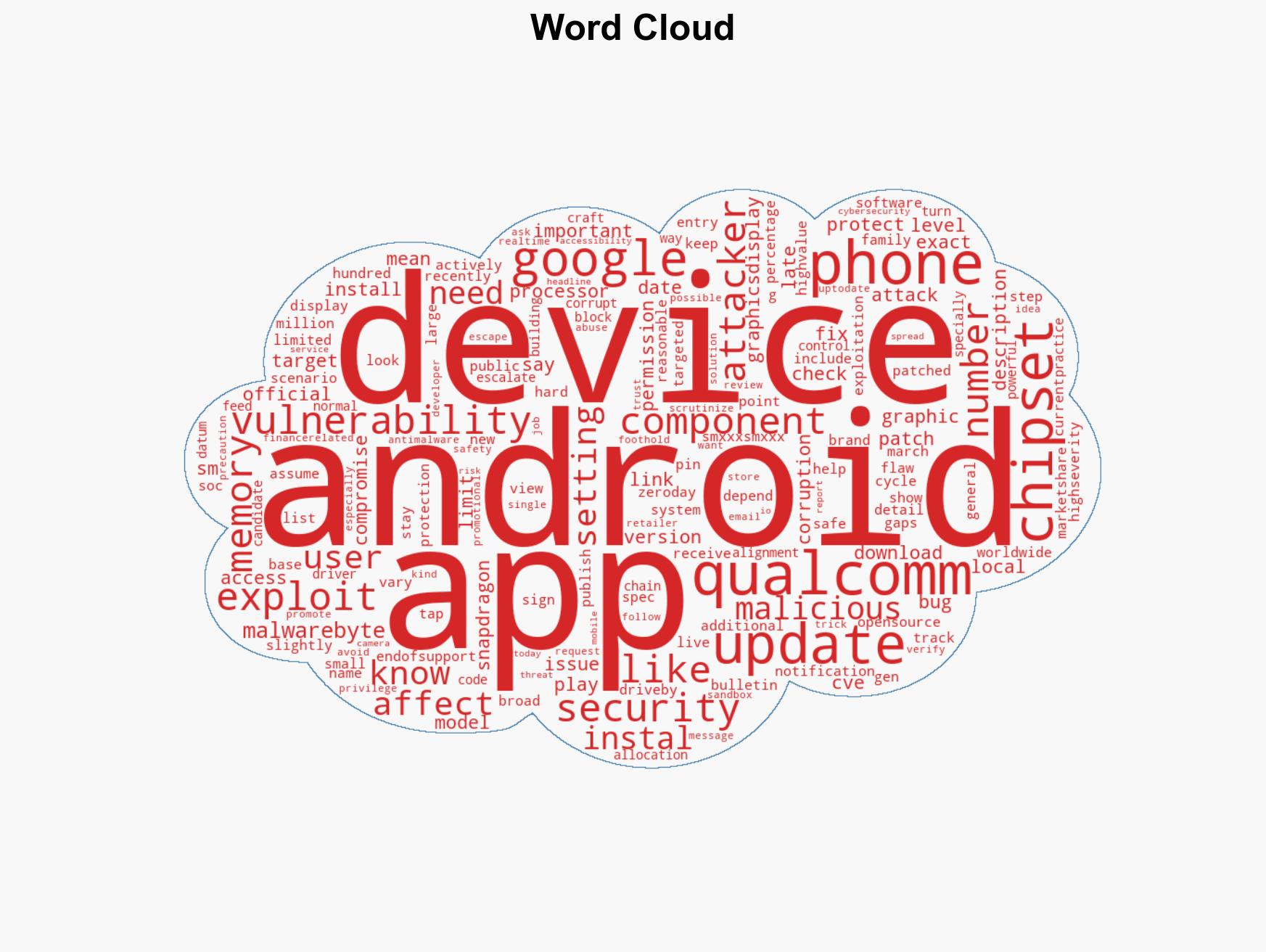
Critical Qualcomm vulnerability targets Android devices amid active exploitation in recent attacks
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: High-severity Qualcomm bug hits Android devices in targeted attacks
1. BLUF (Bottom Line Up Front)
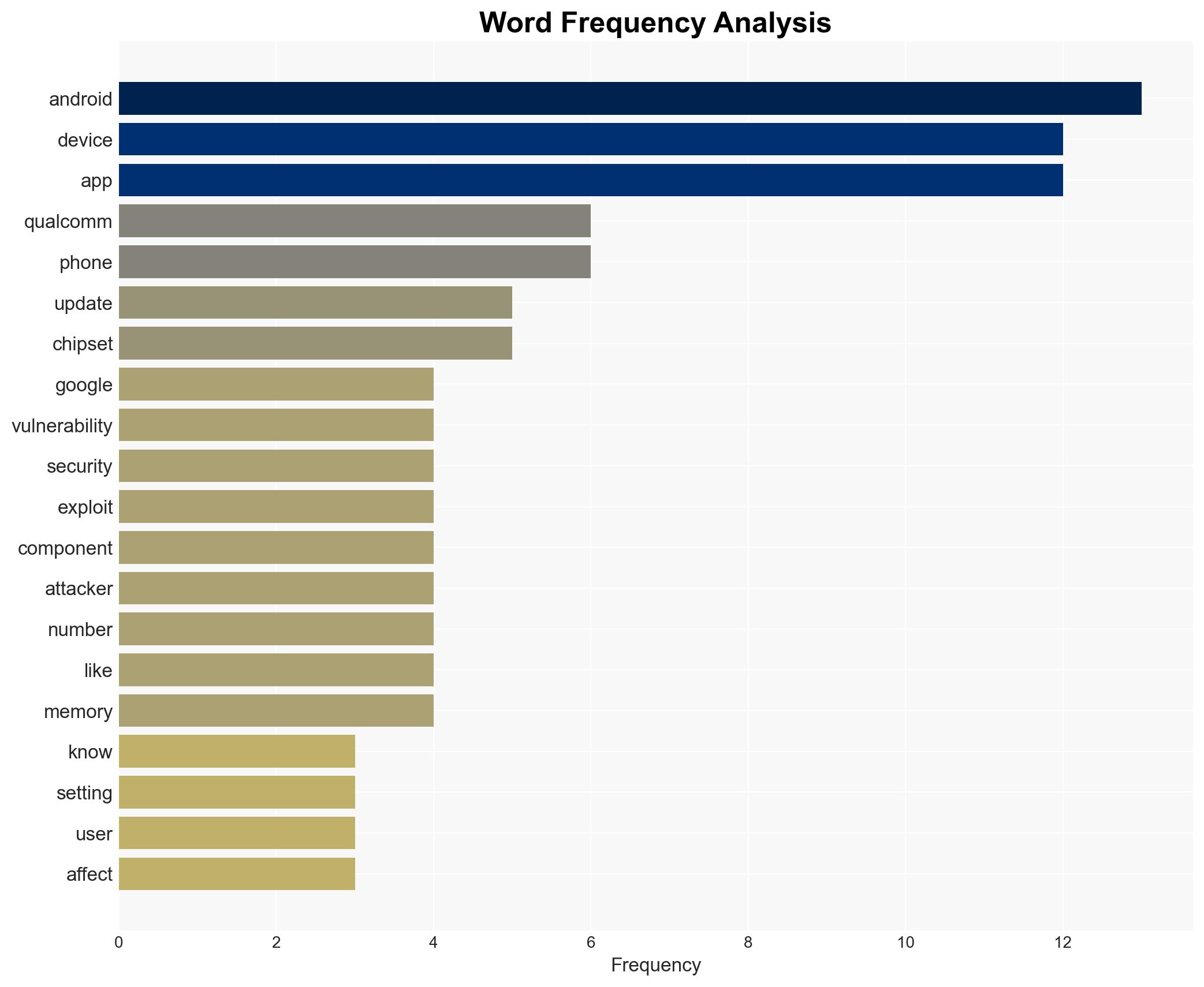
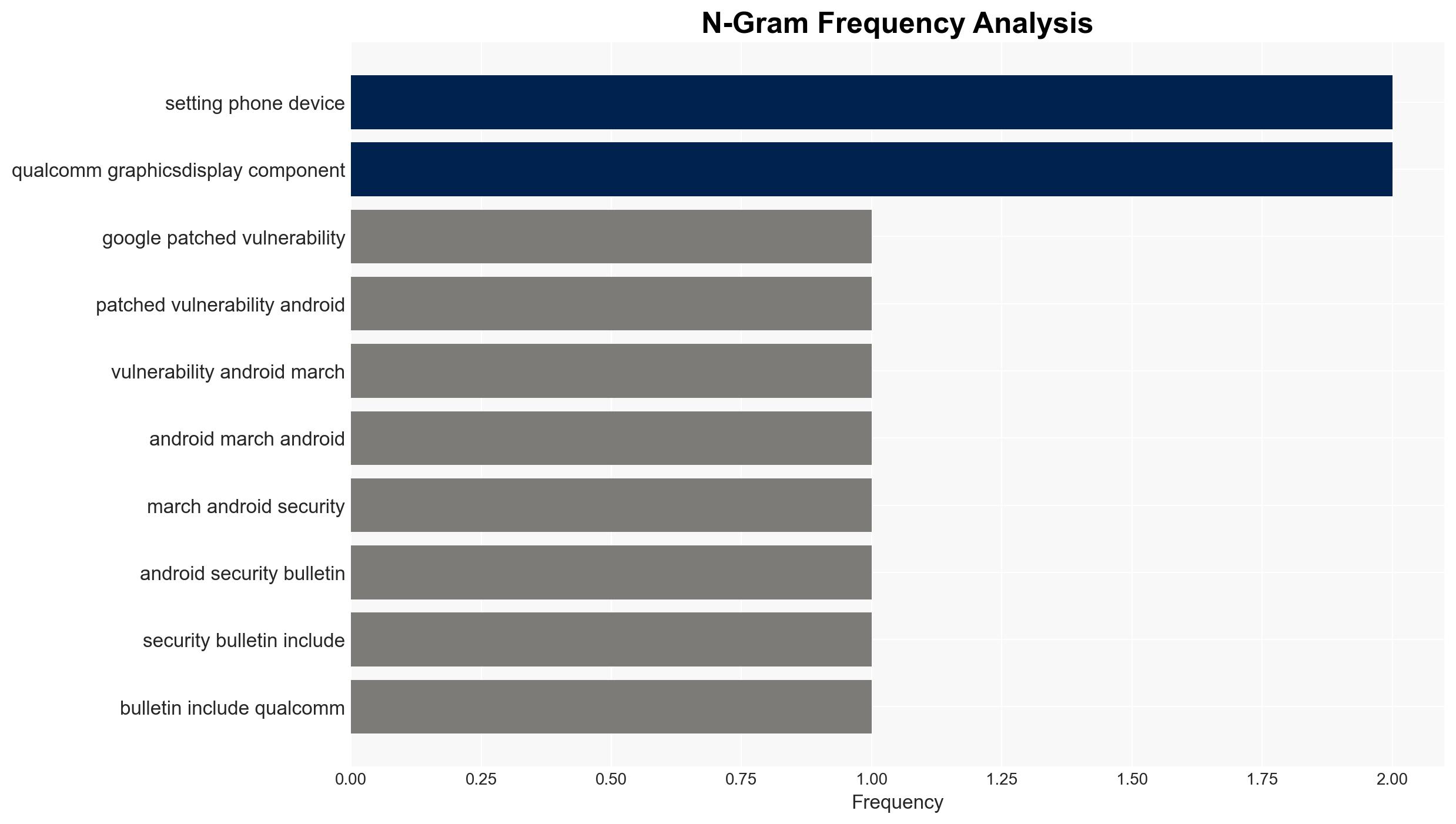
The CVE-2026-21385 vulnerability in Qualcomm graphics components poses a significant threat to Android devices globally, with targeted exploitation already observed. The issue potentially affects hundreds of millions of devices, particularly those using Qualcomm chipsets. The most likely hypothesis is that this vulnerability is being used for targeted attacks on high-value individuals or entities. Overall confidence in this assessment is moderate due to existing information gaps and the complexity of the threat landscape.
2. Competing Hypotheses
- Hypothesis A: The vulnerability is being exploited primarily for targeted attacks on high-value targets. This is supported by Google’s indication of “limited, targeted exploitation” and the complexity of the attack vector, which suggests a focus on specific, high-impact targets rather than widespread attacks. However, the exact scope and nature of these targets remain unclear.
- Hypothesis B: The vulnerability could be used for broader attacks if attackers find ways to automate or simplify the exploitation process. This hypothesis is less supported due to the current need for a local foothold and the complexity of the attack chain, which makes mass exploitation less feasible at this time.
- Assessment: Hypothesis A is currently better supported given the evidence of targeted exploitation and the technical barriers to widespread attacks. Indicators that could shift this judgment include reports of broader exploitation or new methods that lower the complexity of attacks.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability affects a significant portion of Android devices globally; attackers require a local foothold to exploit the vulnerability; patching will mitigate the vulnerability effectively.
- Information Gaps: Specific details on the identity and nature of the targets; comprehensive data on the number of affected devices; insights into the attackers’ capabilities and intentions.
- Bias & Deception Risks: Potential bias in reporting due to reliance on vendor-provided information; risk of deception if attackers are using misinformation to mask broader exploitation efforts.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of Android device security and potential geopolitical tensions if state actors are involved. The vulnerability’s exploitation could evolve into a broader threat if attackers develop more efficient methods.
- Political / Geopolitical: Potential for diplomatic tensions if linked to state-sponsored actors targeting foreign entities.
- Security / Counter-Terrorism: Increased risk to national security if high-value targets are compromised, potentially affecting intelligence operations.
- Cyber / Information Space: Heightened awareness and urgency in cybersecurity measures for Android devices, with potential for increased cyber defense spending.
- Economic / Social: Potential economic impact on affected businesses and loss of consumer trust in Android devices.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage users to update devices promptly; increase monitoring for signs of exploitation; engage with Qualcomm and Google for further insights.
- Medium-Term Posture (1–12 months): Develop resilience measures for Android security; foster partnerships with tech companies for better vulnerability management; enhance public awareness campaigns.
- Scenario Outlook: Best: Vulnerability is contained through effective patching. Worst: Exploitation becomes widespread, affecting critical infrastructure. Most-Likely: Continued targeted attacks with gradual improvements in defense mechanisms.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, Android vulnerability, Qualcomm, targeted attacks, zero-day exploitation, mobile security, patch management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us