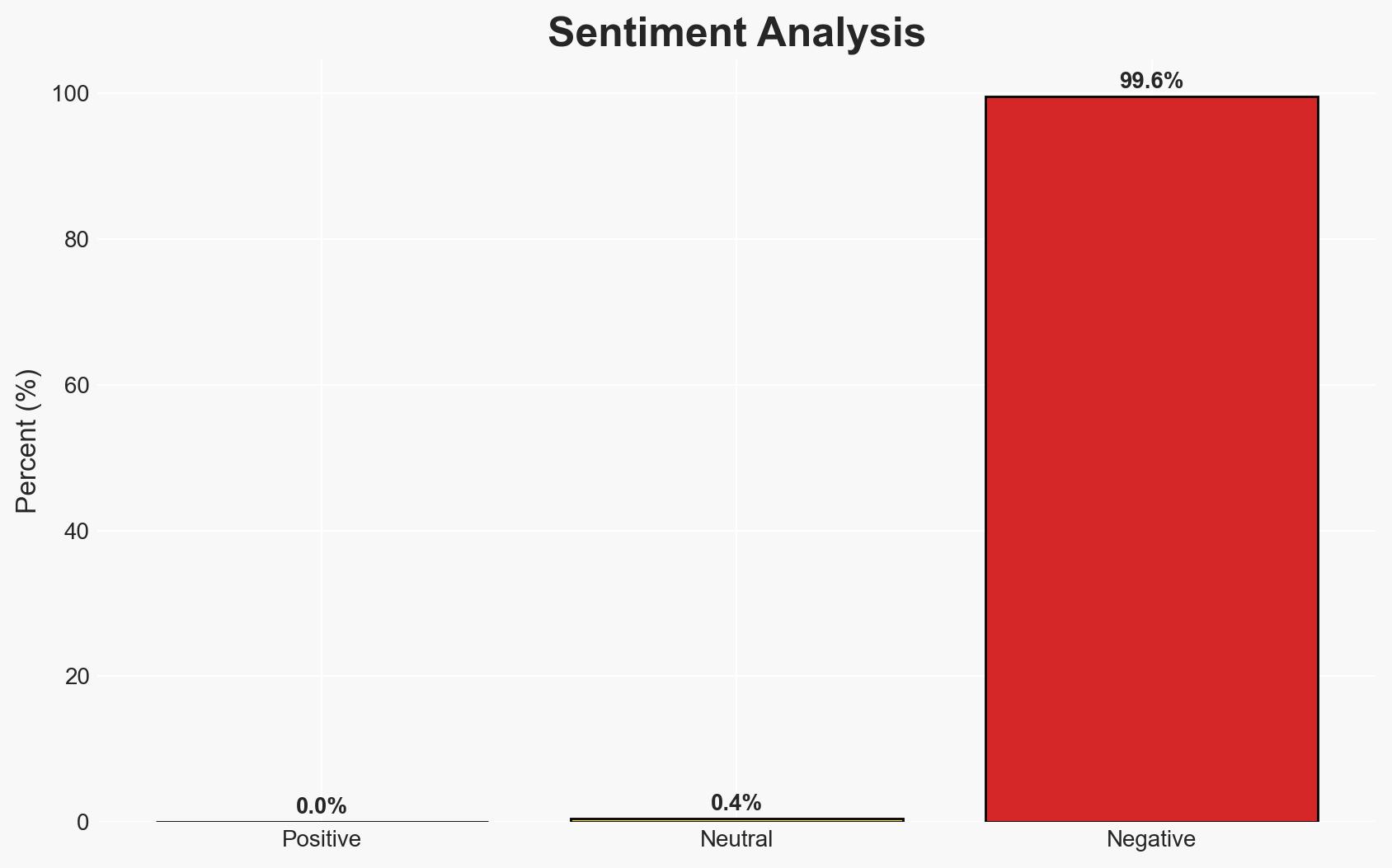
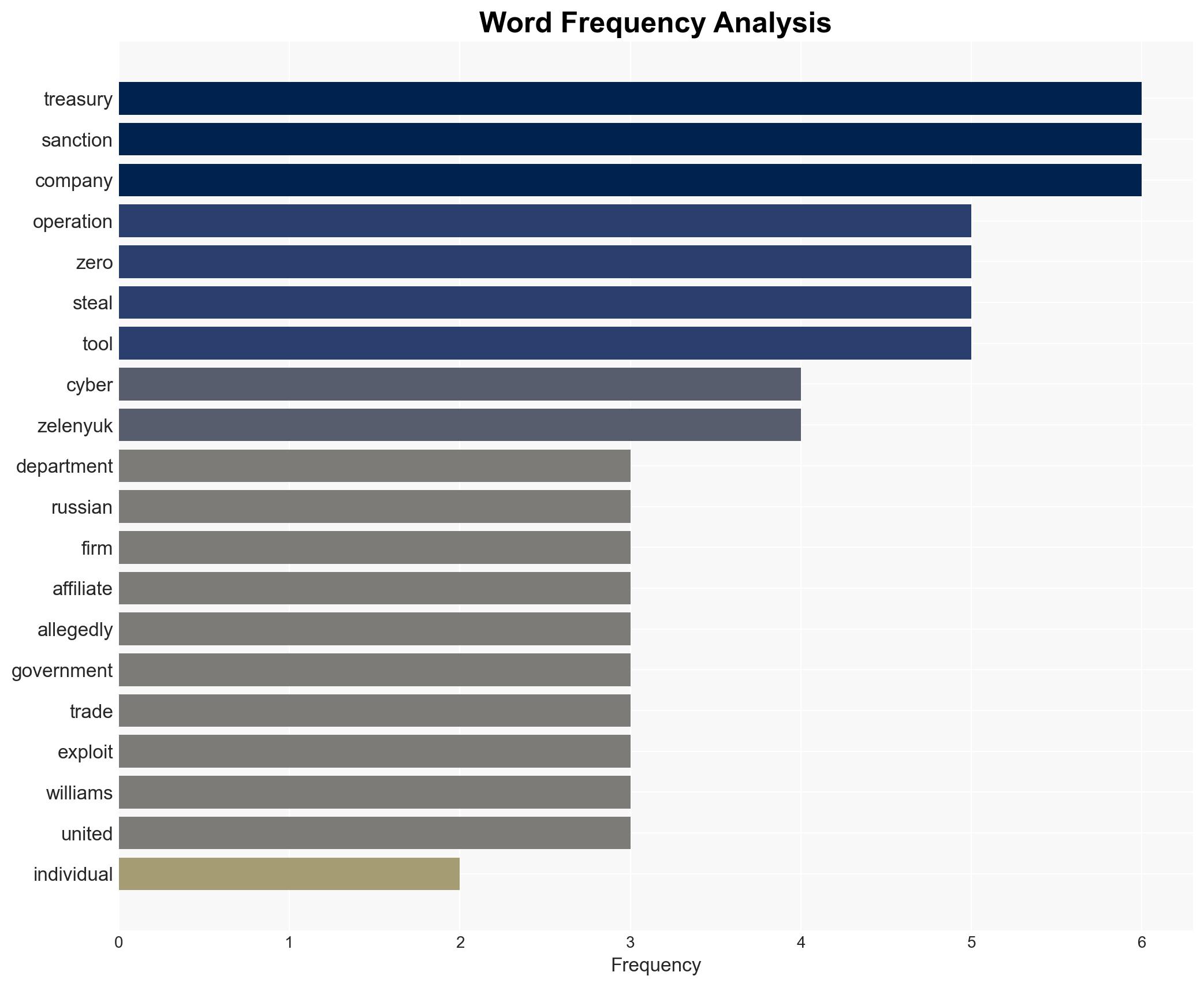
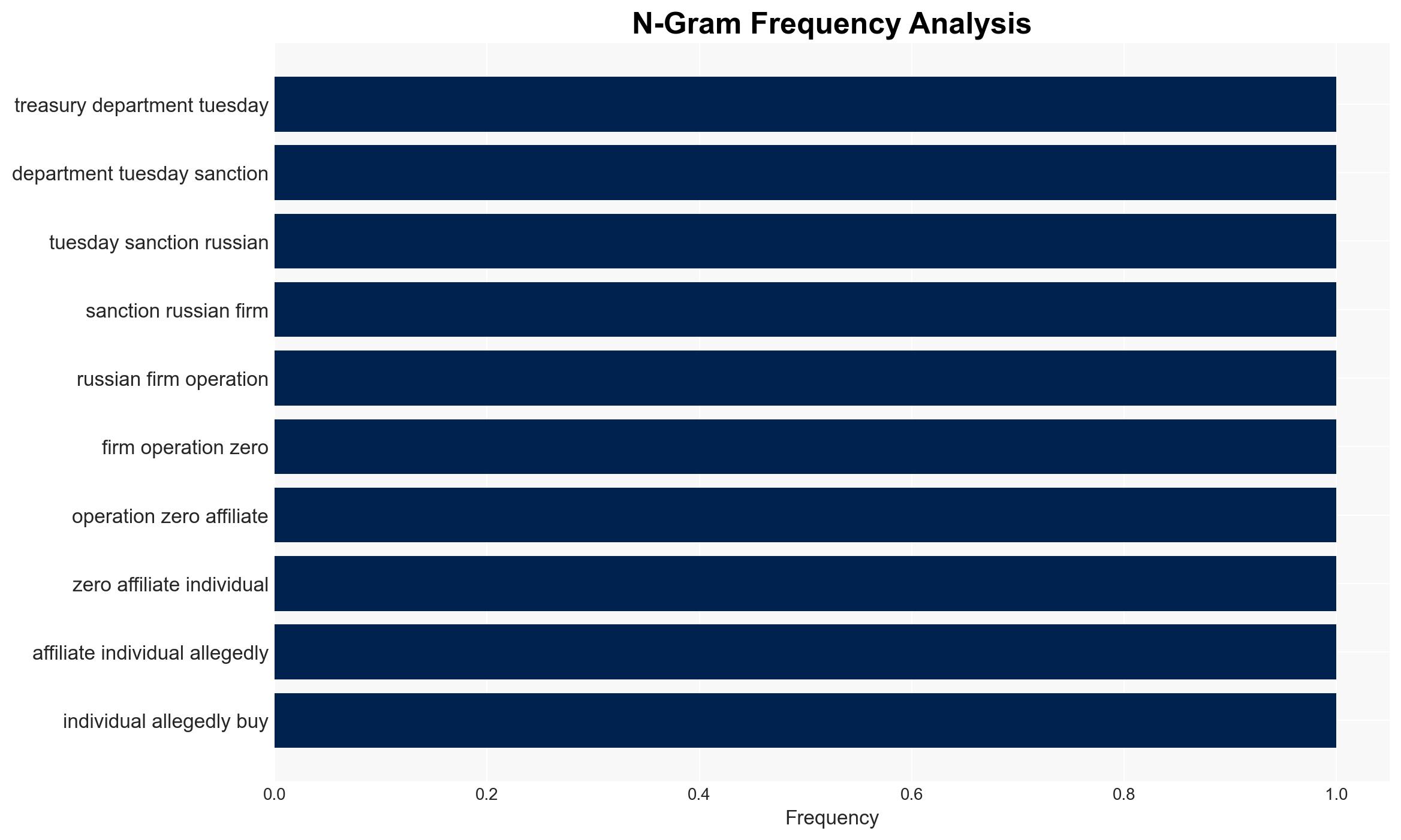
The U.S. Treasury Department has sanctioned the Russian firm Operation Zero and associated individuals for allegedly acquiring and reselling stolen U.S. cyber tools. This action highlights the ongoing threat of cyber espionage and the illicit trade in cyber exploits. The sanctions are part of a broader U.S. strategy to protect national security and intellectual property. Overall confidence in this assessment is moderate, given the complexity of cyber operations and potential for misinformation.
2. Competing Hypotheses
- Hypothesis A: Operation Zero intentionally acquired and resold U.S. cyber tools to unauthorized users, posing a direct threat to U.S. national security. Supporting evidence includes the Treasury’s sanctions and the FBI investigation linking the firm to stolen tools. Key uncertainties involve the full extent of Operation Zero’s network and the potential involvement of state actors.
- Hypothesis B: Operation Zero’s actions were opportunistic and not part of a coordinated effort to undermine U.S. security. This hypothesis is less supported due to the structured nature of the transactions and the involvement of known cybercriminals. However, the lack of direct evidence linking the firm to state-sponsored activities leaves room for doubt.
- Assessment: Hypothesis A is currently better supported due to the alignment of evidence from Treasury and FBI investigations. Key indicators that could shift this judgment include new intelligence on Operation Zero’s connections to state actors or additional evidence of their operational scope.
3. Key Assumptions and Red Flags
- Assumptions: The sanctions will disrupt Operation Zero’s operations; the stolen tools are primarily used for cyber espionage; U.S. sanctions will deter similar future activities.
- Information Gaps: Detailed information on the end-users of the stolen tools and the full scope of Operation Zero’s network is lacking.
- Bias & Deception Risks: Potential bias in source reporting due to geopolitical tensions; risk of misinformation from involved parties to obscure true intentions and capabilities.
4. Implications and Strategic Risks
This development underscores the persistent threat of cyber exploitation and the challenges in safeguarding sensitive technologies. It may lead to increased geopolitical tensions and influence future cyber policy and defense strategies.
- Political / Geopolitical: Potential escalation in U.S.-Russia tensions and impact on diplomatic relations.
- Security / Counter-Terrorism: Heightened threat environment for U.S. government and critical infrastructure sectors.
- Cyber / Information Space: Increased focus on cyber defense and potential retaliatory cyber operations.
- Economic / Social: Potential economic impacts on entities involved in cyber defense and increased scrutiny on cryptocurrency transactions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Operation Zero’s activities; increase collaboration with international partners to track and mitigate cyber threats.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; strengthen public-private partnerships in cybersecurity.
- Scenario Outlook:
- Best: Sanctions effectively dismantle Operation Zero’s operations, reducing cyber threats.
- Worst: Operation Zero adapts and continues operations, potentially with state support.
- Most-Likely: Disruption of Operation Zero’s activities with ongoing challenges in cyber defense.
6. Key Individuals and Entities
- Operation Zero
- Sergey Sergeyevich Zelenyuk
- Peter Williams
- Special Technology Services
- Marina Evgenyevna Vasanovich
- Azizjon Makhmudovich Mamashoyev
- Oleg Vyacheslavovich Kucherov
7. Thematic Tags
cybersecurity, cyber-espionage, sanctions, national security, cybercrime, U.S.-Russia relations, cryptocurrency, intellectual property protection
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us