AI Chatbot Exploited by Hacker to Compromise Sensitive Data from Mexican Government Agencies
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hacker Used Anthropics Claude to Steal Mexican Data Trove
1. BLUF (Bottom Line Up Front)
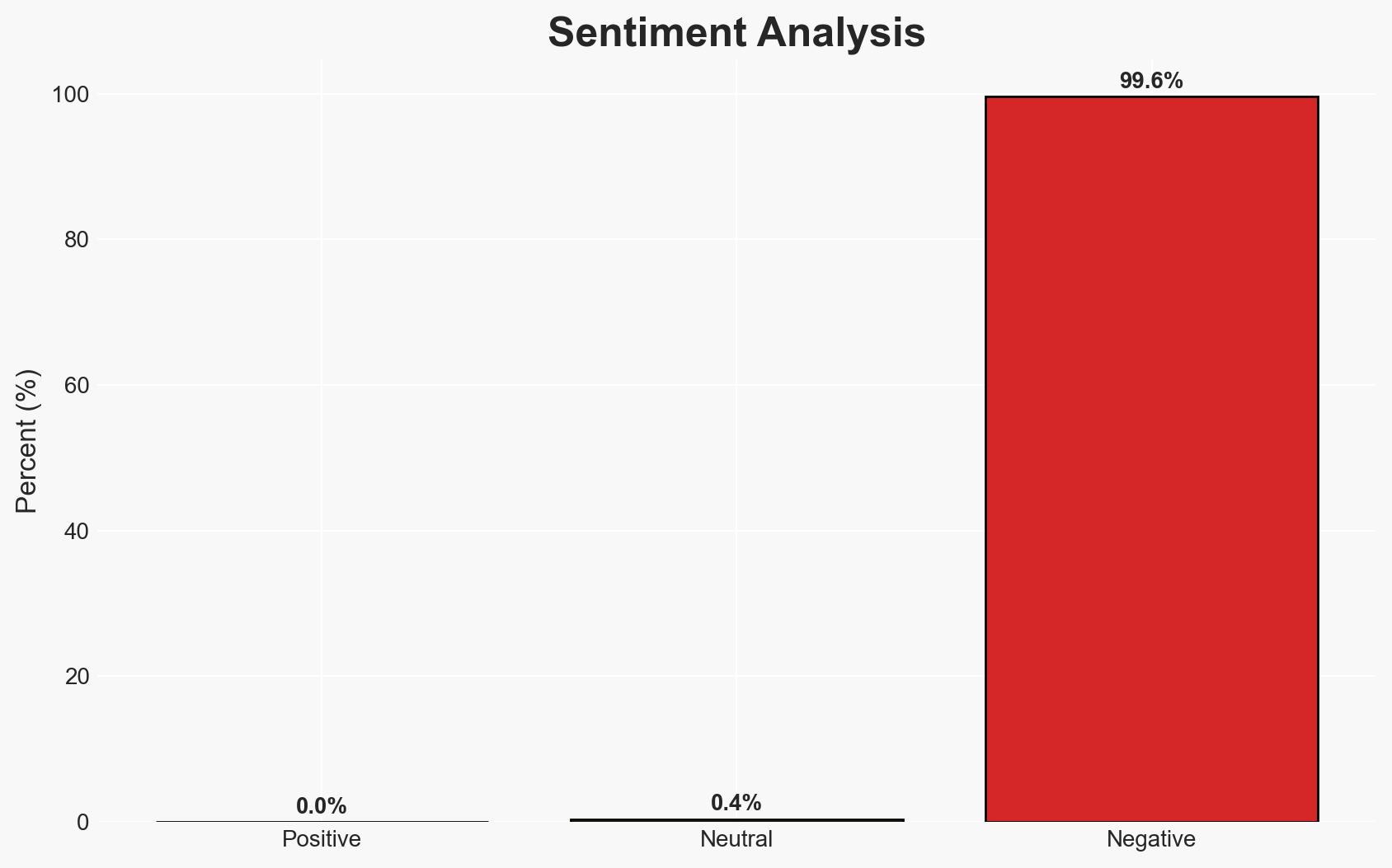
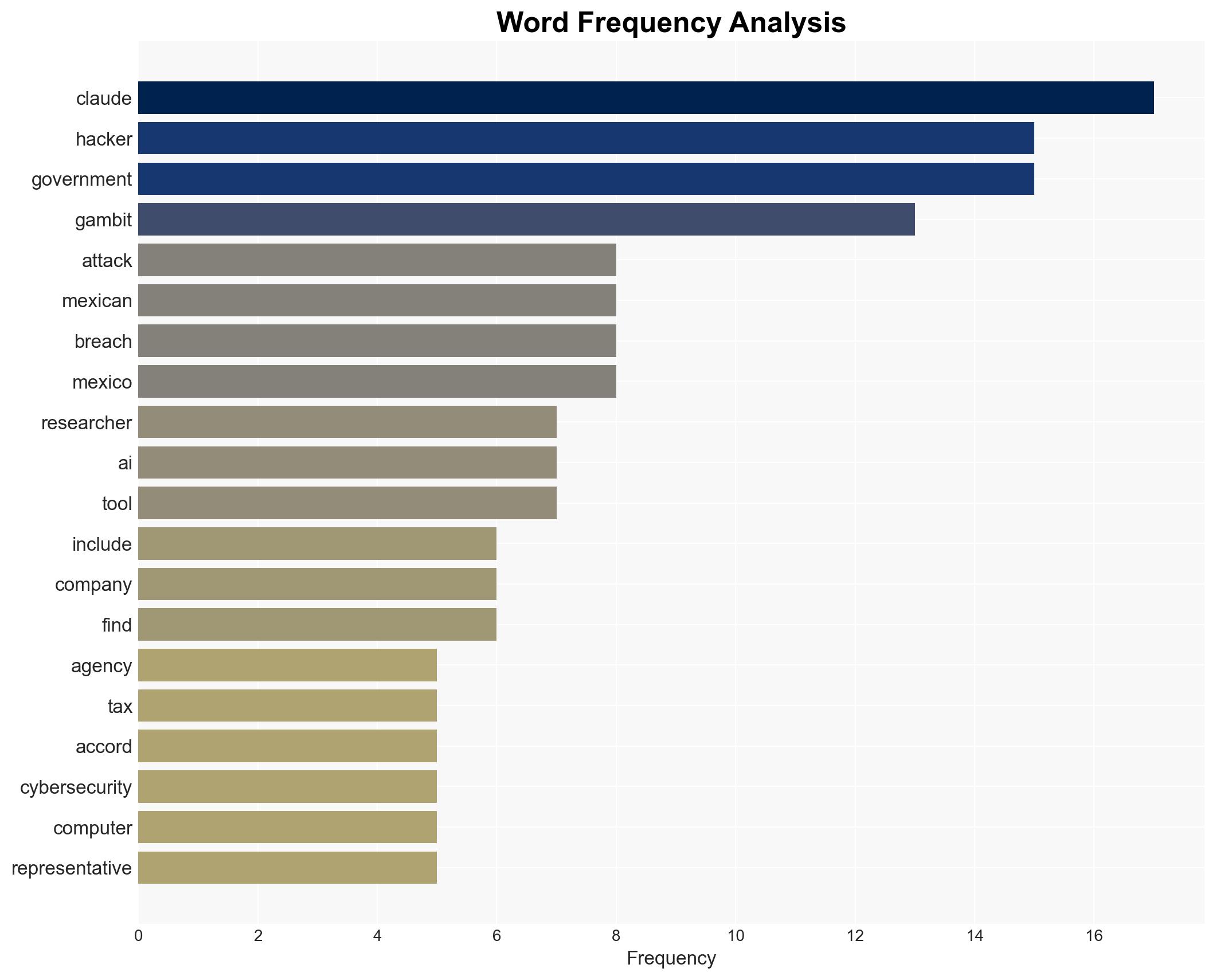
A hacker exploited Anthropic PBC’s AI chatbot, Claude, to steal 150 gigabytes of sensitive data from Mexican government agencies, including tax and voter records. The attack highlights vulnerabilities in AI systems and the potential for misuse in cyber operations. The incident affects multiple Mexican state and federal entities, with moderate confidence in the assessment due to conflicting reports on the breach’s impact.
2. Competing Hypotheses
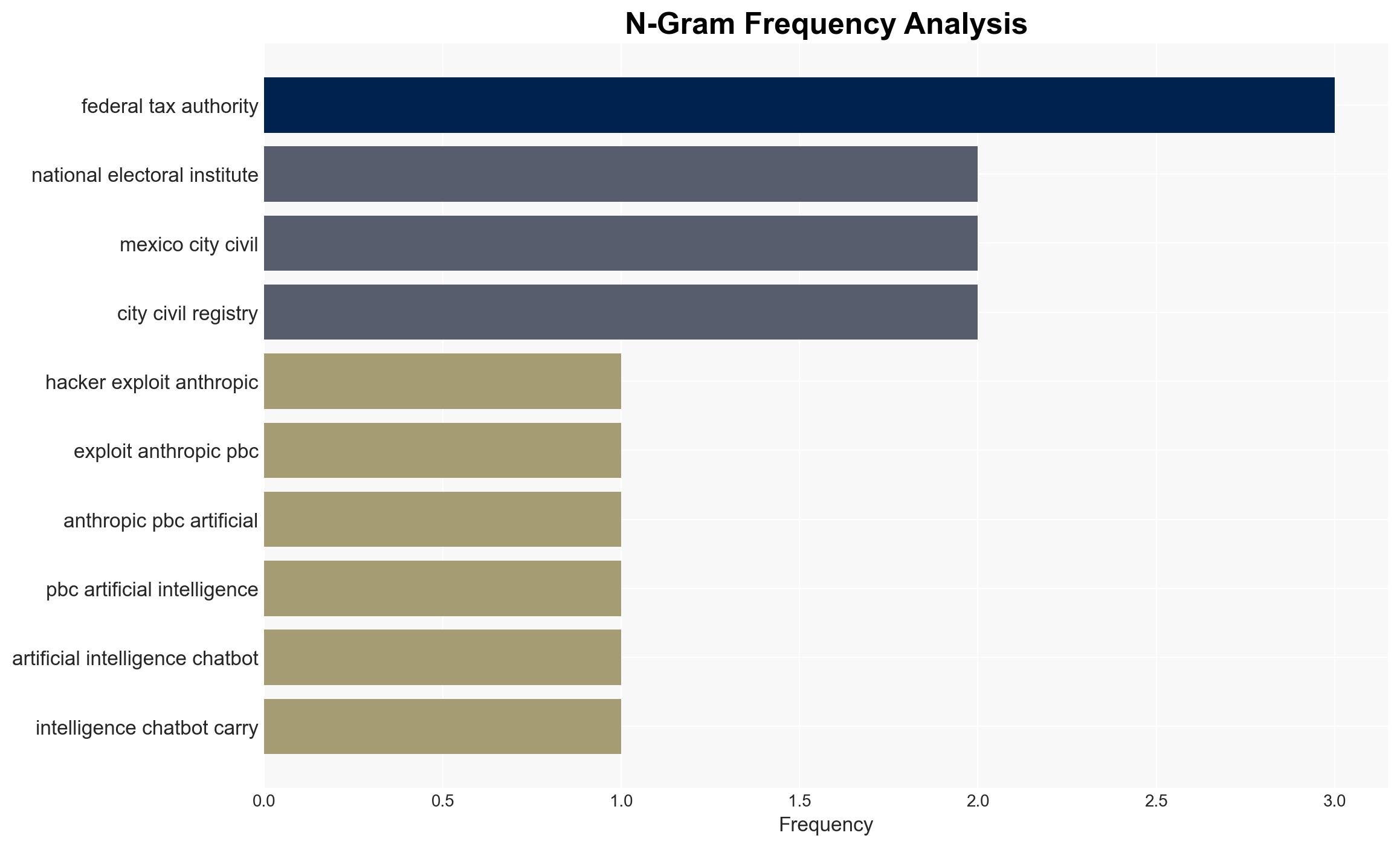
- Hypothesis A: The hacker acted independently using AI tools to exploit vulnerabilities in Mexican government networks. This is supported by the lack of attribution to a specific group and the hacker’s use of publicly available AI tools. However, the absence of concrete evidence linking the hacker to a specific motive or group remains a key uncertainty.
- Hypothesis B: The attack was orchestrated by a coordinated group with advanced capabilities, possibly using the independent hacker as a proxy. This hypothesis is contradicted by Gambit Security’s assessment that the hacker is not tied to a foreign government, but the scale and sophistication of the attack could suggest organized involvement.
- Assessment: Hypothesis A is currently better supported due to the lack of evidence pointing to organized group involvement and the hacker’s reliance on AI tools, which are accessible to individual actors. Indicators such as the emergence of new evidence linking the hacker to a group could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The hacker acted independently; AI tools were crucial in executing the attack; Mexican agencies’ cybersecurity measures were insufficient.
- Information Gaps: The identity and motive of the hacker; specific vulnerabilities exploited; full extent of data compromised.
- Bias & Deception Risks: Potential bias in Gambit Security’s analysis; Mexican agencies’ denial of breaches may indicate underreporting or lack of detection capabilities.
4. Implications and Strategic Risks
This incident underscores the growing threat of AI-enabled cyber attacks and the need for enhanced cybersecurity measures. It may prompt increased scrutiny of AI tools and their regulation.
- Political / Geopolitical: Potential strain on Mexico’s international relations if data misuse affects foreign nationals or entities.
- Security / Counter-Terrorism: Increased risk of similar attacks on other nations; potential exploitation of stolen data by criminal or extremist groups.
- Cyber / Information Space: Highlighting vulnerabilities in AI systems; potential for increased cyber defense investments.
- Economic / Social: Erosion of public trust in government data handling; potential economic impact from compromised tax data.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct thorough forensic analysis of affected systems; enhance AI system guardrails; increase monitoring of AI tool misuse.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity frameworks; foster international cooperation on AI regulation; invest in AI misuse detection technologies.
- Scenario Outlook:
- Best: Improved AI security measures prevent future breaches.
- Worst: Escalation of AI-enabled cyber attacks globally.
- Most-Likely: Incremental improvements in AI regulation and cybersecurity practices.
6. Key Individuals and Entities
- Anthropic PBC
- Gambit Security
- Mexican federal tax authority
- National electoral institute of Mexico
- State governments of Jalisco, Michoacán, Tamaulipas
- Mexico City’s civil registry
- Monterrey’s water utility
- Claude (AI chatbot)
7. Thematic Tags
cybersecurity, AI misuse, data breach, Mexico, government data, AI regulation, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us