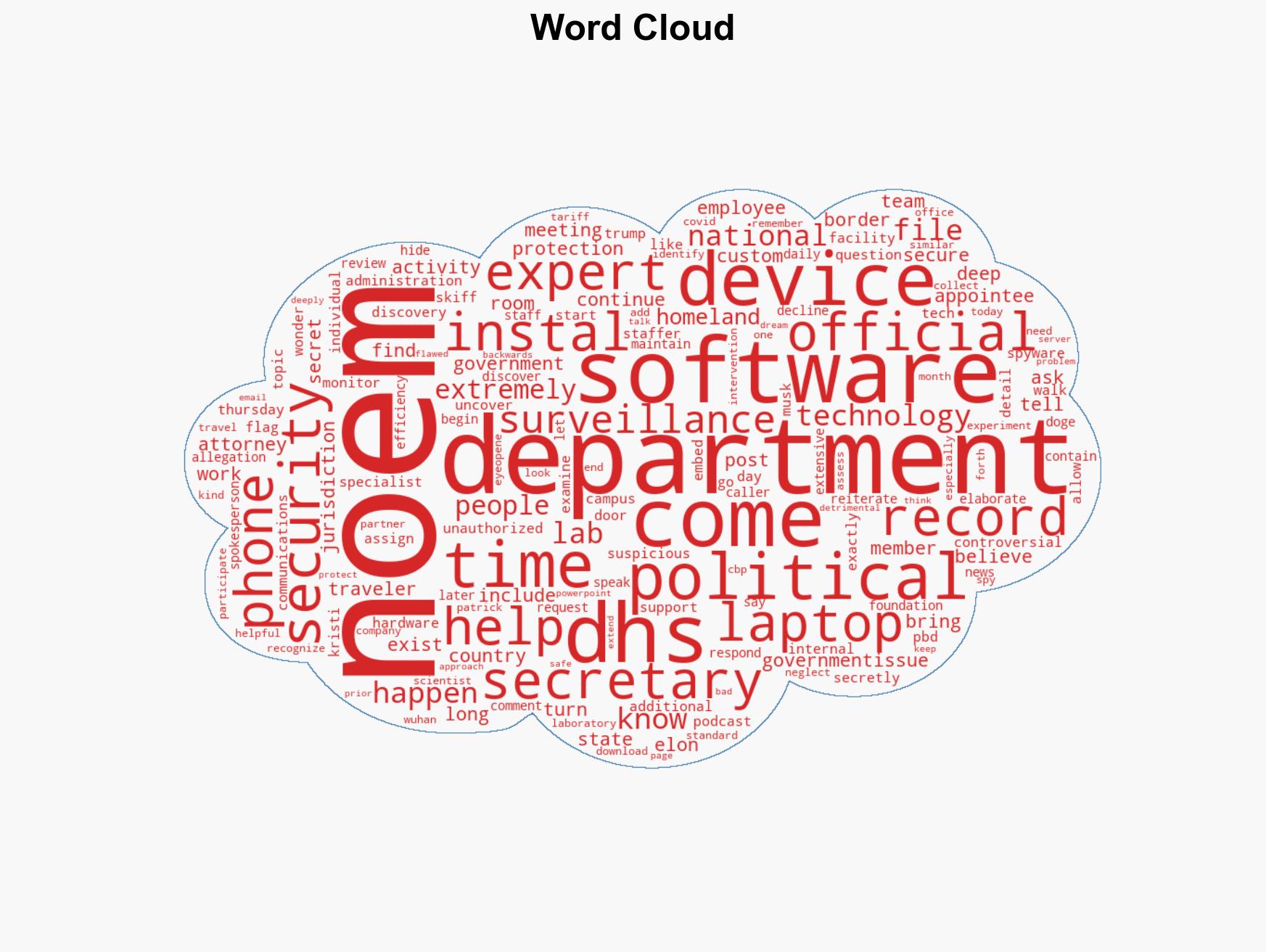
Noem Alleges DHS Installed Spyware on Devices of Trump Administration Officials
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Kristi Noem Accuses Own Department Of Secretly Bugging Trump Official Devices
1. BLUF (Bottom Line Up Front)
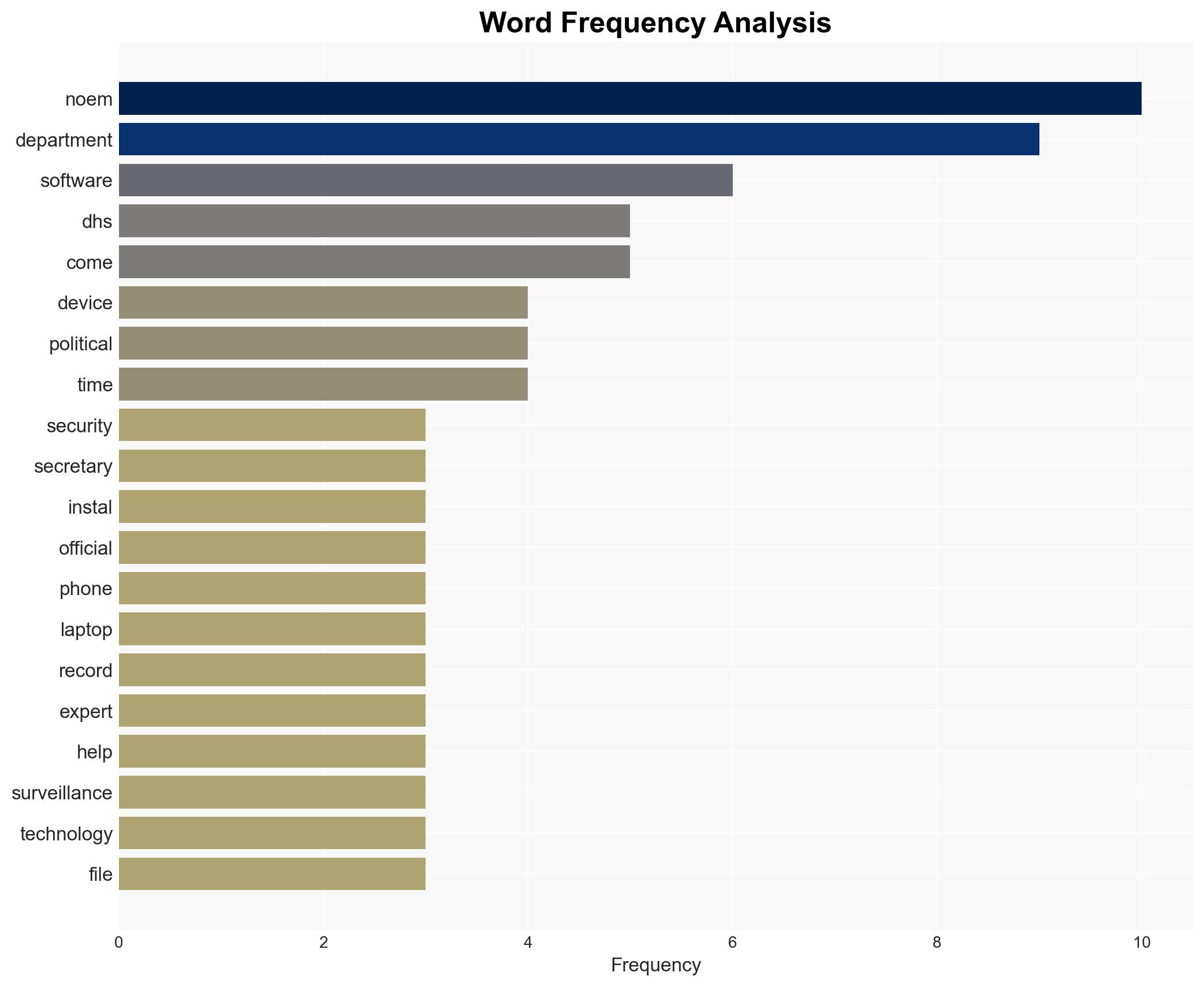
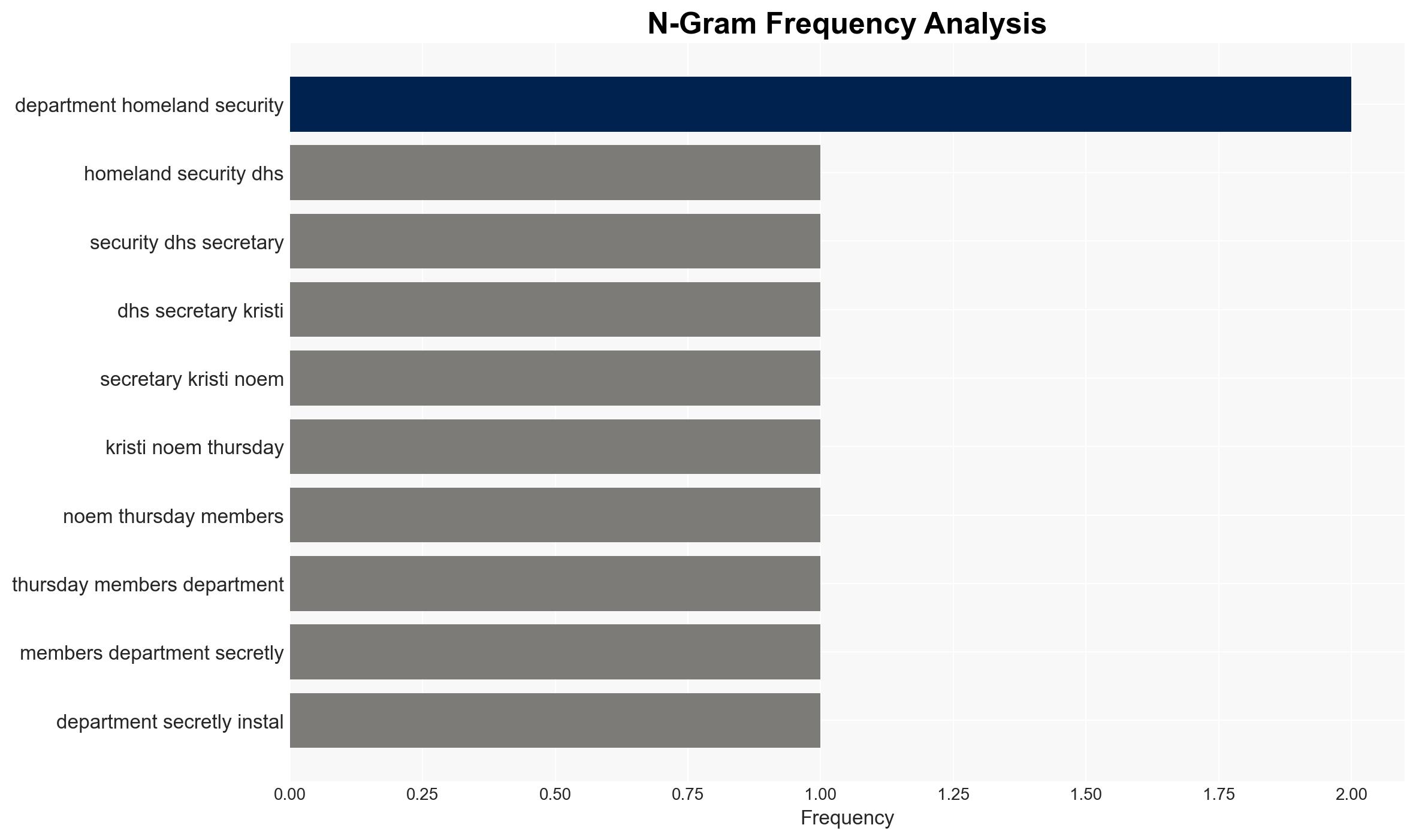
Kristi Noem has alleged unauthorized surveillance activities within her department, claiming spyware was installed on devices used by Trump administration officials. This situation raises significant concerns about internal security protocols and potential breaches of privacy. The most likely hypothesis is that there was unauthorized surveillance, possibly by rogue elements within the department. Overall confidence in this judgment is moderate, pending further investigation.
2. Competing Hypotheses
- Hypothesis A: Unauthorized surveillance was conducted by rogue elements within the Department of Homeland Security (DHS). This is supported by Noem’s claims and the involvement of external experts who identified suspicious software. However, the lack of corroborating evidence from other sources and the DHS’s refusal to elaborate introduce uncertainties.
- Hypothesis B: The allegations are exaggerated or misinterpreted, possibly due to internal misunderstandings or miscommunications. The DHS’s non-committal response and lack of external confirmation support this hypothesis, but it does not explain the alleged discovery of surveillance software.
- Assessment: Hypothesis A is currently better supported due to the specific details provided by Noem and the involvement of external experts. Key indicators that could shift this judgment include independent verification of the spyware’s existence and purpose, or credible denials from multiple DHS sources.
3. Key Assumptions and Red Flags
- Assumptions: Noem’s statements are based on credible findings; external experts conducted a thorough analysis; DHS’s refusal to comment is strategic rather than indicative of innocence.
- Information Gaps: Lack of independent verification of the spyware; absence of detailed technical analysis of the alleged surveillance software; unclear motives behind the alleged surveillance.
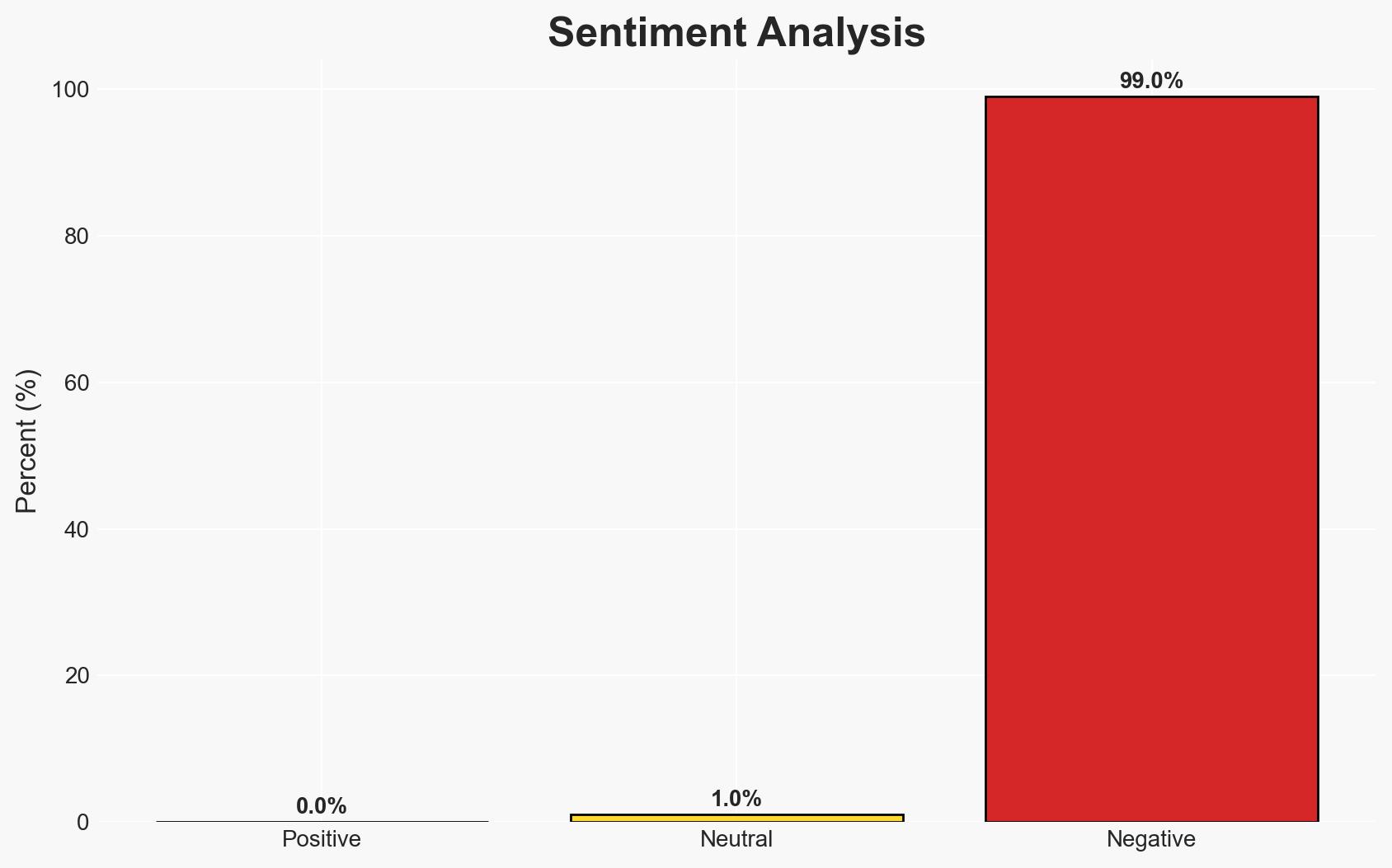
- Bias & Deception Risks: Potential bias in Noem’s statements due to political motivations; risk of deception if the allegations are part of an internal power struggle or misinformation campaign.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of internal security practices within government departments and potential political fallout if the allegations are substantiated.
- Political / Geopolitical: Potential erosion of trust in DHS leadership and internal divisions; possible political ramifications if linked to broader surveillance or privacy issues.
- Security / Counter-Terrorism: Compromised internal communications could affect operational security and counter-terrorism efforts.
- Cyber / Information Space: Highlights vulnerabilities in government-issued devices and the need for robust cybersecurity measures.
- Economic / Social: Public concern over privacy and government surveillance could lead to calls for policy reforms.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct an independent forensic audit of DHS devices; increase monitoring of internal communications; engage external cybersecurity experts for a comprehensive review.
- Medium-Term Posture (1–12 months): Develop and implement enhanced security protocols; foster inter-agency cooperation to prevent similar incidents; invest in cybersecurity training for staff.
- Scenario Outlook:
- Best: Allegations are disproven, leading to improved security measures (trigger: independent audit results).
- Worst: Substantiated claims lead to significant political fallout and restructuring within DHS (trigger: corroboration by multiple sources).
- Most-Likely: Partial confirmation of issues results in moderate reforms and increased oversight (trigger: mixed audit findings).
6. Key Individuals and Entities
- Kristi Noem, Department of Homeland Security (DHS), Customs and Border Protection (CBP), Elon Musk
7. Thematic Tags
cybersecurity, internal security, surveillance, cyber-espionage, government transparency, privacy concerns, DHS, political implications
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us