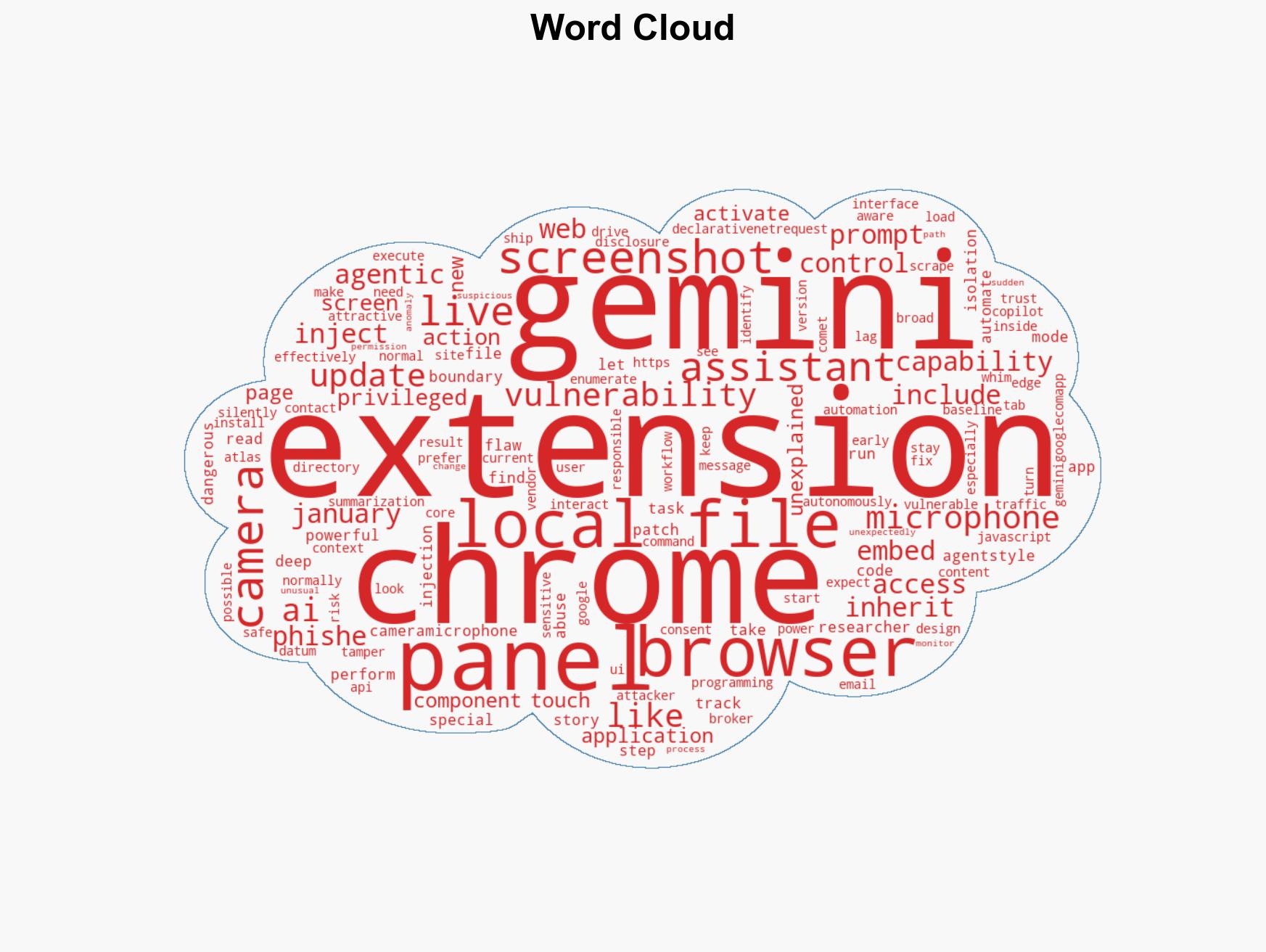
Vulnerability in Chrome’s Gemini panel allowed extensions to exploit camera and file access capabilities
Published on: 2026-03-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Chrome flaw let extensions hijack Geminis camera mic and file access
1. BLUF (Bottom Line Up Front)
The vulnerability in Chrome’s Gemini panel allowed low-privilege extensions to gain unauthorized access to sensitive functions, posing significant security risks. The patch released in January 2026 mitigates these risks, but the incident highlights the broader threat landscape associated with AI-driven browser components. This assessment is made with moderate confidence, given the potential for undisclosed vulnerabilities and evolving threat tactics.
2. Competing Hypotheses
- Hypothesis A: The vulnerability was an isolated incident due to a specific oversight in Chrome’s Gemini panel design. Supporting evidence includes the rapid patch deployment and no immediate reports of widespread exploitation. However, uncertainties remain about the potential for similar vulnerabilities in other AI-driven browser components.
- Hypothesis B: The vulnerability is indicative of a systemic issue with AI-driven browser components, suggesting a broader security risk. This is supported by the inherent complexity and broad access requirements of such components, which may lead to more vulnerabilities. Contradicting evidence includes the lack of similar reported vulnerabilities in other components at this time.
- Assessment: Hypothesis B is currently better supported due to the structural complexities and broad access needs of AI-driven browser components, which inherently increase the risk of vulnerabilities. Key indicators that could shift this judgment include the discovery of similar vulnerabilities in other components or evidence of systemic design flaws.
3. Key Assumptions and Red Flags
- Assumptions: The patch effectively mitigates the vulnerability; AI-driven components will continue to be integrated into browsers; attackers will exploit similar vulnerabilities if present.
- Information Gaps: Details on whether similar vulnerabilities exist in other AI-driven browser components; comprehensive data on exploitation attempts or success rates.
- Bias & Deception Risks: Potential underreporting of exploitation incidents due to reputational concerns; cognitive bias towards assuming patched vulnerabilities are fully resolved.
4. Implications and Strategic Risks
This development underscores the evolving threat landscape associated with AI-driven browser components, potentially leading to increased scrutiny and regulatory oversight.
- Political / Geopolitical: Potential for increased regulatory scrutiny of AI technologies and their integration into consumer products.
- Security / Counter-Terrorism: Enhanced risk of cyber exploitation by state and non-state actors leveraging similar vulnerabilities.
- Cyber / Information Space: Increased focus on securing AI-driven components and potential for new cyber defense strategies.
- Economic / Social: Potential consumer distrust in AI-driven technologies, impacting adoption rates and market dynamics.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Ensure all systems are updated to the latest Chrome version; conduct audits of installed extensions for unauthorized access.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to enhance detection capabilities; invest in research to identify potential vulnerabilities in AI-driven components.
- Scenario Outlook:
- Best: No further vulnerabilities are discovered, and consumer trust in AI-driven technologies is restored.
- Worst: Multiple vulnerabilities are found, leading to significant breaches and regulatory crackdowns.
- Most-Likely: Sporadic vulnerabilities are identified and patched, with gradual improvements in security practices.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, AI-driven technologies, browser vulnerabilities, information security, regulatory oversight, consumer trust
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us