Cyberattackers Accelerate Tactics Amid Advancements in Enterprise Security Measures
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: News brief Attackers gain speed in cybersecurity race
1. BLUF (Bottom Line Up Front)
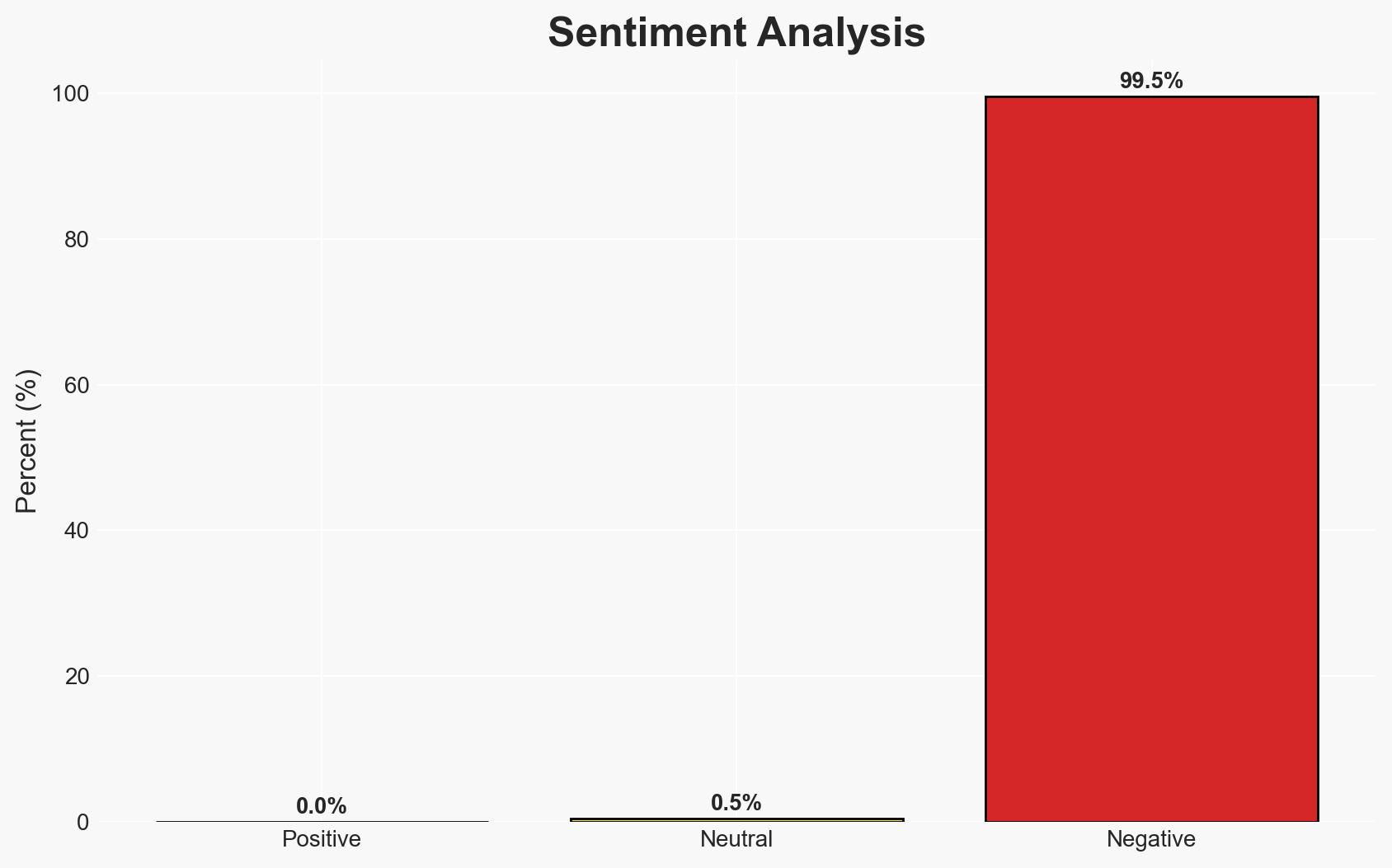
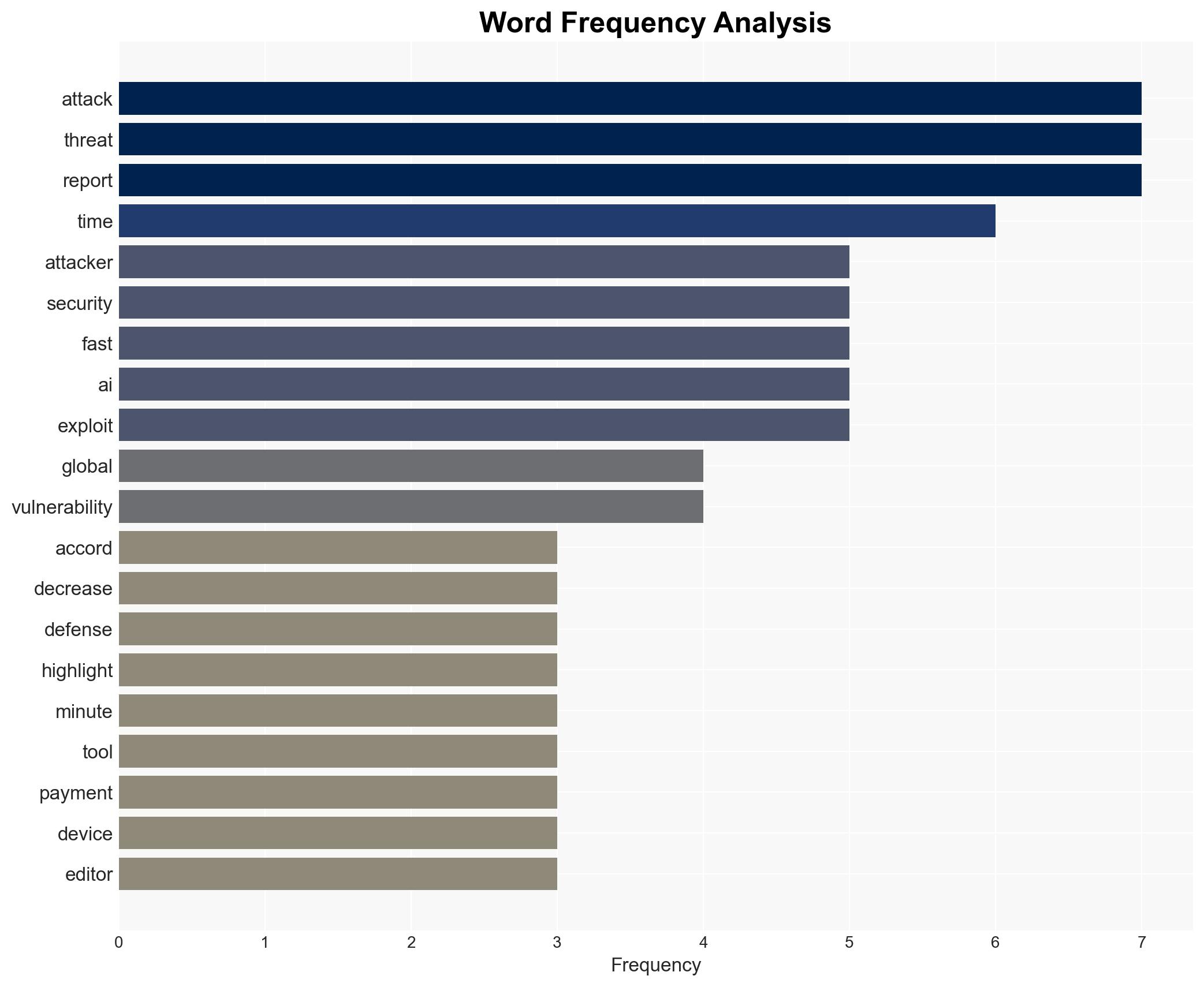
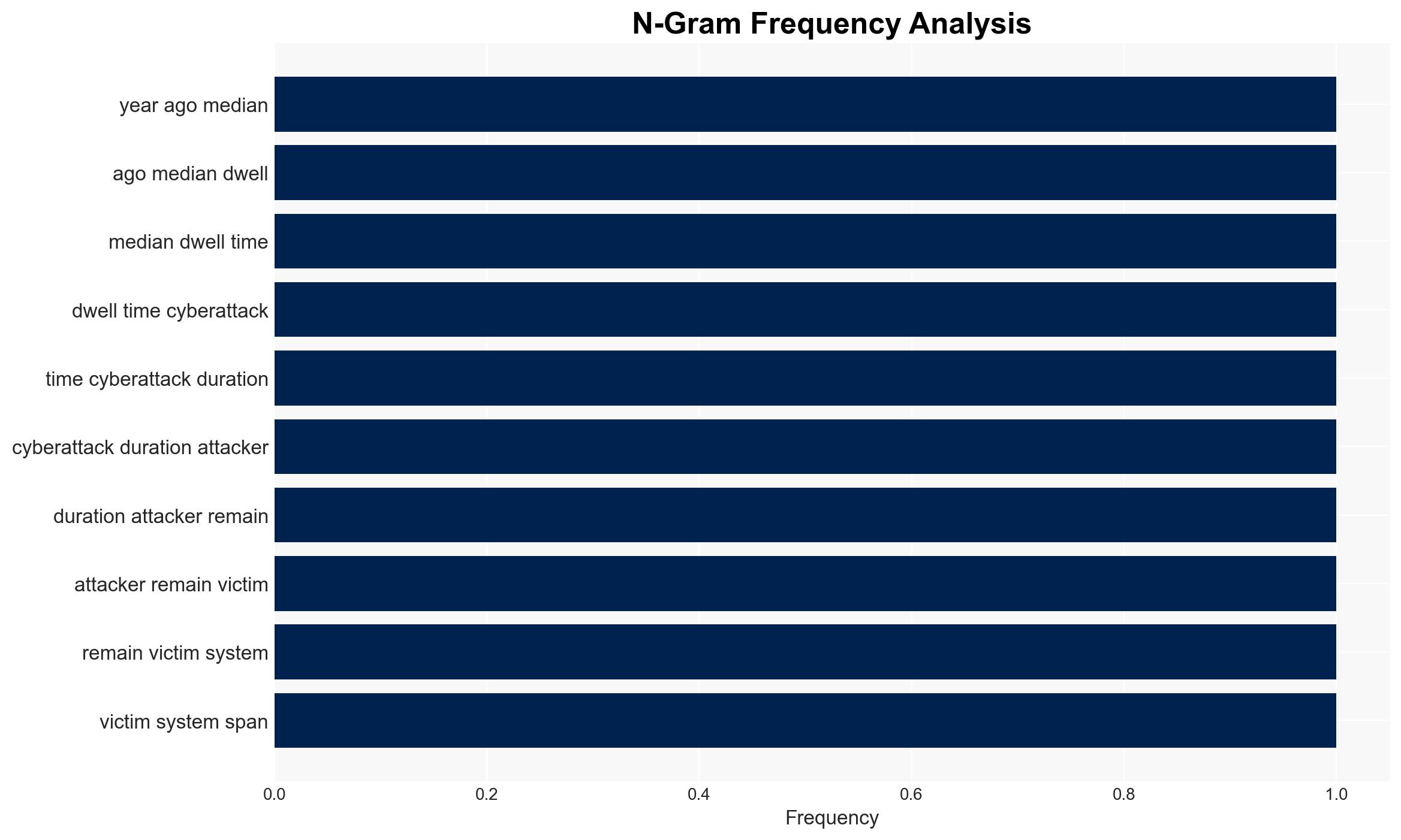
The rapid advancement of AI technologies is significantly reducing the time attackers spend within compromised systems, posing an increasing threat to cybersecurity. Organizations must enhance their defensive capabilities to keep pace with these developments. The most likely hypothesis is that AI-driven tools will continue to accelerate attack timelines, necessitating urgent improvements in cybersecurity strategies. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The reduction in cyberattack dwell time is primarily due to advancements in AI technologies, which enable faster lateral movement and data exfiltration. Supporting evidence includes reports of AI tools like BoaLoader and significant decreases in attack timelines. However, uncertainties remain about the full extent of AI’s role versus other factors.
- Hypothesis B: The decrease in dwell time is mainly due to improved enterprise security measures and quicker detection of certain attack types, such as ransomware. This is supported by the strengthening of security monitoring and alerting capabilities. Contradicting evidence includes ongoing challenges like under-skilled security teams and sophisticated APT tactics.
- Assessment: Hypothesis A is currently better supported due to the consistent reporting of AI’s impact on attack speed across multiple sources. Key indicators that could shift this judgment include new evidence of significant improvements in enterprise security measures or a slowdown in AI tool development.
3. Key Assumptions and Red Flags
- Assumptions: AI technologies will continue to evolve and be integrated into cyberattack strategies; enterprise security capabilities will not outpace attacker innovations; current reports accurately reflect AI’s impact on cyber operations.
- Information Gaps: Detailed data on the specific AI tools used in recent attacks and their operational mechanisms; comprehensive analysis of enterprise security improvements over the same period.
- Bias & Deception Risks: Potential bias in reports emphasizing AI’s role due to industry focus on emerging technologies; risk of deception in attacker tactics to mask true capabilities or intentions.
4. Implications and Strategic Risks
The acceleration of cyberattack timelines due to AI advancements could lead to significant shifts in the cybersecurity landscape, affecting various domains. Organizations may struggle to keep pace, increasing vulnerability to breaches.
- Political / Geopolitical: Potential for increased state-sponsored cyber operations leveraging AI, leading to geopolitical tensions.
- Security / Counter-Terrorism: Enhanced capabilities for cybercriminals and terrorist groups to conduct rapid, impactful attacks.
- Cyber / Information Space: Greater challenges in defending against AI-driven attacks, requiring advanced detection and response strategies.
- Economic / Social: Increased costs for businesses to upgrade cybersecurity measures; potential for widespread economic disruption from successful attacks.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI tool developments; conduct a rapid assessment of current cybersecurity capabilities; prioritize training for security teams on AI-driven threats.
- Medium-Term Posture (1–12 months): Invest in AI-based defensive technologies; establish partnerships for threat intelligence sharing; develop comprehensive incident response plans.
- Scenario Outlook:
- Best: Organizations successfully integrate AI into defense strategies, reducing attack impact.
- Worst: AI-driven attacks outpace defensive measures, leading to widespread breaches.
- Most-Likely: Continued arms race between attackers and defenders, with incremental improvements on both sides.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
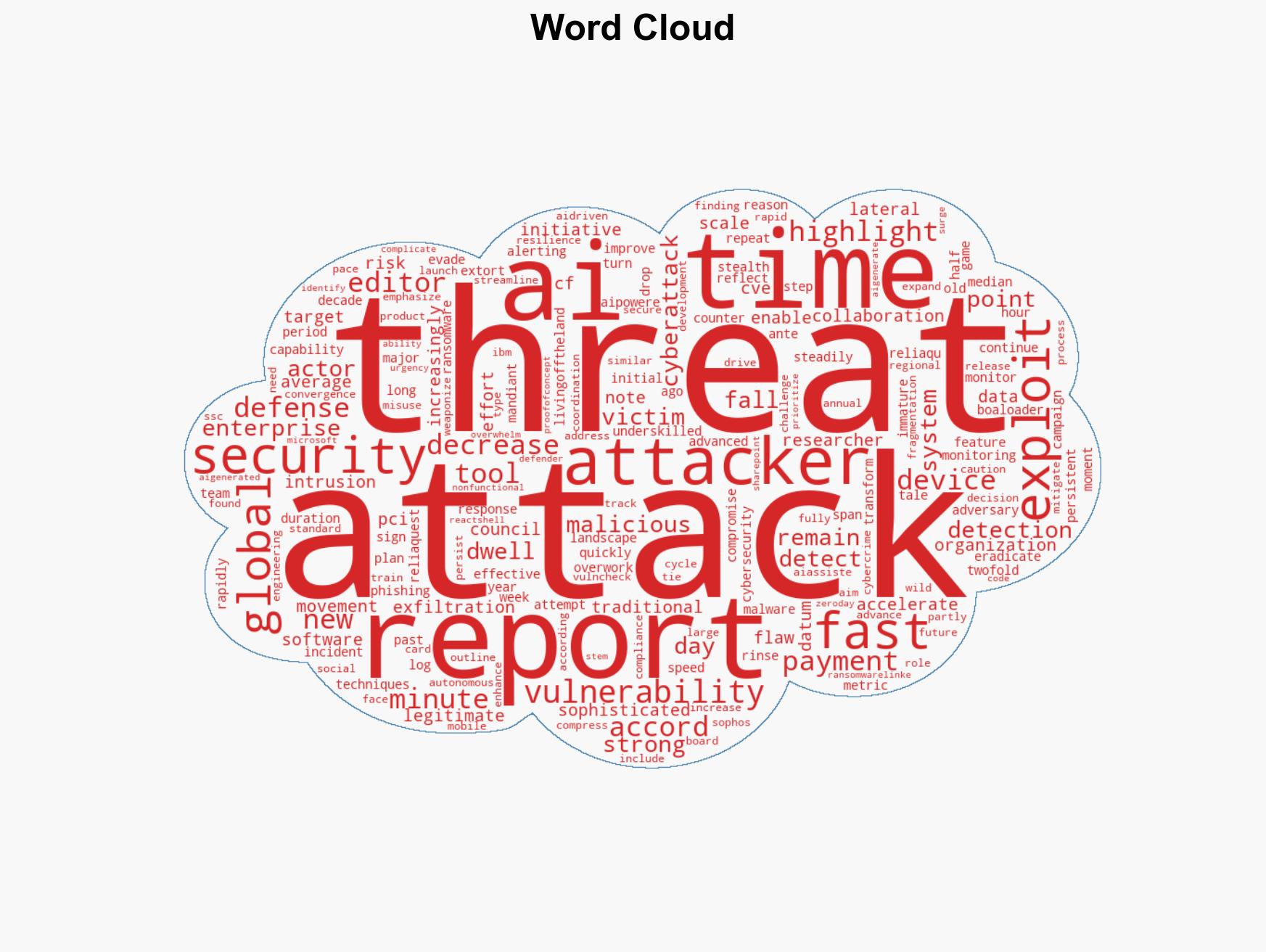
cybersecurity, AI-driven attacks, enterprise defense, cyber threat intelligence, incident response, geopolitical cyber risks, economic impact
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us