Identifying Gaps in Multi-Factor Authentication Coverage for Windows Credential Security
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Where Multi-Factor Authentication Stops and Credential Abuse Starts
1. BLUF (Bottom Line Up Front)
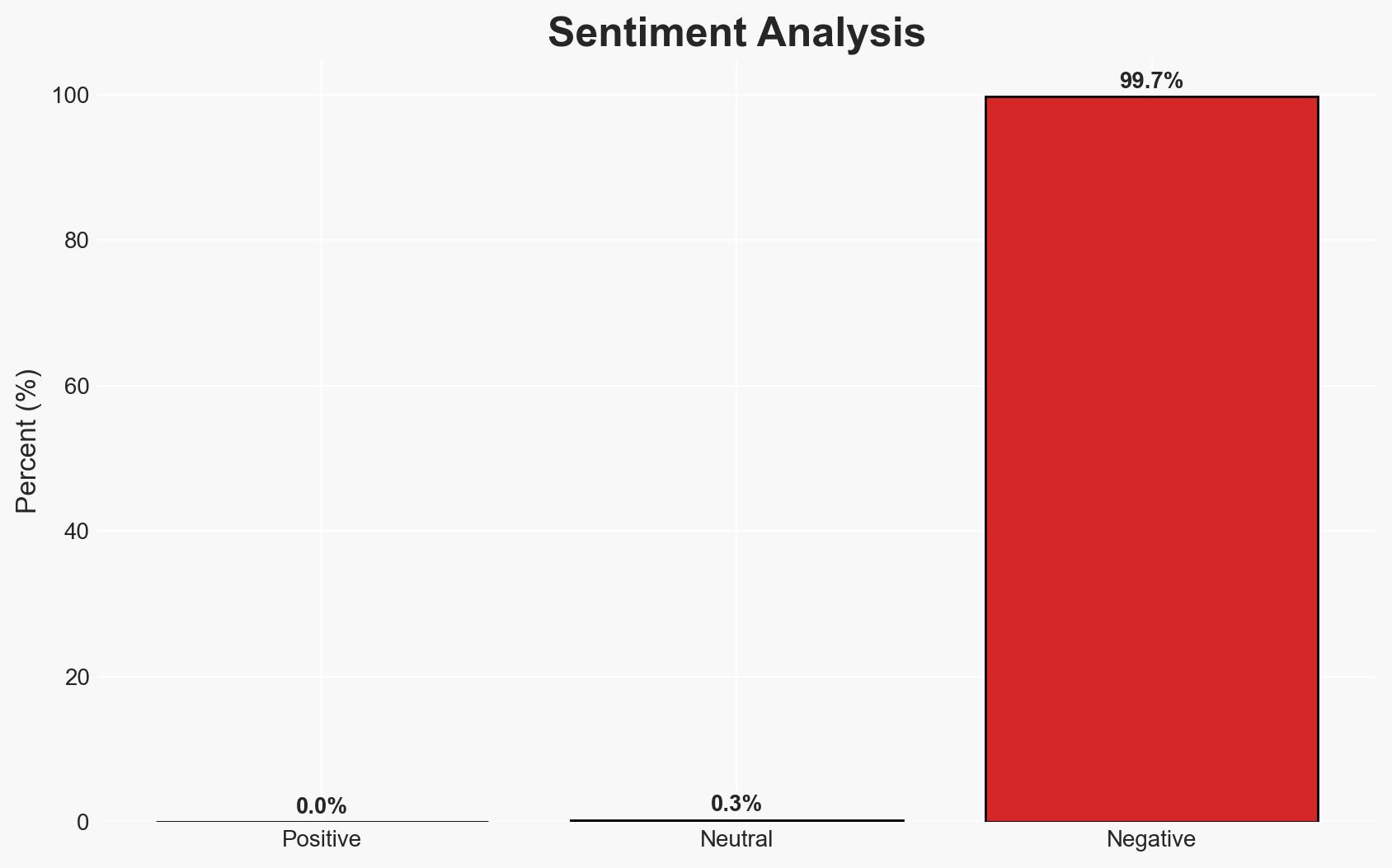
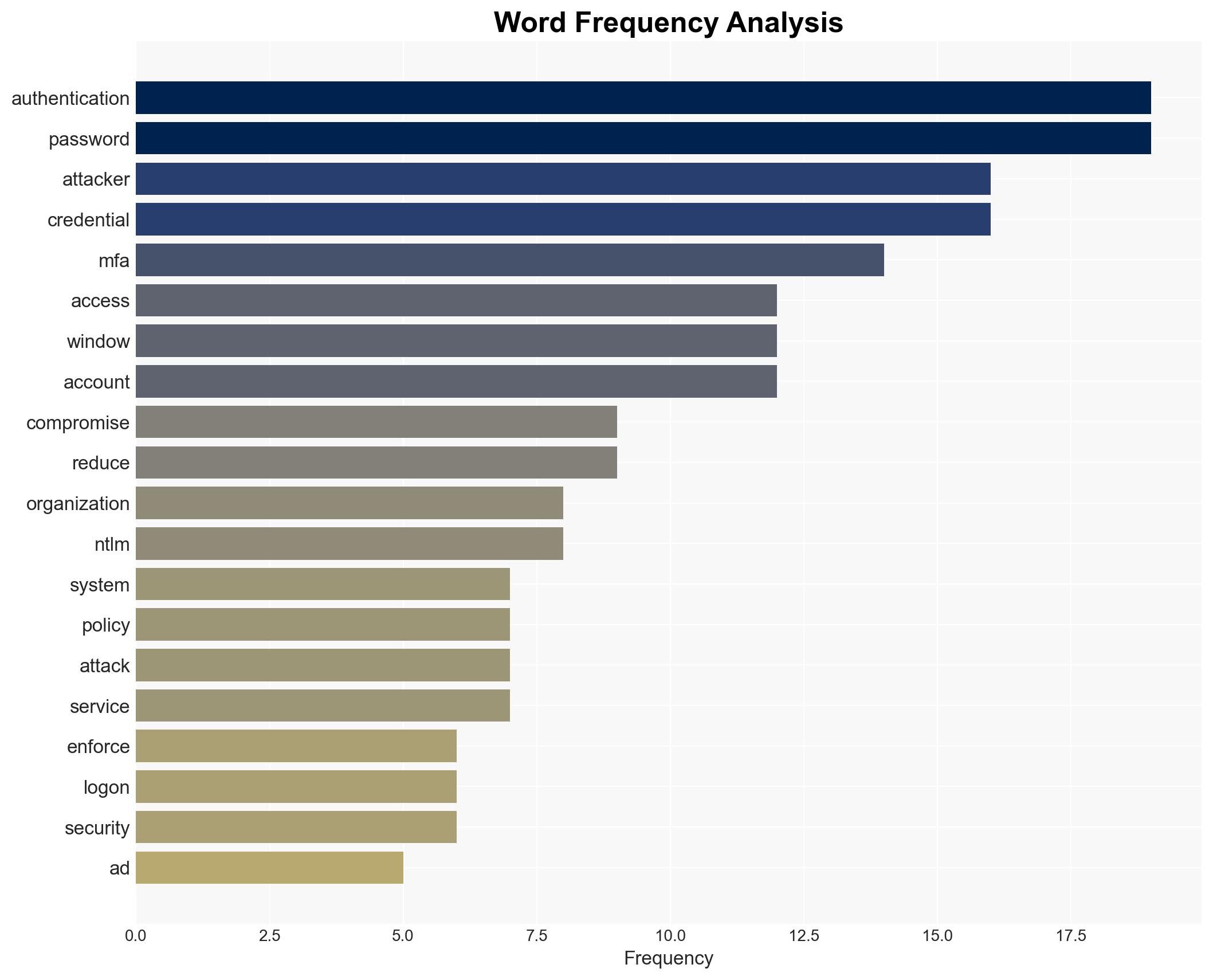
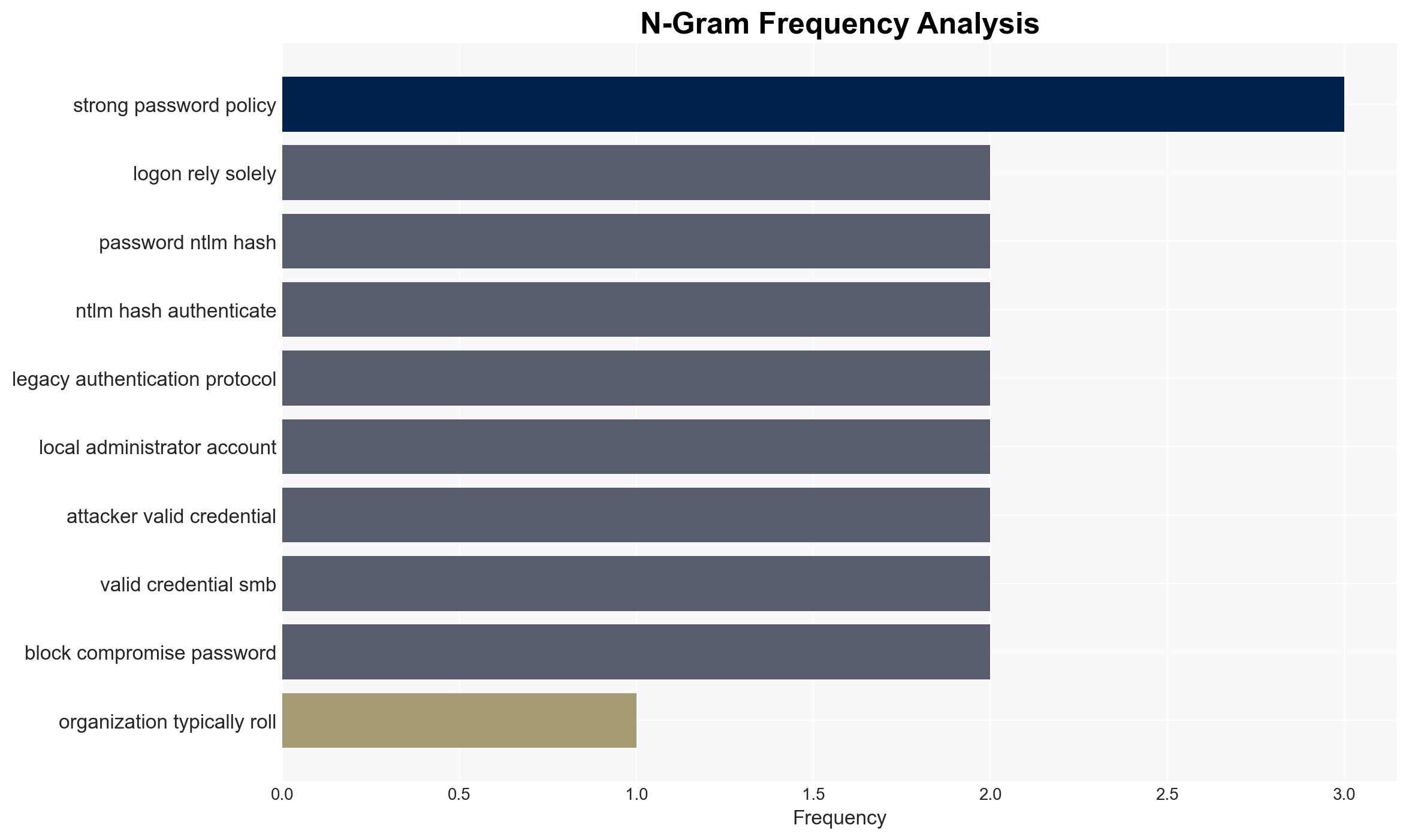
Credential abuse remains a significant threat in Windows environments despite the implementation of multi-factor authentication (MFA). The primary vulnerability arises from authentication paths that bypass MFA, particularly those relying on Active Directory (AD) and legacy protocols like NTLM. This affects organizations using Windows systems, with moderate confidence in the assessment due to potential information gaps regarding specific attack vectors and mitigation effectiveness.
2. Competing Hypotheses
- Hypothesis A: The primary issue is incomplete MFA coverage, allowing attackers to exploit AD and NTLM authentication paths. Evidence includes the continued use of legacy protocols and the lack of MFA prompts in certain logon scenarios. However, uncertainty exists around the extent of organizational awareness and mitigation efforts.
- Hypothesis B: The issue is not solely MFA coverage but also inadequate security practices and awareness within organizations. While MFA gaps are evident, this hypothesis suggests broader systemic issues, such as poor security hygiene and insufficient training, contribute significantly to credential abuse.
- Assessment: Hypothesis A is currently better supported due to specific evidence of MFA bypass through AD and NTLM. Key indicators that could shift this judgment include increased reports of successful mitigations or new vulnerabilities in MFA implementations.
3. Key Assumptions and Red Flags
- Assumptions: Organizations are aware of MFA limitations; attackers have the capability to exploit AD and NTLM; MFA is effectively implemented for cloud services.
- Information Gaps: Detailed data on the prevalence of credential abuse incidents and the effectiveness of specific mitigation tools like Specops Secure Access.
- Bias & Deception Risks: Potential bias in reporting from security tool vendors; lack of independent verification of mitigation effectiveness; possible underreporting of successful attacks.
4. Implications and Strategic Risks
The persistence of credential abuse in Windows environments could lead to increased security breaches, impacting organizational trust and operational integrity. Over time, this may necessitate broader security reforms and investments.
- Political / Geopolitical: Increased cyber threats could strain international relations, particularly if state-sponsored actors exploit these vulnerabilities.
- Security / Counter-Terrorism: Enhanced risk of unauthorized access to sensitive systems, potentially aiding espionage or sabotage efforts.
- Cyber / Information Space: Potential for increased cybercrime and data breaches, necessitating improved cybersecurity measures and awareness.
- Economic / Social: Financial losses from breaches and potential reputational damage could affect market positions and consumer trust.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct comprehensive audits of Windows authentication paths; implement tools like Specops Secure Access; enhance security training for IT staff.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms; invest in advanced threat detection systems; review and update security policies regularly.
- Scenario Outlook:
- Best: Successful mitigation of MFA gaps leads to reduced credential abuse incidents.
- Worst: Continued exploitation of MFA gaps results in significant data breaches and operational disruptions.
- Most-Likely: Incremental improvements in security posture reduce but do not eliminate credential abuse risks.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
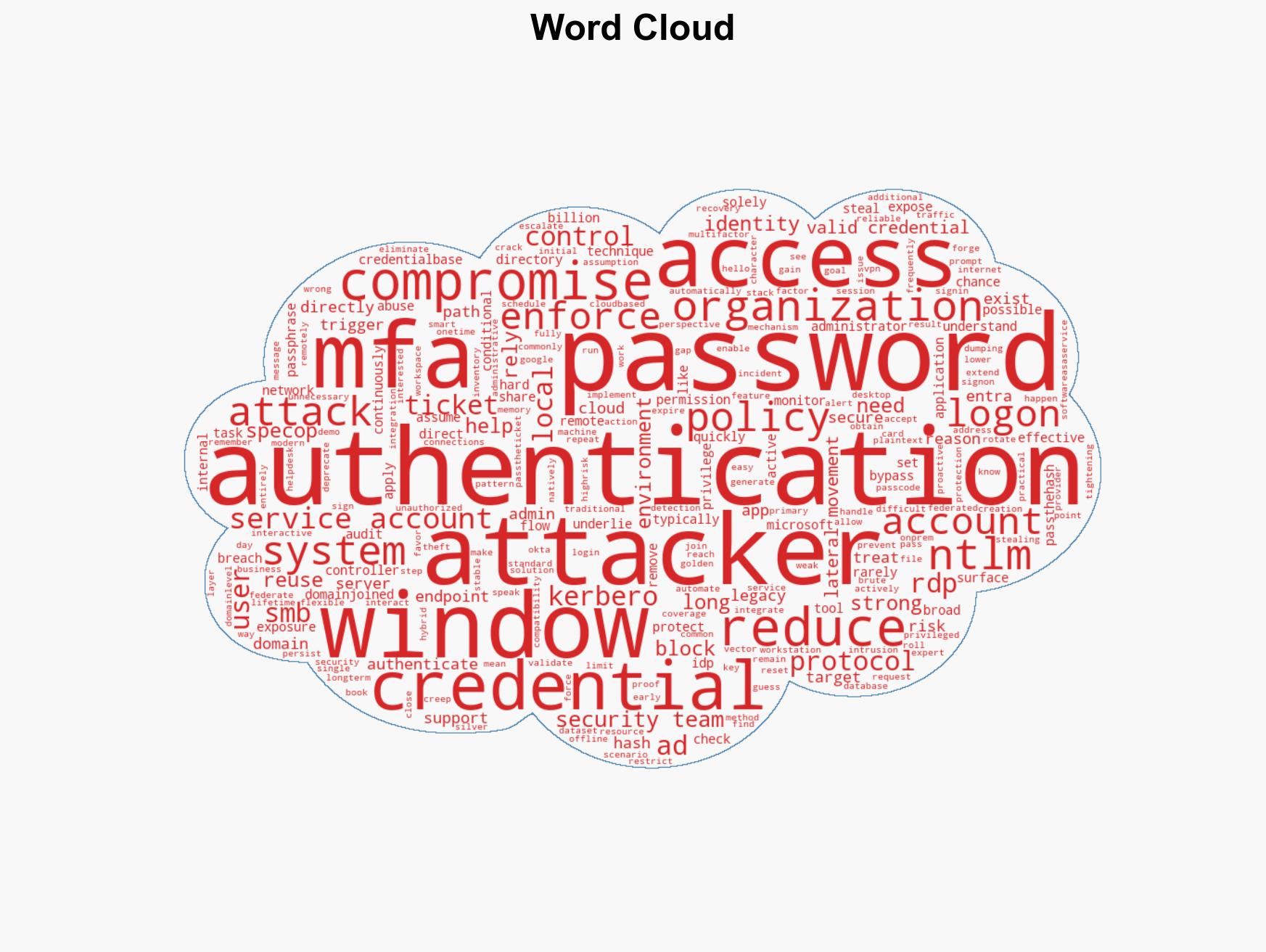
cybersecurity, multi-factor authentication, credential abuse, Windows environments, Active Directory, NTLM, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us