New Android RAT malware exploits security vulnerabilities across major brands, priced below $300.
Published on: 2026-02-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
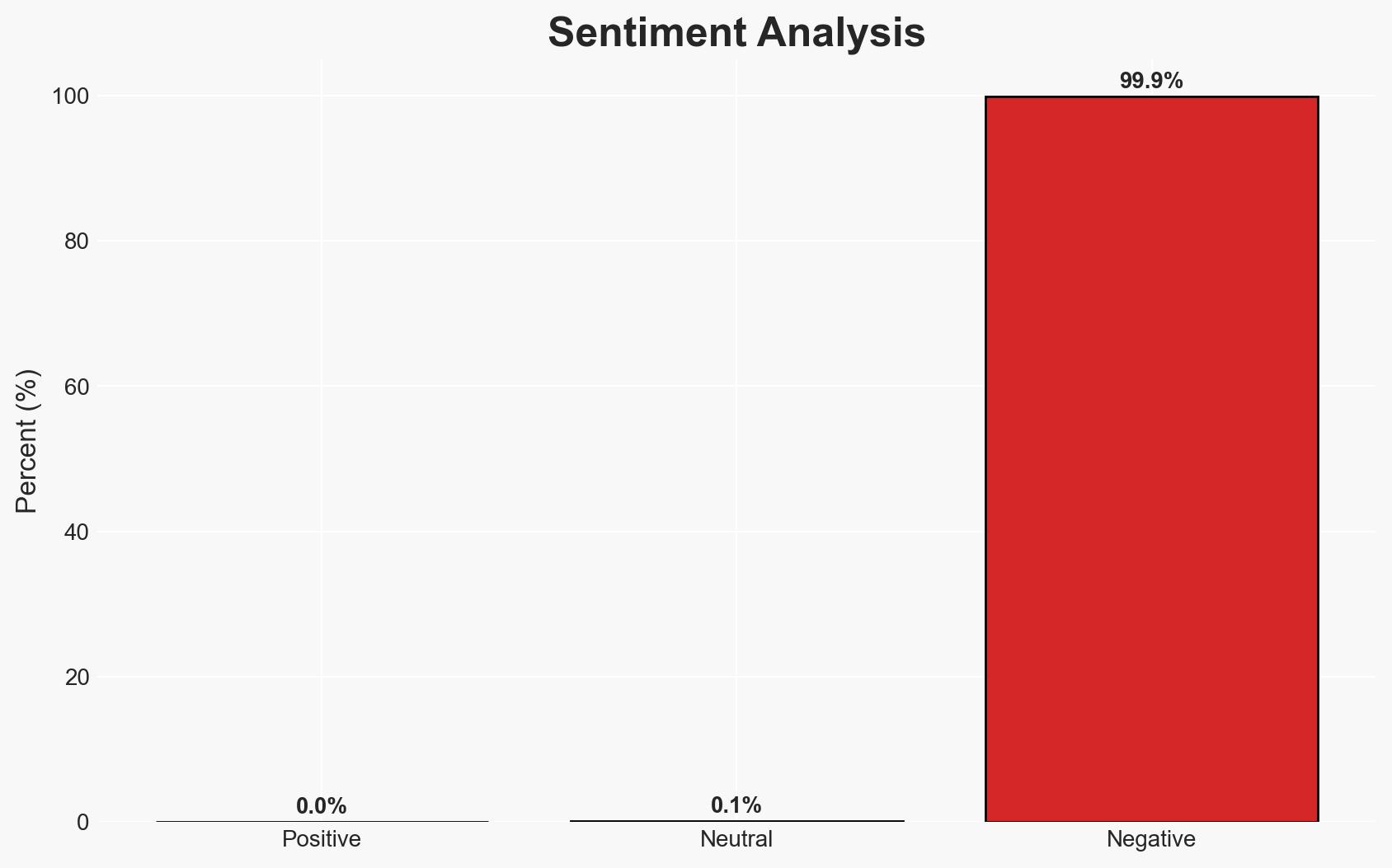
Intelligence Report: I smell a RAT new Android malware can hack every top phone maker’s security and costs less than a second-hand iPhone
1. BLUF (Bottom Line Up Front)
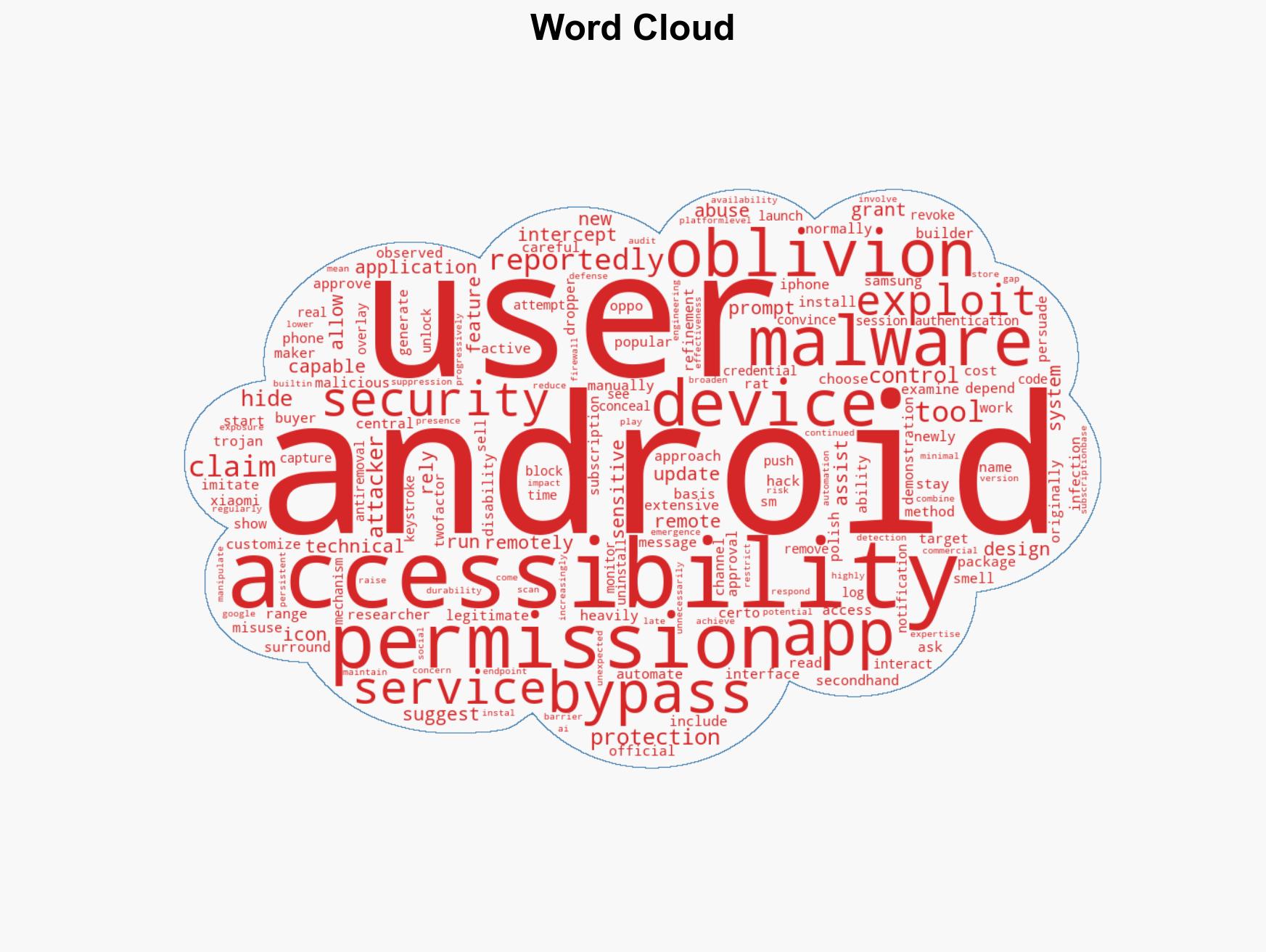
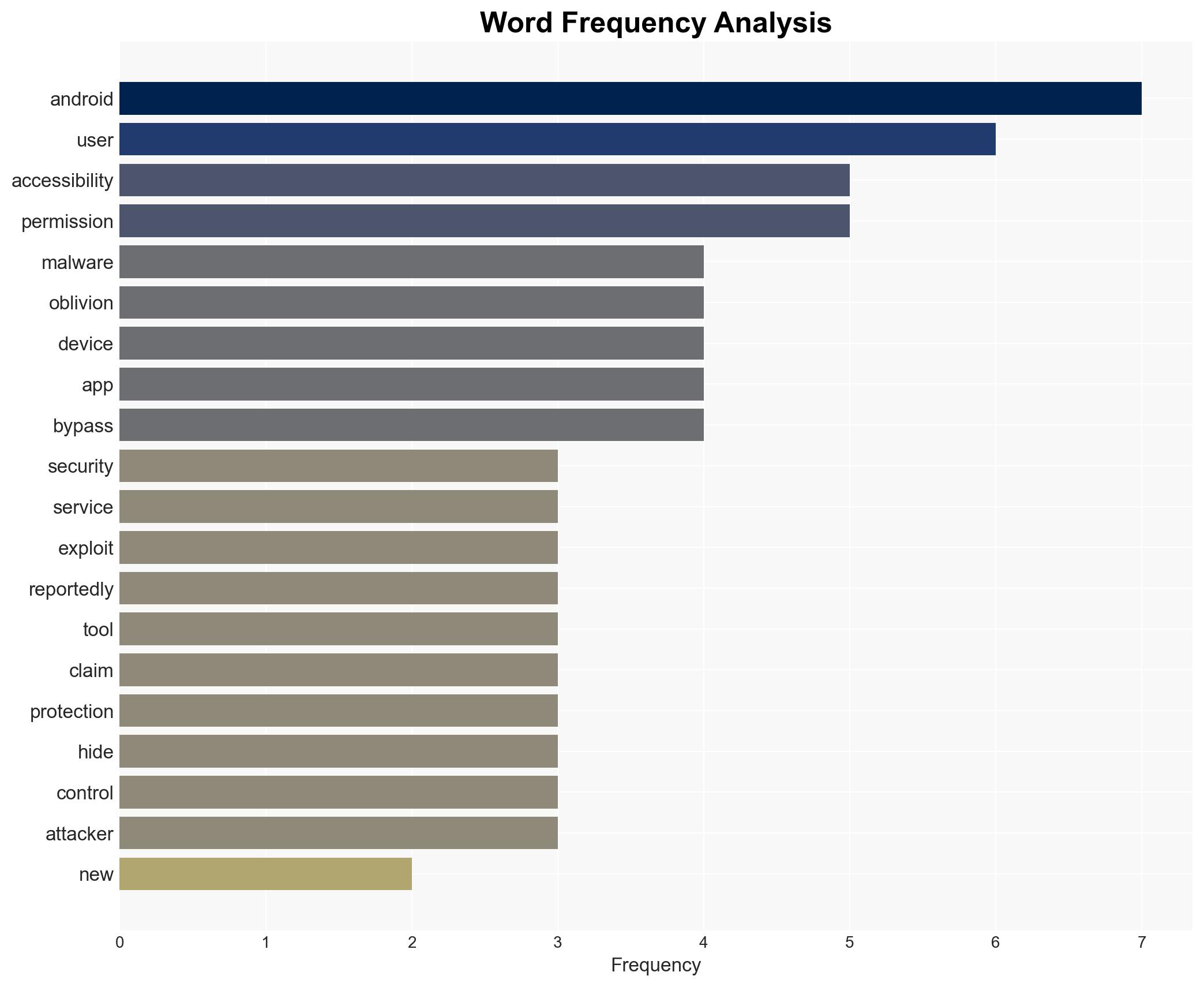
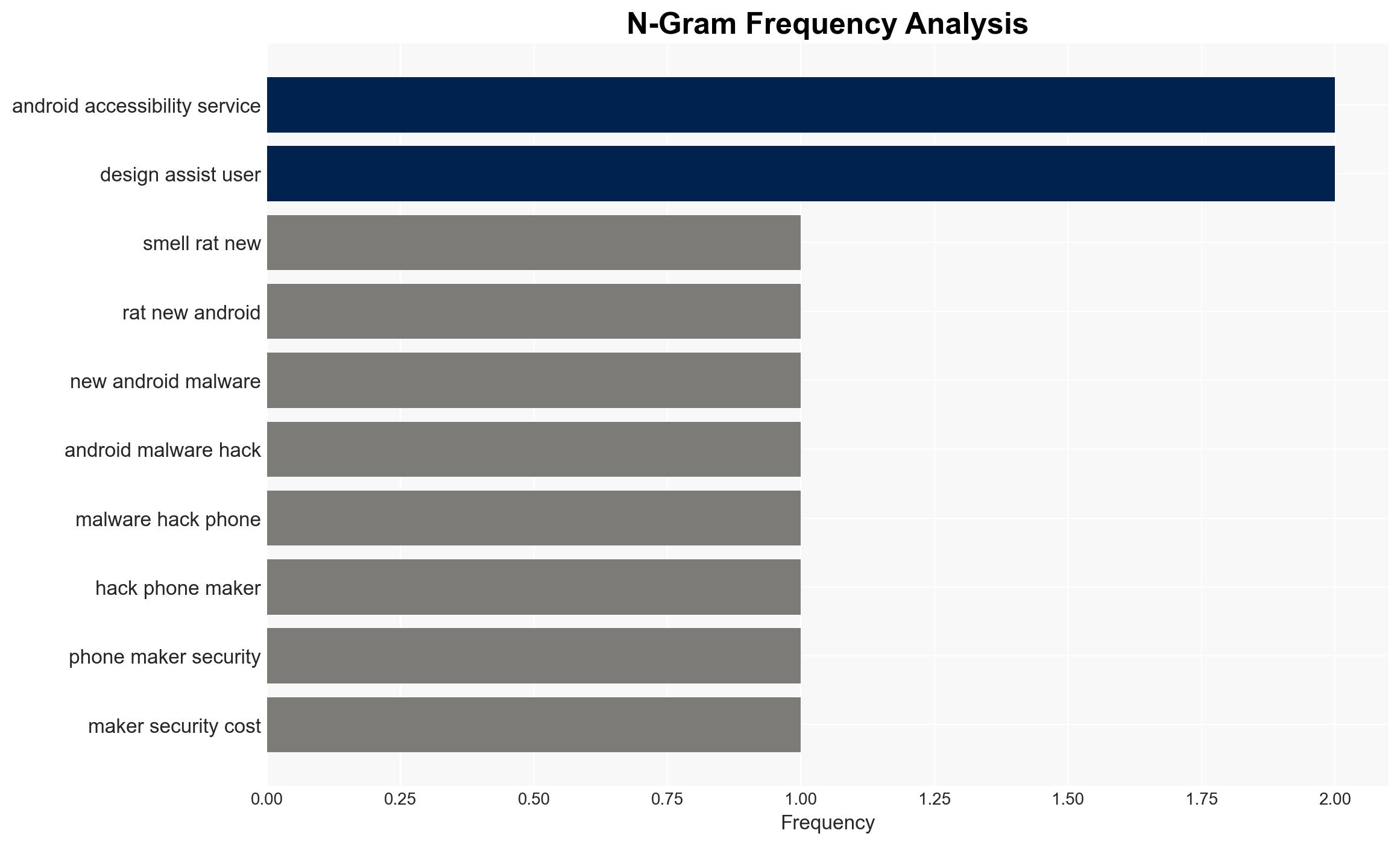
The emergence of the Oblivion Android Remote Access Trojan (RAT) poses a significant threat to mobile security across major Android devices, exploiting the Accessibility Service to bypass security measures. The malware’s subscription-based model makes it accessible to a wide range of potential attackers, increasing the risk of widespread exploitation. This assessment is made with moderate confidence due to the limited information on the malware’s full capabilities and distribution.
2. Competing Hypotheses
- Hypothesis A: Oblivion is primarily a tool for cybercriminals seeking financial gain through data theft and unauthorized access. Supporting evidence includes its ability to intercept SMS messages and two-factor authentication codes, which are often used in financial fraud. However, the extent of its deployment and specific targets remain unclear.
- Hypothesis B: Oblivion could be a state-sponsored tool aimed at espionage and surveillance, leveraging its capabilities to monitor communications and gather intelligence. This hypothesis is less supported due to the commercial availability and relatively low cost of the malware, which suggests broader criminal use rather than exclusive state control.
- Assessment: Hypothesis A is currently better supported due to the malware’s commercial nature and features that align with typical cybercriminal activities. Indicators that could shift this judgment include evidence of targeted attacks on specific high-value entities or geopolitical adversaries.
3. Key Assumptions and Red Flags
- Assumptions: The malware’s capabilities as described are accurate; the subscription model will lead to widespread use; Android’s security measures are insufficient to counteract this threat.
- Information Gaps: Detailed information on the malware’s distribution channels, the identity of its developers, and specific victim profiles.
- Bias & Deception Risks: Potential bias in reporting from security researchers with vested interests; possible exaggeration of capabilities by sellers to increase sales.
4. Implications and Strategic Risks
The proliferation of Oblivion could lead to increased incidents of data breaches and financial fraud, undermining trust in mobile platforms. Over time, this could pressure manufacturers and developers to enhance security measures, potentially leading to regulatory changes.
- Political / Geopolitical: Potential for increased tensions if state actors are implicated in using the malware for espionage.
- Security / Counter-Terrorism: Heightened threat landscape as more actors gain access to advanced cyber tools.
- Cyber / Information Space: Increased demand for cybersecurity solutions and potential shifts in user behavior towards more secure platforms.
- Economic / Social: Potential economic impact on companies facing breaches and on consumers losing trust in mobile transactions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of app stores and third-party app sources; increase public awareness about the risks of installing apps from untrusted sources.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve Android security features; invest in research for advanced detection and prevention tools.
- Scenario Outlook:
- Best: Rapid patching and user education reduce the malware’s impact significantly.
- Worst: Widespread exploitation leads to major breaches and loss of consumer confidence.
- Most-Likely: Gradual increase in incidents with incremental improvements in security responses.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, mobile security, Android, cybercrime, data breach, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us