Ransomware Incidents Surge During Non-Business Hours, Driven by Identity-Related Attacks
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Ransomware activity peaks outside business hours
1. BLUF (Bottom Line Up Front)
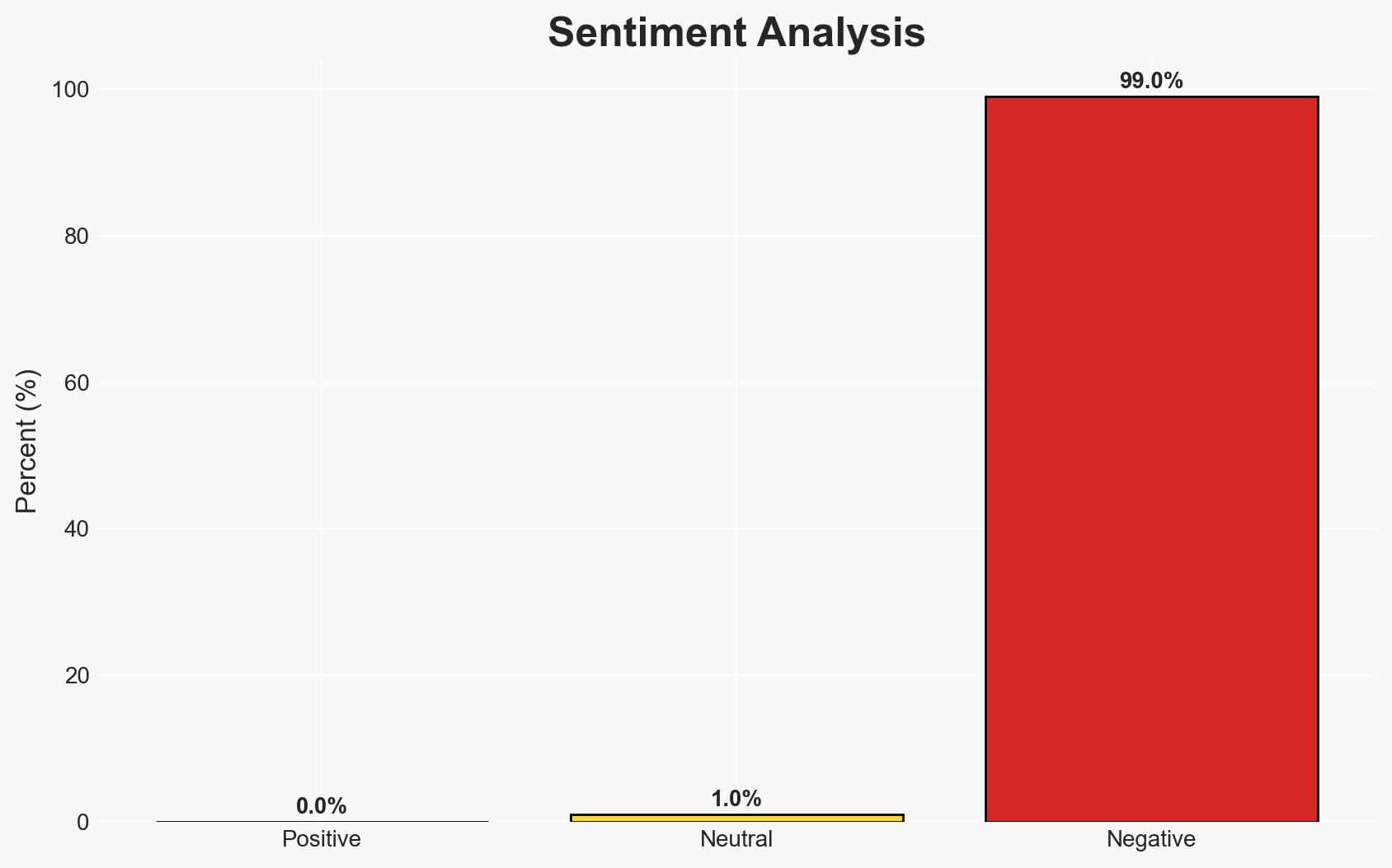
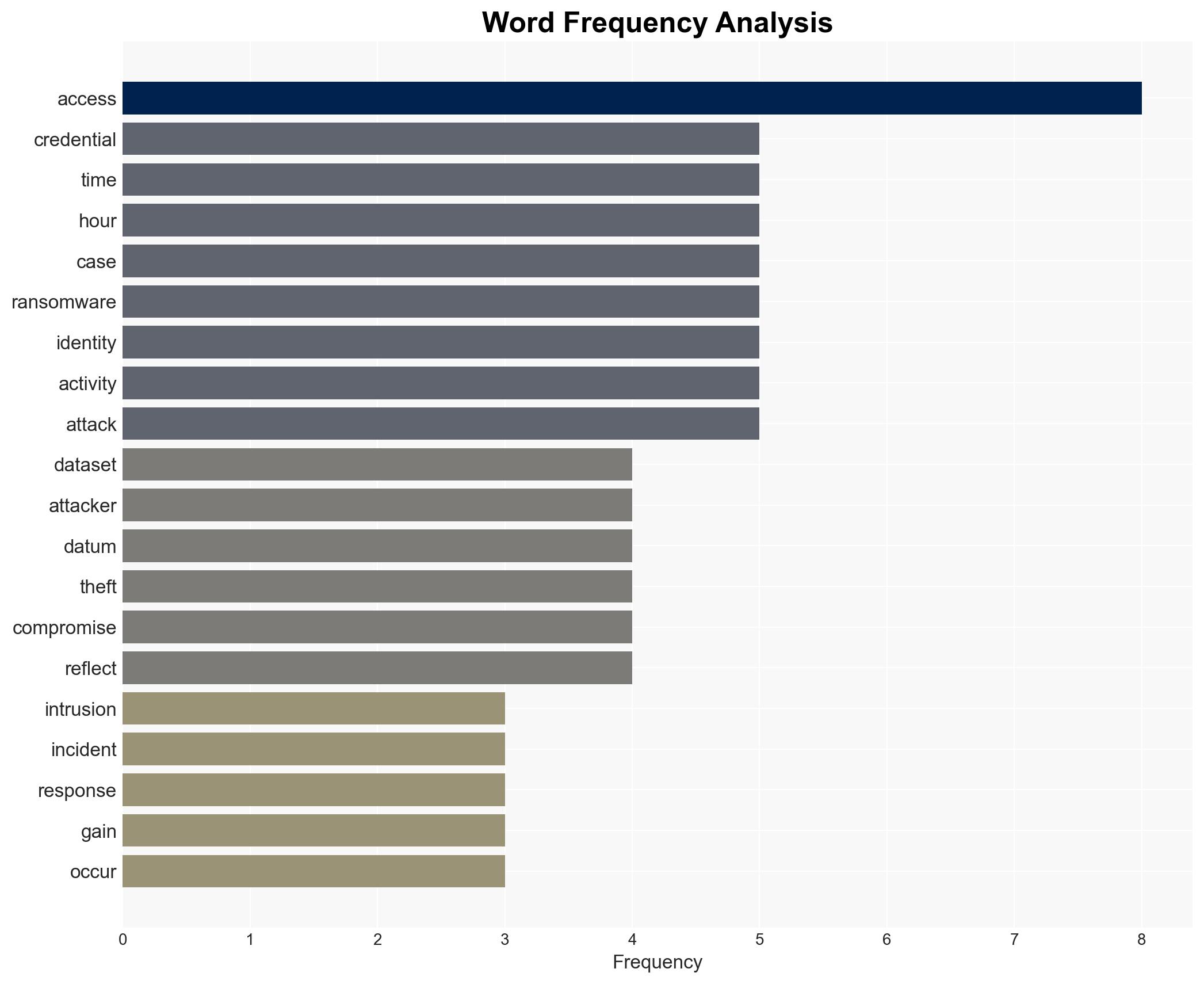
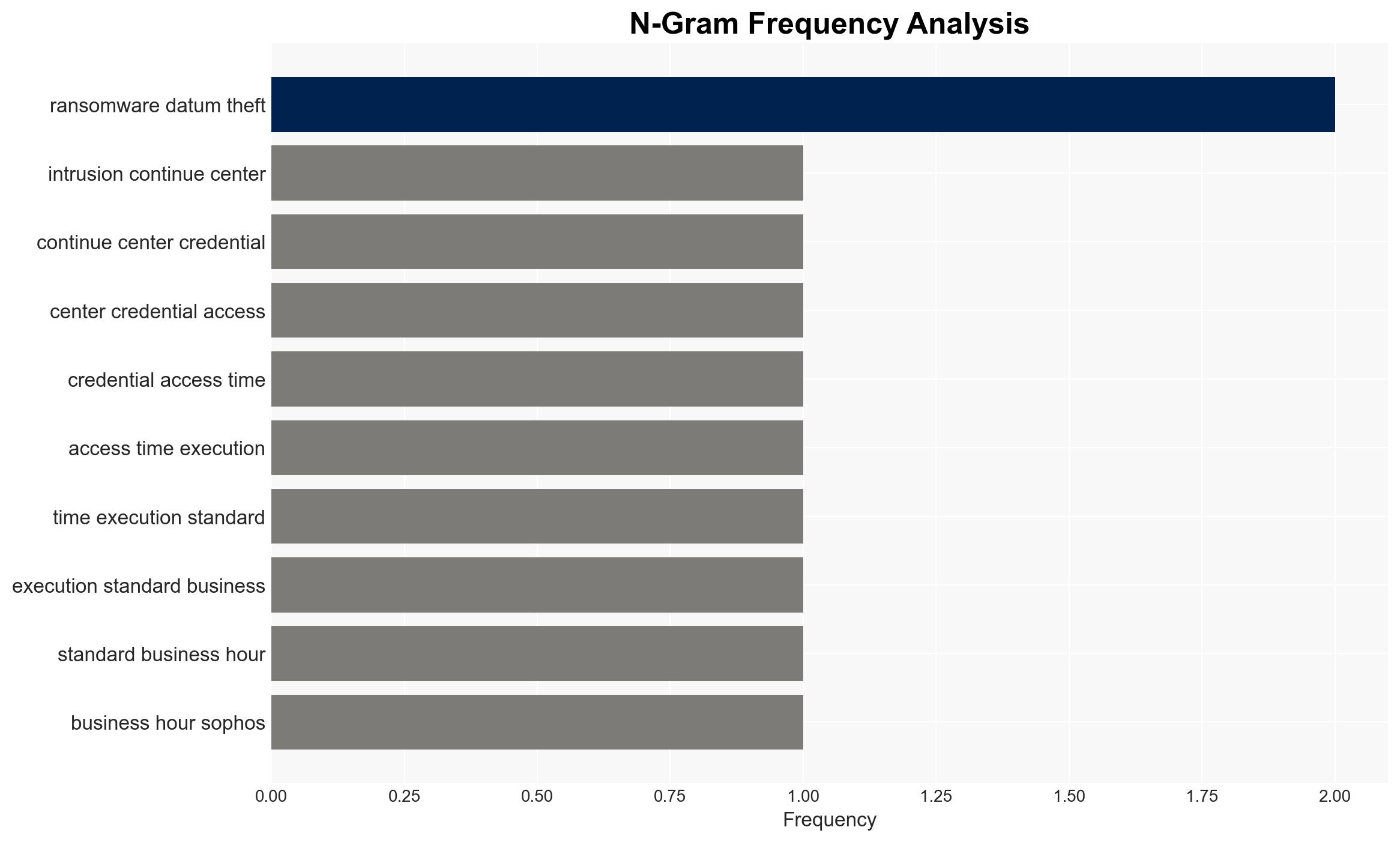
Ransomware activity is increasingly leveraging identity-related techniques, with attacks peaking outside business hours when organizational defenses are typically weaker. The most likely hypothesis is that attackers are exploiting credential misuse to gain rapid access to critical systems, such as Active Directory, within a compressed timeframe. This trend affects organizations globally, with moderate confidence in the assessment due to the comprehensive dataset analyzed.
2. Competing Hypotheses
- Hypothesis A: Attackers are primarily exploiting identity-related vulnerabilities to gain initial access, as evidenced by the 67% of cases involving credential misuse. The rapid time to reach Active Directory supports this hypothesis, but uncertainties include the potential underreporting of other access methods.
- Hypothesis B: Alternative entry points, such as vulnerability exploitation, are equally significant but underreported. The focus on identity-related techniques may be biased by the dataset’s collection methods or reporting practices.
- Assessment: Hypothesis A is currently better supported due to the dominance of identity-related techniques in the dataset and the rapid attack timelines observed. Key indicators that could shift this judgment include new data on the prevalence of non-identity-related access methods.
3. Key Assumptions and Red Flags
- Assumptions: Credential misuse is the primary method of initial access; attackers target off-hours to exploit reduced staffing; Active Directory is a critical target for lateral movement.
- Information Gaps: Detailed breakdown of non-identity-related access methods; specific industries or regions most affected by these trends.
- Bias & Deception Risks: Potential bias in data collection favoring identity-related incidents; risk of attackers using deception to mask true entry methods.
4. Implications and Strategic Risks
This development could lead to increased sophistication in ransomware tactics, with attackers refining their timing and methods to exploit organizational vulnerabilities. Over time, this may drive changes in cybersecurity strategies and policies.
- Political / Geopolitical: Potential for increased international cooperation on cybersecurity standards and incident response.
- Security / Counter-Terrorism: Heightened threat environment requiring enhanced monitoring and rapid response capabilities.
- Cyber / Information Space: Increased focus on identity protection and authentication system hardening; potential for new cyber defense technologies.
- Economic / Social: Economic impact on affected organizations; potential for increased cybersecurity investments and workforce demands.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring during off-hours; conduct audits of identity management systems; increase staff awareness of phishing and credential threats.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in advanced authentication technologies; implement continuous security training programs.
- Scenario Outlook: Best: Improved defenses reduce attack success rates; Worst: Increased attack sophistication overwhelms defenses; Most-Likely: Continued adaptation by both attackers and defenders, with incremental improvements in security posture.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
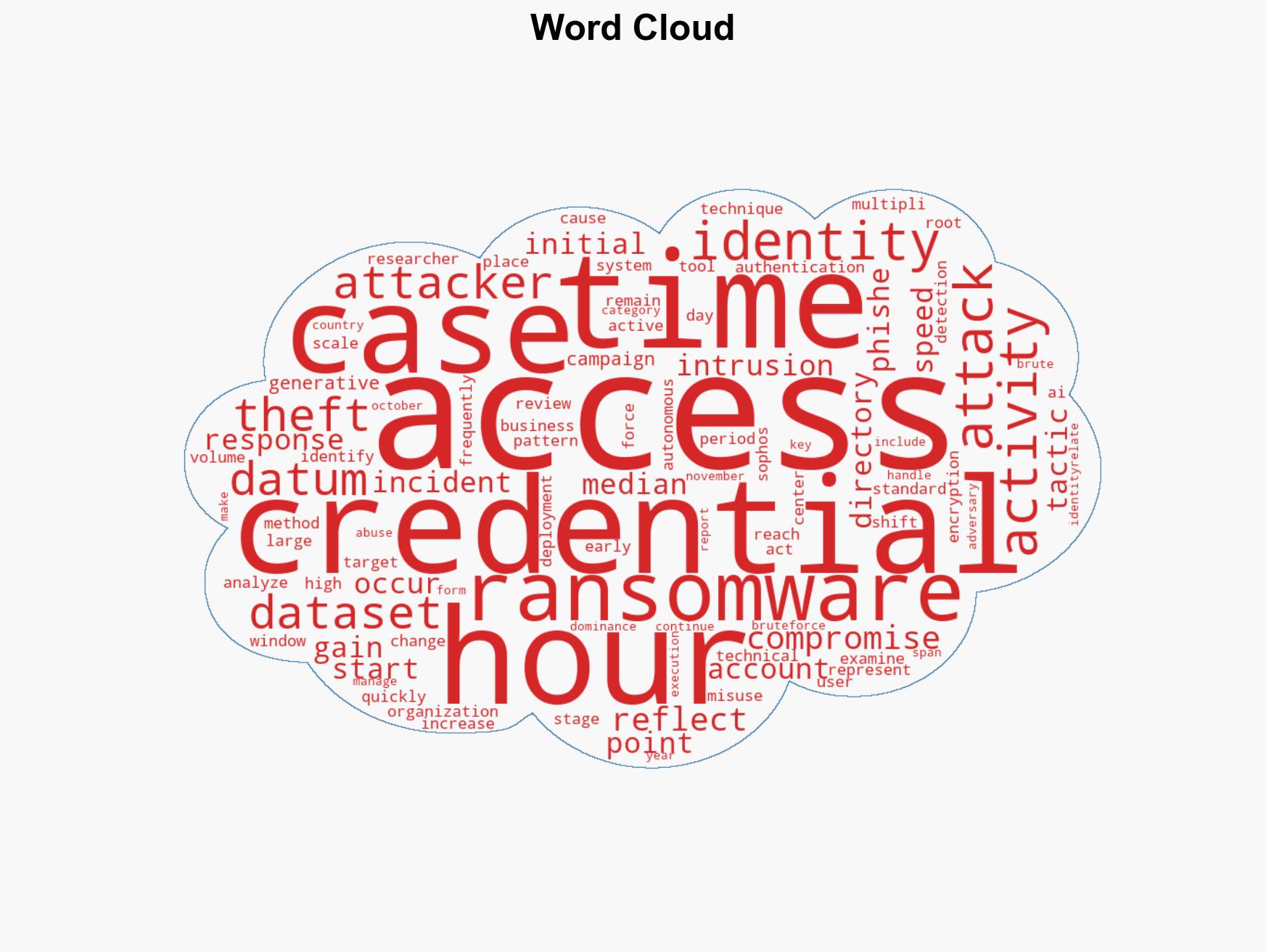
cybersecurity, ransomware, identity theft, cyber defense, credential misuse, Active Directory, cybersecurity strategy, off-hours attacks
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us