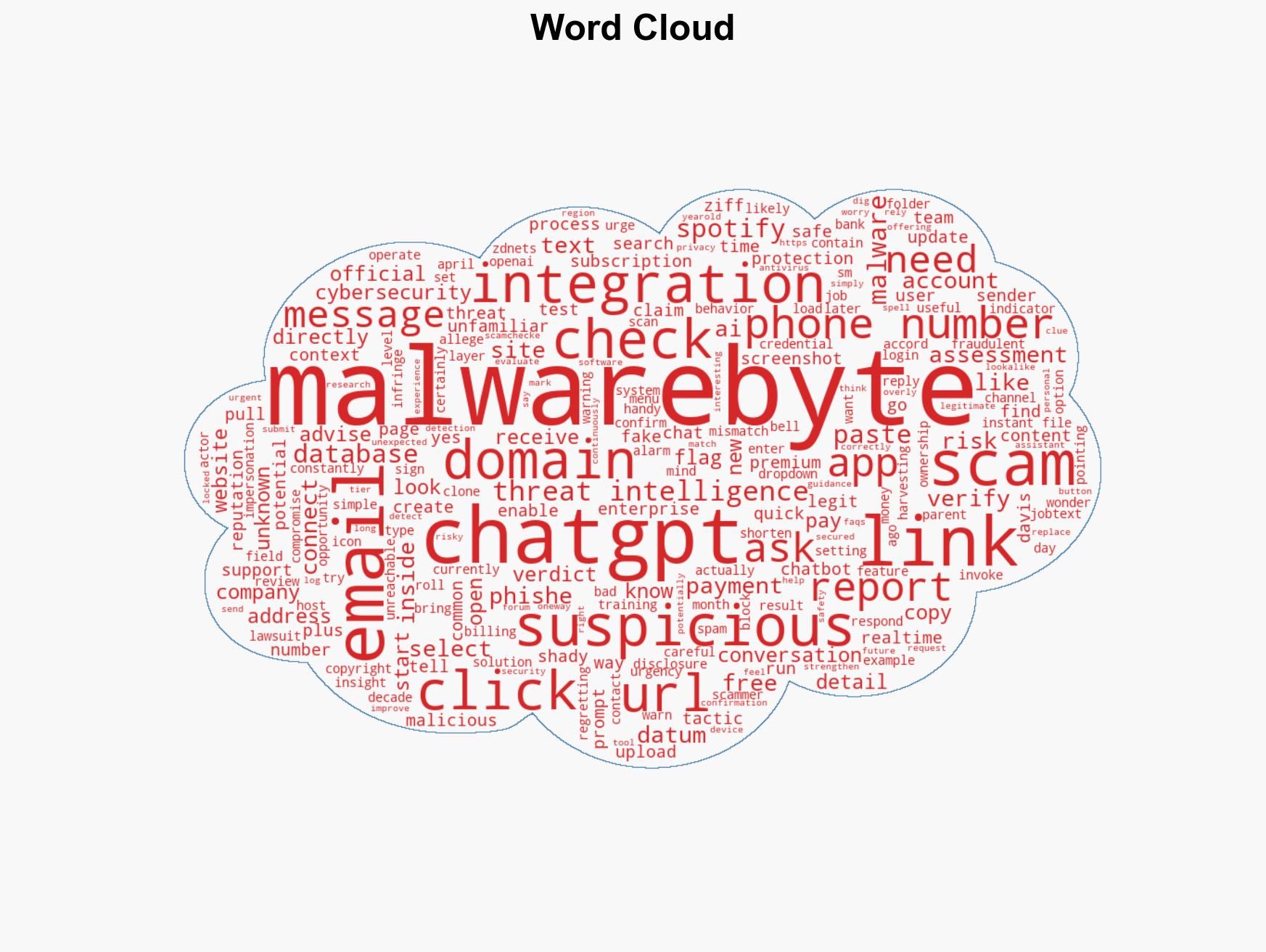
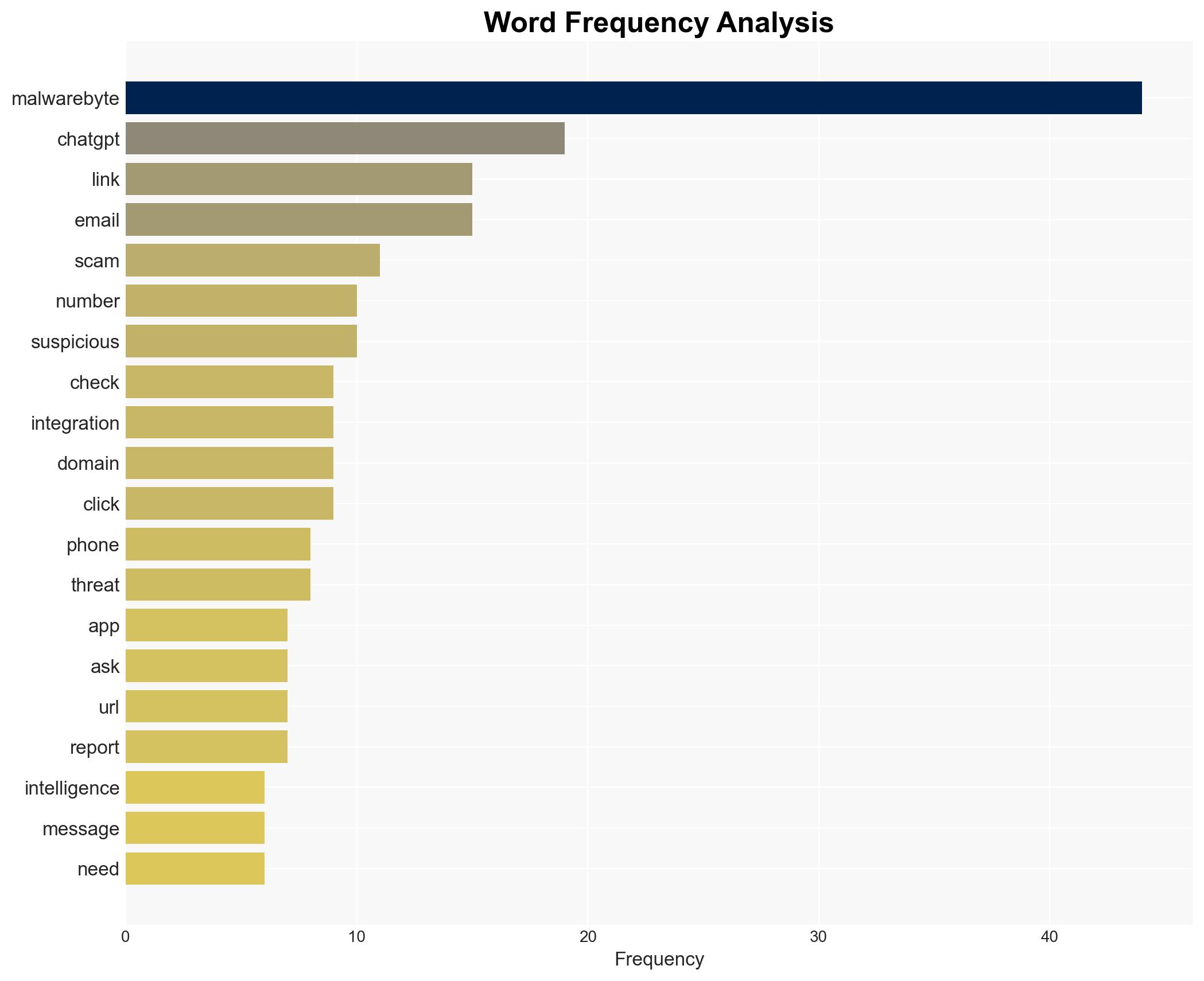
Leveraging Malwarebytes Integration in ChatGPT for Effective Scam Detection at No Cost
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How I turned ChatGPT into a scam detector using the new Malwarebytes integration – for free
1. BLUF (Bottom Line Up Front)
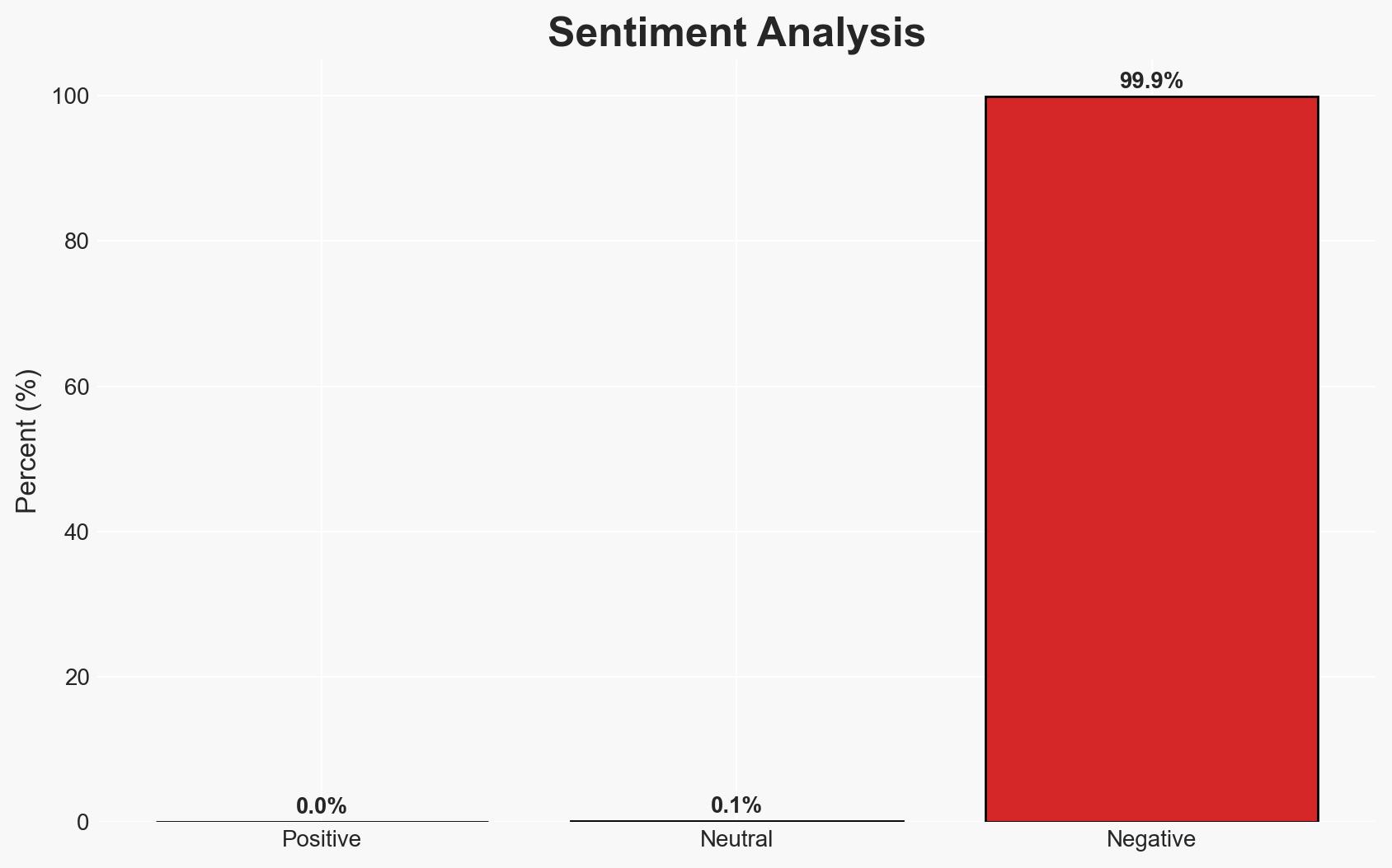
The integration of Malwarebytes with ChatGPT offers a potentially effective tool for identifying scams through AI-driven threat intelligence. This development may enhance cybersecurity measures for users by providing real-time insights into suspicious communications. However, the effectiveness of this integration is contingent on the accuracy and comprehensiveness of the underlying data. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
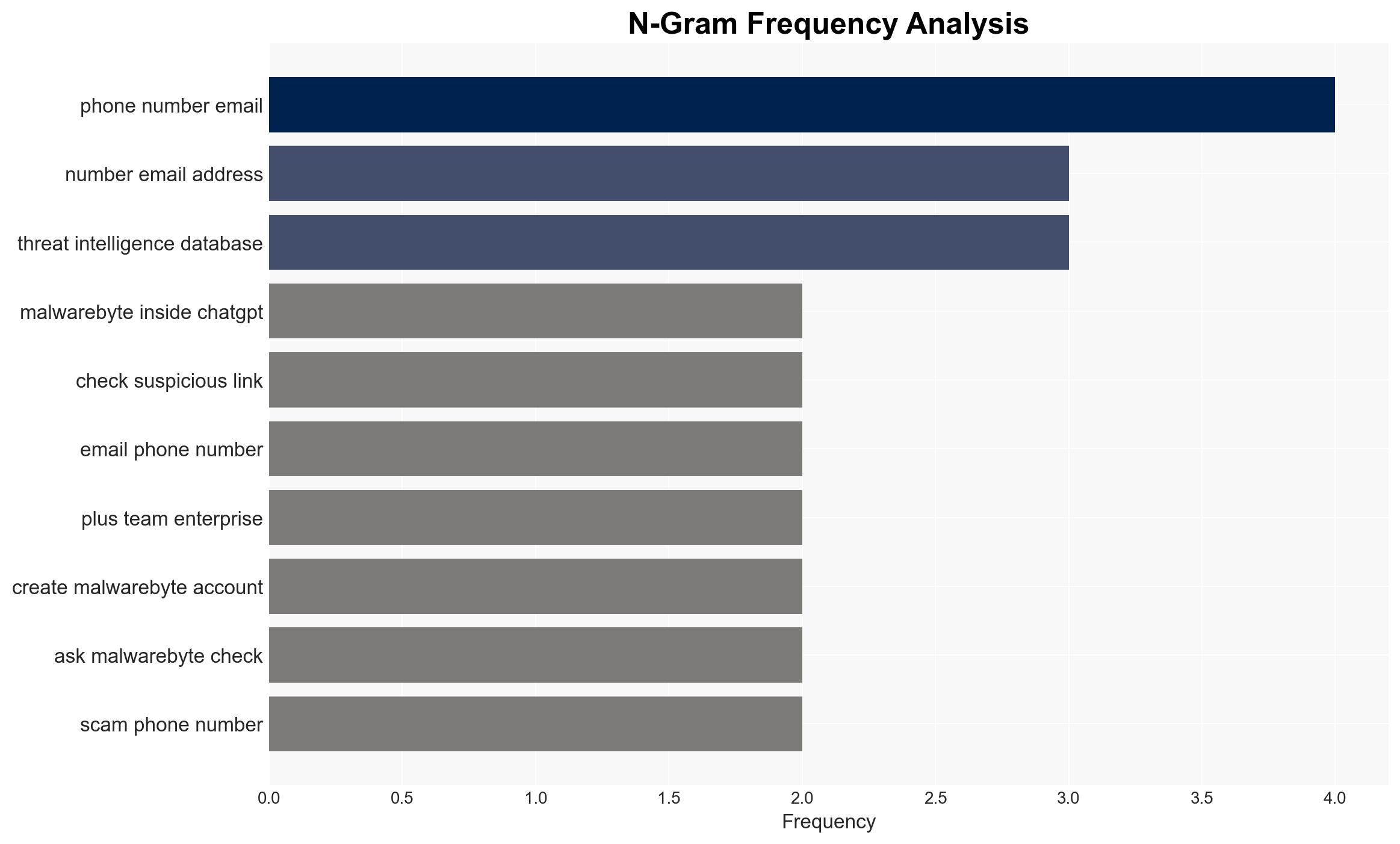
- Hypothesis A: The integration of Malwarebytes with ChatGPT significantly enhances users’ ability to detect scams by leveraging extensive cybersecurity databases. This hypothesis is supported by the integration’s access to decades of threat intelligence data. However, uncertainties include the potential for false positives or negatives in scam detection.
- Hypothesis B: The integration may have limited impact due to potential inaccuracies in threat detection and user reliance on AI without critical evaluation. This hypothesis is supported by the inherent limitations of AI in contextual understanding and the risk of users over-relying on automated assessments.
- Assessment: Hypothesis A is currently better supported due to the integration’s access to a comprehensive database and the potential for real-time threat intelligence to improve scam detection. Key indicators that could shift this judgment include evidence of significant false detection rates or user feedback indicating limited utility.
3. Key Assumptions and Red Flags
- Assumptions: The Malwarebytes database is up-to-date and comprehensive; users will correctly interpret AI-generated insights; the integration functions as described without technical issues.
- Information Gaps: Detailed performance metrics of the integration’s accuracy in detecting scams; user adoption rates and feedback on utility.
- Bias & Deception Risks: Potential cognitive bias in over-reliance on AI assessments; source bias from Malwarebytes’ data; risk of adversarial manipulation of AI inputs.
4. Implications and Strategic Risks
This development could influence the cybersecurity landscape by integrating AI with existing threat intelligence, potentially reducing the success rate of scams. However, reliance on AI without human oversight could introduce new vulnerabilities.
- Political / Geopolitical: Minimal direct implications; however, increased cybersecurity could indirectly affect state-sponsored cyber operations.
- Security / Counter-Terrorism: Enhanced scam detection may reduce the operational success of financially motivated cybercriminals.
- Cyber / Information Space: The integration represents a shift towards AI-driven cybersecurity solutions, potentially influencing future developments in digital threat detection.
- Economic / Social: Improved scam detection could enhance consumer confidence in digital communications, but over-reliance on AI could lead to complacency.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor the integration’s performance and gather user feedback to assess effectiveness; educate users on the limitations of AI-driven assessments.
- Medium-Term Posture (1–12 months): Develop partnerships with other cybersecurity entities to enhance data sharing; invest in improving AI accuracy and contextual understanding.
- Scenario Outlook:
- Best: Integration significantly reduces scam success rates, leading to broader adoption of AI-driven cybersecurity.
- Worst: High false detection rates undermine user trust, leading to decreased reliance on AI tools.
- Most-Likely: Moderate improvement in scam detection with ongoing refinements needed to address accuracy and user education.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, AI integration, scam detection, threat intelligence, user education, digital safety, AI limitations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us