Phishing Attack Targets Edge Users with Fake Google Security Prompt to Steal Data Without Exploits
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
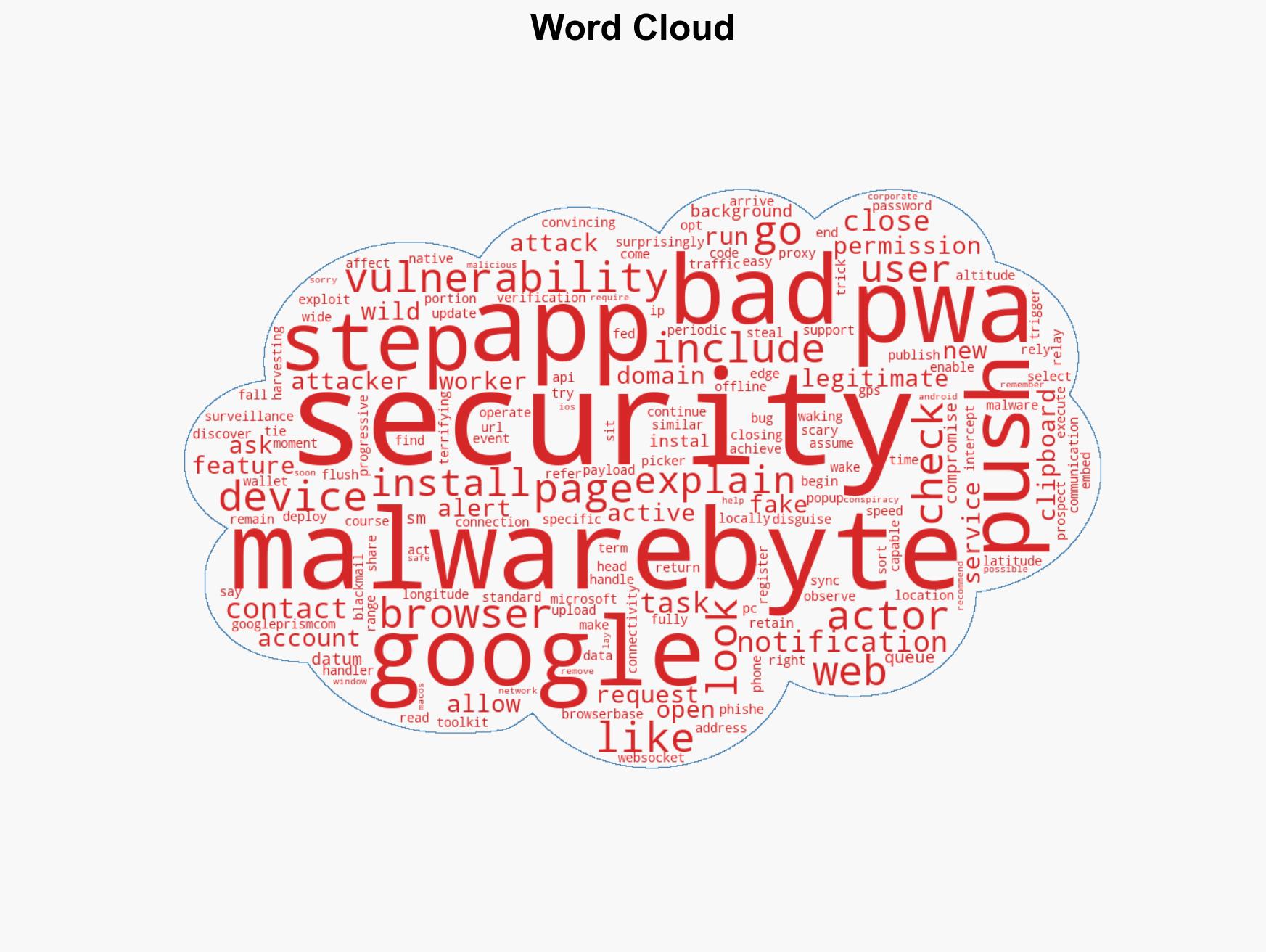
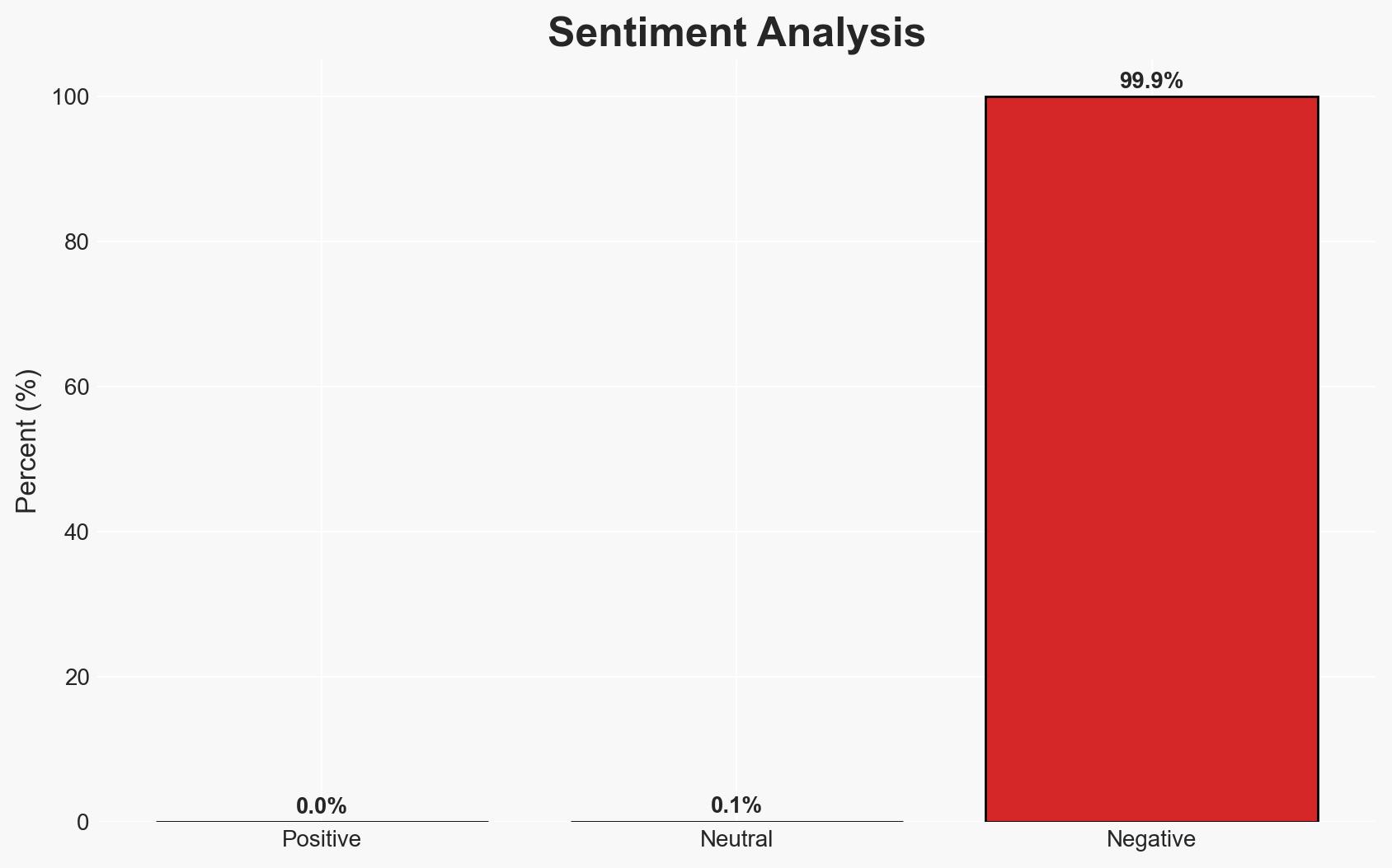
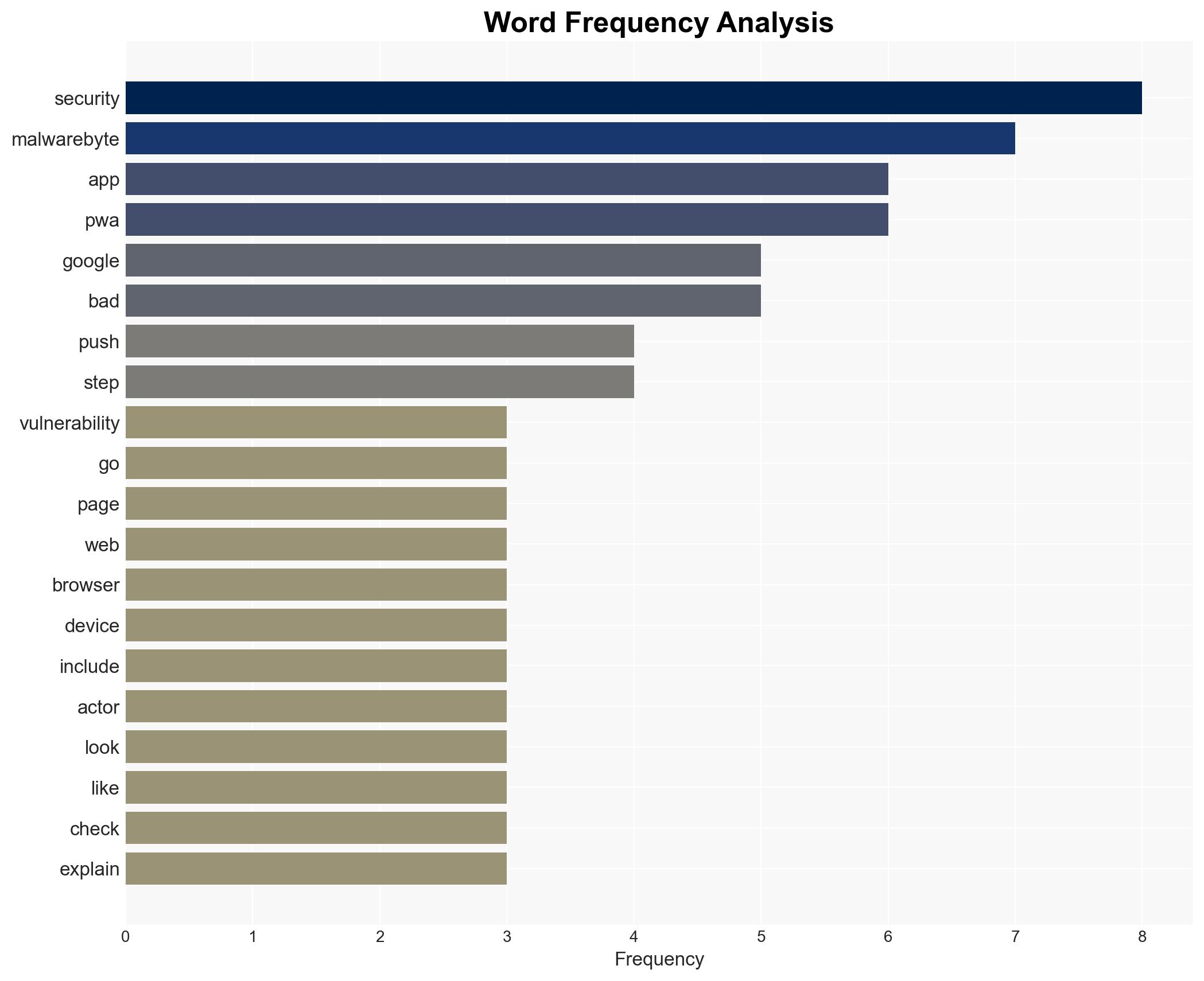
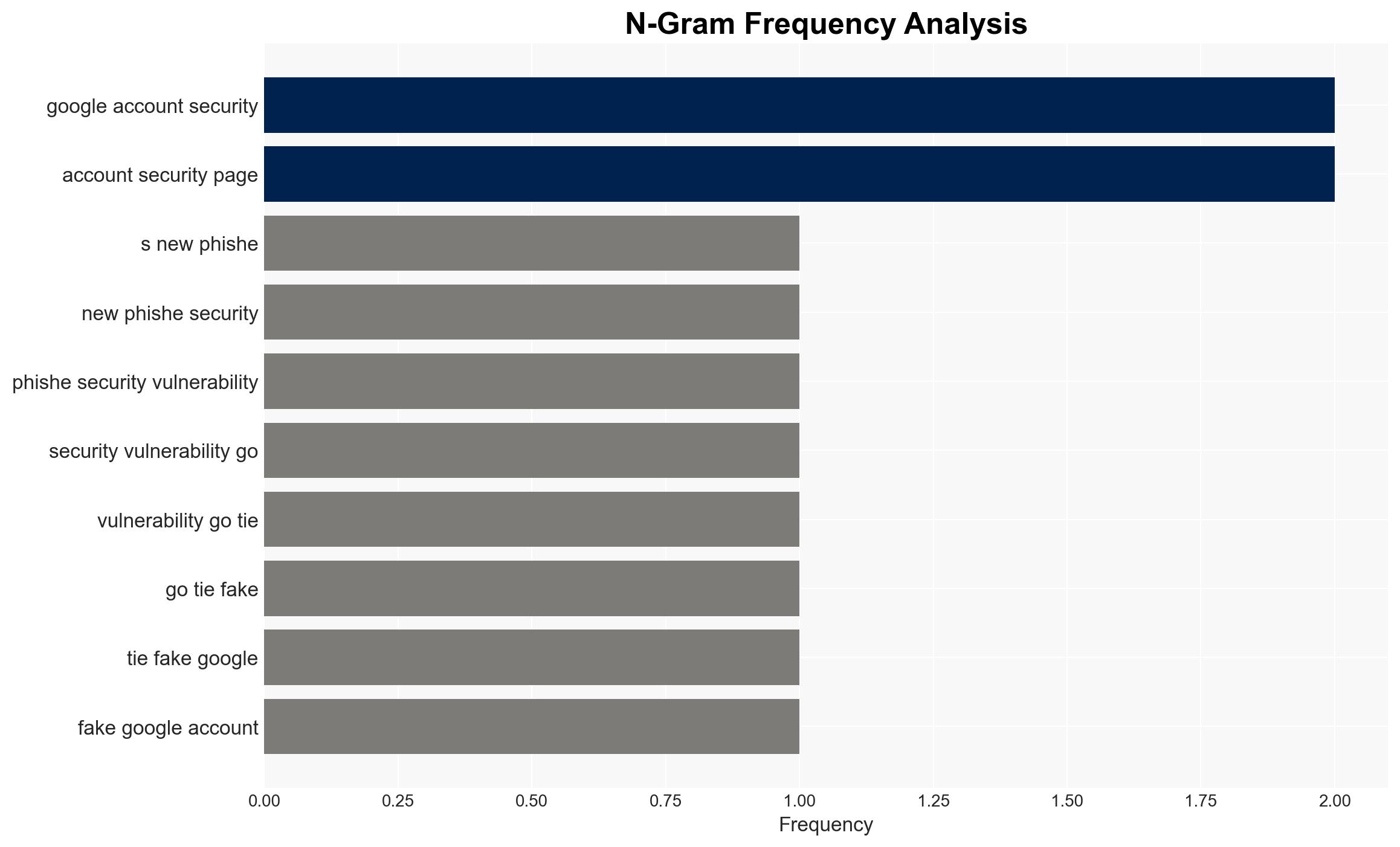
Intelligence Report: Edge users are being targeted by a fake Google security prompt that steals data No bug or exploit required makes this hack particularly nasty
1. BLUF (Bottom Line Up Front)
A sophisticated phishing campaign is targeting users across multiple platforms, exploiting a fake Google security prompt to deploy a surveillance toolkit. This attack, which does not rely on traditional vulnerabilities, poses a significant threat to user privacy and data integrity. The most likely hypothesis is that this is a financially motivated cybercrime operation. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The campaign is primarily financially motivated, aiming to harvest sensitive data for resale or direct financial exploitation. This is supported by the comprehensive data collection methods and the lack of a specific exploit, making it accessible to a wide range of threat actors. Key uncertainties include the identity and location of the perpetrators.
- Hypothesis B: The campaign is state-sponsored, intended for espionage or political manipulation. This could be supported by the sophisticated nature of the toolkit and the potential for data to be used in geopolitical contexts. However, the lack of direct evidence linking to state actors contradicts this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the broad targeting and typical financial motivations associated with similar phishing operations. Indicators that could shift this judgment include evidence of targeted attacks on specific political or governmental entities.
3. Key Assumptions and Red Flags
- Assumptions: The attackers are motivated by financial gain; the phishing toolkit is widely distributed and not limited to specific targets; users are unaware of the fake security prompt.
- Information Gaps: The identity and location of the attackers; the full scope of affected users; potential connections to larger cybercrime networks.
- Bias & Deception Risks: Confirmation bias towards financial motivations; potential manipulation of open-source reporting by the attackers to obscure true intent.
4. Implications and Strategic Risks
This development could lead to increased scrutiny on web security practices and user education, potentially influencing regulatory measures and cybersecurity policies.
- Political / Geopolitical: Potential for diplomatic tensions if state-sponsored involvement is suspected.
- Security / Counter-Terrorism: Increased threat to personal and organizational data security, requiring enhanced defensive measures.
- Cyber / Information Space: Highlights vulnerabilities in user awareness and the need for improved cybersecurity education.
- Economic / Social: Potential financial losses for individuals and businesses; erosion of trust in digital services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of phishing campaigns; enhance public awareness and education on identifying fake security prompts; collaborate with tech companies to block malicious domains.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in user education programs; strengthen regulatory frameworks for digital security.
- Scenario Outlook:
- Best: Rapid identification and neutralization of the threat, leading to minimal impact.
- Worst: Prolonged exploitation resulting in significant data breaches and financial losses.
- Most-Likely: Continued phishing attempts with moderate success, prompting ongoing defensive measures.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, phishing, data privacy, financial crime, digital security, user awareness, cyber-espionage
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us