Trend Micro addresses critical vulnerabilities in Apex One, urging immediate updates to prevent remote code e…
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Trend Micro fixes two critical flaws in Apex One
1. BLUF (Bottom Line Up Front)
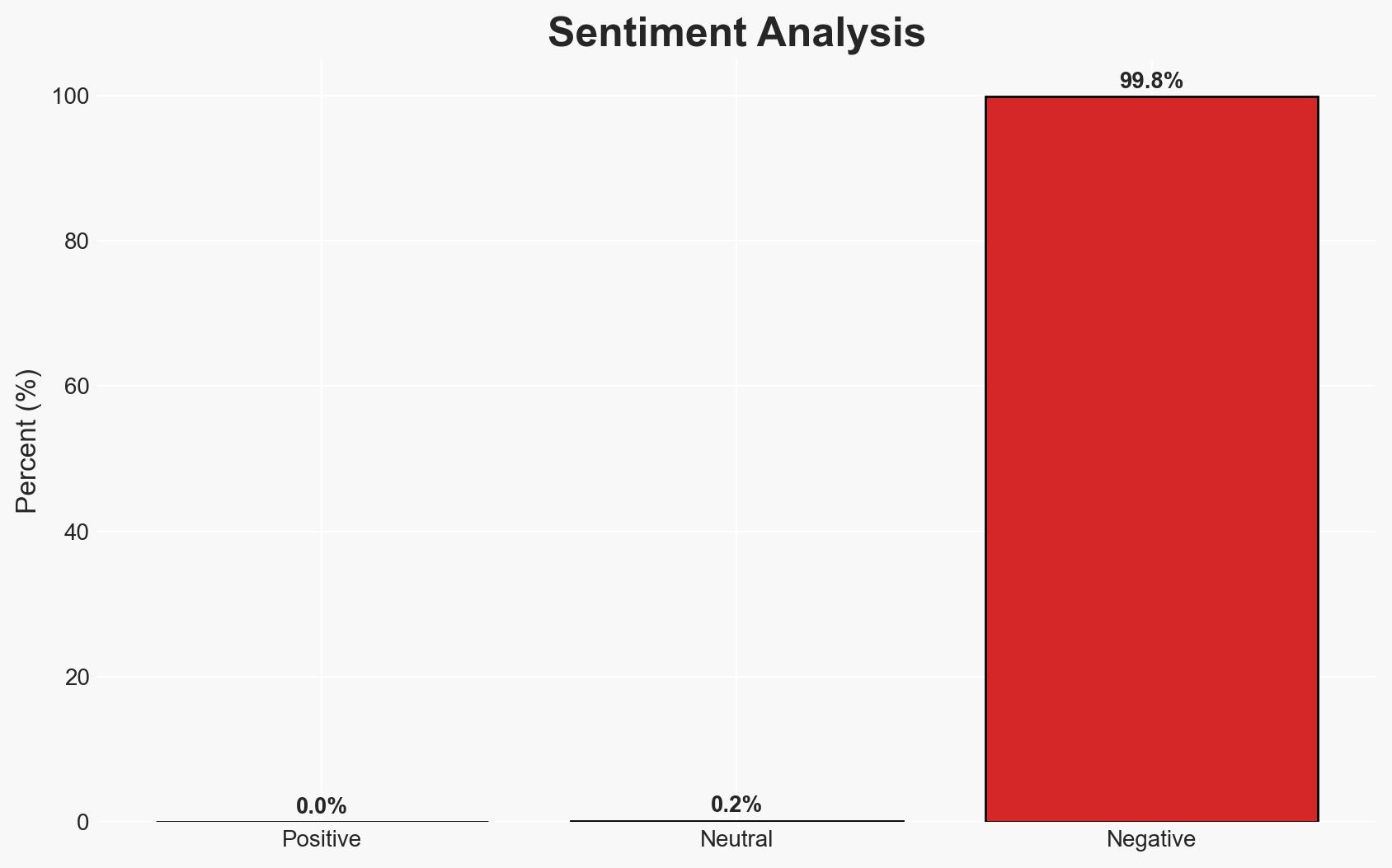
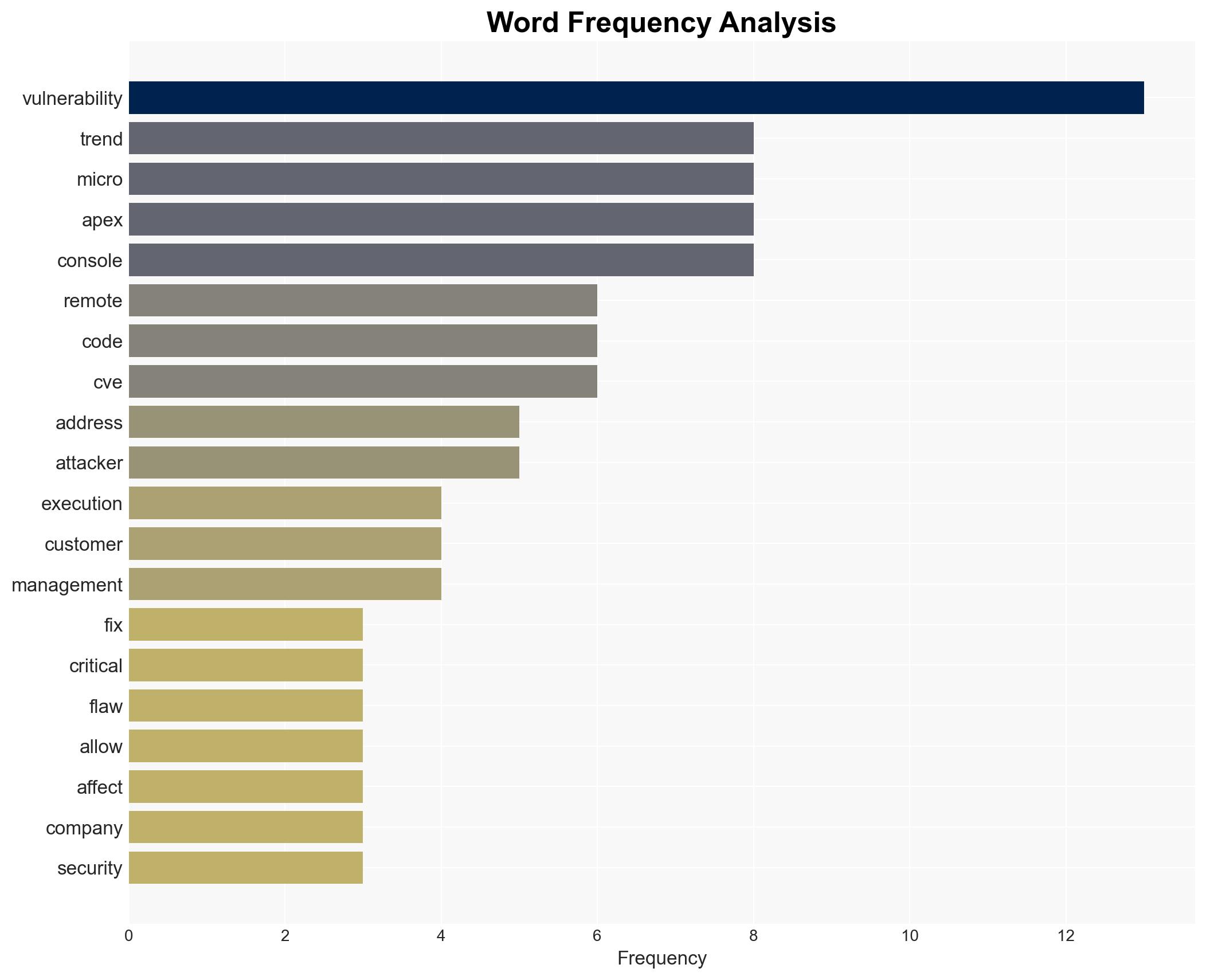
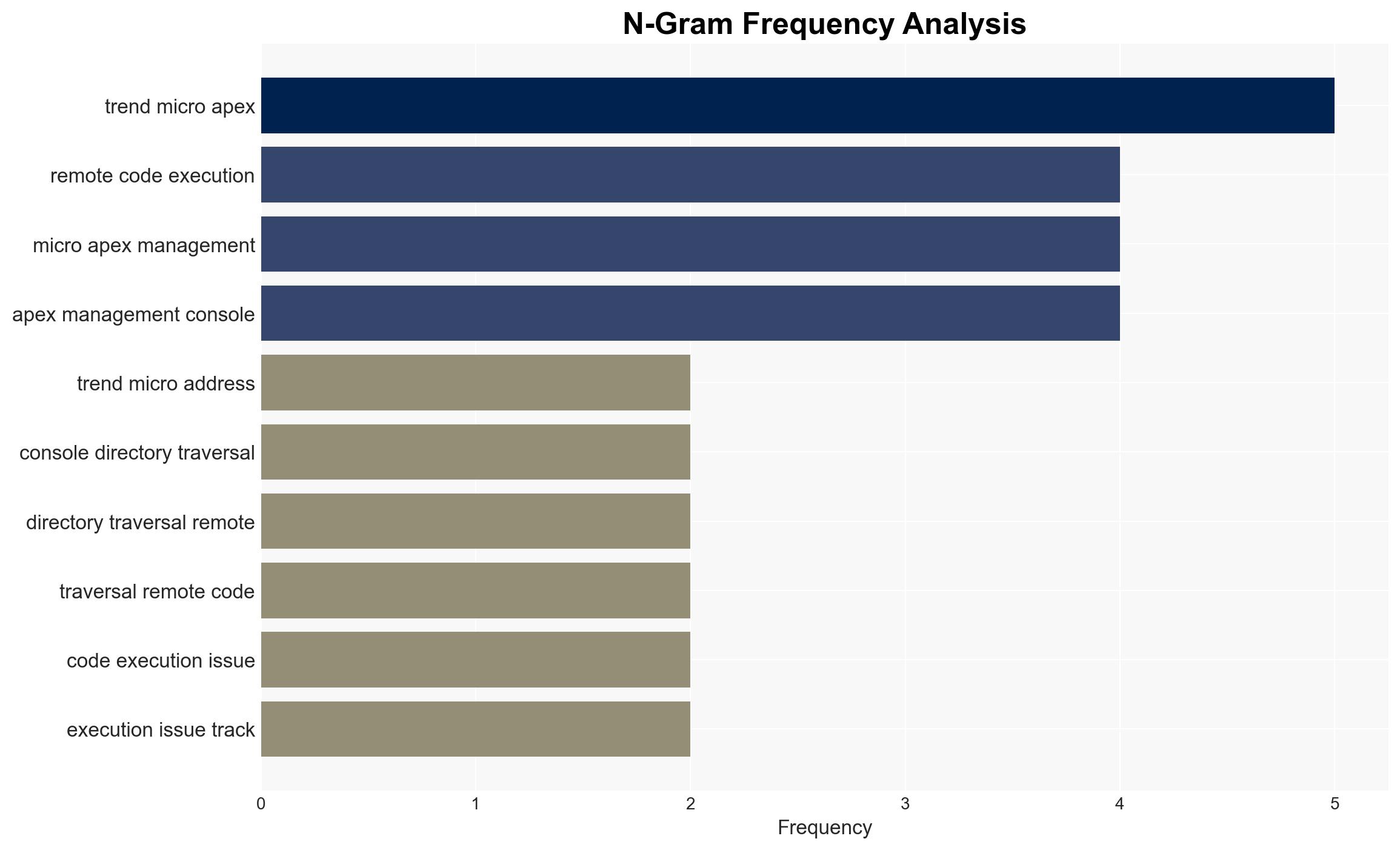
Trend Micro has patched two critical vulnerabilities in its Apex One endpoint security solution, which could allow remote code execution on Windows systems. The most likely hypothesis is that these vulnerabilities, if exploited, could significantly compromise affected systems, particularly those with exposed management consoles. The overall confidence level in this assessment is moderate, given the lack of evidence of active exploitation.
2. Competing Hypotheses
- Hypothesis A: The vulnerabilities are being actively exploited by threat actors to compromise systems. Supporting evidence includes the critical nature of the vulnerabilities and the potential for significant impact. Contradicting evidence is the lack of reported active exploitation.
- Hypothesis B: The vulnerabilities are not currently being exploited in the wild, and Trend Micro’s prompt patching has mitigated immediate risks. Supporting evidence includes Trend Micro’s proactive patching and lack of exploitation reports. Contradicting evidence is the high CVSS score indicating severe potential risk.
- Assessment: Hypothesis B is currently better supported due to the absence of confirmed exploitation reports and Trend Micro’s swift response. Indicators that could shift this judgment include credible reports of exploitation or increased scanning activity targeting these vulnerabilities.
3. Key Assumptions and Red Flags
- Assumptions: Trend Micro’s patches are effective; no widespread exploitation has occurred; affected systems will apply patches promptly.
- Information Gaps: Lack of data on whether any exploitation attempts have been detected; unclear if all affected systems are aware of the patches.
- Bias & Deception Risks: Potential underreporting of exploitation attempts; reliance on vendor-provided information may introduce bias.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of endpoint security solutions and highlight the importance of timely patch management. Over time, failure to patch could result in significant breaches.
- Political / Geopolitical: Minimal direct implications unless state actors exploit these vulnerabilities for espionage.
- Security / Counter-Terrorism: Increased risk of cyber intrusions and data breaches if vulnerabilities are exploited.
- Cyber / Information Space: Potential for increased cyber threat activity targeting unpatched systems.
- Economic / Social: Organizations may face financial losses and reputational damage if systems are compromised.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Ensure all systems apply the latest patches; monitor for any signs of exploitation attempts.
- Medium-Term Posture (1–12 months): Enhance patch management processes; consider additional security measures for exposed management consoles.
- Scenario Outlook: Best: No exploitation occurs due to effective patching. Worst: Widespread exploitation leads to significant breaches. Most-Likely: Limited exploitation attempts with minimal impact due to proactive patching.
6. Key Individuals and Entities
- Trend Micro
- Jacky Hsieh
- Charles Yang
- CoreCloud Tech
7. Thematic Tags
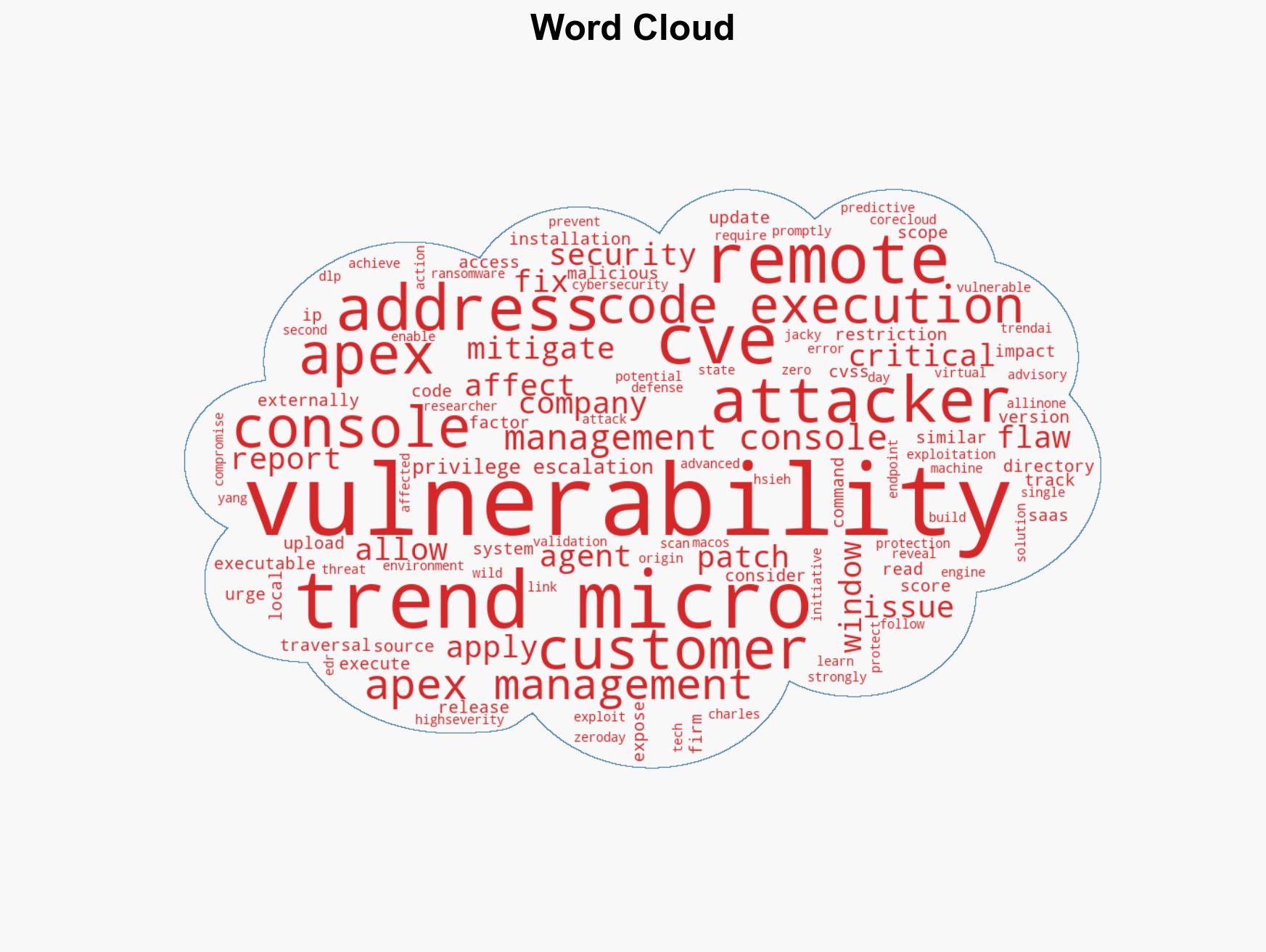
cybersecurity, vulnerability management, endpoint security, remote code execution, patch management, cyber threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us