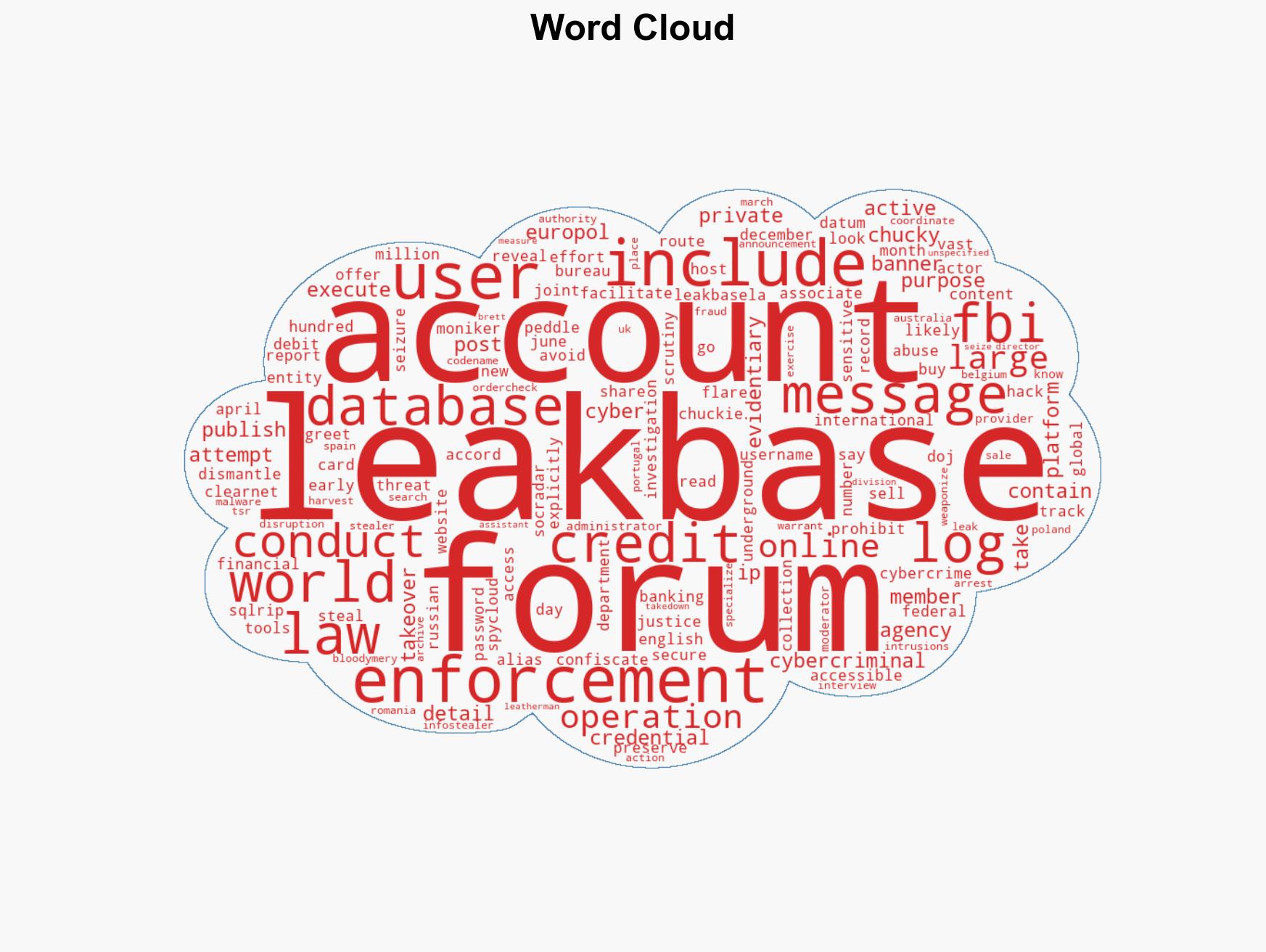
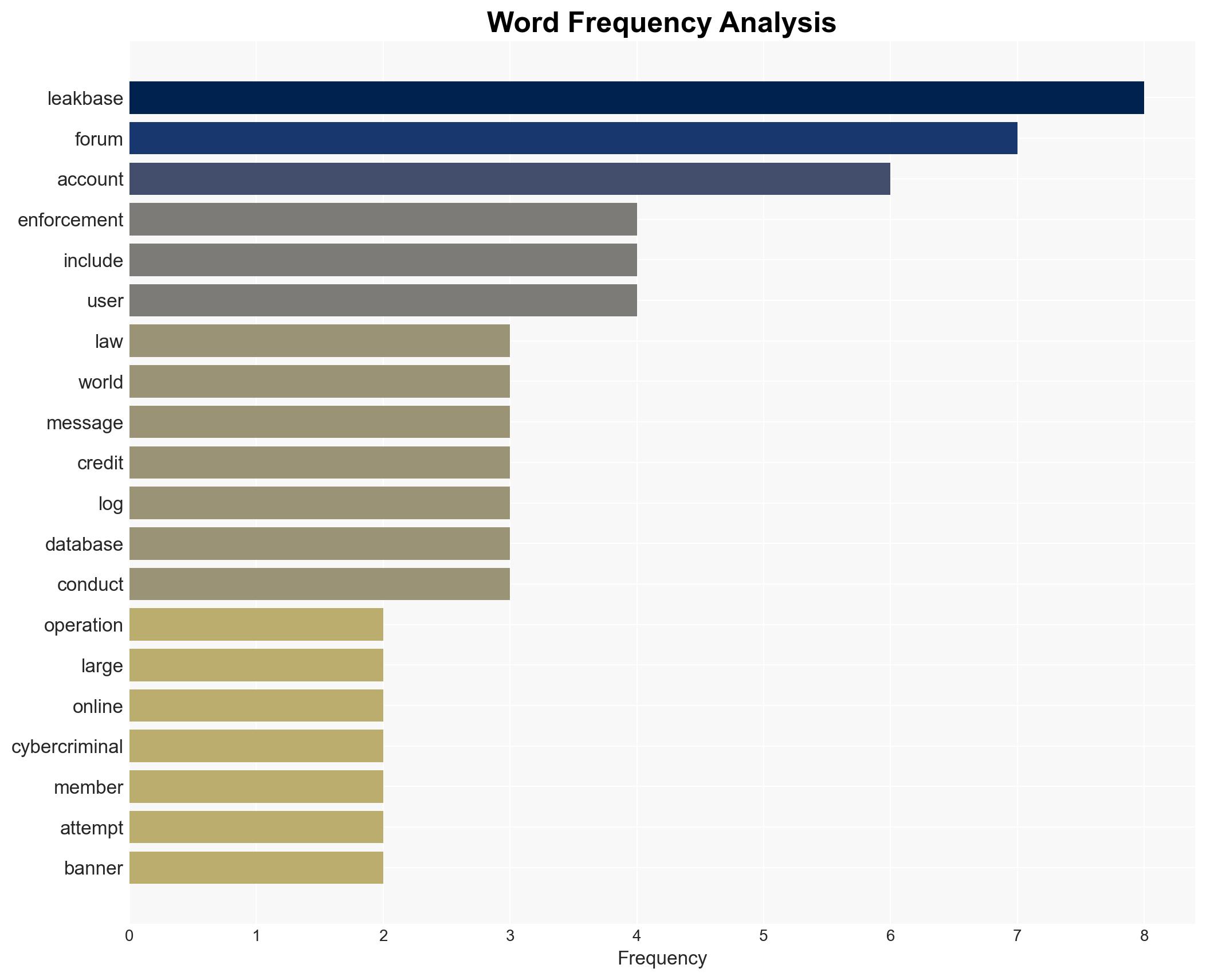
FBI and Europol Take Down Major Cybercrime Forum LeakBase, Securing Stolen Data and User Information
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: FBI and Europol Seize LeakBase Forum Used to Trade Stolen Credentials
1. BLUF (Bottom Line Up Front)
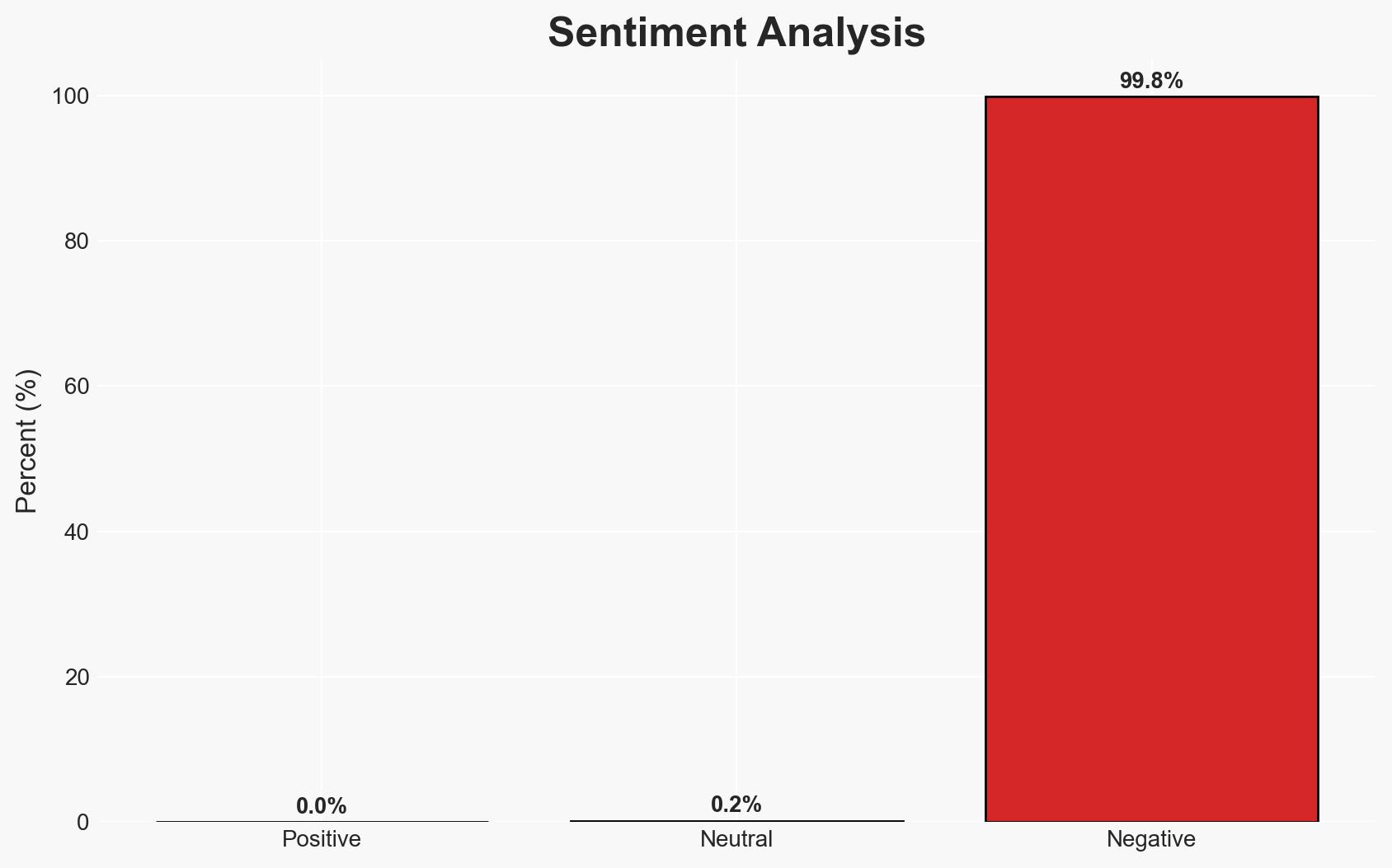
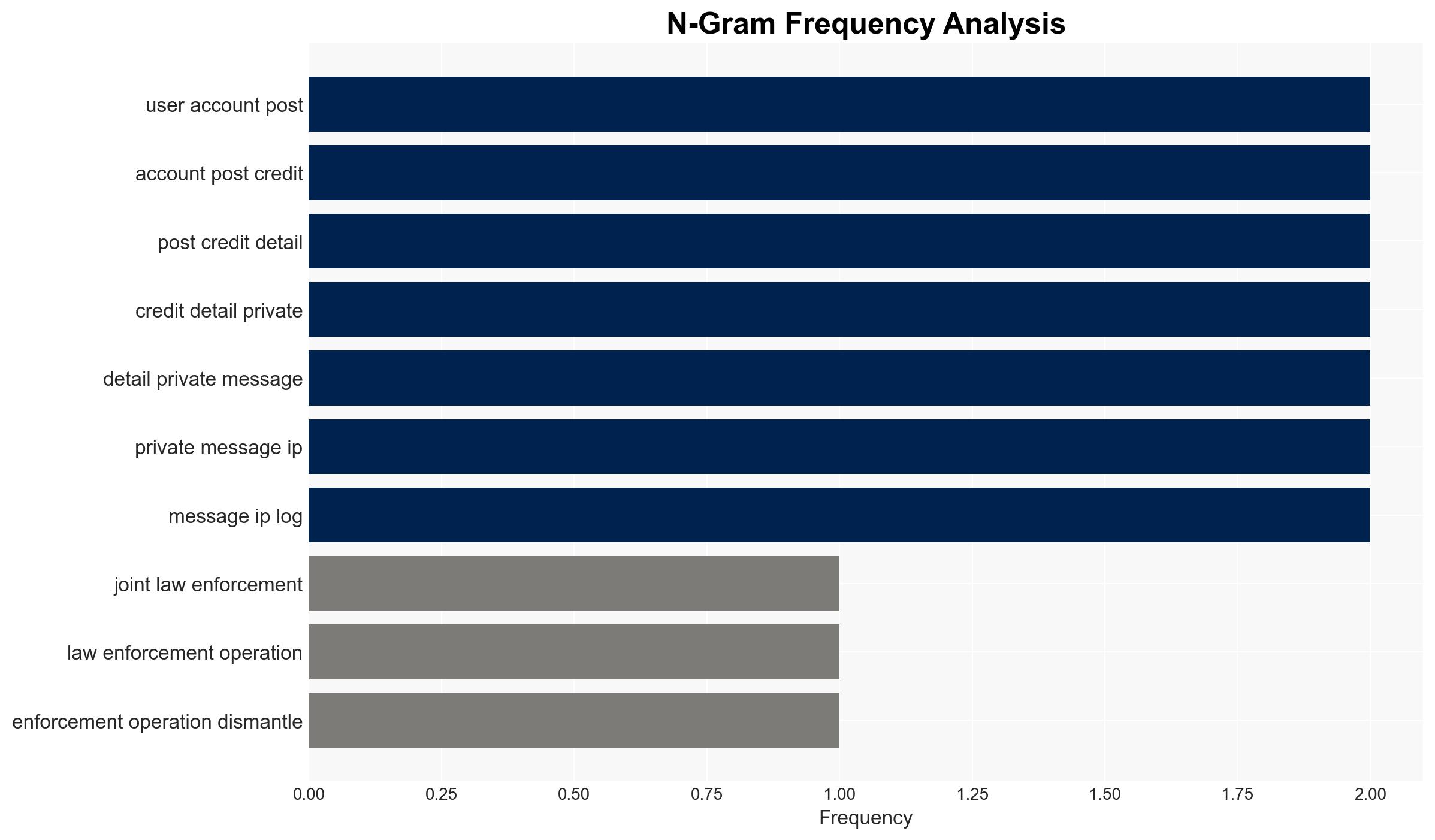
The joint operation by the FBI and Europol successfully dismantled LeakBase, a major cybercriminal forum, disrupting a significant channel for trading stolen credentials. This action affects global cybercriminal networks and may temporarily reduce account takeover incidents. Overall, this assessment is made with moderate confidence due to potential unknowns regarding the full extent of the network’s reach and resilience.
2. Competing Hypotheses
- Hypothesis A: The dismantling of LeakBase will significantly disrupt cybercriminal activities by removing a major platform for trading stolen data. Supporting evidence includes the seizure of user data and the arrest of key individuals, but uncertainty remains about the existence of backup forums or networks.
- Hypothesis B: The takedown of LeakBase will have a limited long-term impact as cybercriminals will migrate to other platforms or create new ones. This is supported by historical patterns of cybercriminal adaptation and the report of Chucky seeking new hosting, though the immediate disruption is evident.
- Assessment: Hypothesis B is currently better supported due to the adaptability of cybercriminal networks and the likelihood of migration to alternative platforms. Indicators such as the emergence of new forums or increased activity on existing ones could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Law enforcement has secured all critical data from LeakBase; cybercriminals will seek alternative platforms; the operation has disrupted a significant portion of the network.
- Information Gaps: The extent of data leakage prior to the takedown and the full network of associated forums remain unclear.
- Bias & Deception Risks: Potential bias in reporting from law enforcement sources aiming to emphasize success; possible deception by cybercriminals regarding the forum’s significance.
4. Implications and Strategic Risks
This development could lead to a temporary reduction in cybercrime activities but may also drive cybercriminals to innovate or consolidate on other platforms, potentially increasing their resilience long-term.
- Political / Geopolitical: Enhanced international cooperation may lead to further joint operations, potentially escalating tensions with countries perceived as safe havens for cybercriminals.
- Security / Counter-Terrorism: Short-term disruption of cybercriminal activities, but potential for increased sophistication in future operations.
- Cyber / Information Space: Potential for increased cybercriminal activity on the dark web and encrypted platforms, complicating monitoring efforts.
- Economic / Social: Temporary reduction in fraud-related economic losses, but potential long-term impacts if cybercriminals adapt effectively.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor dark web and alternative forums for migration patterns; enhance international intelligence-sharing mechanisms.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; strengthen partnerships with private cybersecurity firms.
- Scenario Outlook:
- Best: Cybercriminal networks remain fragmented, reducing their operational effectiveness.
- Worst: Rapid adaptation and consolidation on new platforms, leading to increased sophistication of attacks.
- Most-Likely: Gradual migration to alternative forums with a moderate increase in cybercrime sophistication.
6. Key Individuals and Entities
- Chucky (also known as Chuckies, Sqlrip)
- BloodyMery
- OrderCheck
- TSR
- FBI
- Europol
7. Thematic Tags
cybersecurity, cybercrime, international cooperation, law enforcement, data breach, cyber resilience, dark web, cyber adaptation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us