Microsoft Alerts on OAuth Scams Exploiting Redirects for Malware Attacks on Public Sector Organizations
Published on: 2026-03-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Phish of the day Microsoft OAuth scams abuse redirects for malware delivery
1. BLUF (Bottom Line Up Front)
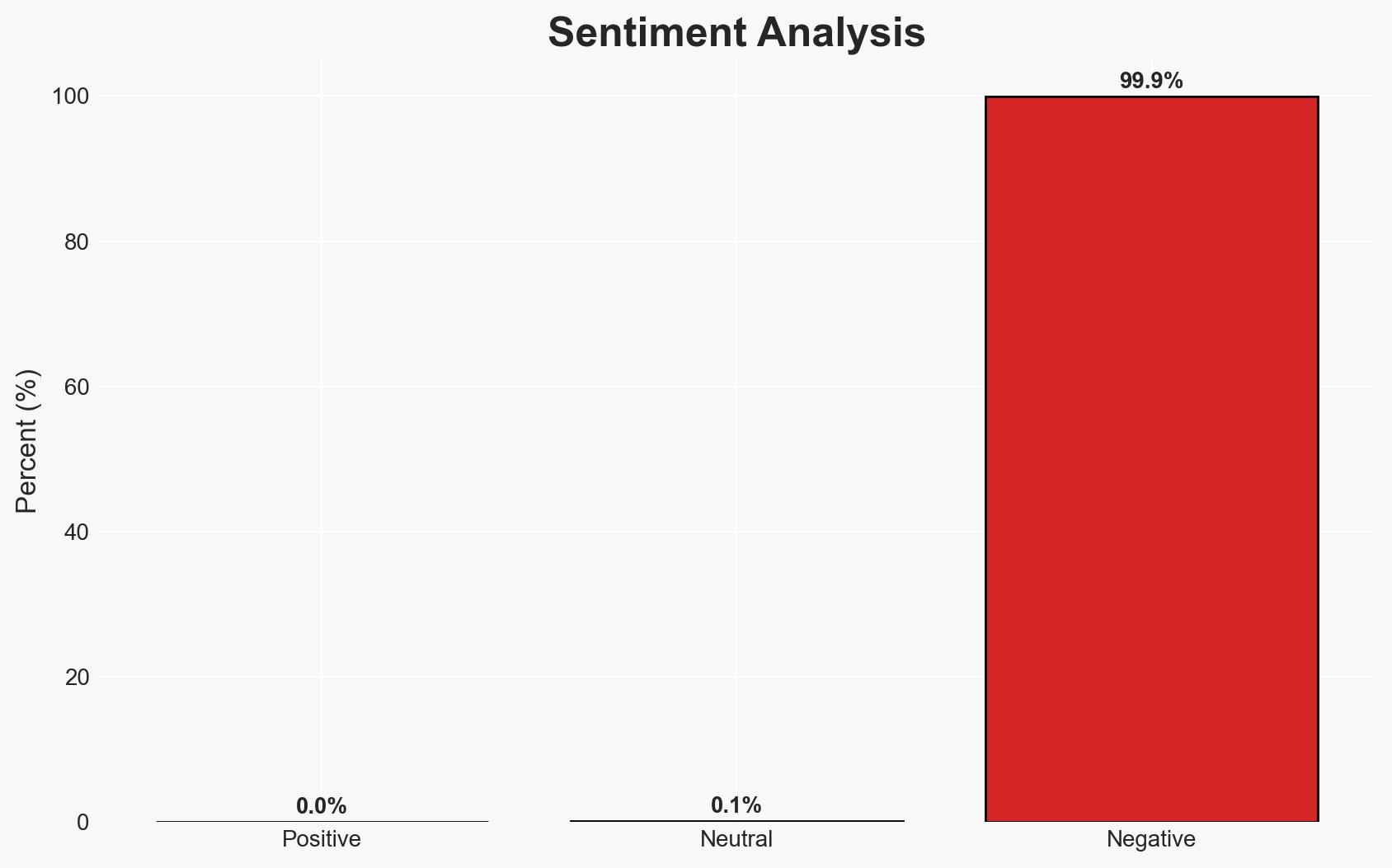
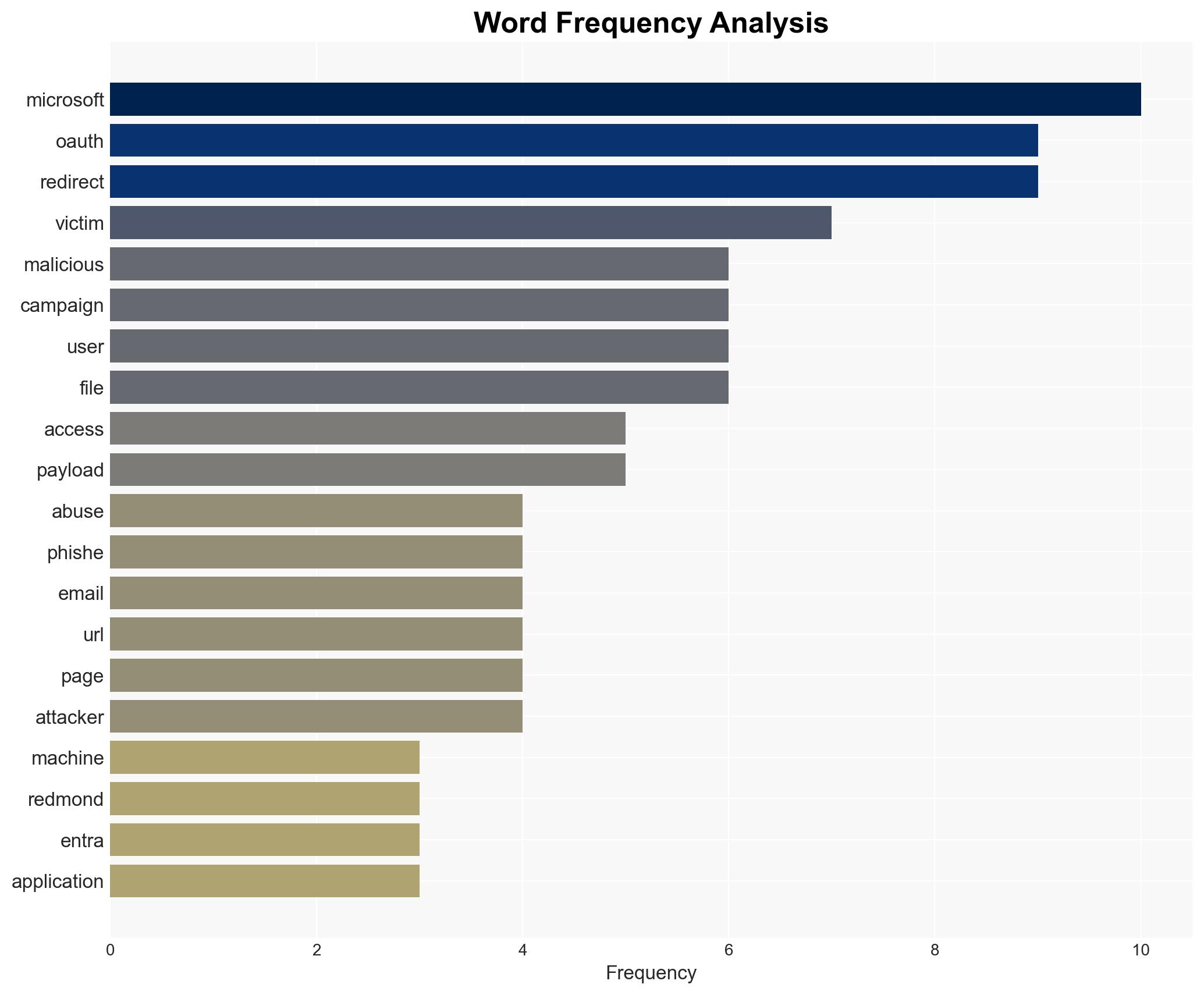
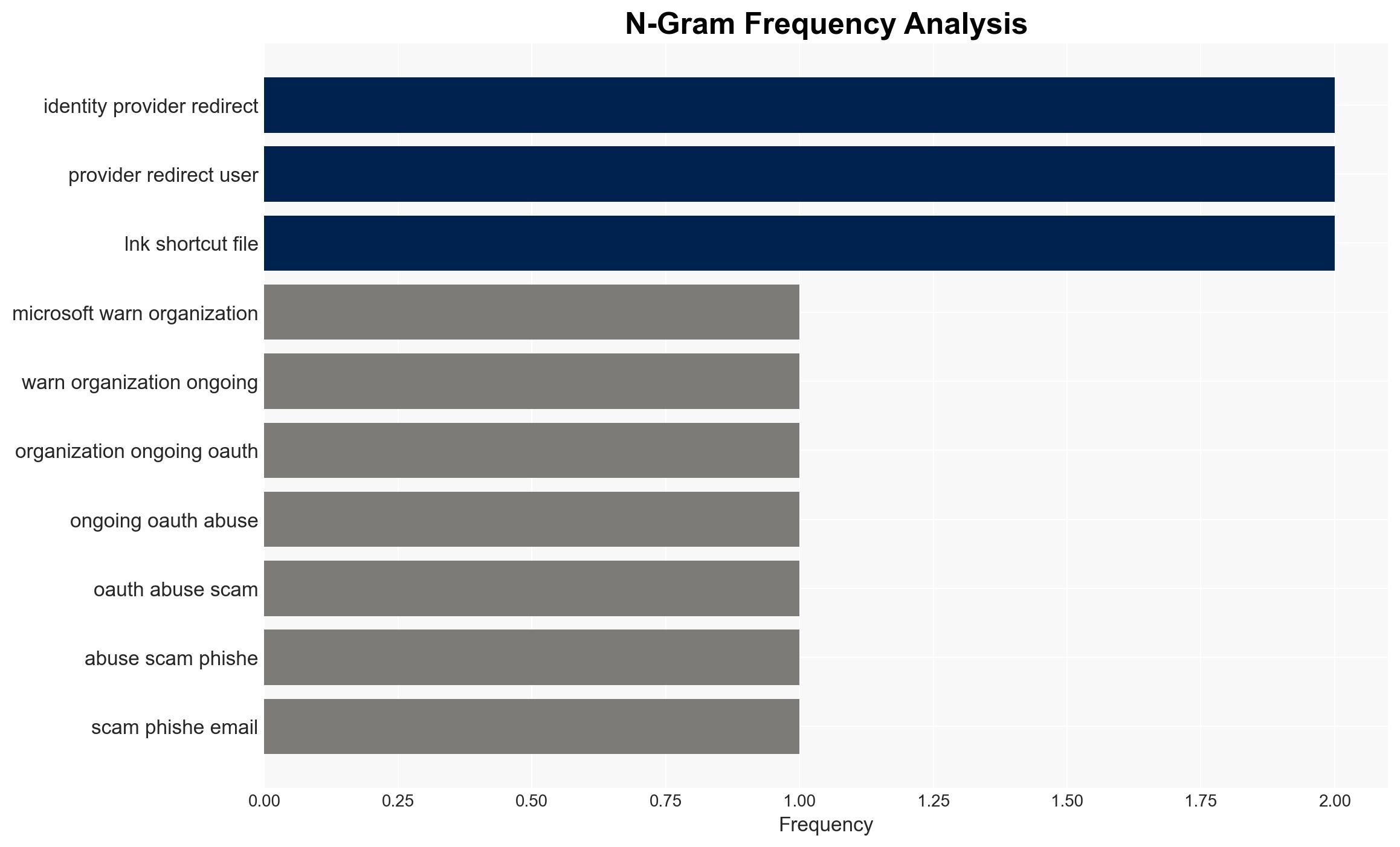
Microsoft has identified ongoing OAuth abuse scams targeting government and public-sector organizations, using phishing emails and URL redirects to deliver malware. The most likely hypothesis is that these campaigns are part of a broader trend of sophisticated cyber threats leveraging legitimate protocols for malicious purposes. This assessment is made with moderate confidence due to limited information on the scope and scale of the campaigns.
2. Competing Hypotheses
- Hypothesis A: The OAuth abuse scams are isolated incidents conducted by independent cybercriminal groups exploiting known vulnerabilities in OAuth protocols. Supporting evidence includes the use of common phishing tactics and tools. However, the lack of detailed information on the actors and their coordination limits this hypothesis.
- Hypothesis B: The scams are part of a coordinated effort by a sophisticated threat actor group targeting specific sectors for strategic gain. This is supported by the targeted nature of the attacks on government and public-sector organizations and the use of advanced techniques like phishing-as-a-service. Contradicting evidence includes the use of publicly available tools, which could suggest less sophistication.
- Assessment: Hypothesis B is currently better supported due to the targeted nature of the attacks and the use of advanced techniques. Indicators that could shift this judgment include evidence of coordination among multiple groups or identification of a specific threat actor.
3. Key Assumptions and Red Flags
- Assumptions: The OAuth protocol vulnerabilities are well-known and exploitable; the targeted organizations have insufficient defenses against such phishing tactics; the attackers have the capability to adapt to countermeasures.
- Information Gaps: Detailed information on the size, scope, and specific targets of the campaigns; identification of the actors behind the attacks; the full impact on affected organizations.
- Bias & Deception Risks: Potential bias in overestimating the sophistication of the attackers due to the use of advanced techniques; risk of deception if attackers are using false flags to mislead attribution efforts.
4. Implications and Strategic Risks
This development could lead to increased cyber threats against public-sector entities, potentially compromising sensitive information and disrupting operations. Over time, it may necessitate enhanced cybersecurity measures and international cooperation.
- Political / Geopolitical: Potential for increased tensions if state-sponsored involvement is suspected or confirmed.
- Security / Counter-Terrorism: Heightened threat environment requiring improved defensive measures and threat intelligence sharing.
- Cyber / Information Space: Increased focus on securing OAuth implementations and improving phishing detection capabilities.
- Economic / Social: Potential economic impact due to resource allocation for cybersecurity and possible public trust erosion in digital services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of OAuth activity, conduct phishing awareness training, and implement stricter email filtering protocols.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing, invest in advanced cybersecurity technologies, and review OAuth implementation security.
- Scenario Outlook:
- Best: Successful mitigation of threats with improved defenses and no major breaches.
- Worst: Significant breaches leading to data loss and operational disruptions.
- Most-Likely: Continued attempts with varying success, leading to incremental improvements in defenses.
6. Key Individuals and Entities
- Microsoft Security Researchers
- Microsoft Entra
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
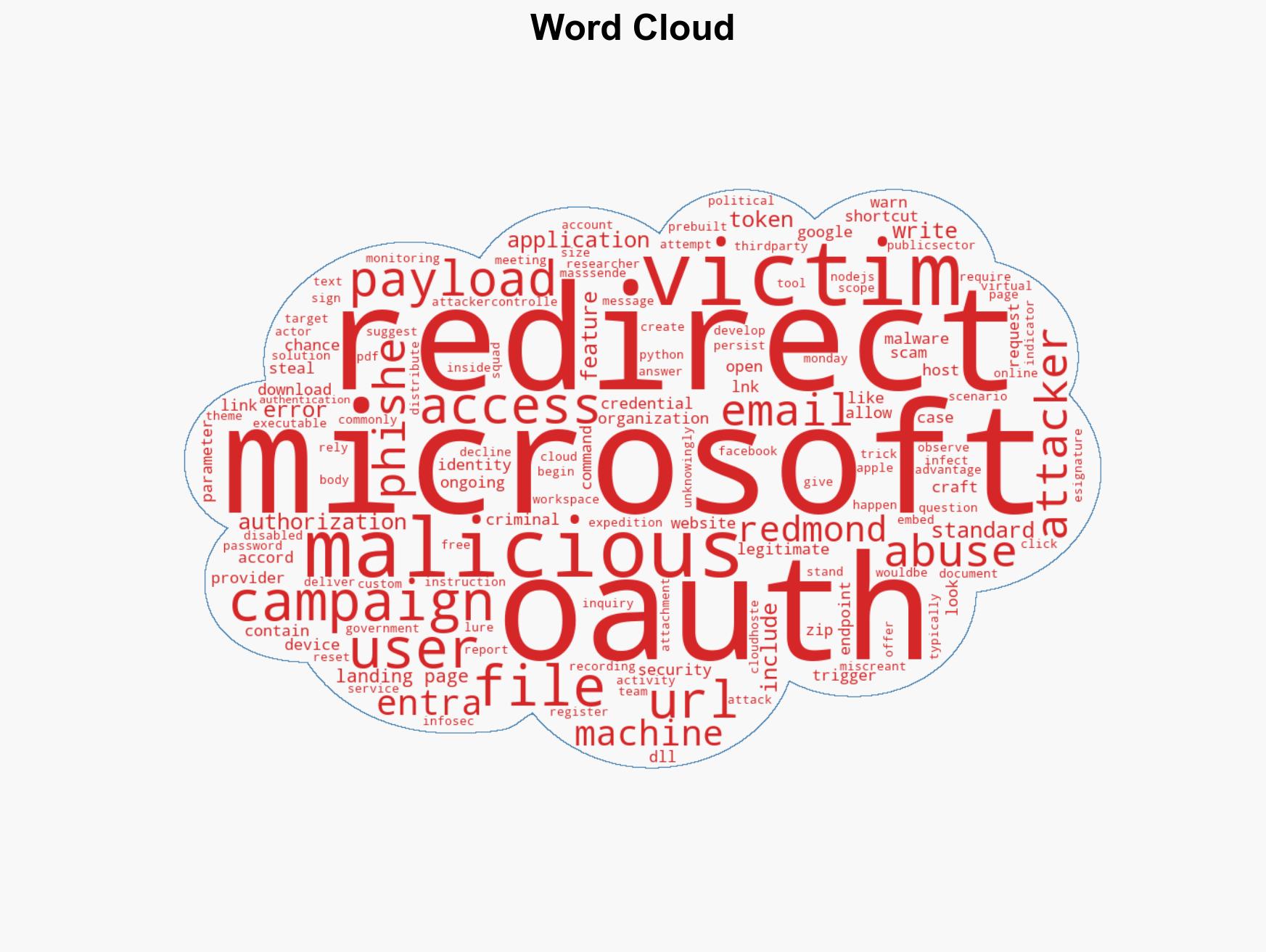
cybersecurity, phishing, OAuth abuse, malware delivery, public-sector targeting, threat intelligence, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us