Ex-Defense Contractor Sentenced to 7 Years for Selling National Security Exploits to Russian Broker
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Former Defense Contractor Boss Gets 7 Years for Selling Zero Days
1. BLUF (Bottom Line Up Front)
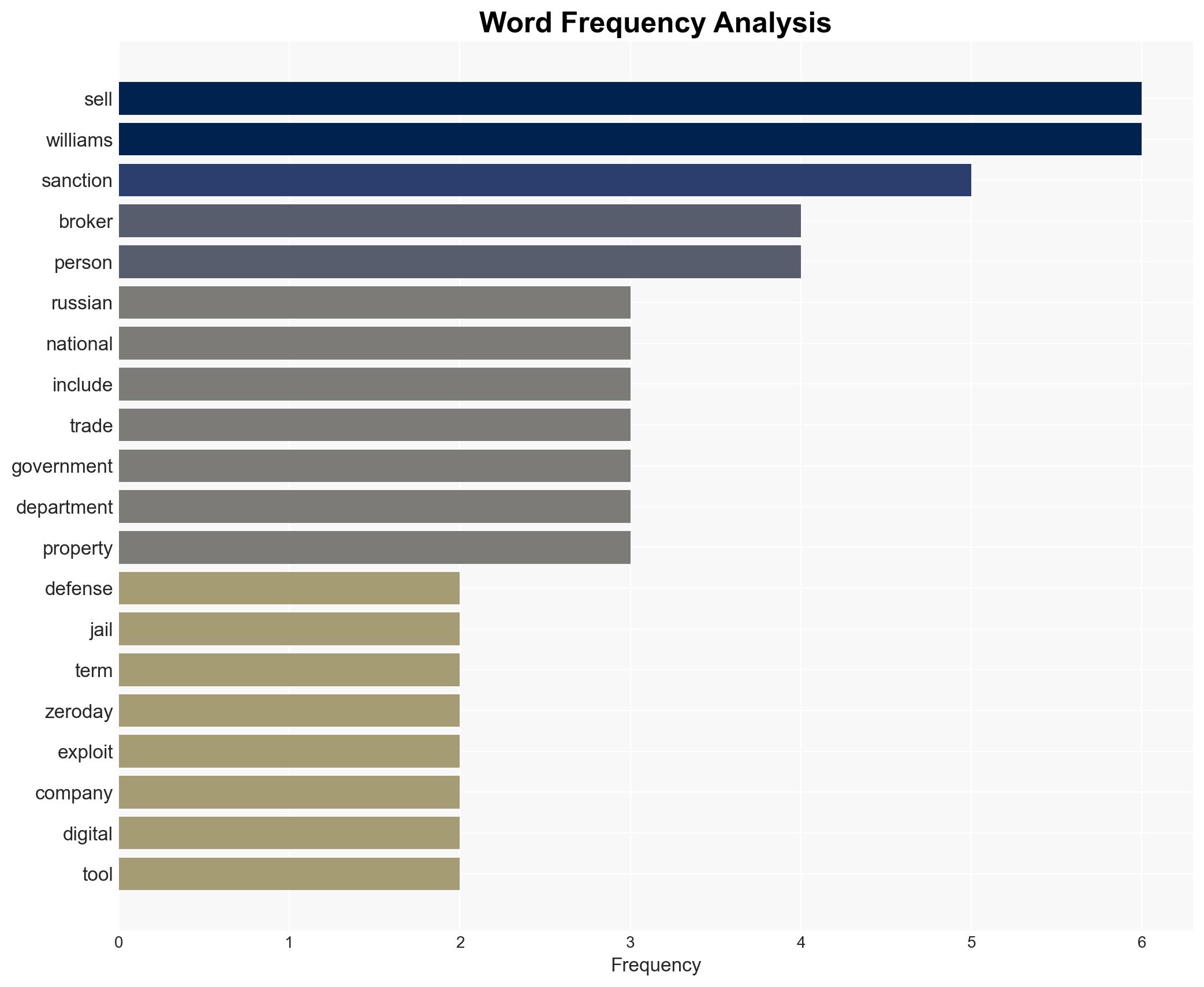
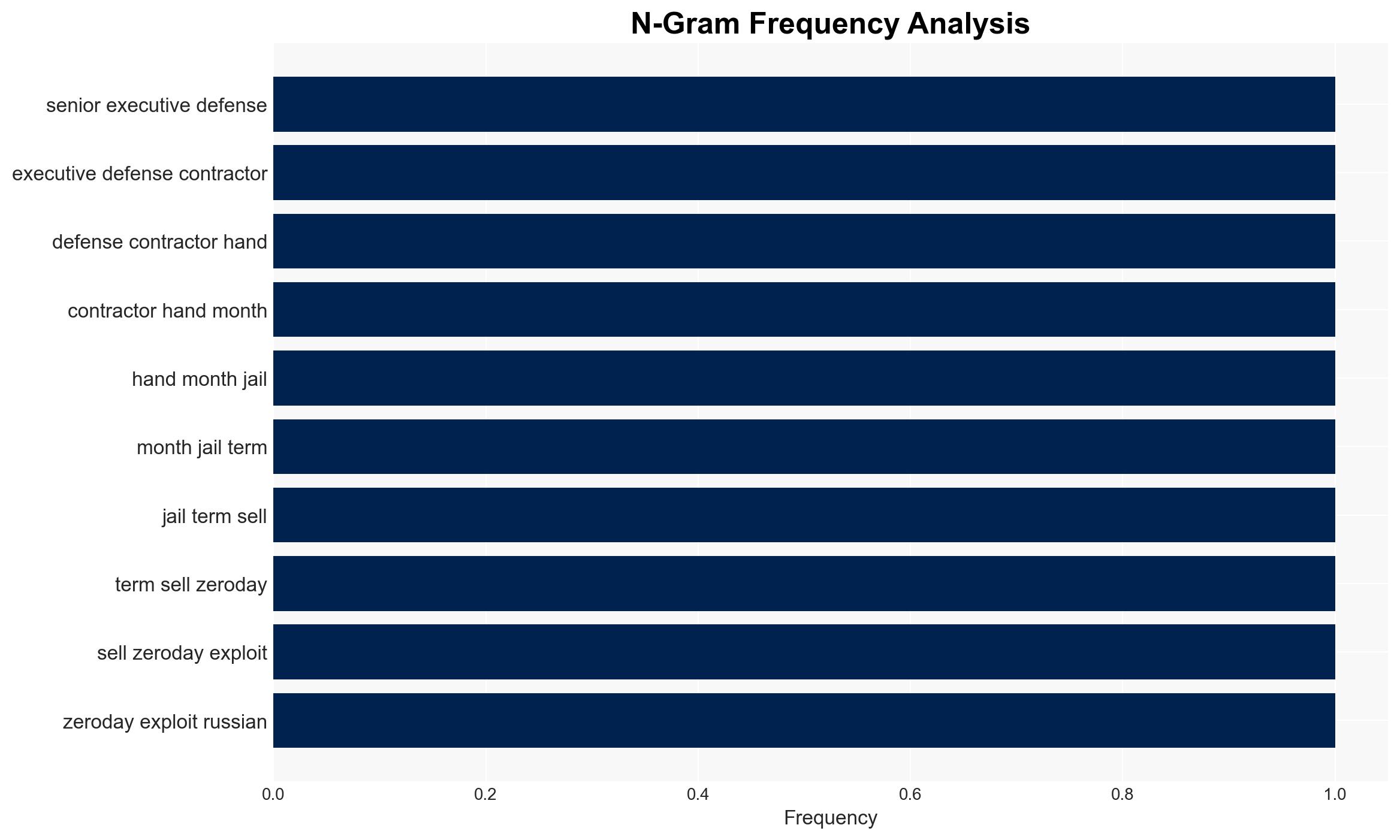
Peter Williams, a former executive at a US defense contractor, has been sentenced to 87 months for selling zero-day exploits to a Russian broker, posing significant national security risks. The most likely hypothesis is that Williams acted primarily for financial gain, impacting US and allied cybersecurity. This assessment is made with moderate confidence due to limited visibility into his motivations and the full extent of the broker’s network.
2. Competing Hypotheses
- Hypothesis A: Williams sold zero-day exploits primarily for financial gain, as evidenced by the $4 million in cryptocurrency payments and forfeited luxury items. However, uncertainties remain about whether financial motives were his sole driver.
- Hypothesis B: Williams was potentially coerced or influenced by external actors, possibly including the Russian government, to sell the exploits. This is less supported due to the lack of direct evidence of coercion or ideological alignment.
- Assessment: Hypothesis A is currently better supported due to the financial transactions and lack of evidence for coercion. Indicators such as communications with the broker or changes in lifestyle could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Williams acted independently; the broker has direct ties to the Russian government; the exploits sold were not previously known to US authorities.
- Information Gaps: Details on Williams’ communications with the broker and any potential accomplices; the full scope of the broker’s client network.
- Bias & Deception Risks: Potential bias in US sources emphasizing national security threats; possible deception by Williams regarding the extent of his cooperation with the broker.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of defense contractors and their cybersecurity practices, as well as heightened tensions between the US and Russia.
- Political / Geopolitical: Potential diplomatic friction between the US and Russia, influencing broader geopolitical dynamics.
- Security / Counter-Terrorism: Increased risk of cyber-attacks on US and allied infrastructure using the sold exploits.
- Cyber / Information Space: Heightened awareness and potential regulatory actions against commercial spyware and zero-day markets.
- Economic / Social: Potential financial losses for affected companies and increased costs for cybersecurity measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of defense contractors’ cybersecurity practices; increase intelligence sharing on zero-day markets.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve detection and mitigation of zero-day exploits; strengthen legal frameworks against cyber espionage.
- Scenario Outlook:
- Best: Strengthened cybersecurity measures prevent further exploitation, reducing national security risks.
- Worst: Exploits are used in significant cyber-attacks, causing widespread damage and escalating geopolitical tensions.
- Most-Likely: Incremental improvements in cybersecurity posture with ongoing threats from zero-day markets.
6. Key Individuals and Entities
- Peter Williams – Former executive at L3Harris
- Matrix LLC (aka Operation Zero) – Russian broker
- Sergey Sergeyevich Zelenyuk – Owner of Matrix LLC
- Special Technology Services – UAE-based company
- Trenchant/L3Harris – US defense contractor
7. Thematic Tags
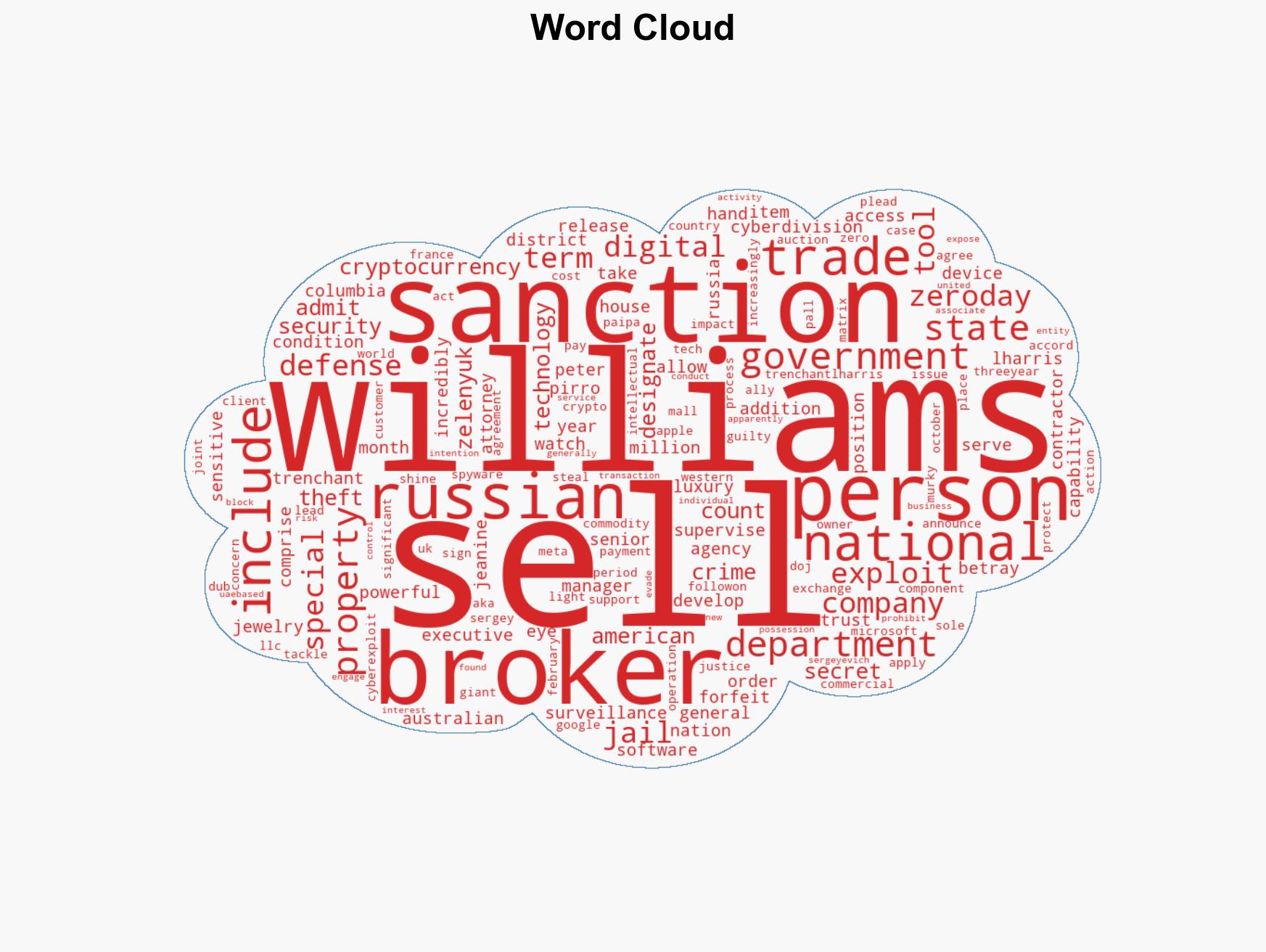
cybersecurity, cyber-espionage, national security, zero-day exploits, sanctions, defense contracting, US-Russia relations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us