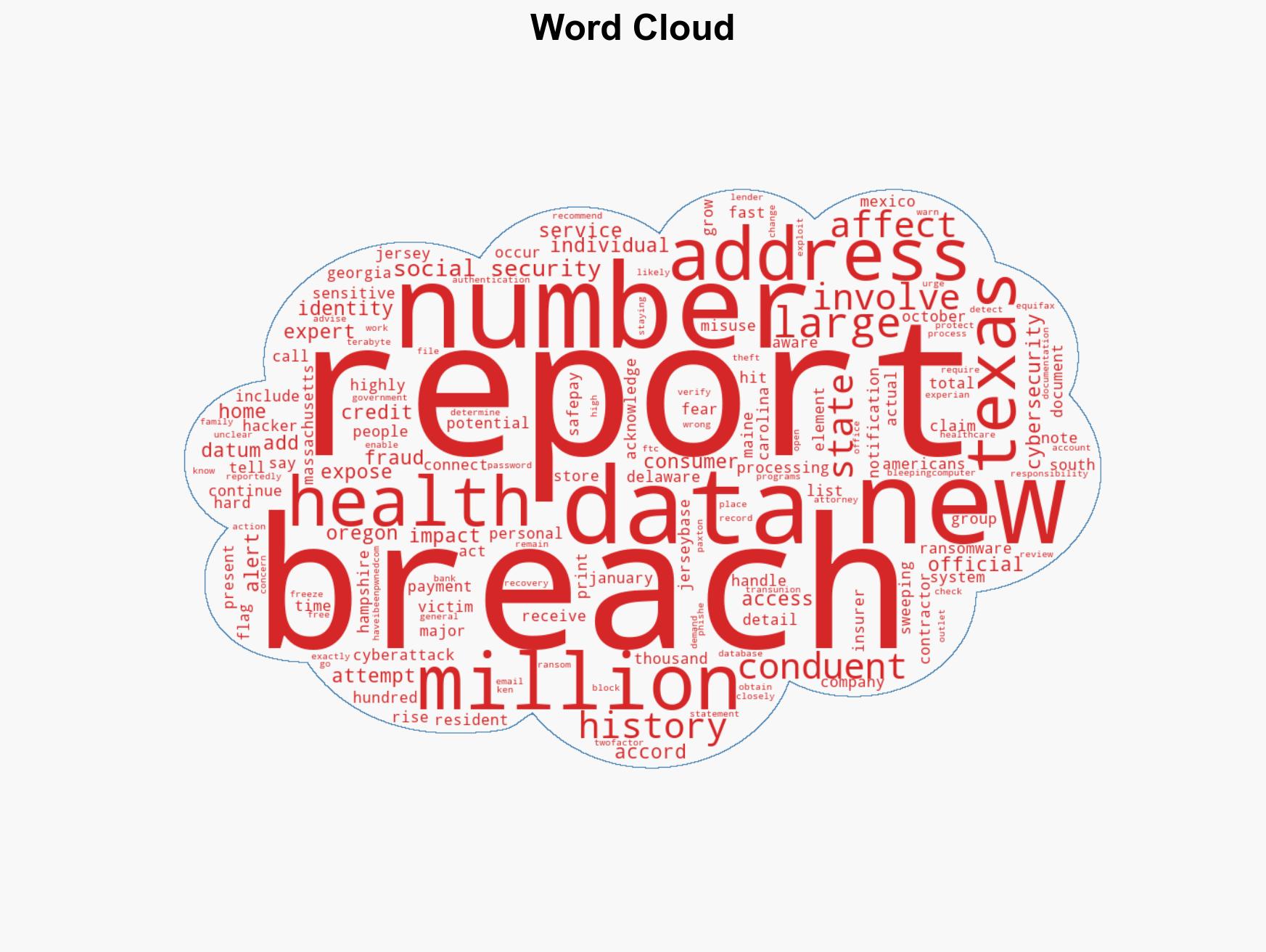
Massive Cyberattack Exposes Data of Over 25 Million Americans in Unprecedented Security Breach
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Over 25 million hit in whats being called the largest data breach in US history
1. BLUF (Bottom Line Up Front)
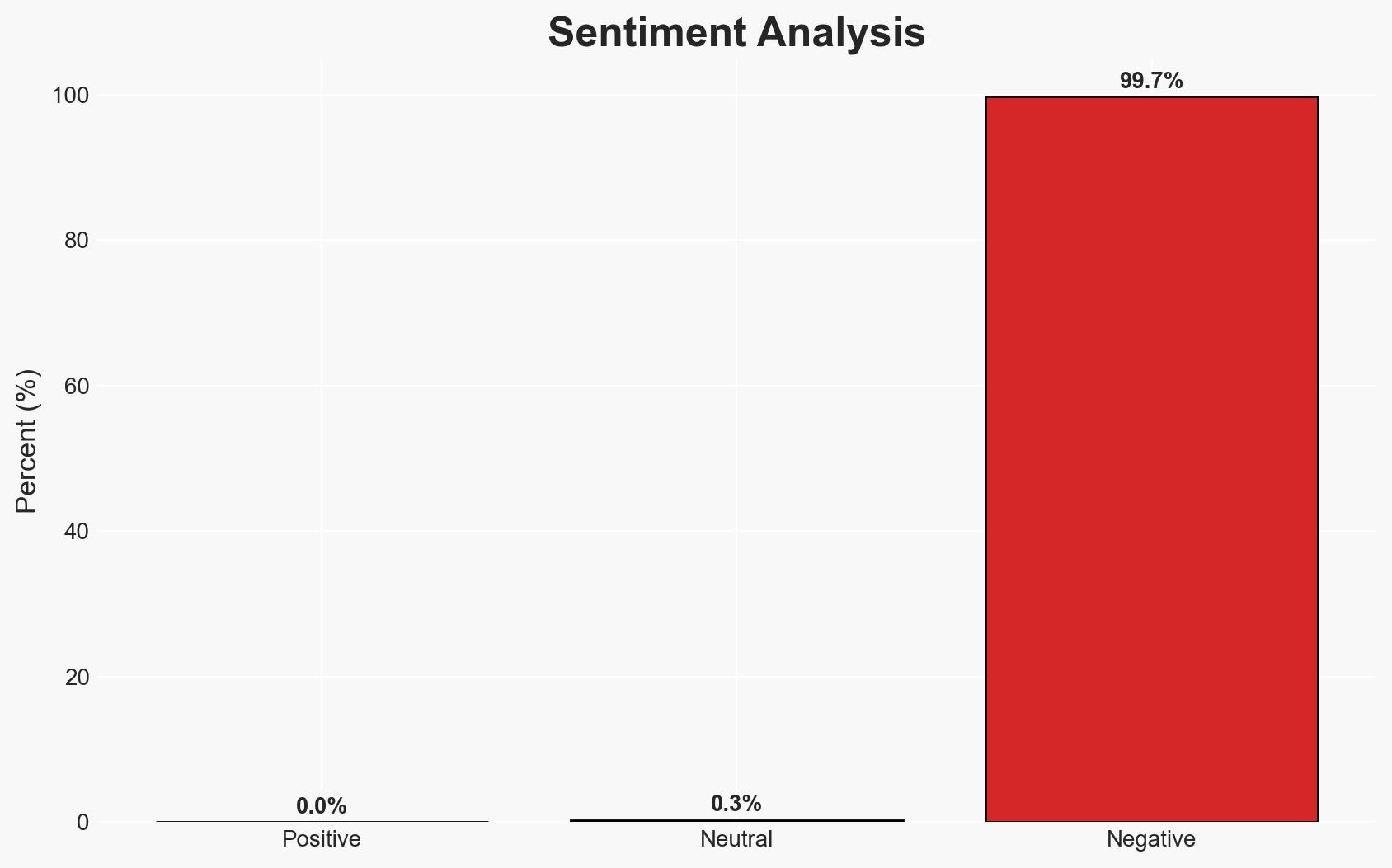
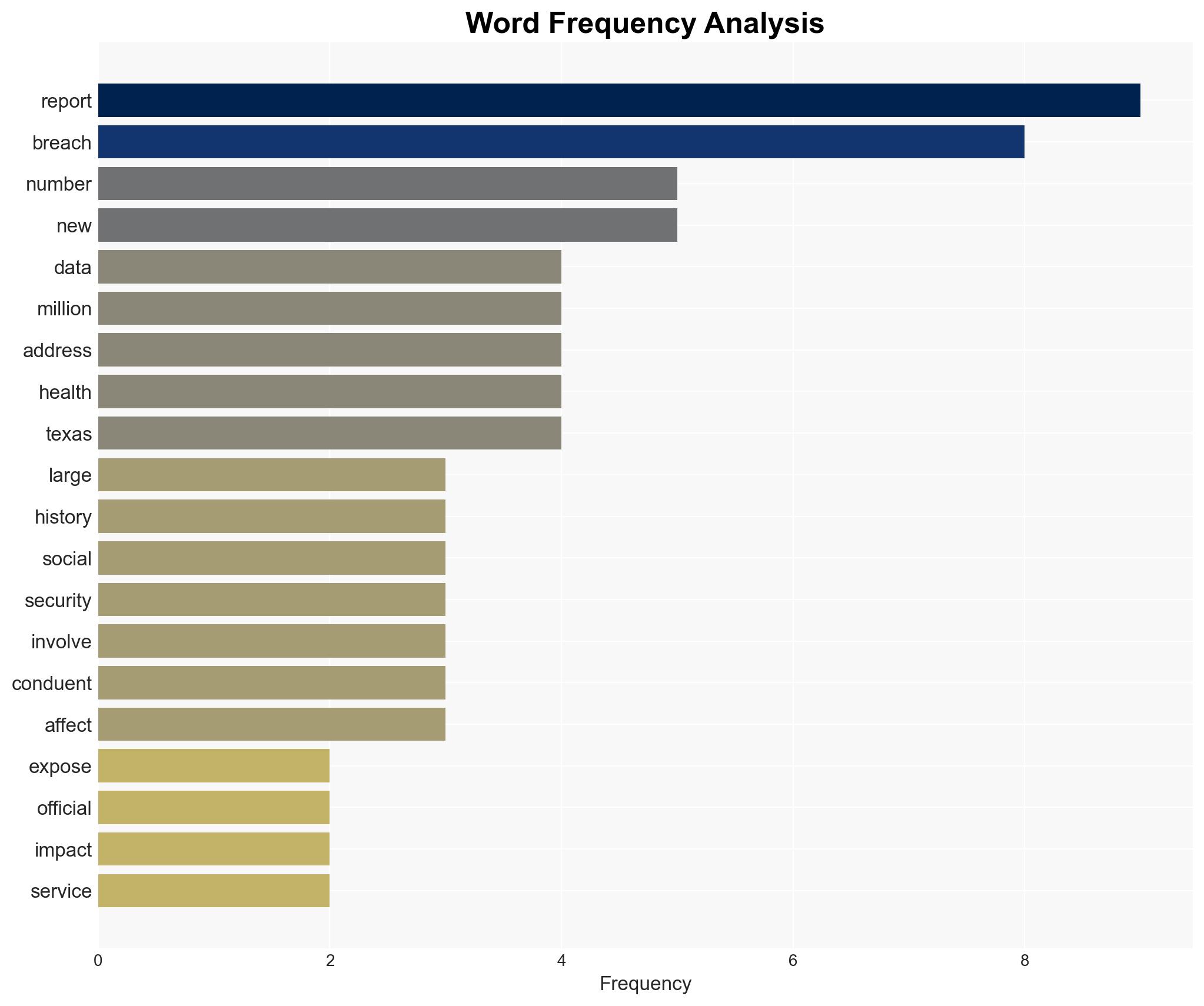
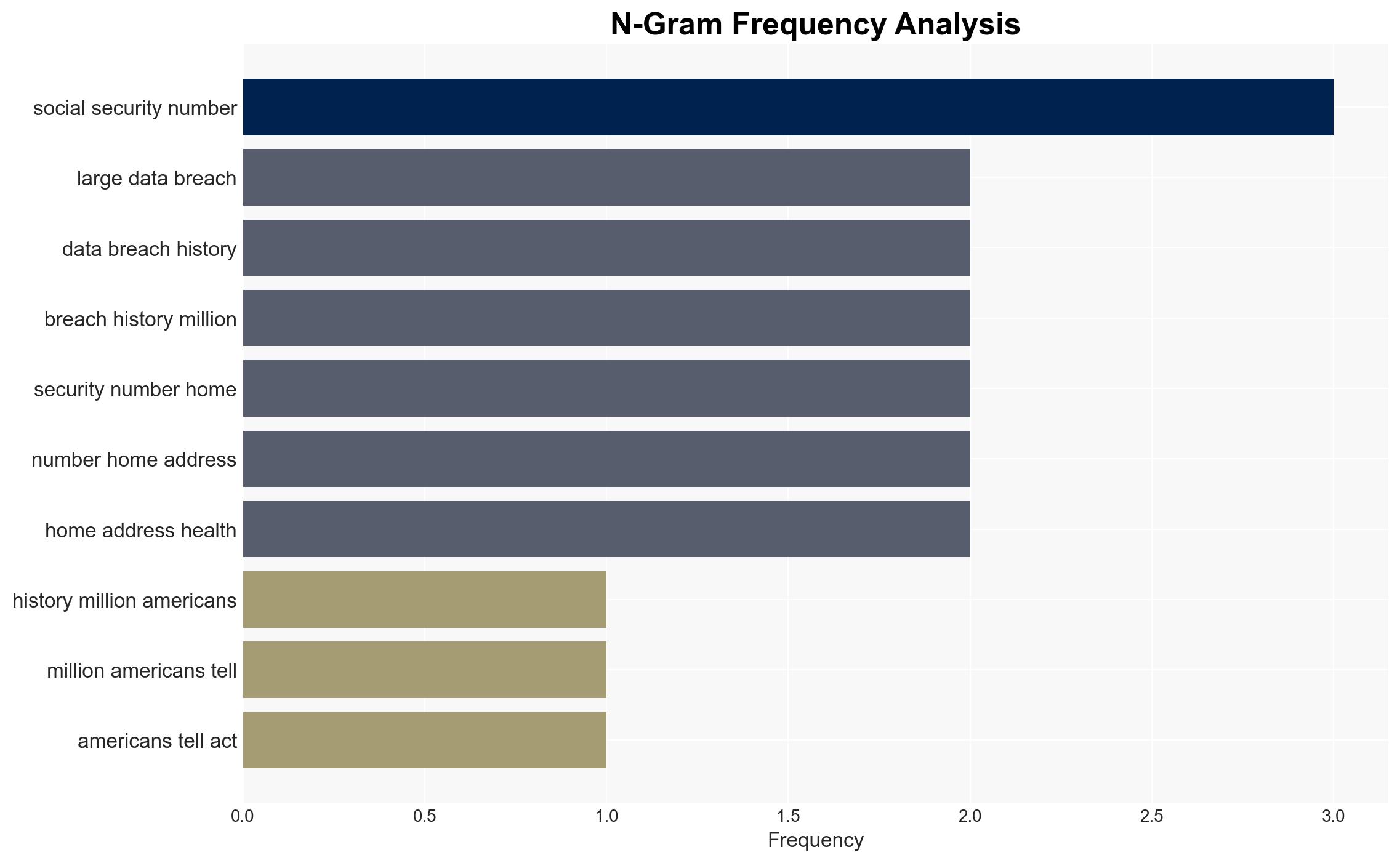
The largest data breach in U.S. history has compromised sensitive personal information of over 25 million individuals, primarily affecting residents in Texas and Oregon. The breach involves Conduent, a contractor for major health insurers, and was claimed by the Safepay ransomware group. The breach poses significant risks to personal and financial security, with moderate confidence in the assessment that the breach was primarily for financial gain.
2. Competing Hypotheses
- Hypothesis A: The breach was conducted by the Safepay ransomware group primarily for financial gain, as indicated by their claim of responsibility and the nature of the data accessed. However, there is no confirmed ransom demand, which introduces uncertainty about their motives.
- Hypothesis B: The breach may have been state-sponsored or conducted for espionage purposes, given the scale and sensitivity of the data involved. The lack of immediate misuse of data and the absence of a ransom demand could support this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the claim by the Safepay group and the typical financial motivations of ransomware attacks. Indicators such as a ransom demand or evidence of state involvement could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The breach was technically feasible for a ransomware group; Conduent’s security measures were insufficient; the data accessed is valuable for financial exploitation.
- Information Gaps: Details on whether a ransom was demanded, the specific vulnerabilities exploited, and any potential state involvement remain unknown.
- Bias & Deception Risks: Potential bias in attributing the breach solely to financial motives; reliance on claims from the Safepay group without independent verification.
4. Implications and Strategic Risks
This data breach could have cascading effects on national security, economic stability, and public trust in digital infrastructure. The exposure of sensitive information may lead to identity theft and financial fraud, impacting millions of individuals.
- Political / Geopolitical: Potential for increased scrutiny on data protection laws and international tensions if state involvement is suspected.
- Security / Counter-Terrorism: Increased risk of identity theft and fraud could strain law enforcement and cybersecurity resources.
- Cyber / Information Space: The breach highlights vulnerabilities in contractor-managed systems, necessitating improved cybersecurity protocols.
- Economic / Social: Financial losses from fraud and identity theft could impact consumer confidence and economic stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of affected systems, issue public guidance on protective measures, and initiate a comprehensive forensic investigation.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms, improve data protection regulations, and invest in cybersecurity infrastructure.
- Scenario Outlook:
- Best: Rapid containment and no misuse of data.
- Worst: Widespread identity theft and financial fraud.
- Most-Likely: Limited financial exploitation with increased regulatory scrutiny.
6. Key Individuals and Entities
- Conduent
- Safepay ransomware group
- Texas Attorney General Ken Paxton
- Not clearly identifiable from open sources in this snippet for other individuals.
7. Thematic Tags
cybersecurity, data breach, ransomware, identity theft, national security, financial fraud, regulatory response
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us