Pentagon identifies final two U.S. soldiers killed in Kuwait drone strike, bringing total to six fatalities
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Last 2 names of 6 US soldiers who died in Kuwait attack identified by the Pentagon
1. BLUF (Bottom Line Up Front)
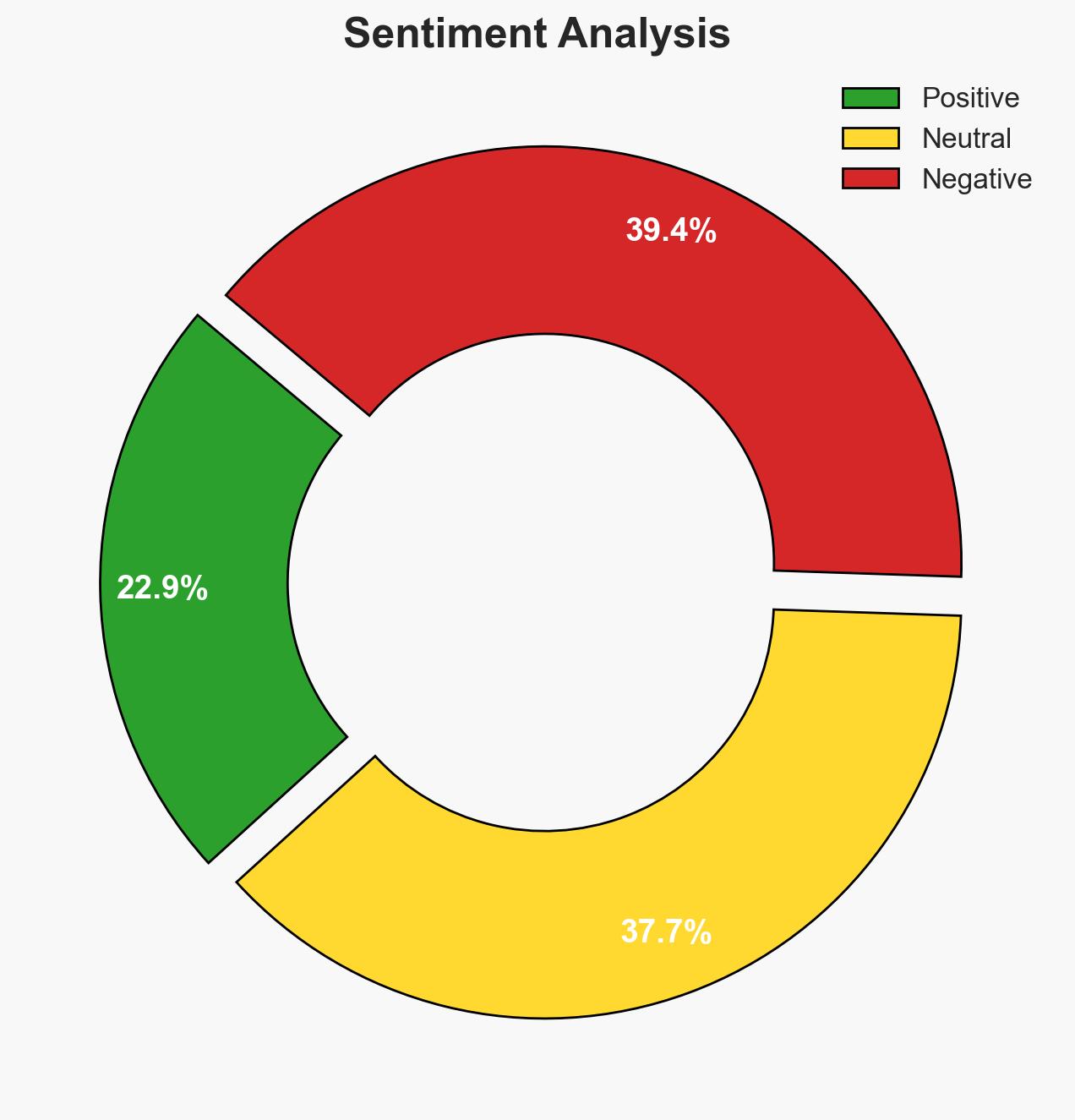
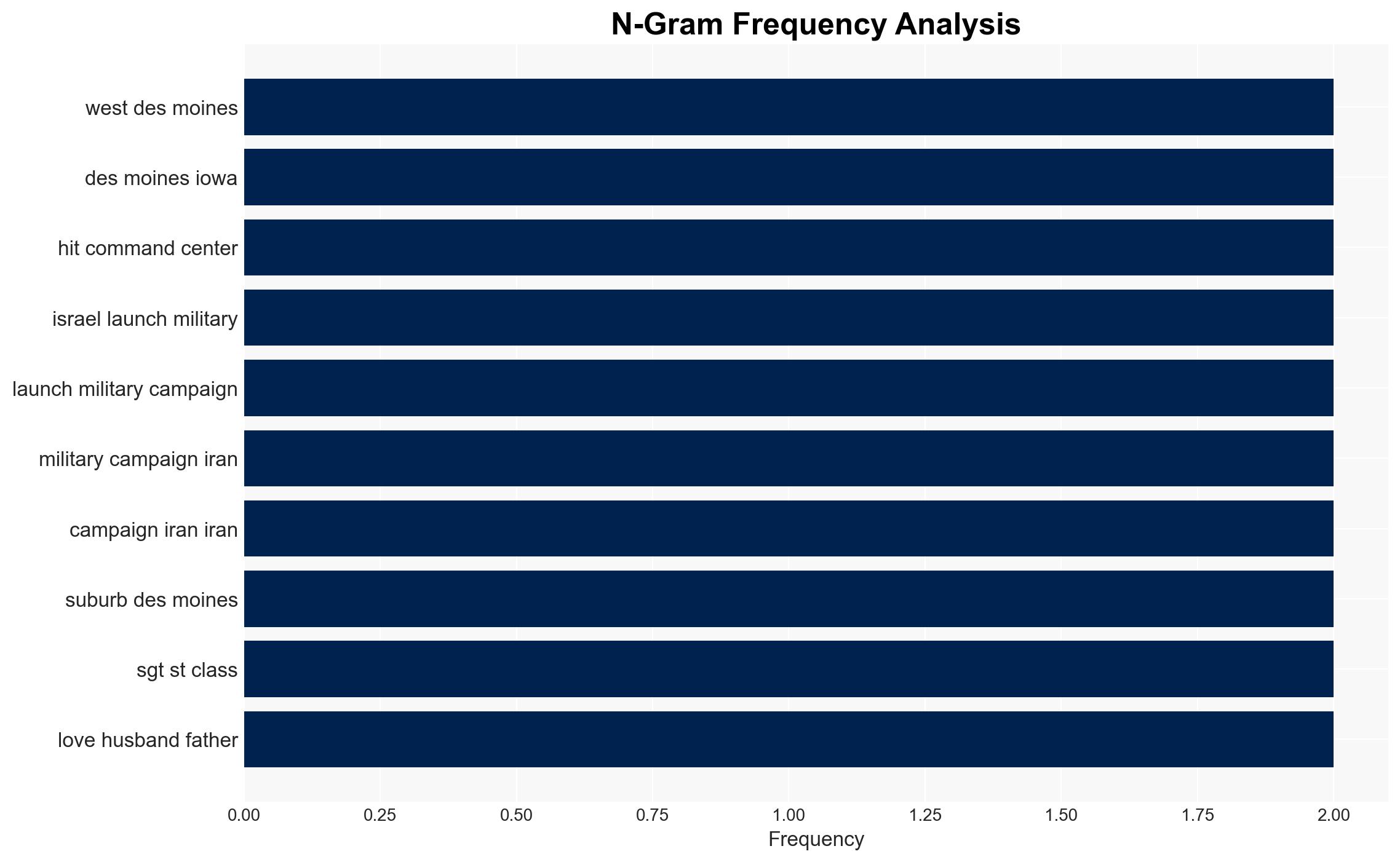
The identification of the last two U.S. soldiers killed in a drone strike in Kuwait highlights escalating tensions following U.S. and Israeli military actions against Iran. The attack underscores potential vulnerabilities in U.S. military logistics operations in the region. This assessment is made with moderate confidence, given the current geopolitical climate and available information.
2. Competing Hypotheses
- Hypothesis A: The drone strike was a direct retaliatory action by Iran in response to U.S. and Israeli military operations. This is supported by the timing of the attack and Iran’s known capabilities and willingness to use drones in asymmetric warfare. However, the specific targeting of logistics personnel may suggest a broader strategic aim.
- Hypothesis B: The attack was conducted by a proxy group with Iranian support, aiming to disrupt U.S. military operations in the Gulf region. This hypothesis is supported by Iran’s history of using proxies to achieve strategic objectives while maintaining plausible deniability. The lack of immediate claims of responsibility adds uncertainty.
- Assessment: Hypothesis A is currently better supported due to the direct correlation between the U.S.-Israeli actions and Iran’s retaliatory capabilities. Key indicators that could shift this judgment include claims of responsibility from non-state actors or evidence of proxy involvement.
3. Key Assumptions and Red Flags
- Assumptions: The attack was a direct response to U.S. and Israeli military actions; Iran has operational control over the drones used; U.S. military logistics operations are a strategic target.
- Information Gaps: Details on the drone’s origin and control, the specific strategic intent behind targeting logistics personnel, and any communications intercepts indicating Iranian or proxy involvement.
- Bias & Deception Risks: Potential confirmation bias in attributing the attack directly to Iran; source bias from regional actors; possible deception by Iran or proxies to obscure true operational control.
4. Implications and Strategic Risks
The attack could lead to increased military engagements in the region, affecting U.S. strategic posture and alliances. It may also prompt a reassessment of U.S. military logistics security and counter-drone capabilities.
- Political / Geopolitical: Potential escalation between U.S., Israel, and Iran, affecting regional stability and diplomatic relations.
- Security / Counter-Terrorism: Heightened threat environment for U.S. forces in the Gulf; potential for further asymmetric attacks.
- Cyber / Information Space: Increased risk of cyber operations targeting U.S. military infrastructure; potential information warfare to influence public perception.
- Economic / Social: Disruption of oil supply routes could impact global markets; increased regional instability may affect local economies and social cohesion.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance security protocols for U.S. military logistics; increase intelligence monitoring of Iranian and proxy communications; engage in diplomatic efforts to de-escalate tensions.
- Medium-Term Posture (1–12 months): Develop resilience measures against drone threats; strengthen regional alliances and partnerships; invest in counter-drone technology and capabilities.
- Scenario Outlook:
- Best Case: Diplomatic resolution reduces tensions, leading to decreased military engagements.
- Worst Case: Escalation leads to broader regional conflict involving multiple state and non-state actors.
- Most Likely: Continued low-intensity conflicts with sporadic retaliatory actions and diplomatic stalemates.
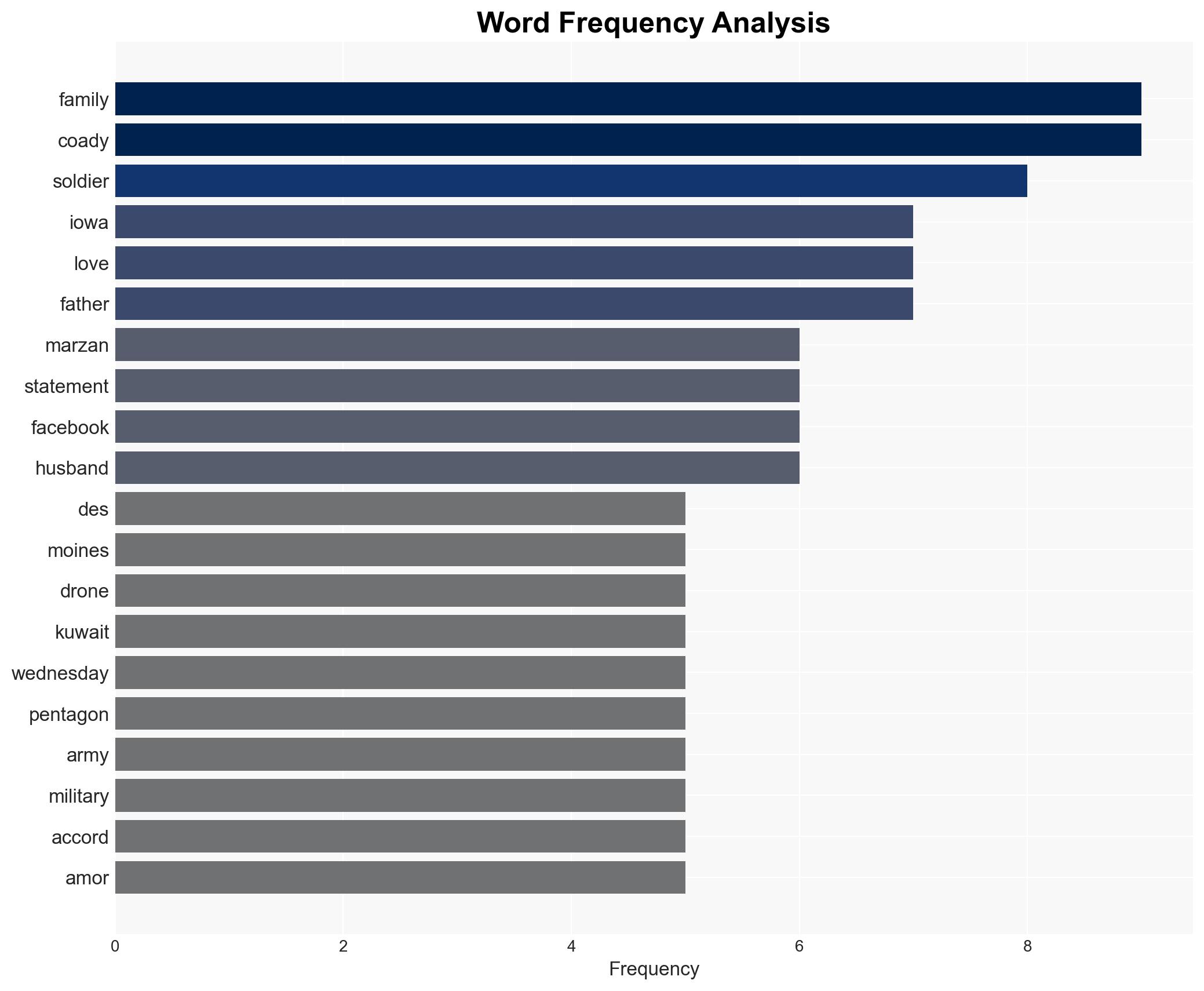
6. Key Individuals and Entities
- Chief Warrant Officer 3 Robert Marzan
- Maj. Jeffrey O’Brien
- Sgt. Declan Coady
- Sgt. 1st Class Nicole Amor
- Capt. Cody Khork
- Sgt. 1st Class Noah Tietjens
- 103rd Sustainment Command
7. Thematic Tags
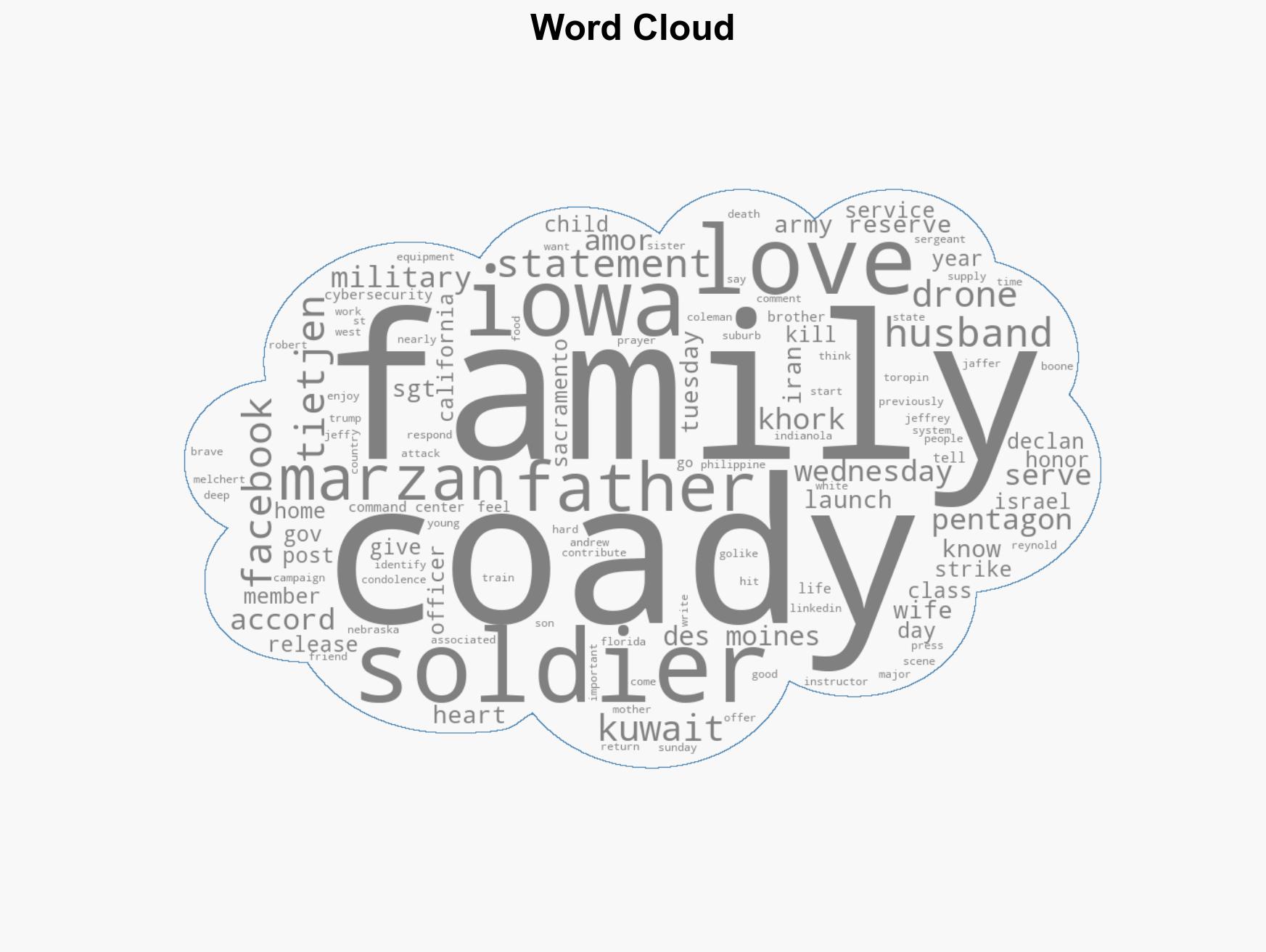
cybersecurity, military logistics, drone warfare, Iran-U.S. tensions, asymmetric warfare, regional stability, counter-terrorism, military strategy
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us