Digital Vulnerabilities: The Threat of Remote Explosions and Surveillance in Modern Devices
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Digital Detonation A wake-up call for the digital age
1. BLUF (Bottom Line Up Front)
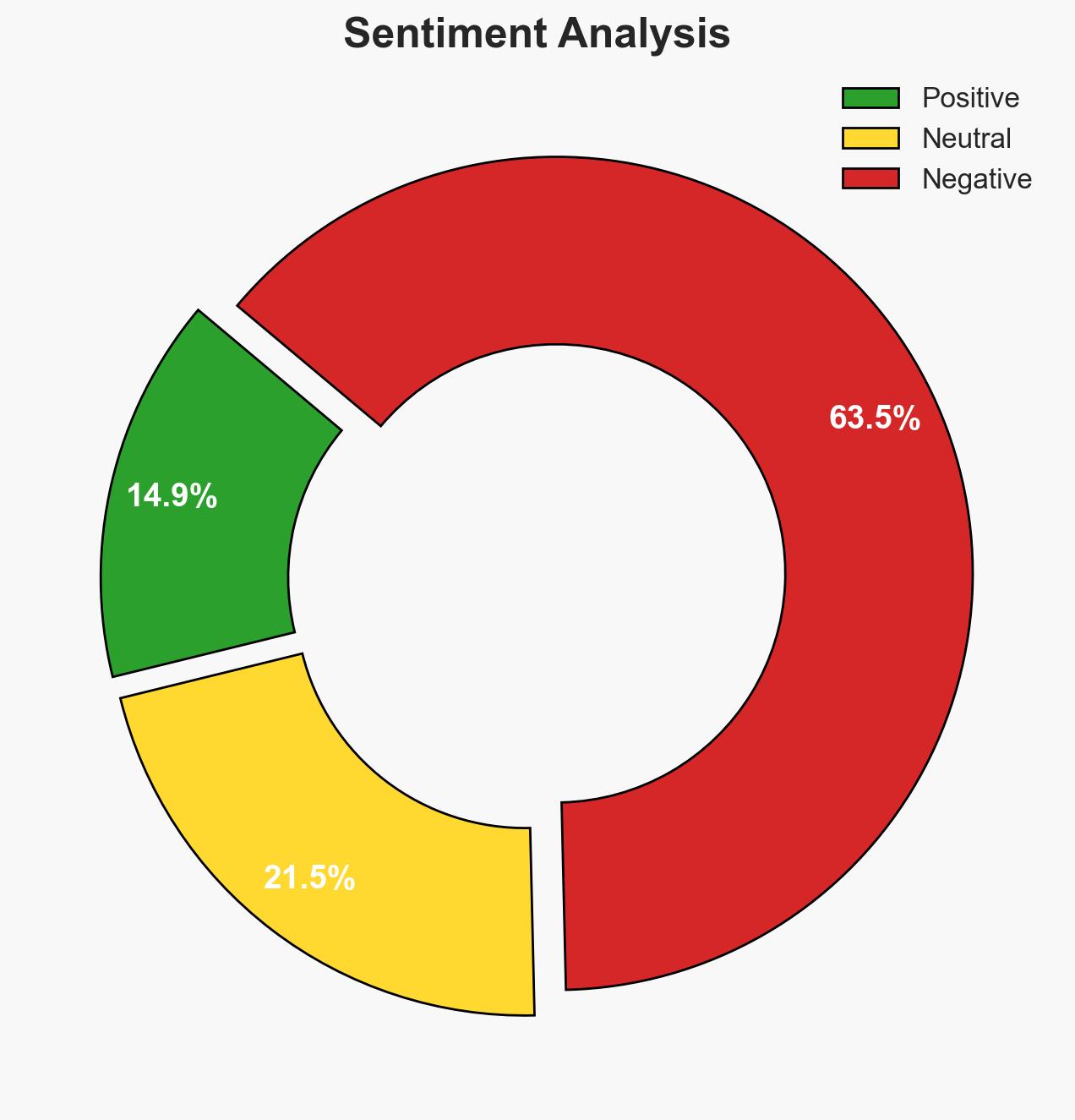
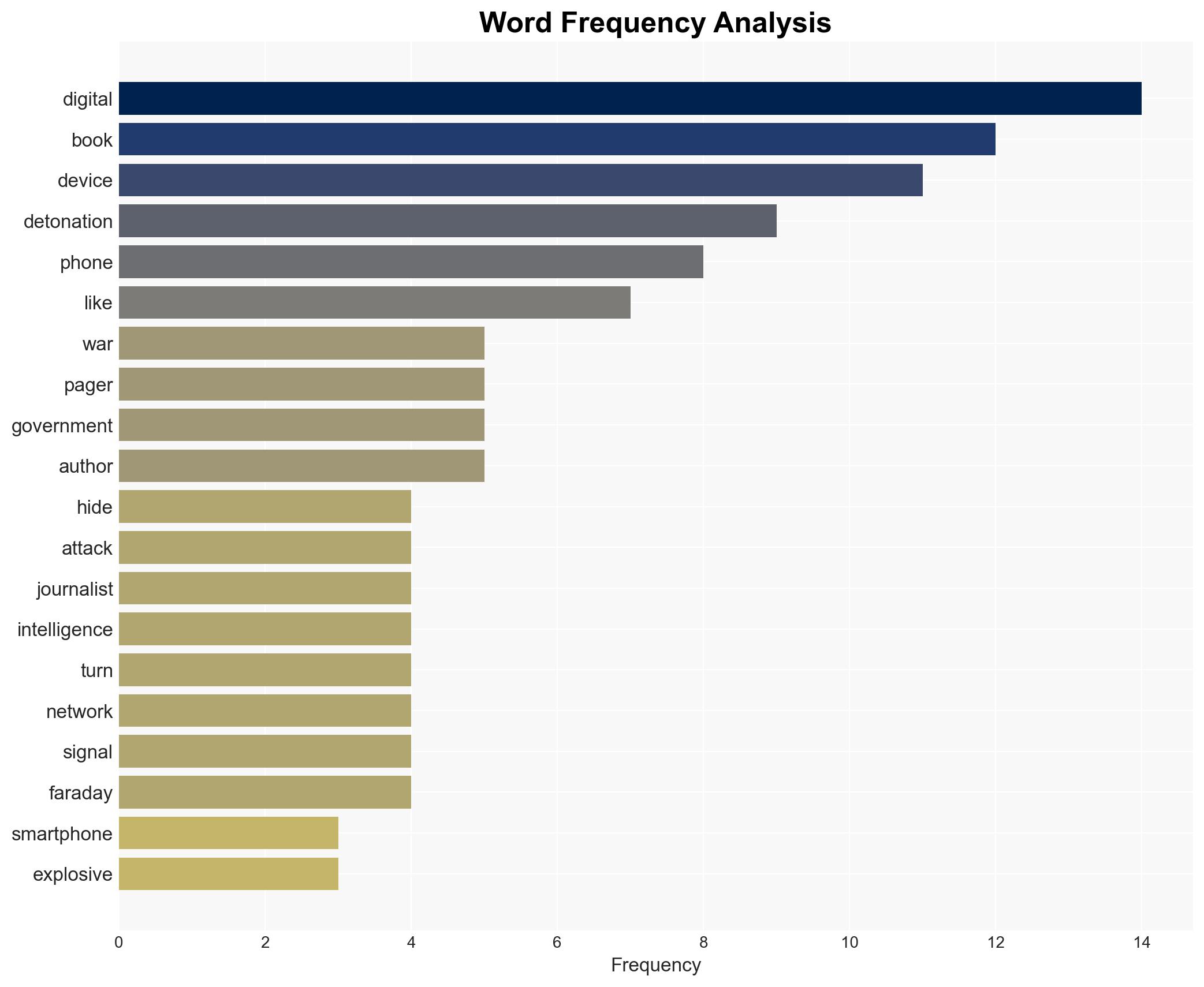
The book “Digital Detonation” highlights the vulnerabilities of consumer electronics to remote manipulation, posing significant security threats. The most likely hypothesis is that these vulnerabilities will be increasingly exploited by state and non-state actors, affecting individuals globally, particularly activists and journalists. Overall confidence in this judgment is moderate due to the complexity and evolving nature of the threat landscape.
2. Competing Hypotheses
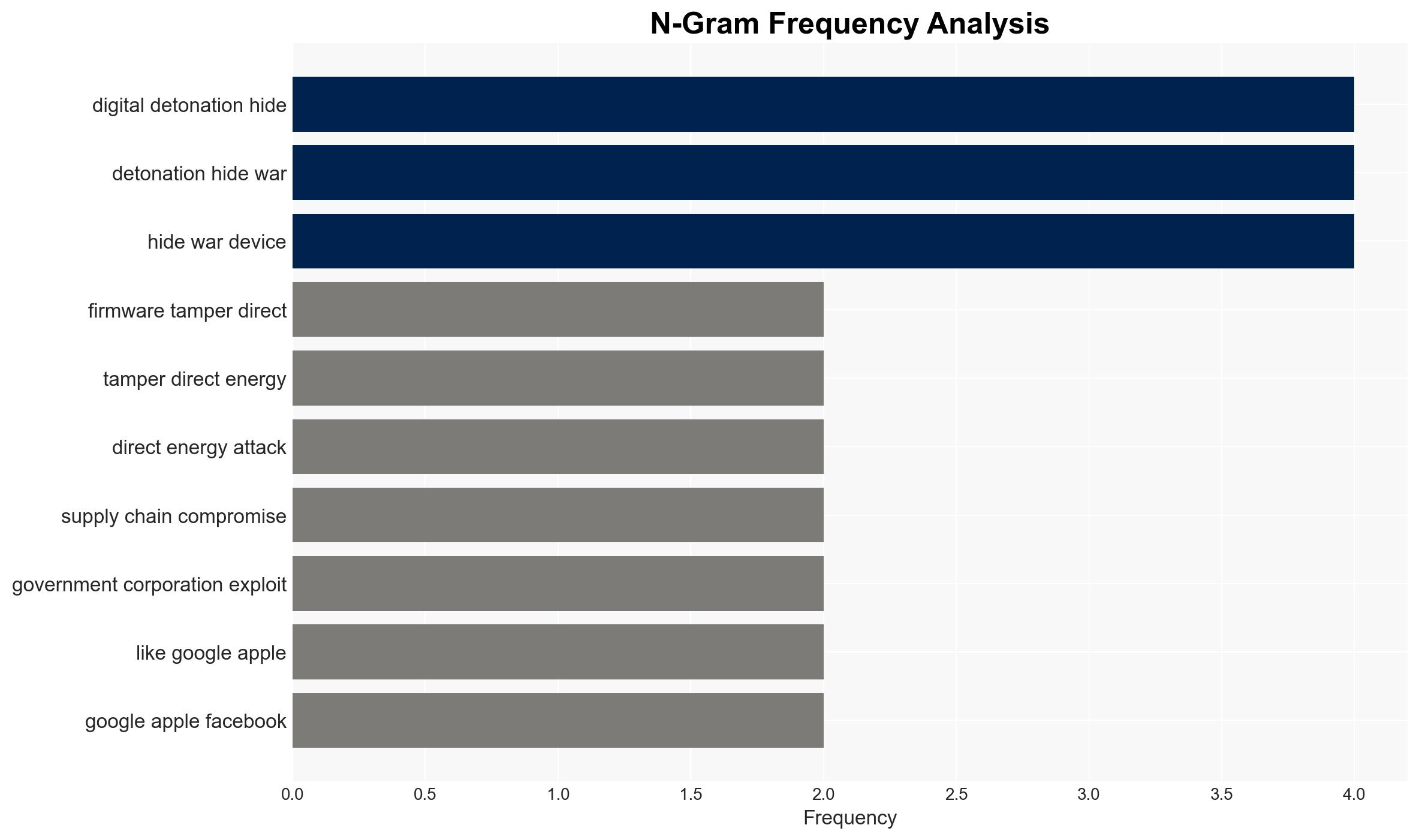
- Hypothesis A: Consumer electronics are increasingly being weaponized by state actors through supply chain compromises and remote manipulation, as evidenced by the 2024 Lebanon pager bombings and potential Chinese involvement in manufacturing vulnerabilities. Key uncertainties include the extent of state actor involvement and the scale of current operations.
- Hypothesis B: The threat is overstated, with isolated incidents being used to exaggerate the risk for political or commercial gain. Supporting evidence includes the lack of widespread documented cases outside specific incidents. However, this is contradicted by the documented capabilities of spyware like Pegasus.
- Assessment: Hypothesis A is currently better supported due to documented incidents and the technical feasibility of such attacks. Indicators that could shift this judgment include new evidence of widespread exploitation or credible denials from implicated state actors.
3. Key Assumptions and Red Flags
- Assumptions: State actors have the capability and intent to exploit consumer electronics; supply chain vulnerabilities are significant; current security measures are insufficient to prevent such exploitation.
- Information Gaps: Specific details on the scale of state actor involvement and the technical specifics of the vulnerabilities exploited.
- Bias & Deception Risks: Potential bias from the author’s perspective as an investigative journalist; possible exaggeration of threats for commercial success of the book; lack of independent verification of claims.
4. Implications and Strategic Risks
This development could lead to increased geopolitical tensions, particularly involving countries implicated in supply chain compromises. Over time, it may drive a shift towards more secure technologies and increased regulation of tech companies.
- Political / Geopolitical: Potential escalation in cyber and trade tensions, particularly between Western nations and China.
- Security / Counter-Terrorism: Increased threat to individuals from targeted attacks, necessitating enhanced protective measures for high-risk groups.
- Cyber / Information Space: Greater focus on cybersecurity measures and potential increase in cyber warfare activities.
- Economic / Social: Potential economic impacts on tech companies and shifts in consumer trust; social unrest if surveillance and targeting become widespread.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of supply chain vulnerabilities; enhance security protocols for high-risk individuals; engage with tech companies to assess current vulnerabilities.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing on cyber threats; invest in research for secure technology alternatives; advocate for stronger regulations on tech manufacturing.
- Scenario Outlook:
- Best: Enhanced security measures mitigate threats, leading to increased consumer trust.
- Worst: Widespread exploitation of vulnerabilities leads to significant geopolitical and social instability.
- Most-Likely: Incremental improvements in security and regulation, with ongoing isolated incidents.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
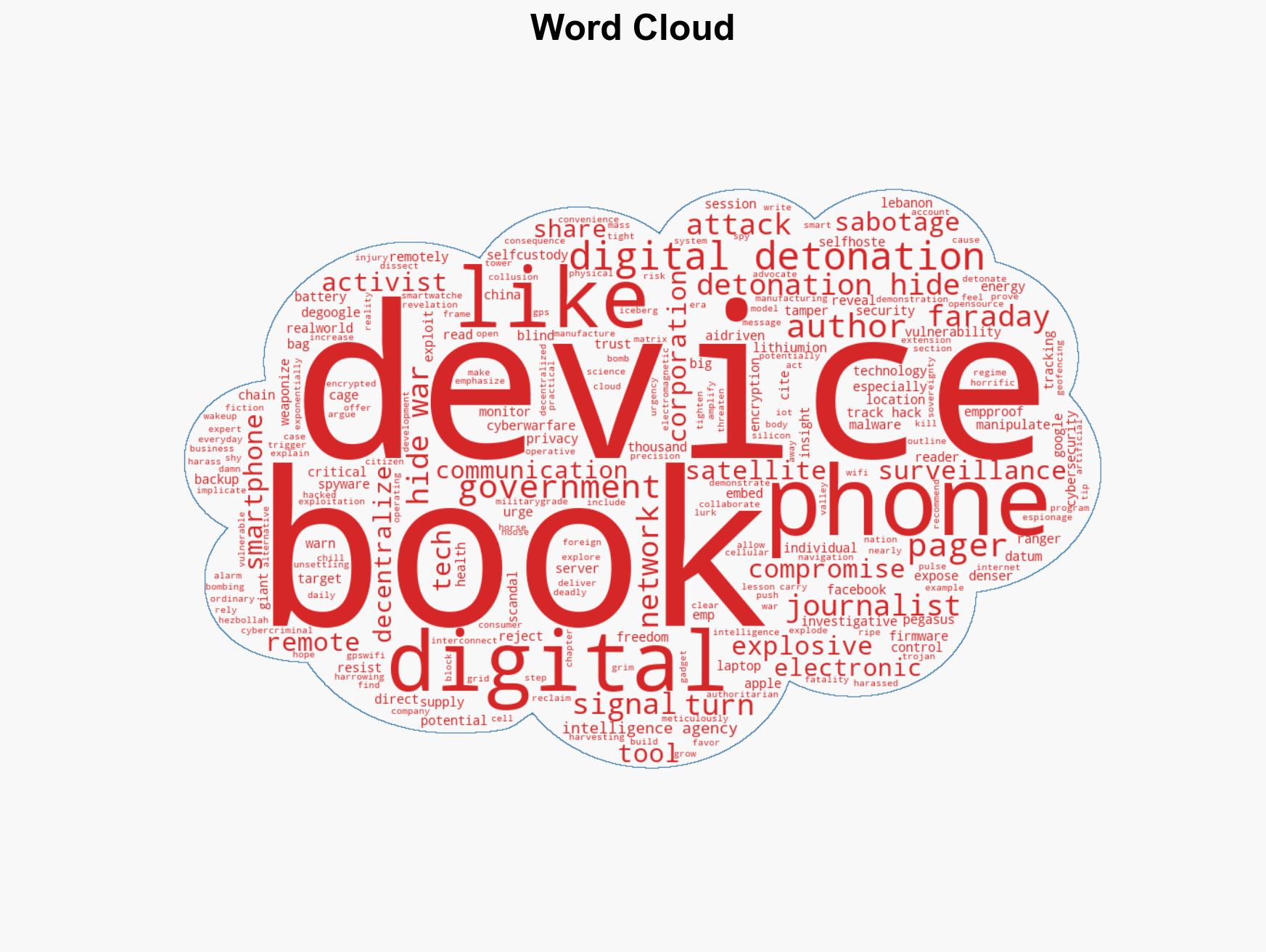
7. Thematic Tags
cybersecurity, supply chain vulnerabilities, state actors, surveillance, digital espionage, tech regulation, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us