Cisco Talos Assesses Cyber Threat Landscape Amid Ongoing Middle East Conflict
Published on: 2026-03-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
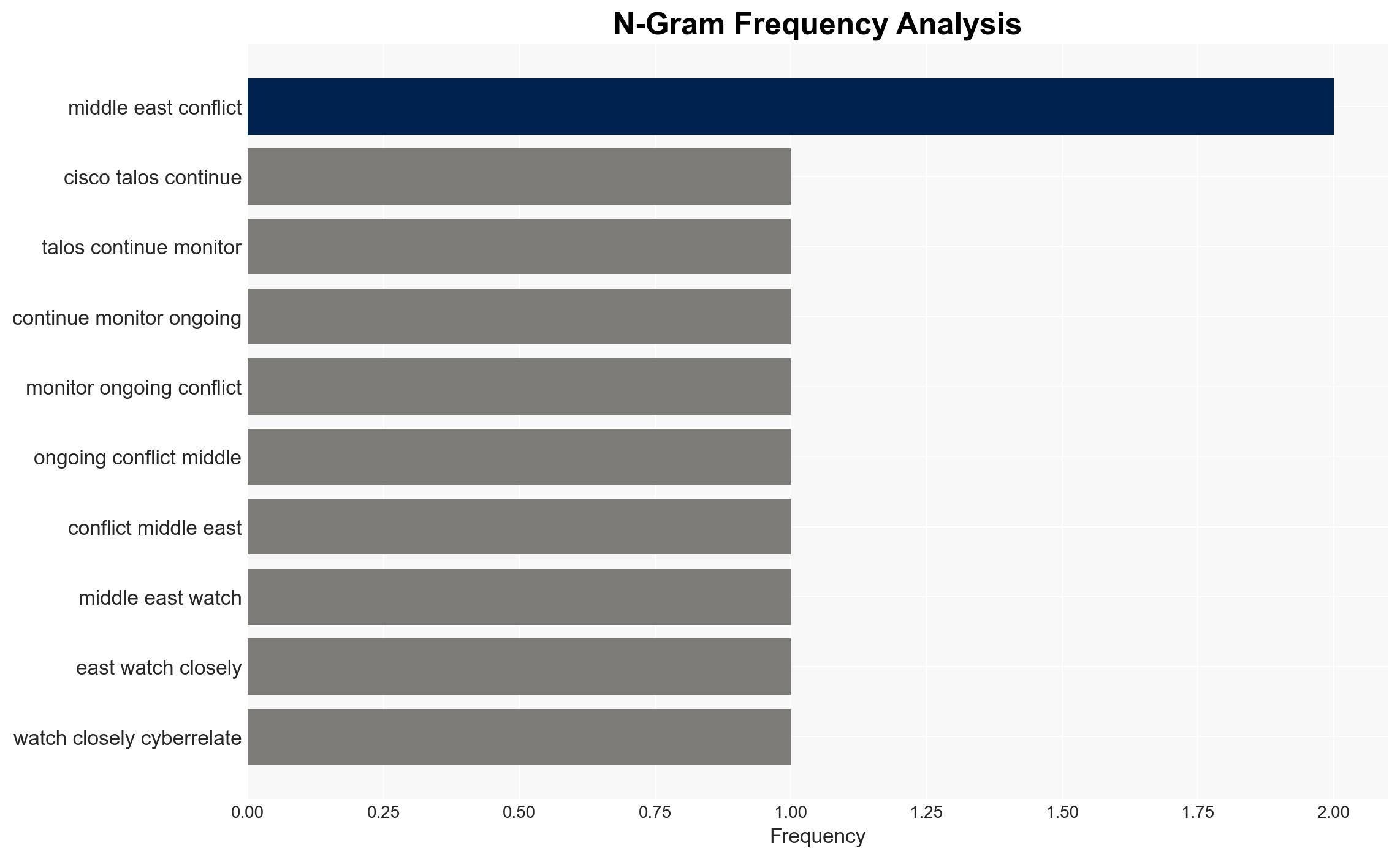
Intelligence Report: Talos on the developing situation in the Middle East
1. BLUF (Bottom Line Up Front)
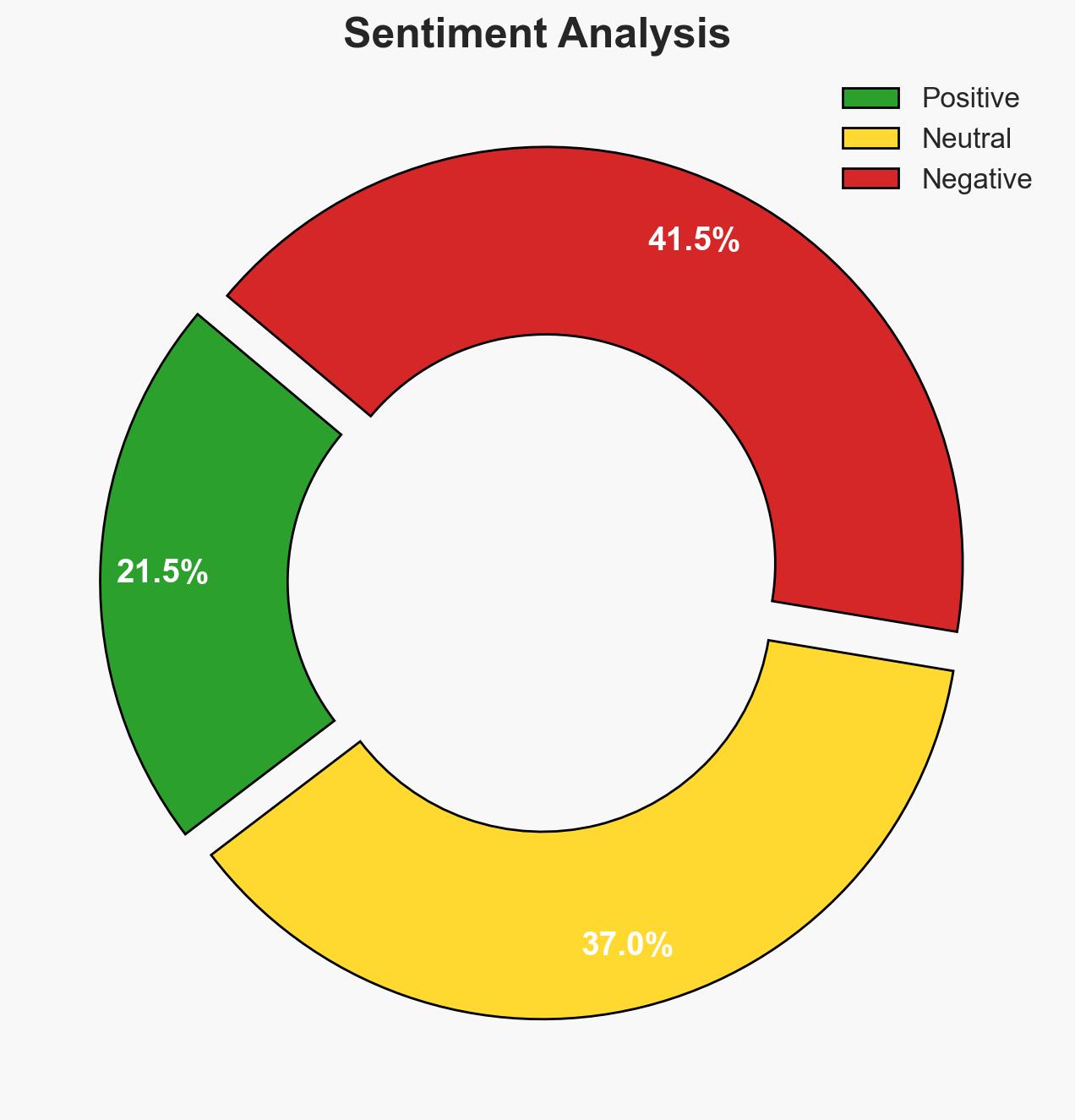
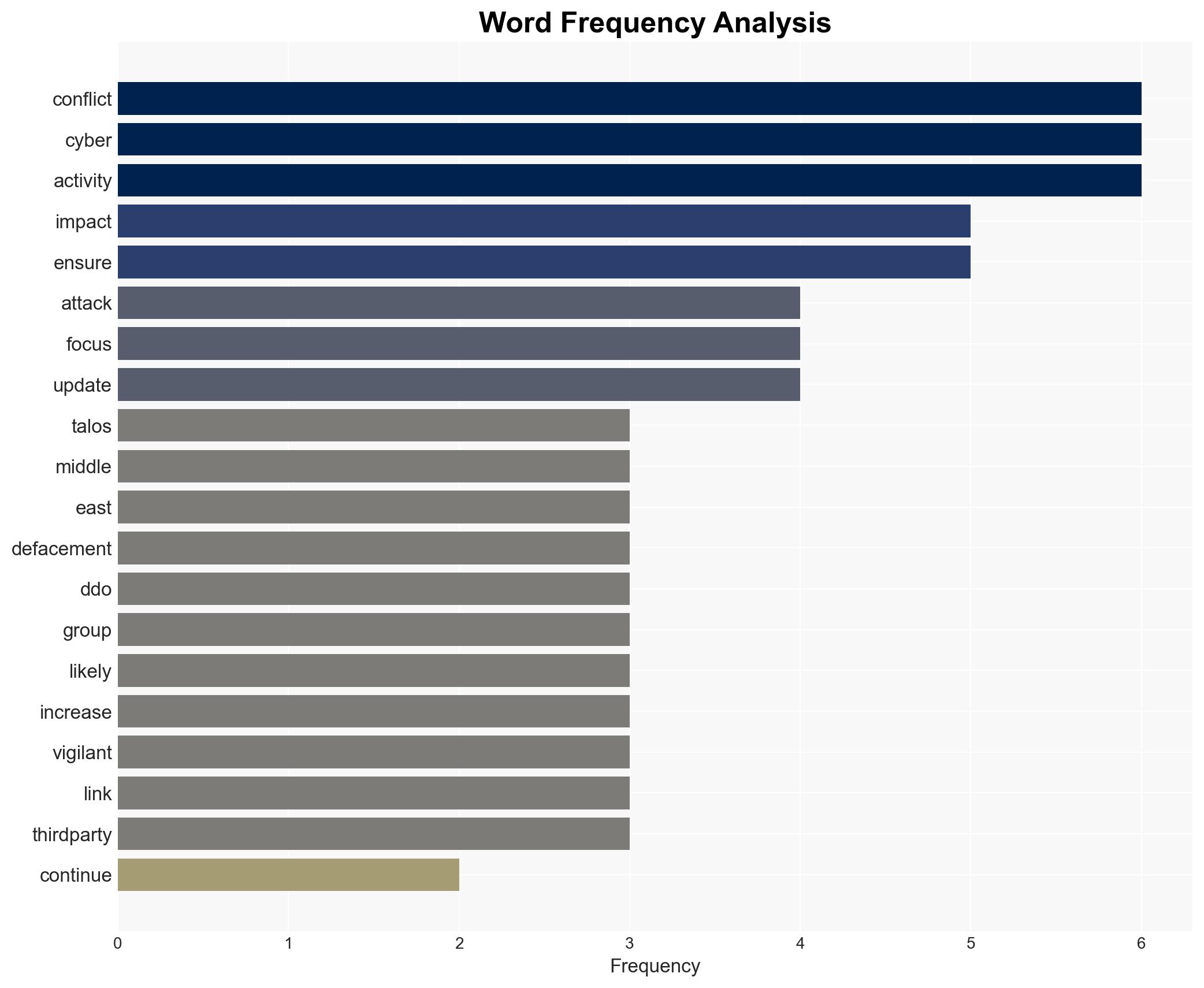
The current cyber threat landscape in the Middle East conflict remains limited to minor incidents such as web defacements and small-scale DDoS attacks. There is no significant increase in state-sponsored cyber activity observed. The primary concern lies with hacktivist groups and cybercriminals exploiting the situation. Overall, there is moderate confidence in these assessments, with vigilance required due to the fluid nature of the conflict.
2. Competing Hypotheses
- Hypothesis A: The cyber threat environment will remain limited to minor incidents with no significant escalation from state-sponsored actors. This is supported by the lack of observed increase in cyber activity from state-affiliated groups and historical patterns of regional conflict focusing on kinetic operations. Key uncertainties include potential shifts in geopolitical dynamics that could trigger increased cyber operations.
- Hypothesis B: There will be an escalation in cyber activities by state-sponsored actors as the conflict progresses. This hypothesis is contradicted by current observations but remains plausible if geopolitical tensions escalate or if there is a strategic decision to leverage cyber capabilities more aggressively.
- Assessment: Hypothesis A is currently better supported due to the absence of significant state-sponsored cyber activities and the historical focus on kinetic warfare. Indicators that could shift this judgment include increased cyber reconnaissance or preparatory activities by state actors.
3. Key Assumptions and Red Flags
- Assumptions: The conflict will remain primarily kinetic; state-sponsored cyber actors will not significantly escalate operations without strategic impetus; hacktivist activities will remain opportunistic and limited in scope.
- Information Gaps: Detailed intelligence on the strategic intentions of state-sponsored cyber actors; real-time data on cyber incidents in the region; insights into the coordination between hacktivists and state actors.
- Bias & Deception Risks: Potential underestimation of state-sponsored capabilities; reliance on open-source data which may not capture covert operations; possible misinformation campaigns by involved parties.
4. Implications and Strategic Risks
The ongoing conflict in the Middle East, while currently focused on kinetic operations, has the potential to evolve into a more complex cyber conflict if geopolitical dynamics change. The current cyber threat landscape is manageable but requires close monitoring.
- Political / Geopolitical: Escalation of cyber activities could lead to broader regional instability and international diplomatic tensions.
- Security / Counter-Terrorism: Increased cyber operations could complicate counter-terrorism efforts and strain security resources.
- Cyber / Information Space: Hacktivist and cybercriminal activities could disrupt critical infrastructure and spread misinformation.
- Economic / Social: Cyber disruptions could impact economic stability and social cohesion, particularly if critical services are targeted.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber activities, particularly from hacktivist groups; reinforce cybersecurity hygiene practices; maintain open communication with regional partners.
- Medium-Term Posture (1–12 months): Develop resilience measures against potential cyber escalations; strengthen partnerships with regional and international cybersecurity entities; invest in capability development for rapid response.
- Scenario Outlook:
- Best: Conflict remains kinetic with limited cyber impact; vigilance maintained.
- Worst: Significant cyber escalation disrupts critical infrastructure and international relations.
- Most-Likely: Continued minor cyber incidents with potential for increased hacktivist activity.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
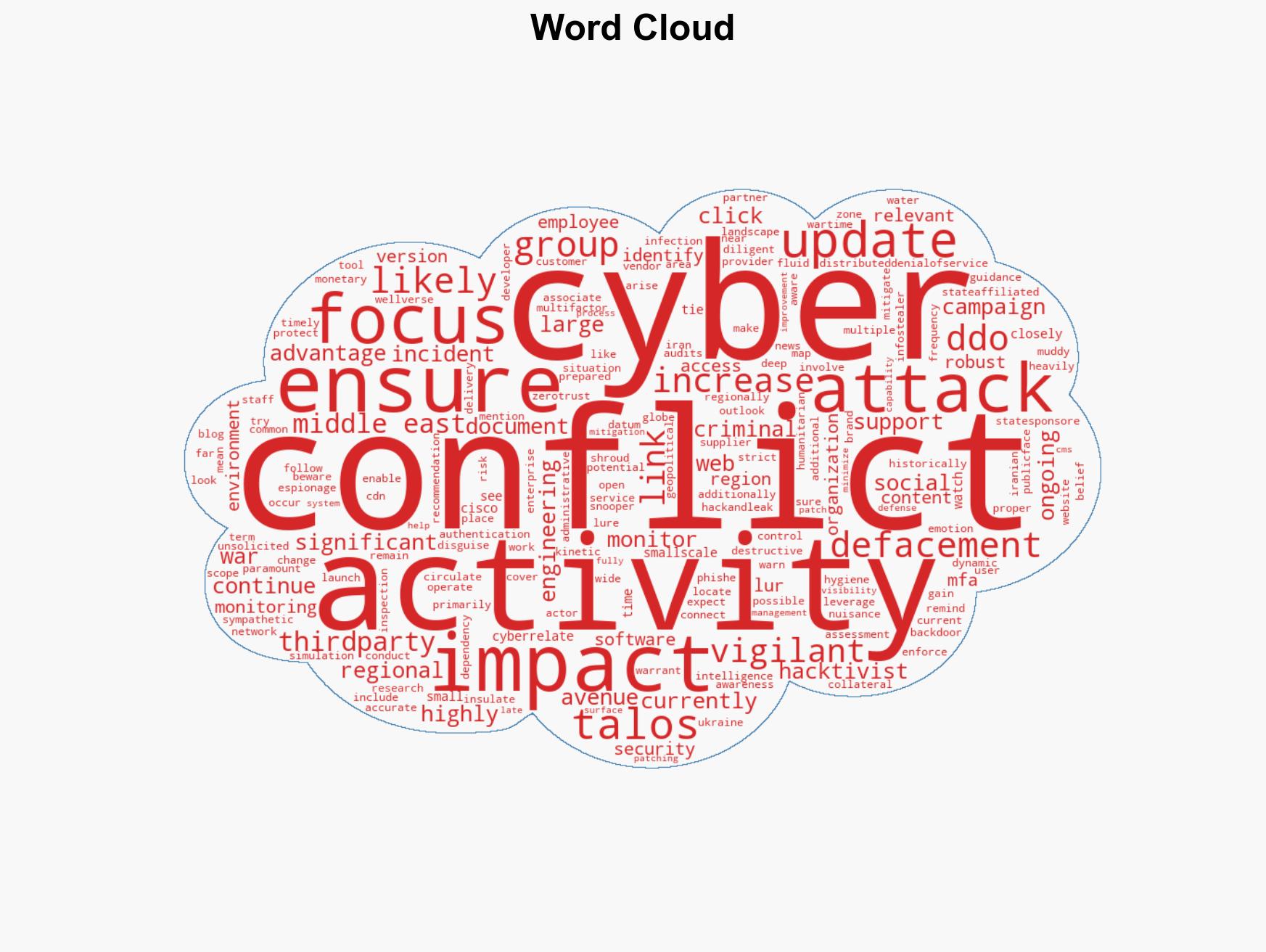
cybersecurity, Middle East conflict, hacktivism, state-sponsored cyber activity, geopolitical tensions, cybercrime, information warfare
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us