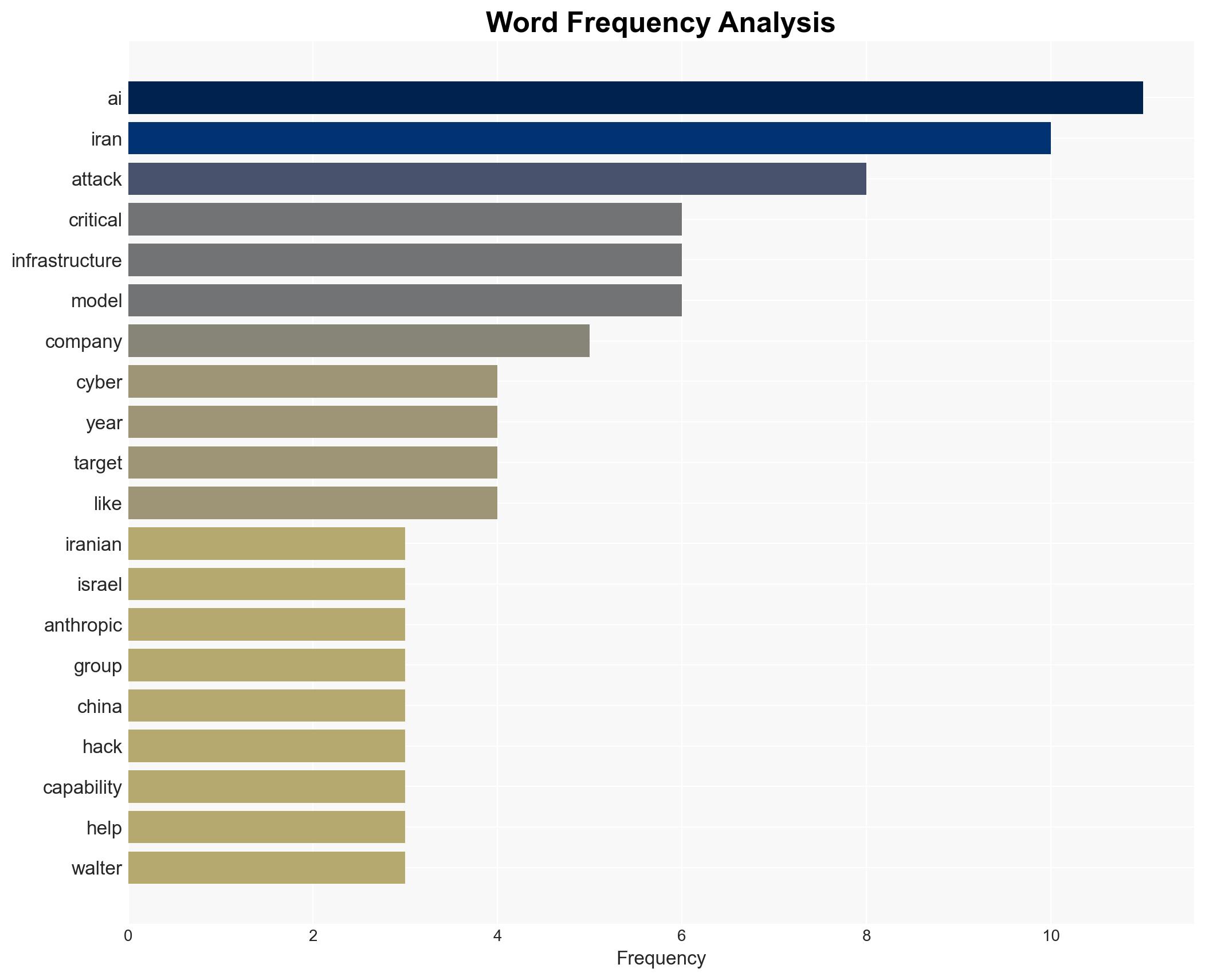
Iran’s Advancements in AI Tools Heighten Cyberattack Threats to U.S. and Allies
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran has the intent and increasingly the tools for AI-powered cyberattacks
1. BLUF (Bottom Line Up Front)
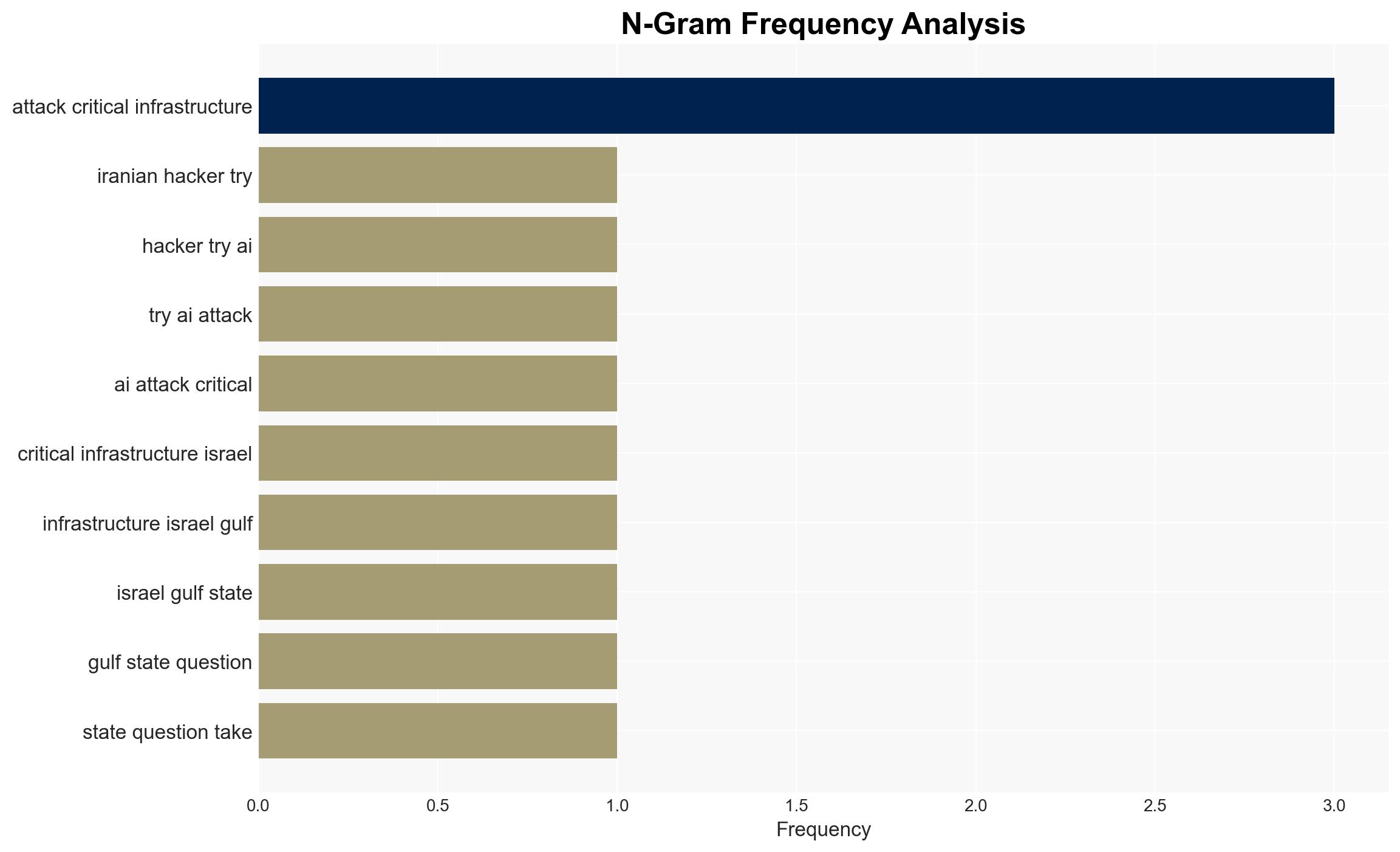
Iran is likely developing AI-powered cyber capabilities, presenting a growing threat to critical infrastructure in the U.S., Israel, and the Gulf States. While there is no public evidence of Iran’s AI capabilities matching those of China, Iran’s historical cyber activity and access to open-source AI models suggest a significant potential for advancement. Overall, there is moderate confidence in this assessment.
2. Competing Hypotheses
- Hypothesis A: Iran is actively developing and deploying AI-powered cyberattack capabilities. This is supported by Iran’s history of cyber operations, the use of AI in espionage and phishing, and access to open-source AI models. However, the lack of public evidence of AI usage at the scale seen in China introduces uncertainty.
- Hypothesis B: Iran’s AI cyber capabilities are overstated, and current activities are limited to traditional cyber operations. This is supported by the absence of documented large-scale AI cyberattacks by Iran. The reliance on open-source models may limit the sophistication of their capabilities.
- Assessment: Hypothesis A is currently better supported due to Iran’s demonstrated intent and capability in cyber operations and the strategic advantage of using open-source AI models. Indicators such as evidence of AI-driven attacks or increased sophistication in operations could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Iran has access to and the capability to utilize open-source AI models; Iran maintains intent to target U.S. and allied critical infrastructure; Iran’s cyber operations are state-sponsored and strategically directed.
- Information Gaps: Specific details on Iran’s current AI capabilities and deployment strategies; evidence of AI-driven cyberattacks by Iran; insights into Iran’s strategic objectives with AI in cyber operations.
- Bias & Deception Risks: Potential overestimation of Iran’s capabilities due to historical bias; reliance on open-source information may omit classified insights; adversarial deception in overstating or understating capabilities.
4. Implications and Strategic Risks
The development of AI-powered cyber capabilities by Iran could significantly alter the cyber threat landscape, impacting geopolitical stability and security dynamics.
- Political / Geopolitical: Increased tensions between Iran and Western nations, potential for retaliatory cyber or kinetic actions.
- Security / Counter-Terrorism: Enhanced threat to critical infrastructure, requiring updated defense and response strategies.
- Cyber / Information Space: Escalation in cyber warfare tactics, potential for more sophisticated and automated attacks.
- Economic / Social: Potential disruptions to economic activities and public services, impacting social stability and trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of Iranian cyber activities, enhance defenses against AI-driven attacks, and engage in intelligence sharing with allies.
- Medium-Term Posture (1–12 months): Develop resilience measures, invest in AI countermeasures, and strengthen international partnerships for cyber defense.
- Scenario Outlook:
- Best: Iran’s AI capabilities remain limited, with no significant escalation.
- Worst: Iran successfully deploys AI-driven cyberattacks, causing widespread disruption.
- Most-Likely: Gradual increase in sophistication of Iranian cyber operations, requiring ongoing vigilance and adaptation.
6. Key Individuals and Entities
- Allie Mellen, Principal Analyst at Forrester Research
- Bob Kolasky, Senior Vice President of Critical Infrastructure at Exiger
- Leeron Walter, Vice President of Strategy at Teramind
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, AI in cyber warfare, Iran cyber capabilities, critical infrastructure threats, open-source AI models, geopolitical tensions, cyber defense strategies
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us