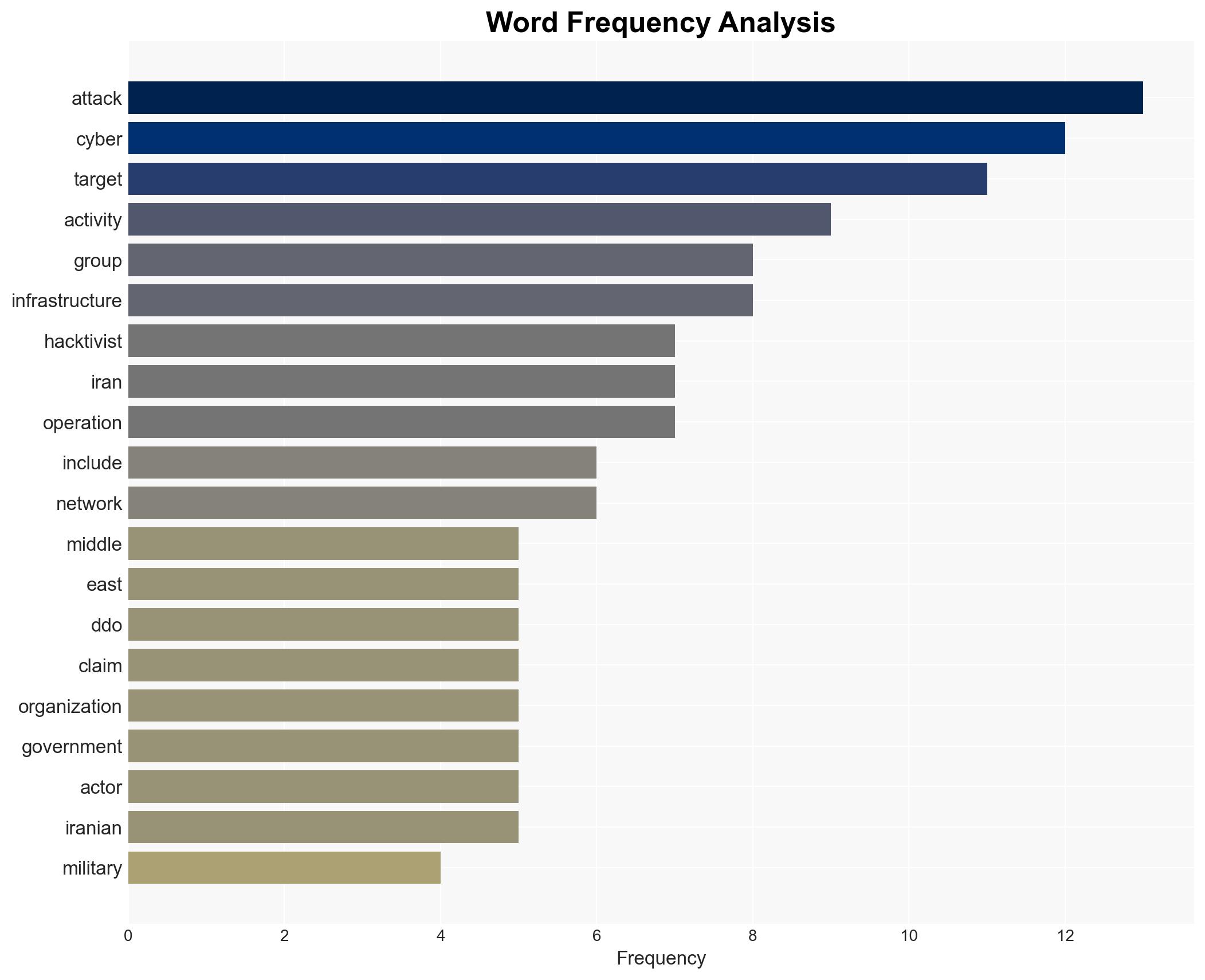
Surge in Hacktivist DDoS Attacks Targets 110 Organizations Across 16 Countries Amid Middle East Tensions
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: 149 Hacktivist DDoS Attacks Hit 110 Organizations in 16 Countries After Middle East Conflict
1. BLUF (Bottom Line Up Front)
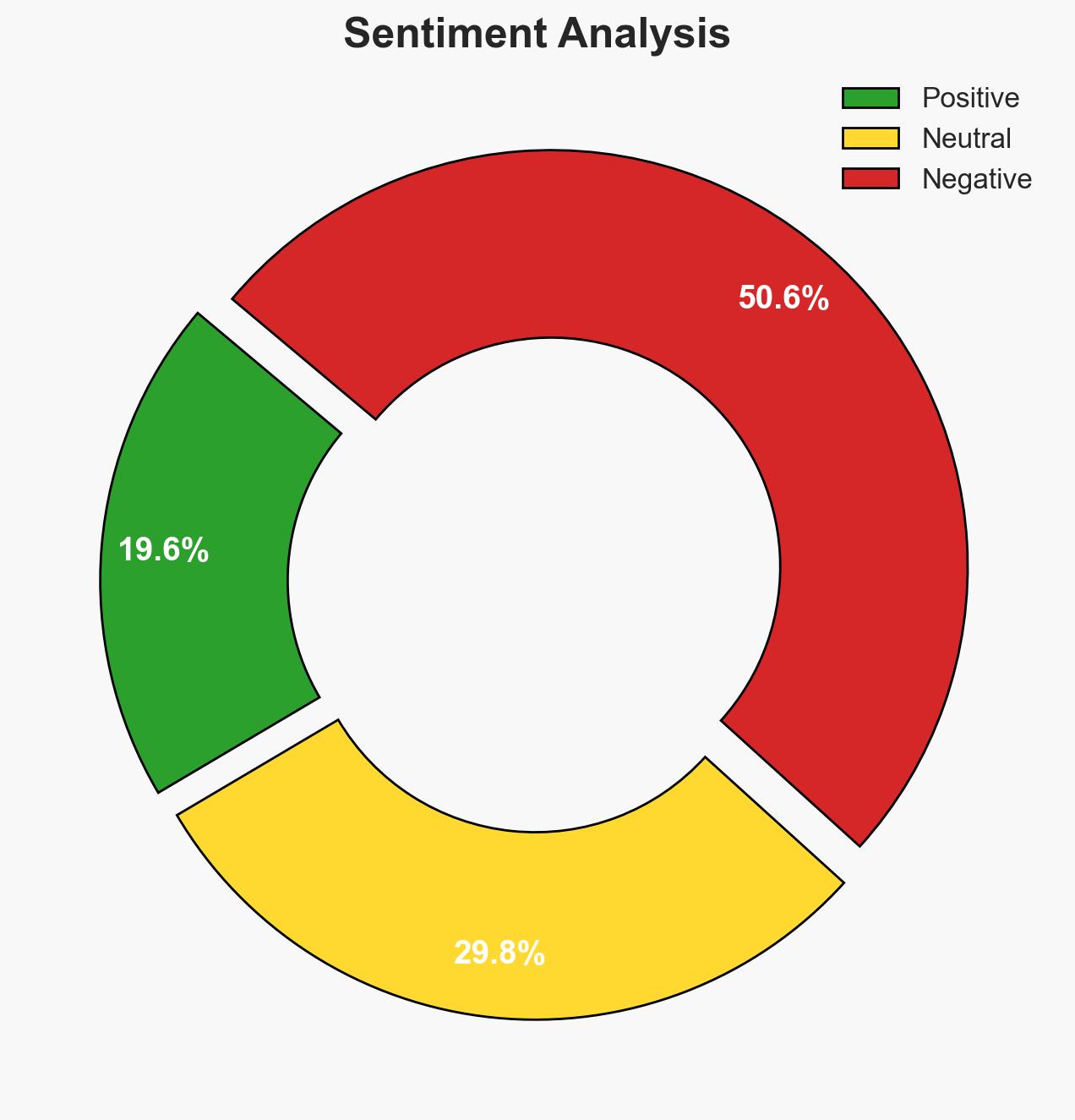
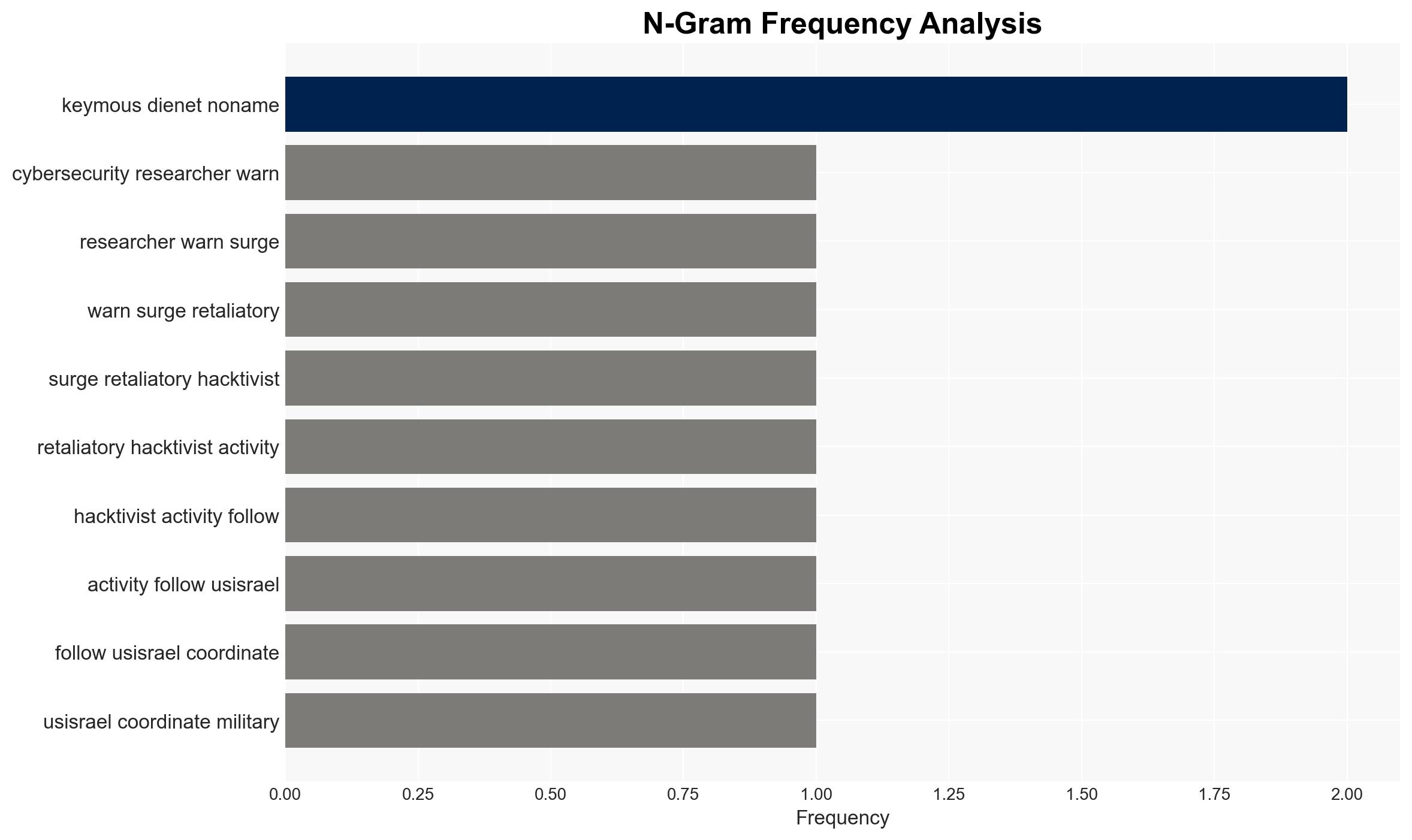
The recent surge in hacktivist DDoS attacks following the U.S.-Israel military campaign against Iran highlights a significant escalation in cyber activities targeting governmental and critical infrastructure sectors, predominantly in the Middle East. The most likely hypothesis is that these attacks are a coordinated retaliatory effort by pro-Palestinian and pro-Russian hacktivist groups. This assessment is made with moderate confidence due to the concentration of attacks and the involvement of known hacktivist entities.
2. Competing Hypotheses
- Hypothesis A: The DDoS attacks are a coordinated response by pro-Palestinian and pro-Russian hacktivist groups to the U.S.-Israel military actions. This is supported by the timing of the attacks, the groups involved, and the targets chosen. However, there is uncertainty about the level of coordination between different groups.
- Hypothesis B: The attacks are opportunistic actions by disparate hacktivist groups exploiting the geopolitical tension to advance their individual agendas. This is supported by the diversity of groups and the varying targets, but it does not fully explain the concentrated attack pattern.
- Assessment: Hypothesis A is currently better supported due to the alignment of attack timing with geopolitical events and the involvement of groups with known political motivations. Indicators such as increased communication between groups or a shift in target selection could alter this assessment.
3. Key Assumptions and Red Flags
- Assumptions: The hacktivist groups have the capability to sustain prolonged cyber operations; the geopolitical events directly influence hacktivist motivations; the reported data accurately reflects the scope and scale of attacks.
- Information Gaps: Specific motivations and coordination mechanisms between hacktivist groups; detailed attribution of individual attacks; the full extent of damage caused by the attacks.
- Bias & Deception Risks: Potential bias in reporting from cybersecurity firms with vested interests; possible exaggeration of attack impacts by hacktivist groups for propaganda purposes.
4. Implications and Strategic Risks
The escalation of hacktivist activities could lead to increased geopolitical tensions and a broader cyber conflict involving state and non-state actors. The digital front is becoming a critical battleground, influencing political, security, and economic stability in the region.
- Political / Geopolitical: Potential for increased diplomatic tensions and retaliatory cyber operations between involved nations.
- Security / Counter-Terrorism: Heightened threat environment with potential spillover into physical security domains.
- Cyber / Information Space: Expansion of cyber conflict, with increased sophistication and frequency of attacks on critical infrastructure.
- Economic / Social: Disruption of services in targeted sectors could lead to economic instability and social unrest in affected regions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats, increase collaboration with international cybersecurity agencies, and implement immediate defensive measures for critical infrastructure.
- Medium-Term Posture (1–12 months): Develop resilience strategies, strengthen public-private partnerships, and invest in cybersecurity capability development.
- Scenario Outlook: Best: De-escalation of cyber activities with diplomatic interventions. Worst: Escalation into a broader cyber conflict affecting global stability. Most-Likely: Continued sporadic attacks with periodic escalations aligned with geopolitical events.
6. Key Individuals and Entities
- Keymous+, DieNet, NoName057(16), Hider Nex (Tunisian Maskers Cyber Force), Nation of Saviors (NOS), Conquerors Electronic Army (CEA), Cardinal, Russian Legion
7. Thematic Tags
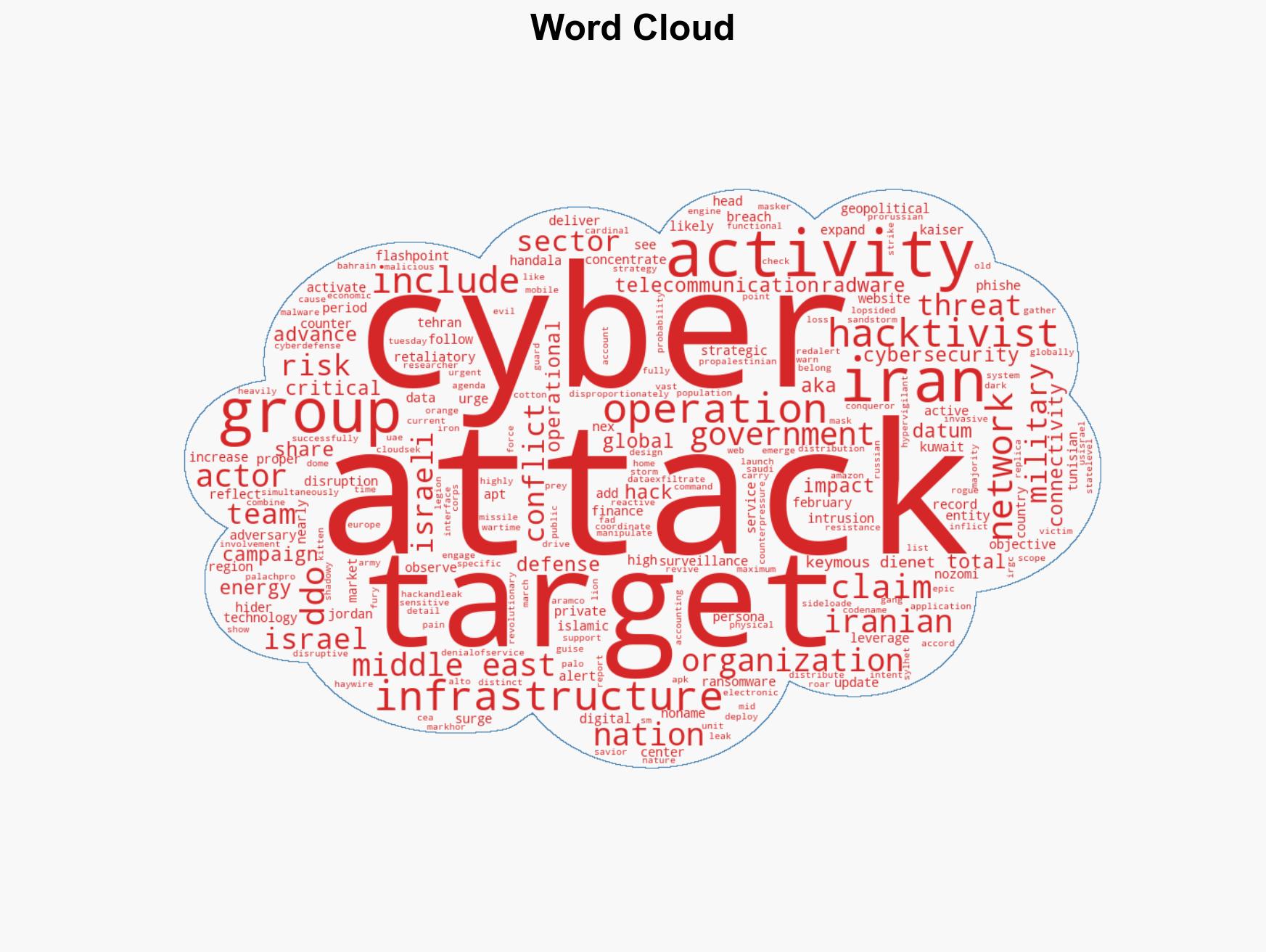
cybersecurity, hacktivism, cyber warfare, Middle East conflict, geopolitical tensions, critical infrastructure, cyber defense, pro-Palestinian
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us