Congress Investigates Computer Vulnerabilities to Long-Standing TEMPEST Surveillance Techniques
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How Vulnerable Are Computers to an 80-Year-Old Spy Technique Congress Wants Answers
1. BLUF (Bottom Line Up Front)
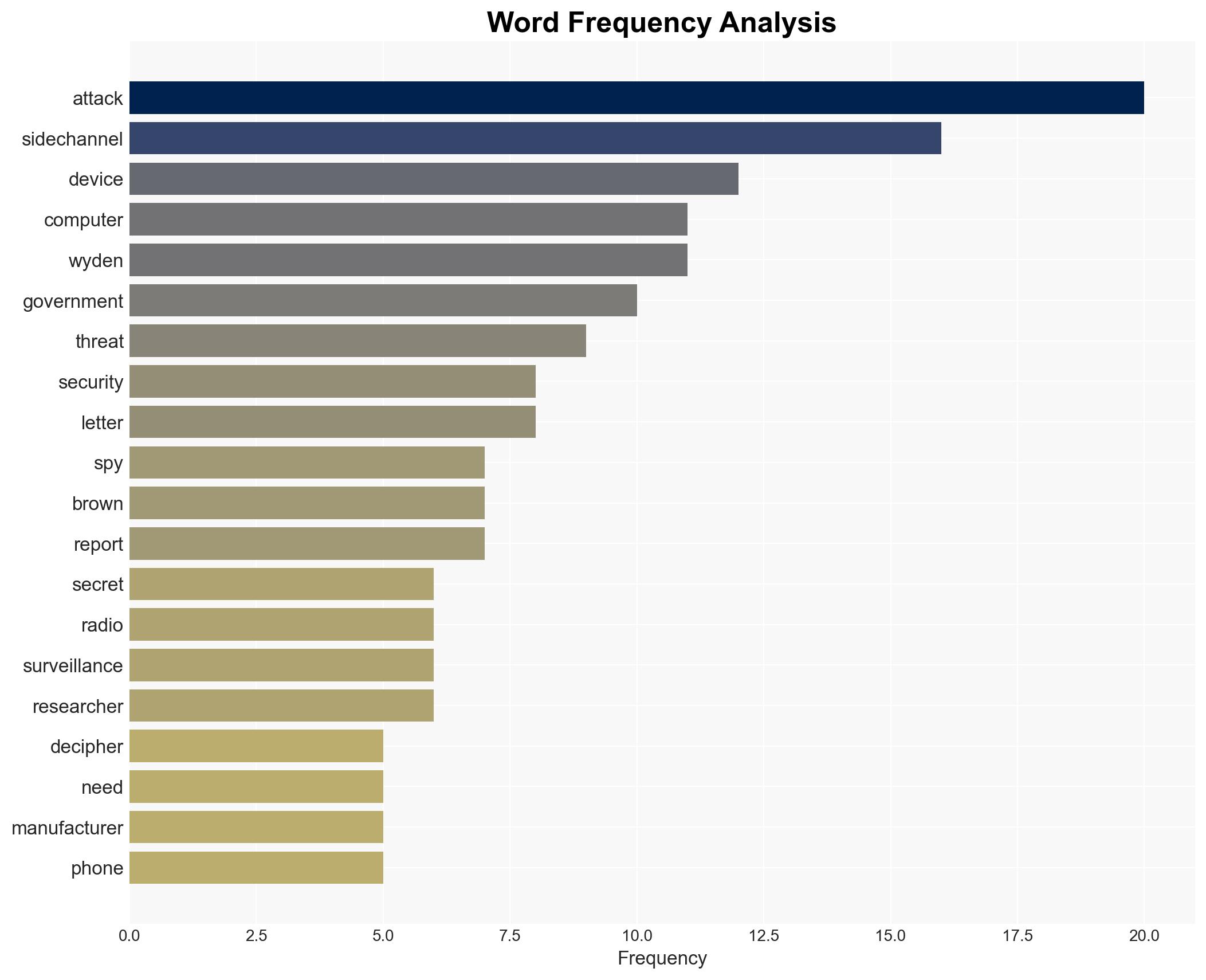
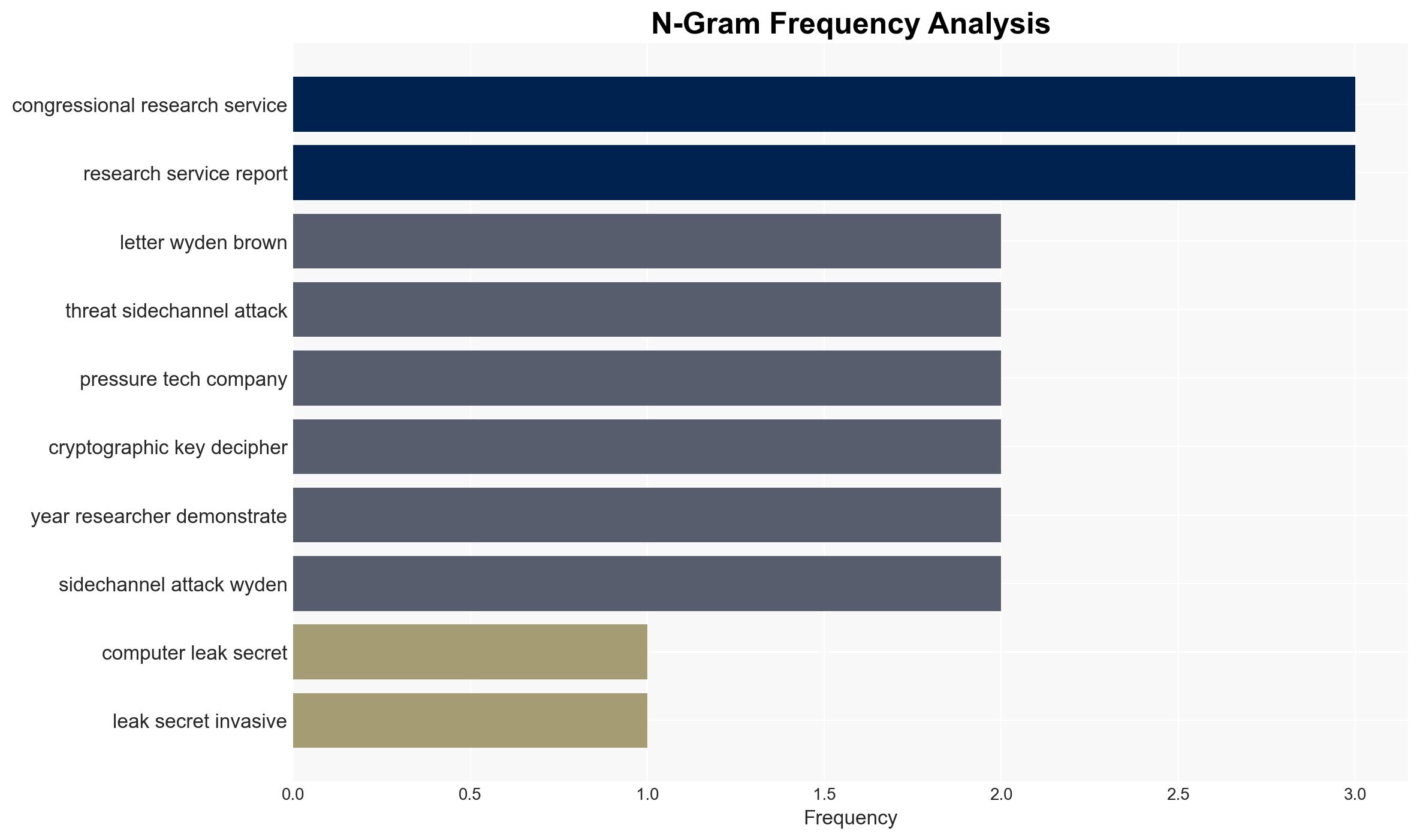
The investigation into TEMPEST-style side-channel attacks highlights a significant vulnerability in consumer electronics, potentially exposing sensitive data to adversaries. The current assessment suggests that these vulnerabilities pose a moderate risk to national security and economic interests, particularly if not addressed by manufacturers. Overall confidence in this judgment is moderate, pending further investigation by the GAO.
2. Competing Hypotheses
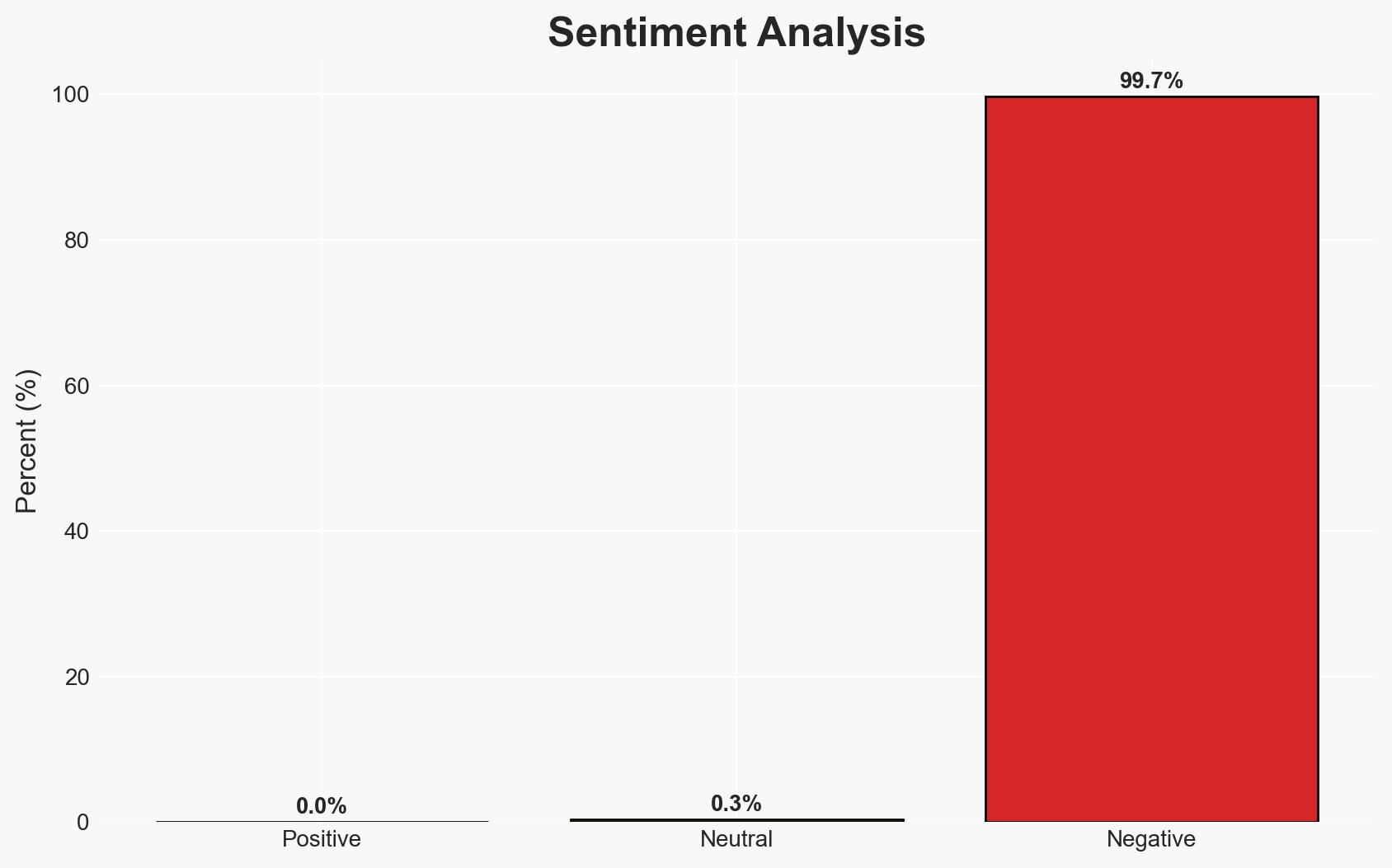
- Hypothesis A: TEMPEST-style side-channel attacks represent a significant and growing threat to both national security and private sector data integrity. Supporting evidence includes the historical use of these techniques and the lack of current consumer protections. However, the scale of the threat remains uncertain due to limited public awareness and technical understanding.
- Hypothesis B: The threat from TEMPEST-style attacks is overstated, with existing security measures and the technical complexity of such attacks limiting their practical impact. This hypothesis is supported by the absence of widespread reported incidents and the technical challenges involved in executing such attacks effectively.
- Assessment: Hypothesis A is currently better supported due to the proactive steps by lawmakers to investigate and the historical precedent of side-channel vulnerabilities. Indicators that could shift this judgment include new data on the frequency of such attacks or advancements in protective technologies.
3. Key Assumptions and Red Flags
- Assumptions: The technical feasibility of side-channel attacks remains high; adversaries have the capability and intent to exploit these vulnerabilities; current consumer electronics lack adequate protections.
- Information Gaps: Detailed data on the prevalence of side-channel attacks in the private sector; effectiveness of current mitigation strategies; adversary capabilities and intent.
- Bias & Deception Risks: Potential bias in the Congressional report towards highlighting vulnerabilities to justify regulatory action; risk of underestimating adversary capabilities due to lack of public incidents.
4. Implications and Strategic Risks
The investigation into side-channel vulnerabilities could lead to increased regulatory scrutiny and pressure on manufacturers to enhance security features. This may also prompt adversaries to accelerate their exploitation of these vulnerabilities before countermeasures are implemented.
- Political / Geopolitical: Potential for increased tensions with nations suspected of exploiting these vulnerabilities; legislative actions could impact international trade relations.
- Security / Counter-Terrorism: Enhanced risk of espionage and data theft targeting critical infrastructure and strategic industries.
- Cyber / Information Space: Increased focus on cybersecurity measures and public awareness campaigns; potential rise in cyber insurance costs.
- Economic / Social: Possible economic impact on technology companies due to increased compliance costs; public concern over privacy and data security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Initiate a comprehensive review of current consumer electronic vulnerabilities; engage with manufacturers to discuss potential security enhancements.
- Medium-Term Posture (1–12 months): Develop industry standards for side-channel attack mitigation; foster public-private partnerships to enhance cybersecurity resilience.
- Scenario Outlook:
- Best: Effective mitigation strategies are developed, reducing the threat level significantly.
- Worst: Adversaries exploit these vulnerabilities extensively before countermeasures are implemented, leading to significant data breaches.
- Most-Likely: Gradual implementation of security measures with intermittent incidents highlighting ongoing vulnerabilities.
6. Key Individuals and Entities
- Senator Ron Wyden
- Representative Shontel Brown
- Government Accountability Office (GAO)
- National Security Agency (NSA)
- Congressional Research Service
7. Thematic Tags
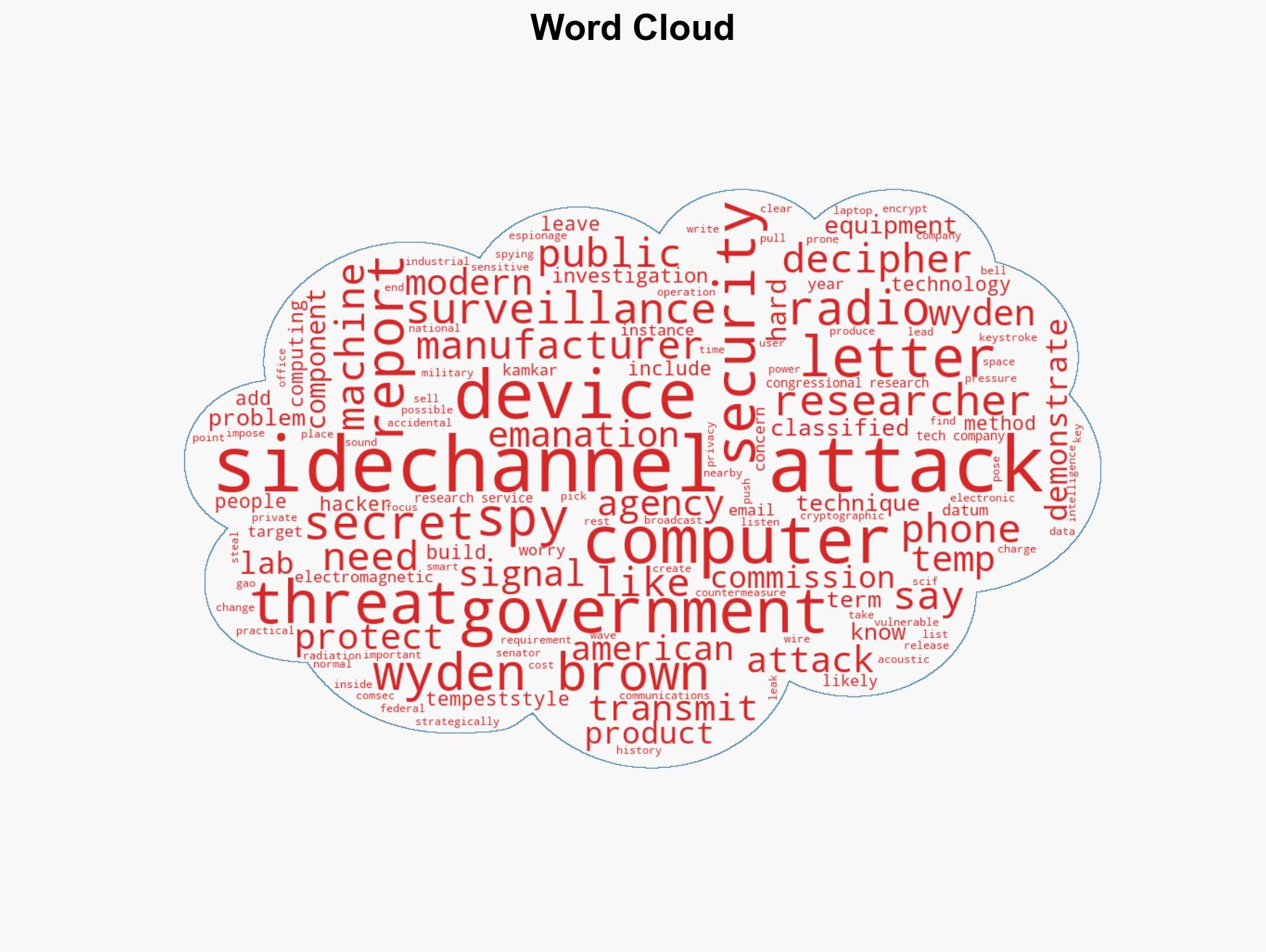
cybersecurity, side-channel attacks, national security, data privacy, regulatory policy, espionage, consumer electronics
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us