Iranian Cyber Warfare Capabilities Diminished Amid US-Israel Military Operations
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iranian Hacking Groups Go Dark During US Israeli Military Strikes
1. BLUF (Bottom Line Up Front)
Iranian hacking groups have shown minimal activity during recent US and Israeli military operations against Iran, suggesting a significant reduction in their cyber capabilities. The most likely hypothesis is that Iran’s cyber capabilities have been degraded, possibly due to previous counter-cyber operations. This situation affects US and Israeli national security interests and could have broader implications for regional stability. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Iranian hacking groups have been strategically degraded by previous US and Israeli cyber operations, limiting their ability to respond effectively. Supporting evidence includes the reported silence of these groups and the hijacking of Iranian media by US and Israeli cyber operations. Key uncertainties include the extent of the degradation and whether it is temporary or permanent.
- Hypothesis B: Iranian hacking groups are deliberately withholding cyber operations as a strategic decision to avoid escalation or exposure. This could be supported by the historical use of proxy groups and the potential for exaggerated claims of cyber activity. Contradicting evidence includes the lack of significant proxy activity and the reported reduction in active groups.
- Assessment: Hypothesis A is currently better supported due to the observable reduction in Iranian cyber activity and the successful US and Israeli cyber operations. Indicators that could shift this judgment include a sudden resurgence in Iranian cyber activity or credible reports of strategic restraint by Iranian cyber units.
3. Key Assumptions and Red Flags
- Assumptions: Iranian cyber capabilities have been effectively degraded; US and Israeli cyber operations were successful; Iranian proxies are not currently active.
- Information Gaps: Detailed intelligence on the current operational status of Iranian cyber units; motivations behind the lack of Iranian cyber response.
- Bias & Deception Risks: Potential bias in Western media reports; possibility of Iranian strategic deception to mask capabilities.
4. Implications and Strategic Risks
The reduction in Iranian cyber activity could lead to a temporary decrease in cyber threats against US and Israeli interests, but it may also prompt Iran to develop more sophisticated cyber capabilities in the long term.
- Political / Geopolitical: Potential for reduced immediate cyber conflict, but risk of future escalation if Iran rebuilds capabilities.
- Security / Counter-Terrorism: Lower immediate cyber threat level, but vigilance required for potential retaliatory actions.
- Cyber / Information Space: Opportunity for US and Israel to capitalize on current cyber superiority; need to monitor for Iranian capability rebuilding.
- Economic / Social: Minimal immediate impact, but potential long-term effects if cyber capabilities are restored and used against critical infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of Iranian cyber activities; strengthen defenses against potential retaliatory cyber attacks.
- Medium-Term Posture (1–12 months): Enhance cyber resilience and partnerships with allies; invest in intelligence capabilities to detect Iranian cyber rebuilding efforts.
- Scenario Outlook:
- Best: Iran’s cyber capabilities remain degraded, reducing threat levels.
- Worst: Iran successfully rebuilds and enhances cyber capabilities, leading to increased attacks.
- Most-Likely: Iran gradually attempts to restore cyber capabilities, with sporadic low-level attacks.
6. Key Individuals and Entities
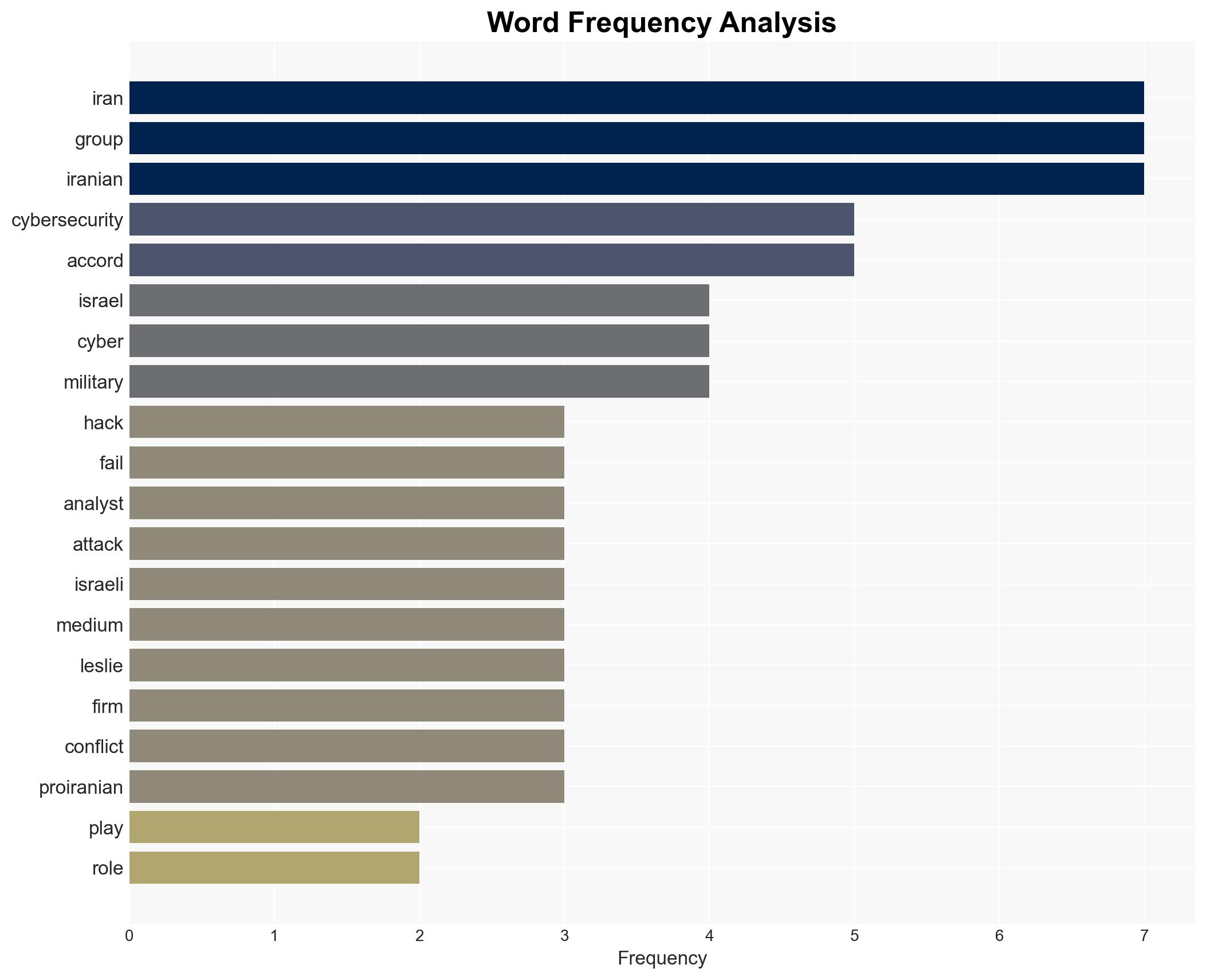
- Gen. Dan Caine, Chair of the Joint Chiefs of Staff
- Alexander Leslie, Threat Analyst at Recorded Future Inc.
- John Hultquist, Chief Analyst at Google Threat Intelligence Group
- Iran’s Islamic Revolutionary Guard Corps
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
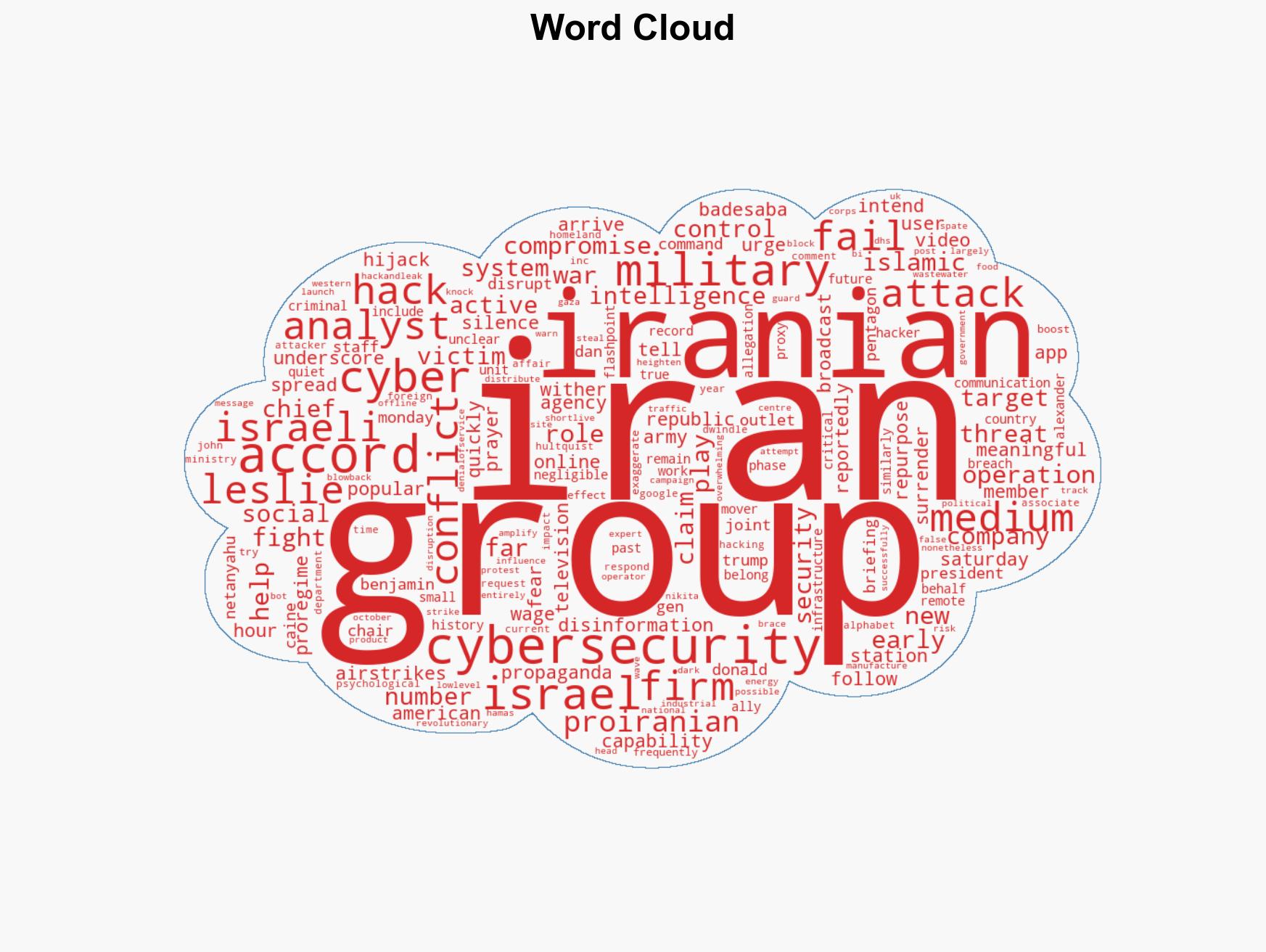
cybersecurity, cyber warfare, Iran, US-Israel relations, military strategy, cyber capabilities, information operations, national security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us