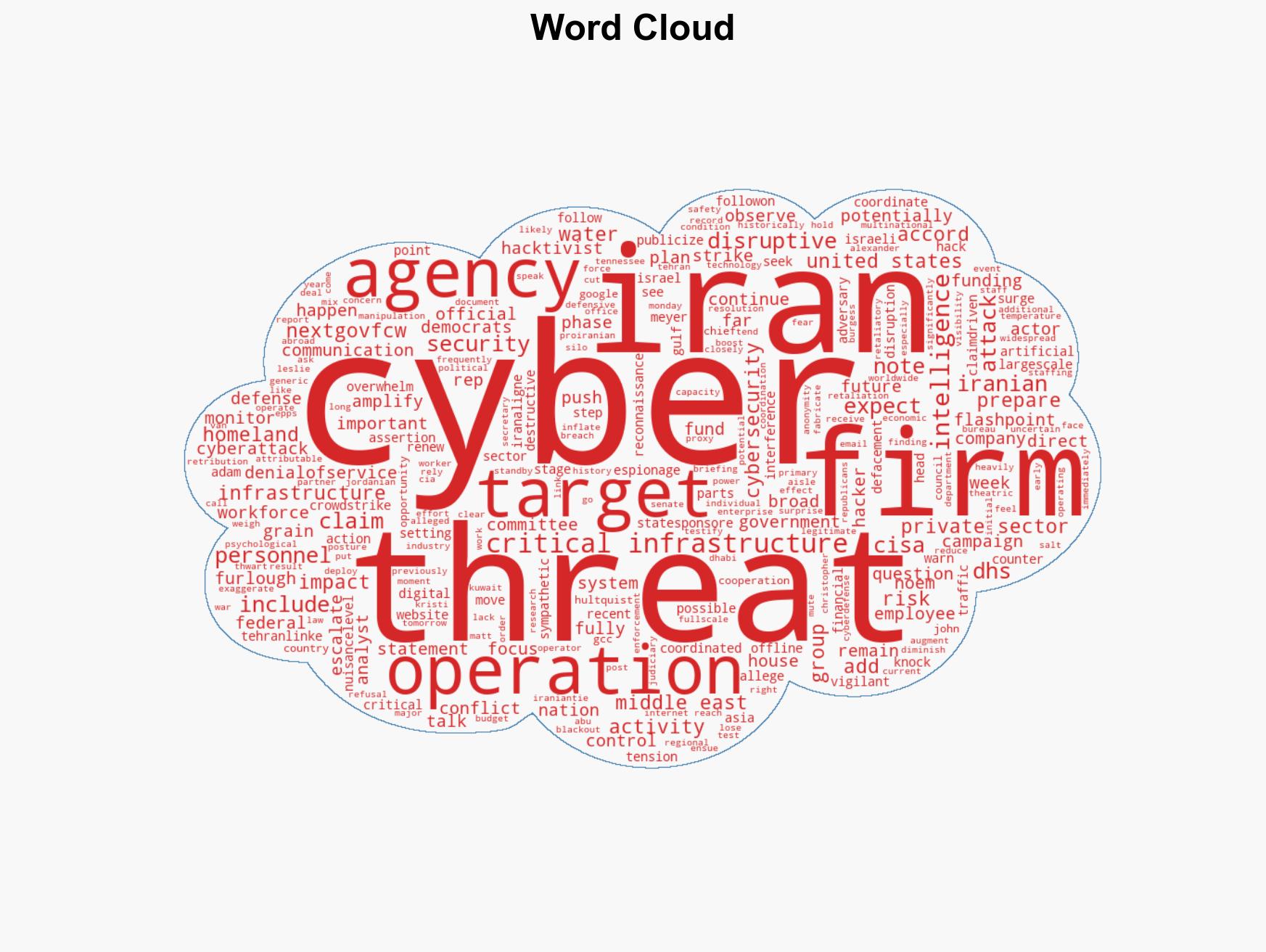
Iranian Cyber Threats Rise Amid U.S.-Israeli Strikes, Firms Warn of Increased Hacktivist Activity
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Intelligence firms watch for uptick in Iran cyber activity after US Israel strikes
1. BLUF (Bottom Line Up Front)
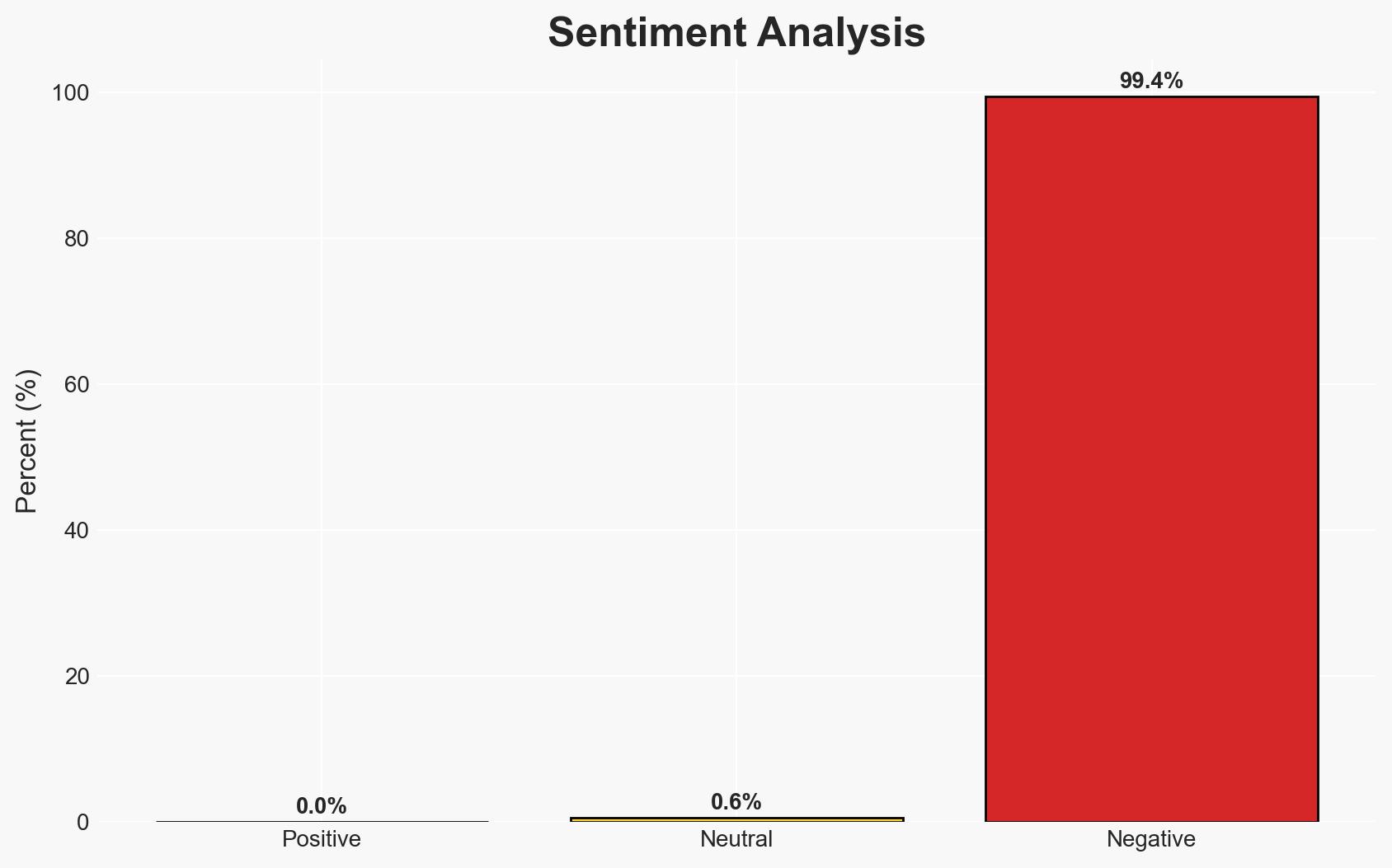
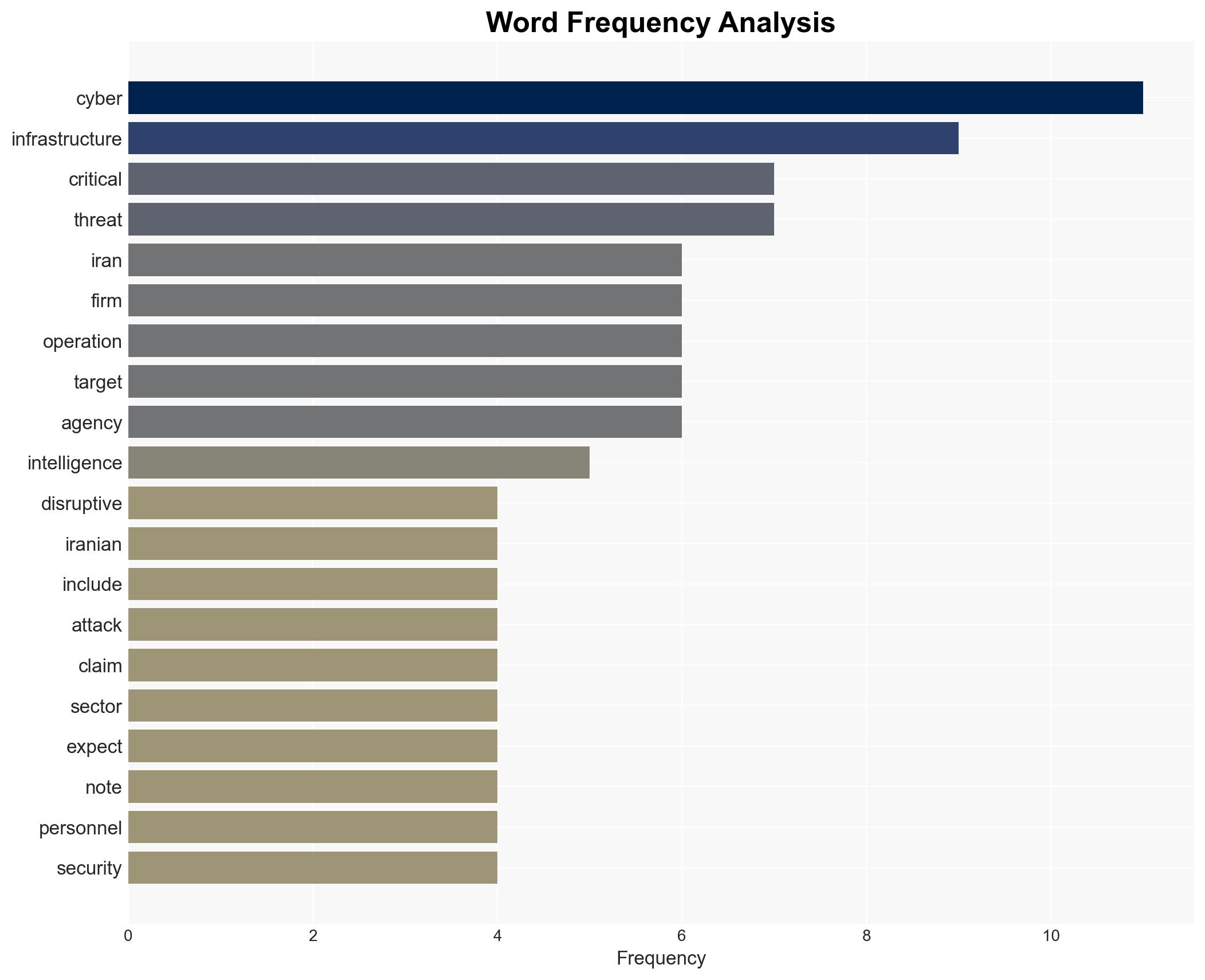
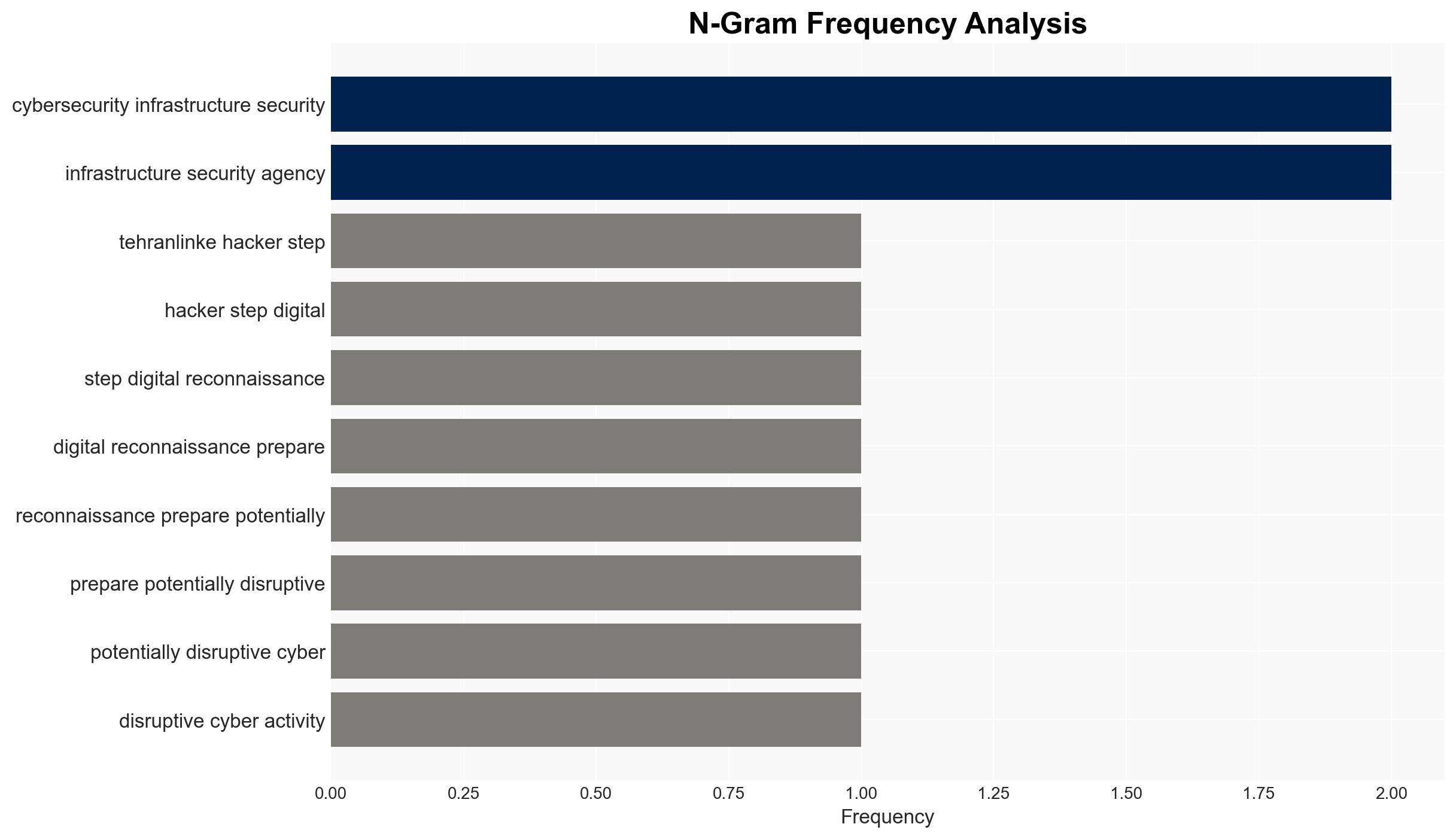
Recent U.S. and Israeli strikes on Iran have likely prompted Tehran-linked hackers to increase digital reconnaissance and prepare for disruptive cyber activities. While no large-scale state-sponsored campaigns have been observed, there is a surge in activity from Iran-aligned hacktivist groups. The primary targets are expected to be U.S., Israeli, and GCC critical infrastructure. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Iran is preparing for a coordinated cyber retaliation against U.S., Israeli, and GCC targets. This is supported by increased reconnaissance and hacktivist claims, but contradicted by the lack of observed large-scale operations and historical mixed results of Iranian cyberattacks.
- Hypothesis B: Iran’s cyber activities are primarily defensive and aimed at psychological impact rather than actual disruption. This is supported by the absence of direct attacks on U.S. critical infrastructure and reliance on exaggerated claims.
- Assessment: Hypothesis A is currently better supported due to the geopolitical context and recent uptick in hacktivist activities. However, indicators such as direct attacks on critical infrastructure could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Iran has the capability to conduct significant cyber operations; Iran-linked groups will act in alignment with state interests; geopolitical tensions will drive cyber activities.
- Information Gaps: Detailed intelligence on specific Iranian cyber capabilities and intentions; visibility into internal Iranian decision-making processes.
- Bias & Deception Risks: Potential exaggeration of capabilities by Iranian sources; confirmation bias in interpreting hacktivist claims as state-sponsored actions.
4. Implications and Strategic Risks
The development could lead to increased cyber hostilities and potential escalation in the Middle East. It may also influence global cyber norms and provoke retaliatory measures.
- Political / Geopolitical: Escalation of tensions between Iran and the U.S./Israel, potential for broader regional conflict.
- Security / Counter-Terrorism: Heightened threat environment for critical infrastructure, increased vigilance required.
- Cyber / Information Space: Surge in cyber espionage and misinformation campaigns, potential for disruptive cyberattacks.
- Economic / Social: Disruption to economic activities, particularly in the energy and financial sectors, could impact global markets.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber activities, strengthen defenses of critical infrastructure, engage in diplomatic efforts to de-escalate tensions.
- Medium-Term Posture (1–12 months): Develop cyber resilience measures, foster international partnerships for collective defense, invest in cyber intelligence capabilities.
- Scenario Outlook:
- Best: Diplomatic resolution reduces cyber hostilities.
- Worst: Full-scale cyber conflict affecting global infrastructure.
- Most-Likely: Continued low-level cyber skirmishes with intermittent disruptive attacks.
6. Key Individuals and Entities
- Adam Meyers, CrowdStrike
- John Hultquist, Google’s Threat Intelligence Group
- Alexander Leslie, Recorded Future
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, Iran, U.S.-Israel relations, hacktivism, critical infrastructure, Middle East tensions, cyber-espionage
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us