Europol Disrupts Major Data Breach Forum LeakBase in Global Law Enforcement Operation
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Europol Operation Seizes LeakBase Data Breach Site
1. BLUF (Bottom Line Up Front)
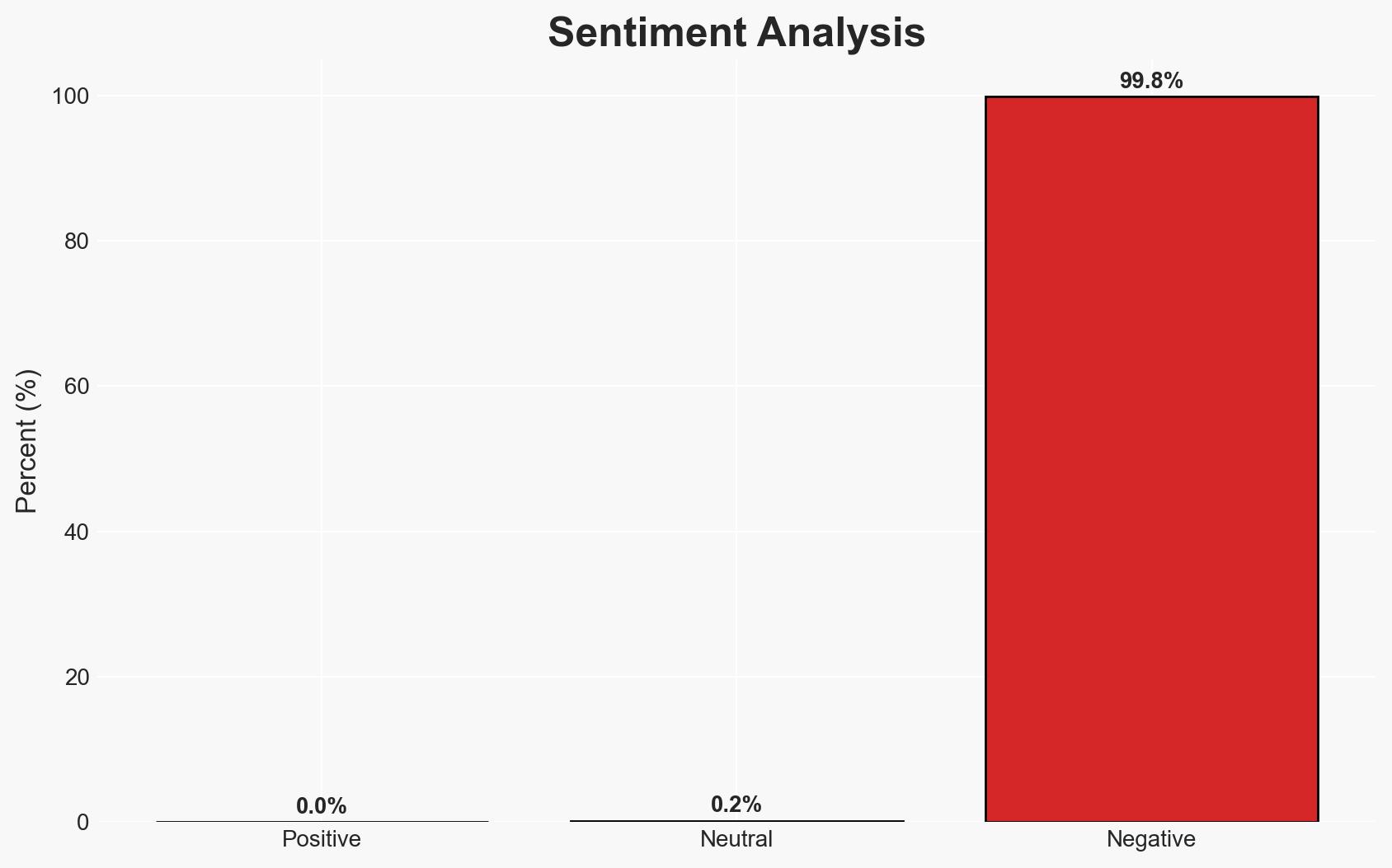
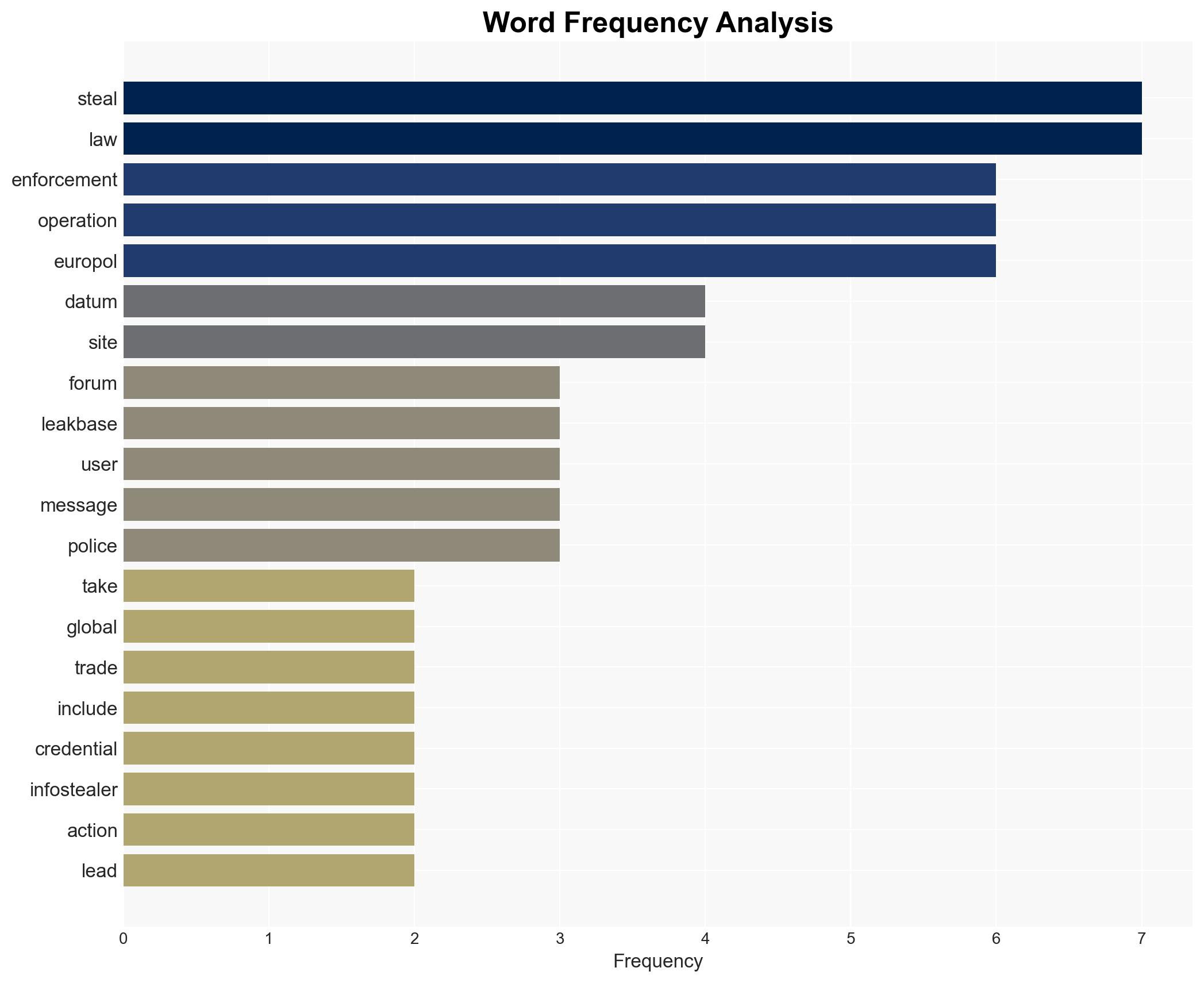
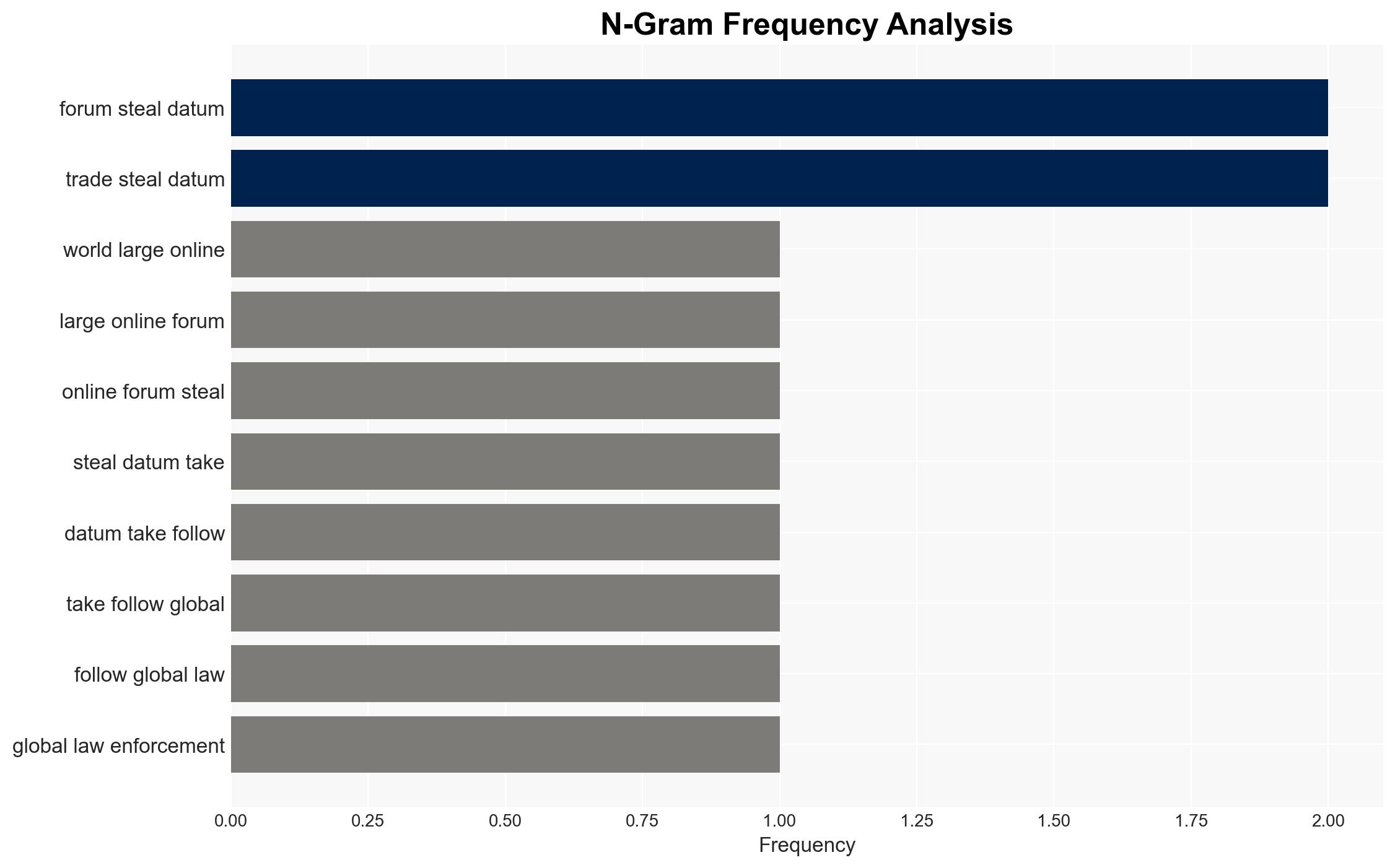
The Europol-coordinated operation successfully dismantled LeakBase, a major online forum for stolen data, impacting a significant portion of the cybercriminal ecosystem. This action underscores the increasing effectiveness of international law enforcement collaboration in combating cybercrime. The most likely hypothesis is that this operation will temporarily disrupt but not eliminate the trade in stolen data. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The takedown of LeakBase will significantly disrupt the illegal trade in stolen data. This is supported by the arrest of key users and the seizure of the forum’s customer database, which could lead to further arrests and deterrence. However, the persistence of similar forums suggests resilience in the cybercriminal community.
- Hypothesis B: The takedown will have a limited long-term impact, as cybercriminals will migrate to other platforms or create new ones. Past experiences with similar operations, such as the re-emergence of BreachForums, support this view.
- Assessment: Hypothesis B is currently better supported due to historical patterns of forum re-emergence and adaptation by cybercriminals. Indicators that could shift this judgment include sustained law enforcement pressure and successful prosecution of key individuals.
3. Key Assumptions and Red Flags
- Assumptions: Law enforcement will continue to prioritize cybercrime; cybercriminals will seek alternative platforms; the seized data will yield actionable intelligence.
- Information Gaps: Details on the specific identities and roles of arrested individuals; the extent of collaboration among international law enforcement agencies.
- Bias & Deception Risks: Potential overestimation of law enforcement impact due to Europol’s public statements; underestimation of cybercriminal adaptability.
4. Implications and Strategic Risks
This development may temporarily disrupt the cybercriminal ecosystem but is unlikely to eliminate the threat. Continued adaptation by cybercriminals could lead to new methods of data theft and distribution.
- Political / Geopolitical: Strengthened international law enforcement cooperation could enhance global cybersecurity efforts.
- Security / Counter-Terrorism: Potential reduction in immediate cyber threats, but long-term risks remain if new forums emerge.
- Cyber / Information Space: Possible shifts in cybercriminal tactics and increased use of encrypted or decentralized platforms.
- Economic / Social: Temporary reduction in data breaches may improve consumer confidence, but persistent threats could undermine long-term trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of alternative forums; analyze seized data for further leads; increase public awareness on data protection.
- Medium-Term Posture (1–12 months): Strengthen international partnerships; invest in advanced cyber threat intelligence capabilities; develop rapid response protocols for emerging threats.
- Scenario Outlook:
- Best: Sustained law enforcement pressure leads to a significant reduction in data breaches.
- Worst: New, more secure forums emerge, exacerbating the cybercrime problem.
- Most-Likely: Temporary disruption followed by adaptation and migration of cybercriminal activities.
6. Key Individuals and Entities
- Edvardas Šileris, Europol’s European Cybercrime Centre
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
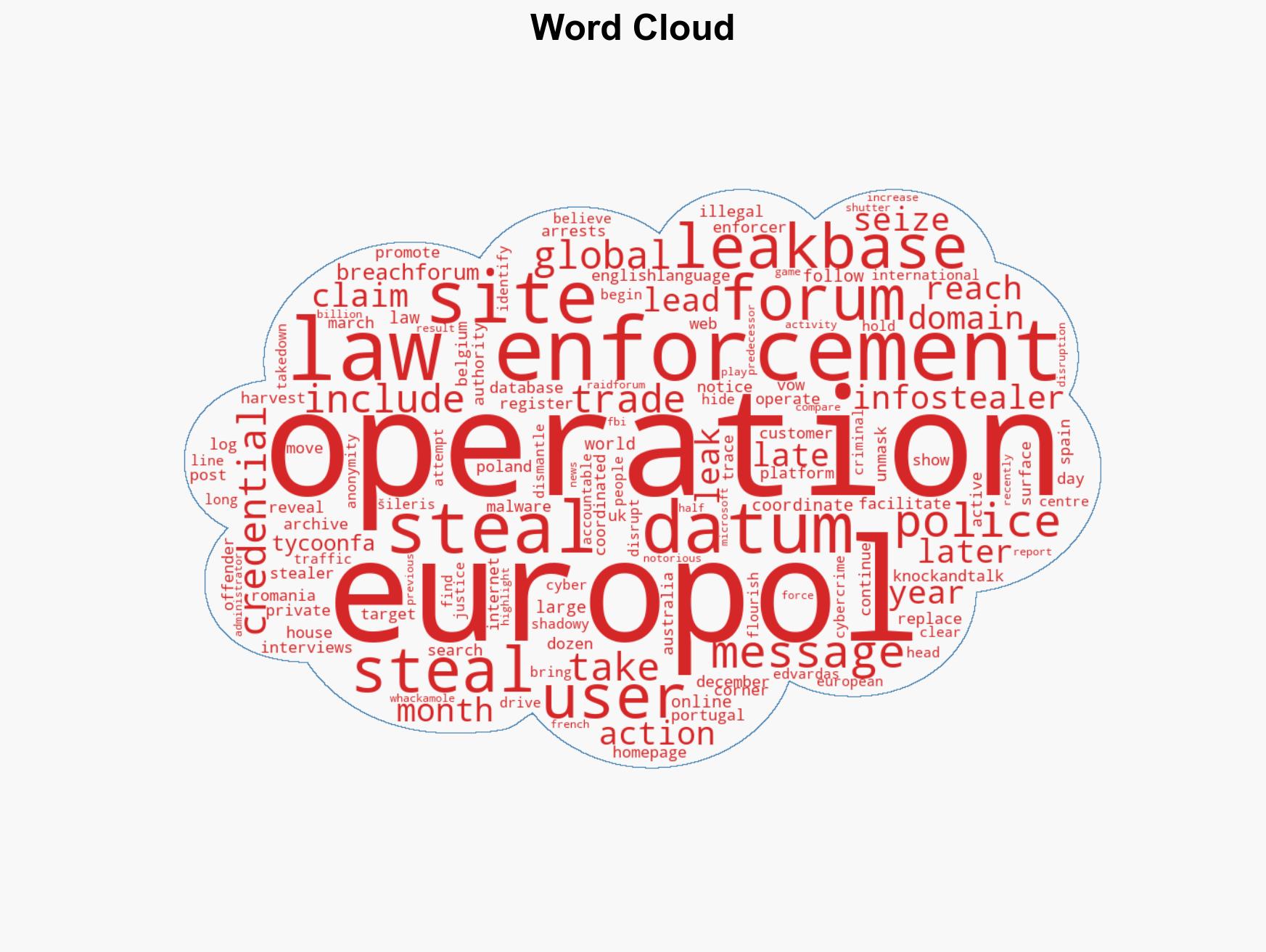
cybersecurity, cybercrime, data breach, law enforcement, international cooperation, cyber resilience, infostealer malware, cyber threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us