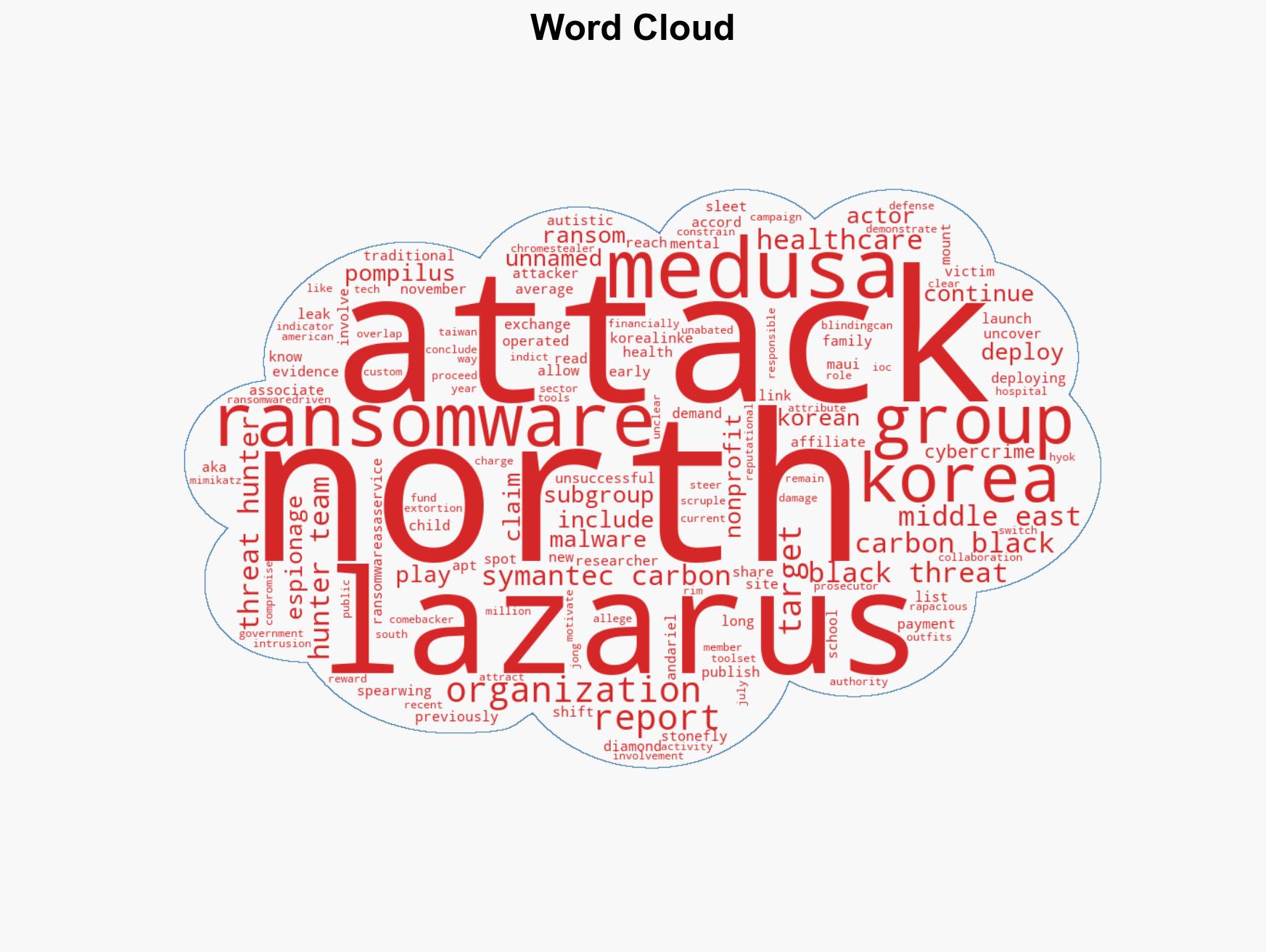
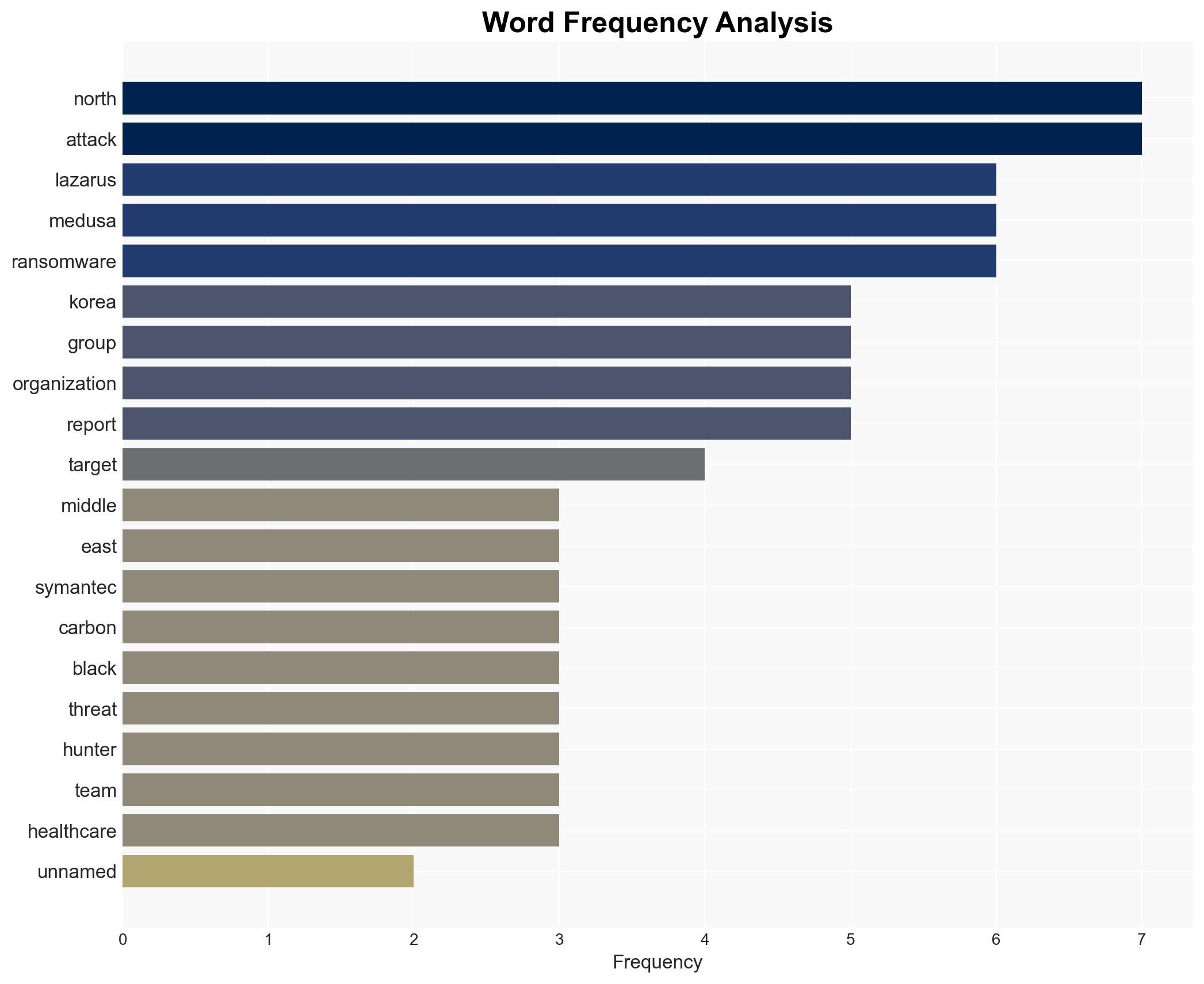
Lazarus Group Targets Middle East Organization with Medusa Ransomware Attack
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Lazarus APT group deployed Medusa Ransomware against Middle East target
1. BLUF (Bottom Line Up Front)
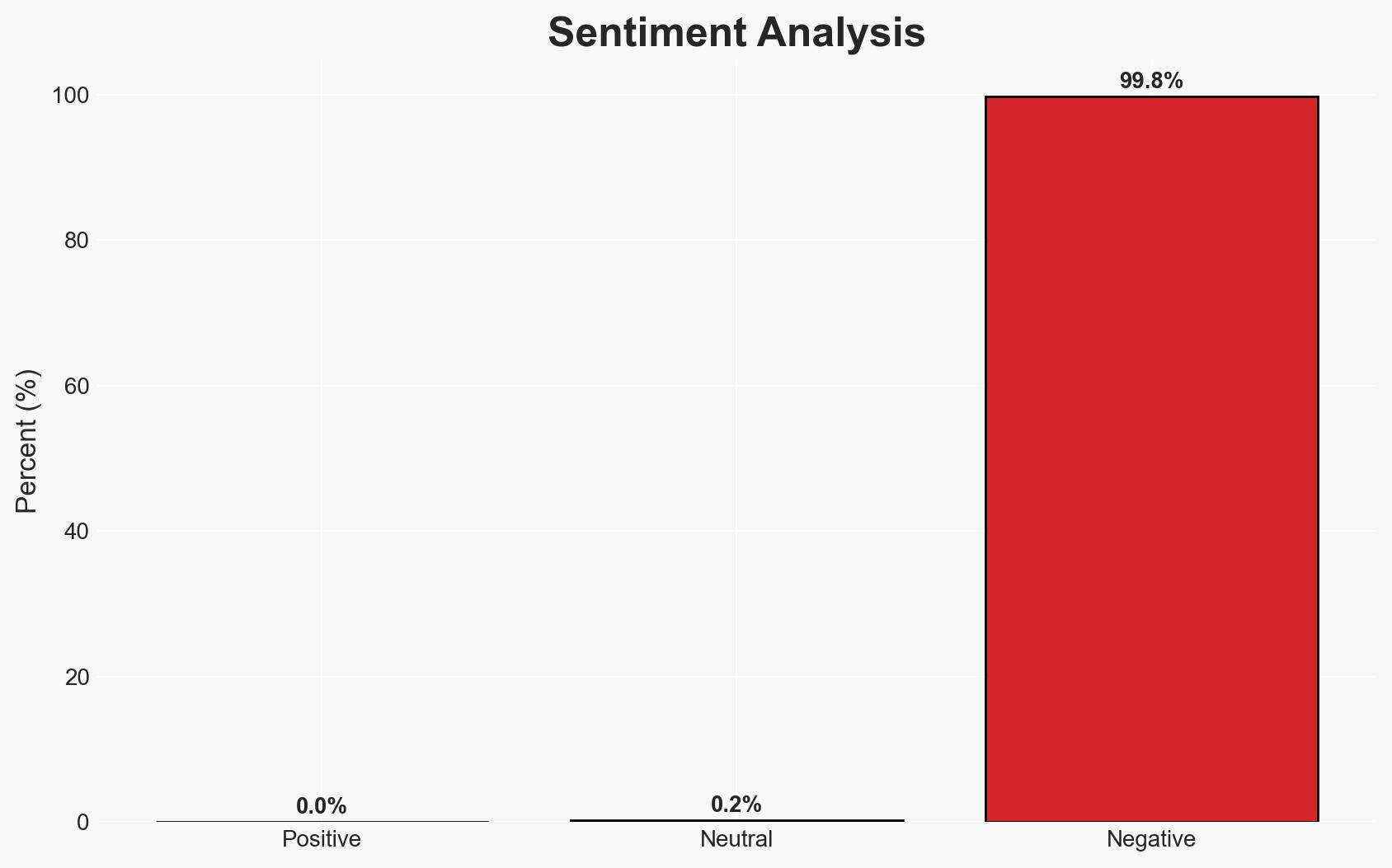
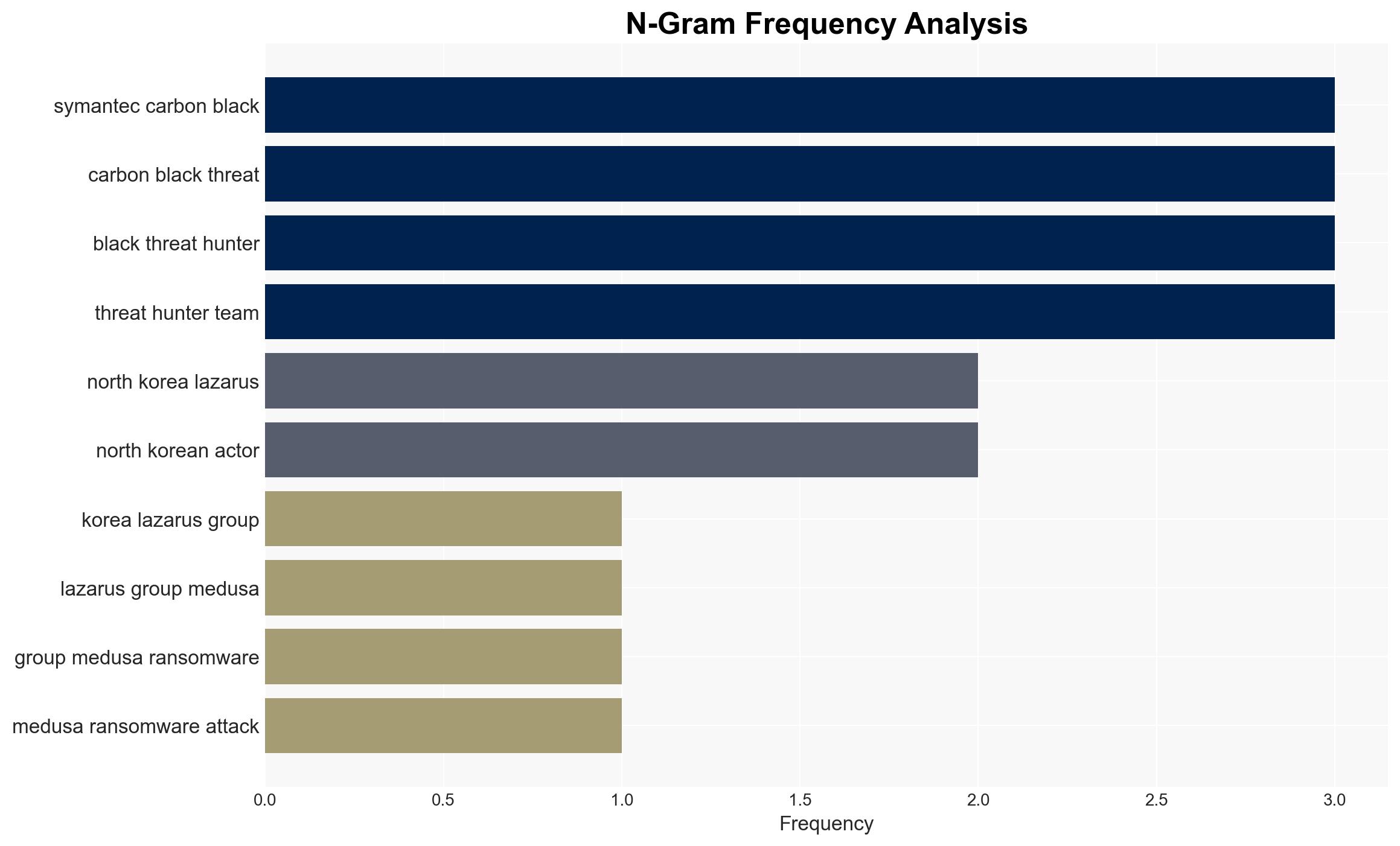
The Lazarus APT group, linked to North Korea, has reportedly deployed Medusa ransomware against an unnamed organization in the Middle East. This incident highlights the group’s ongoing shift towards financially motivated cybercrime. The attack underscores the persistent threat posed by North Korean cyber actors globally, with moderate confidence in the attribution to Lazarus based on toolset overlap and historical patterns.
2. Competing Hypotheses
- Hypothesis A: The Lazarus APT group is responsible for the Medusa ransomware attack on the Middle Eastern target. This is supported by the group’s known use of similar ransomware and historical patterns of targeting diverse sectors. However, the specific subgroup within Lazarus remains unidentified, creating uncertainty.
- Hypothesis B: Another cybercriminal group, possibly impersonating Lazarus, conducted the attack to mislead attribution efforts. This is less supported due to the lack of evidence of significant deviations from Lazarus’s known tactics and toolsets.
- Assessment: Hypothesis A is currently better supported due to the alignment of tactics and historical behavior of Lazarus. Future indicators, such as distinct operational signatures or claims of responsibility, could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attribution to Lazarus is based on consistent use of ransomware; North Korea continues to support financially motivated cyber operations; Medusa ransomware is accessible to Lazarus affiliates.
- Information Gaps: Lack of specific details on the targeted Middle Eastern organization; unclear subgroup within Lazarus responsible for the attack.
- Bias & Deception Risks: Potential confirmation bias in attributing attacks to Lazarus due to their notoriety; risk of deception by other actors mimicking Lazarus’s tactics.
4. Implications and Strategic Risks
This development could exacerbate tensions in the Middle East and increase scrutiny of North Korean cyber activities. The use of ransomware by state-linked actors may prompt international responses and affect diplomatic relations.
- Political / Geopolitical: Potential for increased sanctions or diplomatic actions against North Korea; heightened regional tensions.
- Security / Counter-Terrorism: Increased threat level for organizations in the Middle East and globally; potential for retaliatory cyber operations.
- Cyber / Information Space: Escalation in ransomware deployment by state actors; potential for increased cyber defense measures.
- Economic / Social: Disruption to targeted sectors; potential economic impacts from ransom payments and operational downtime.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of ransomware activities; share Indicators of Compromise (IoCs) with relevant sectors; increase cybersecurity awareness and training.
- Medium-Term Posture (1–12 months): Strengthen international partnerships for cyber threat intelligence sharing; develop resilience strategies against ransomware; invest in advanced threat detection capabilities.
- Scenario Outlook:
- Best: Increased international cooperation leads to effective deterrence and reduction in ransomware attacks.
- Worst: Escalation of cyber operations by North Korea leads to significant geopolitical tensions and economic disruptions.
- Most-Likely: Continued sporadic ransomware attacks by Lazarus with gradual improvements in global cyber defense measures.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, ransomware, North Korea, Lazarus Group, Middle East, cybercrime, international relations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us