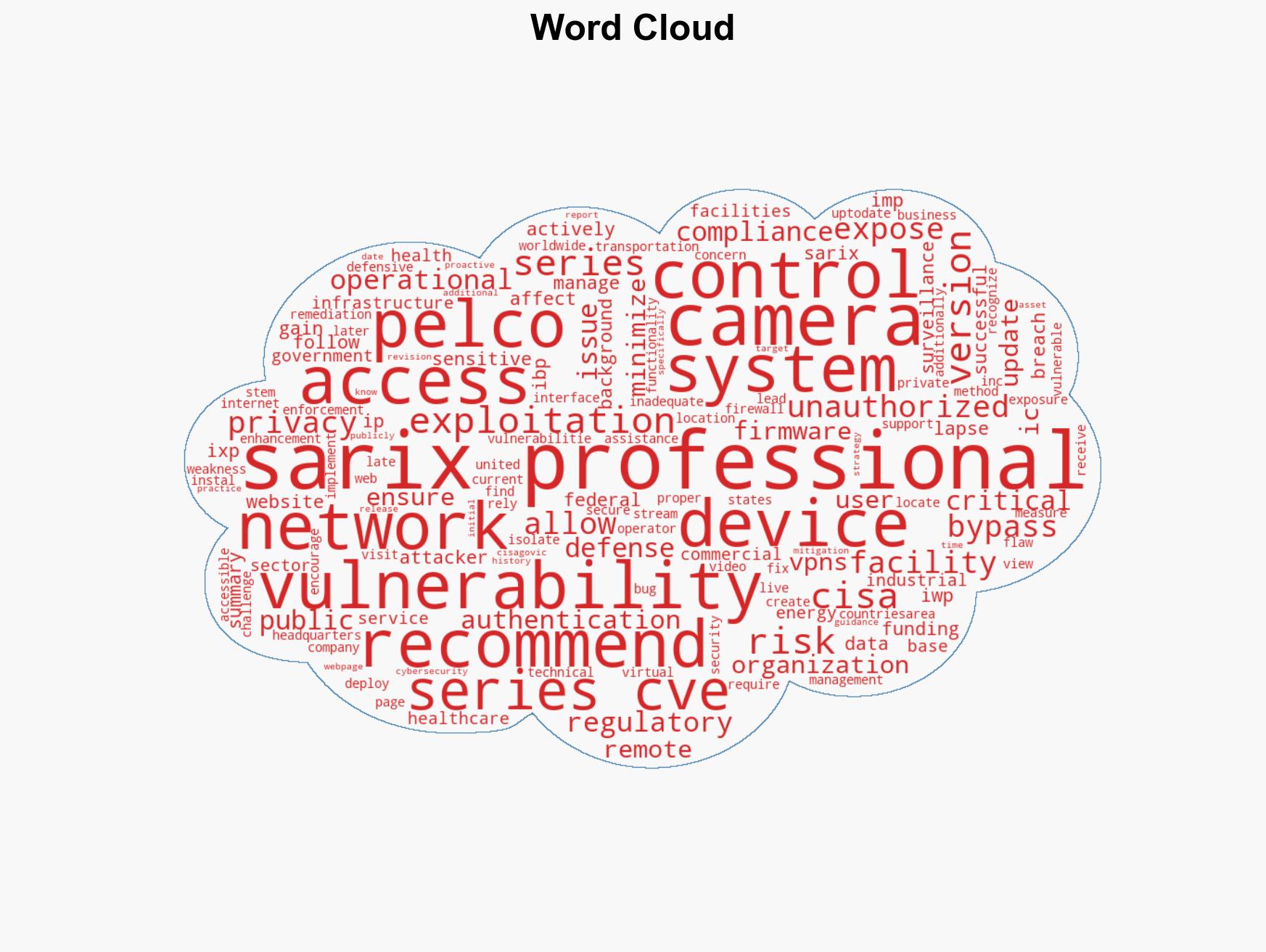
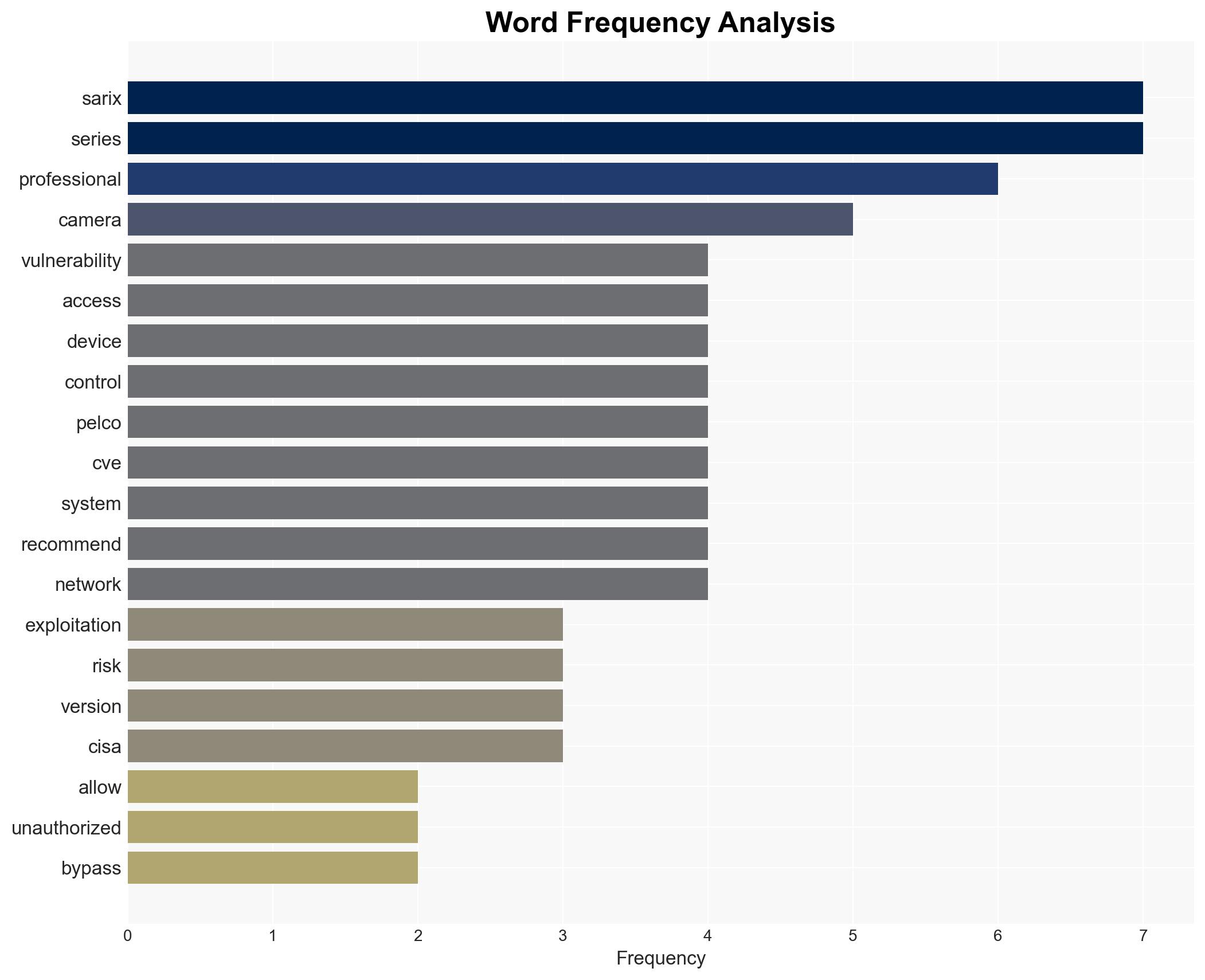
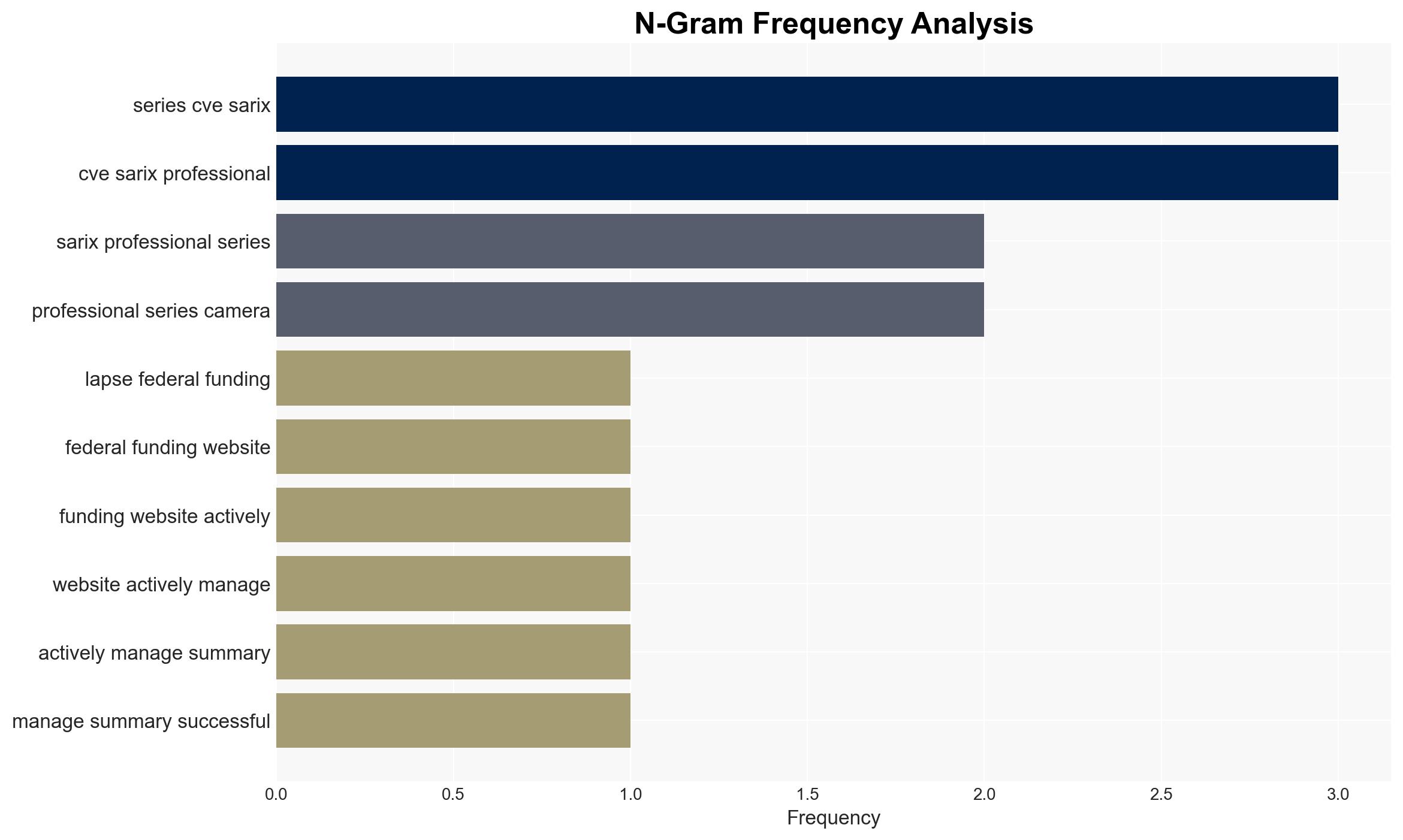
Vulnerability Discovered in Pelco Sarix Pro 3 Series IP Cameras Exposing Sensitive Data and Security Risks
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Pelco Inc Sarix Pro 3 Series IP Cameras
1. BLUF (Bottom Line Up Front)
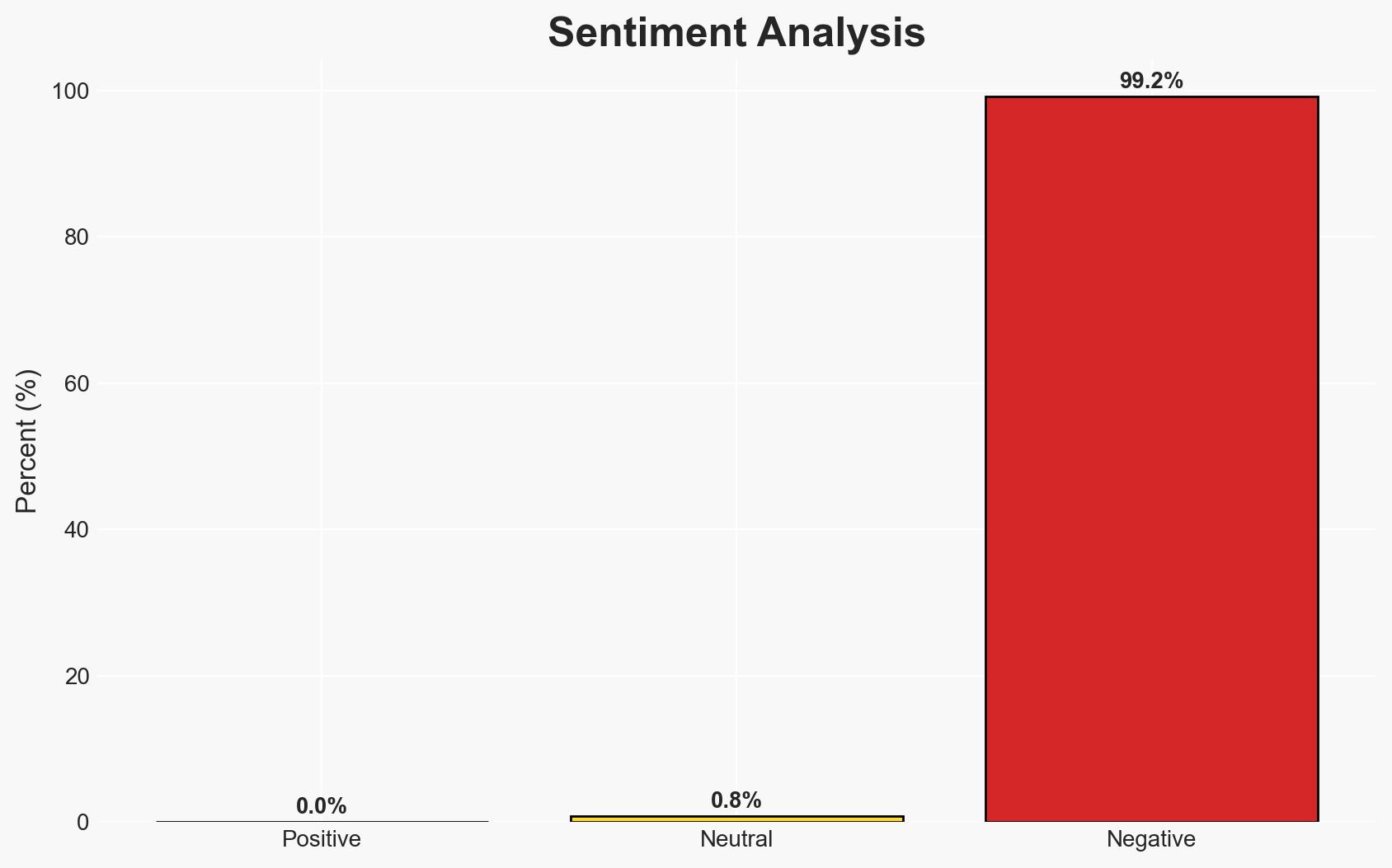
The Pelco Inc Sarix Pro 3 Series IP Cameras are vulnerable to an authentication bypass issue, potentially allowing unauthorized access to sensitive data and live video streams. This vulnerability affects critical infrastructure sectors globally. The most likely hypothesis is that this vulnerability could be exploited by malicious actors to compromise security systems, with moderate confidence due to the lack of reported exploitation incidents.
2. Competing Hypotheses
- Hypothesis A: The vulnerability will be exploited by cybercriminals or state-sponsored actors to gain unauthorized access to sensitive facilities. This is supported by the widespread deployment of these cameras in critical infrastructure sectors and the potential for significant operational impact. However, no known public exploitation has been reported, which contradicts this hypothesis.
- Hypothesis B: The vulnerability will remain largely unexploited due to proactive mitigation measures by affected organizations and the availability of firmware updates. This is supported by the immediate remediation steps recommended by Pelco, Inc. and CISA, although the effectiveness of these measures depends on timely implementation by users.
- Assessment: Hypothesis B is currently better supported due to the lack of reported exploitation and the availability of mitigations. Key indicators that could shift this judgment include reports of successful exploitation or widespread failure to apply updates.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will implement recommended security updates; the vulnerability is not currently being exploited; mitigation measures are effective in preventing unauthorized access.
- Information Gaps: Specific details on the number of affected devices and the extent of their deployment in critical sectors; real-time data on exploitation attempts.
- Bias & Deception Risks: Potential underreporting of exploitation incidents; reliance on vendor-provided information which may be biased towards minimizing perceived risk.
4. Implications and Strategic Risks
This vulnerability could evolve into a significant security risk if not addressed promptly, potentially affecting global critical infrastructure sectors.
- Political / Geopolitical: Potential for diplomatic tensions if state-sponsored actors are implicated in exploiting the vulnerability.
- Security / Counter-Terrorism: Increased risk of unauthorized surveillance and data breaches in sensitive facilities.
- Cyber / Information Space: Potential for increased cyber espionage activities targeting vulnerable systems.
- Economic / Social: Possible financial losses and reputational damage for affected organizations, leading to decreased trust in security technologies.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Organizations should immediately update camera firmware and implement CISA’s recommended cybersecurity measures.
- Medium-Term Posture (1–12 months): Develop and maintain robust cybersecurity protocols, conduct regular security audits, and enhance incident response capabilities.
- Scenario Outlook:
- Best Case: Vulnerability is patched, and no exploitation occurs, leading to increased trust in security systems.
- Worst Case: Widespread exploitation leads to significant operational disruptions and geopolitical tensions.
- Most Likely: Limited exploitation occurs, mitigated by effective security measures and updates.
6. Key Individuals and Entities
- Pelco, Inc.
- Cybersecurity and Infrastructure Security Agency (CISA)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, critical infrastructure, vulnerability management, surveillance technology, information security, operational risk, regulatory compliance
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us