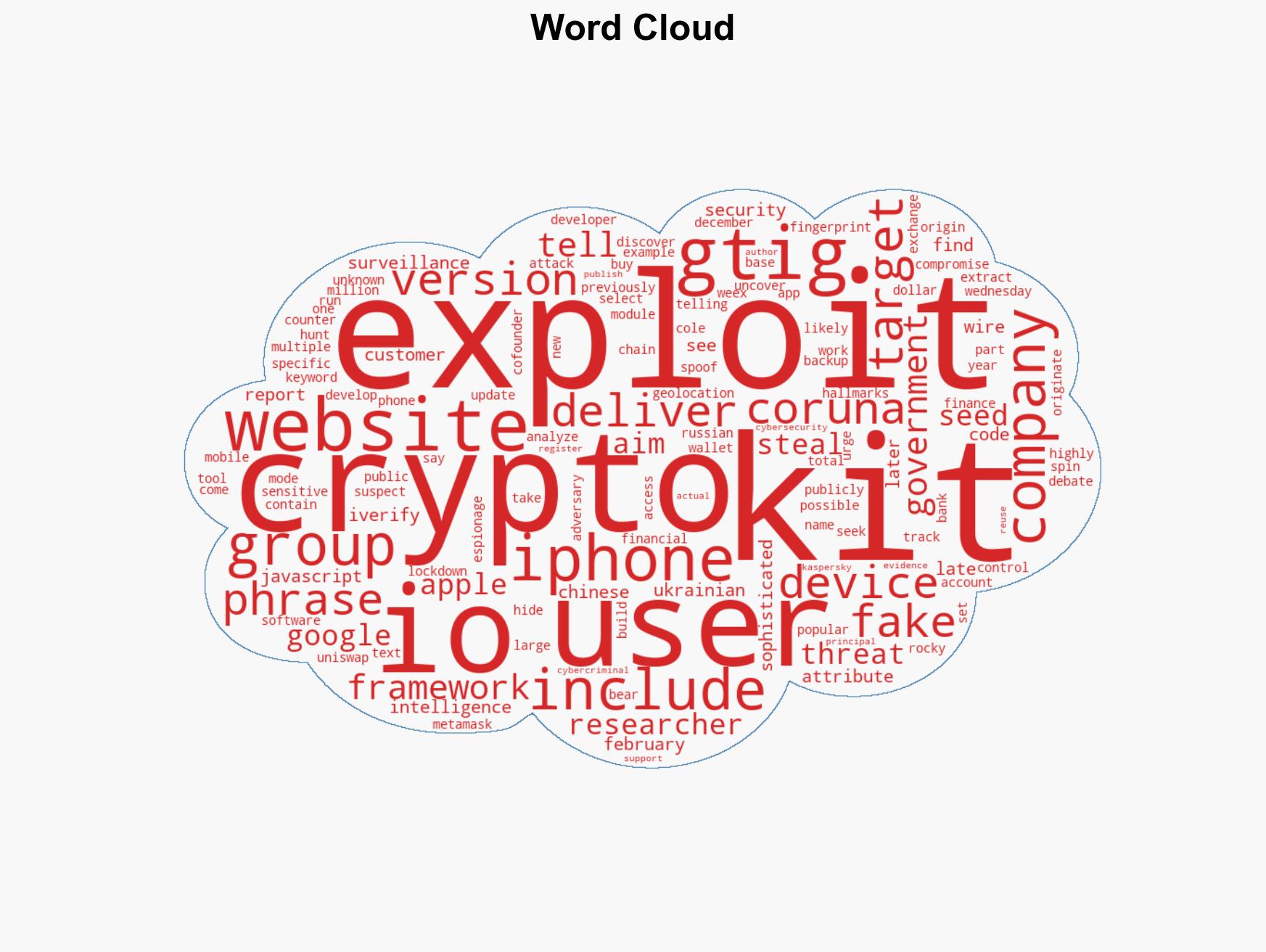
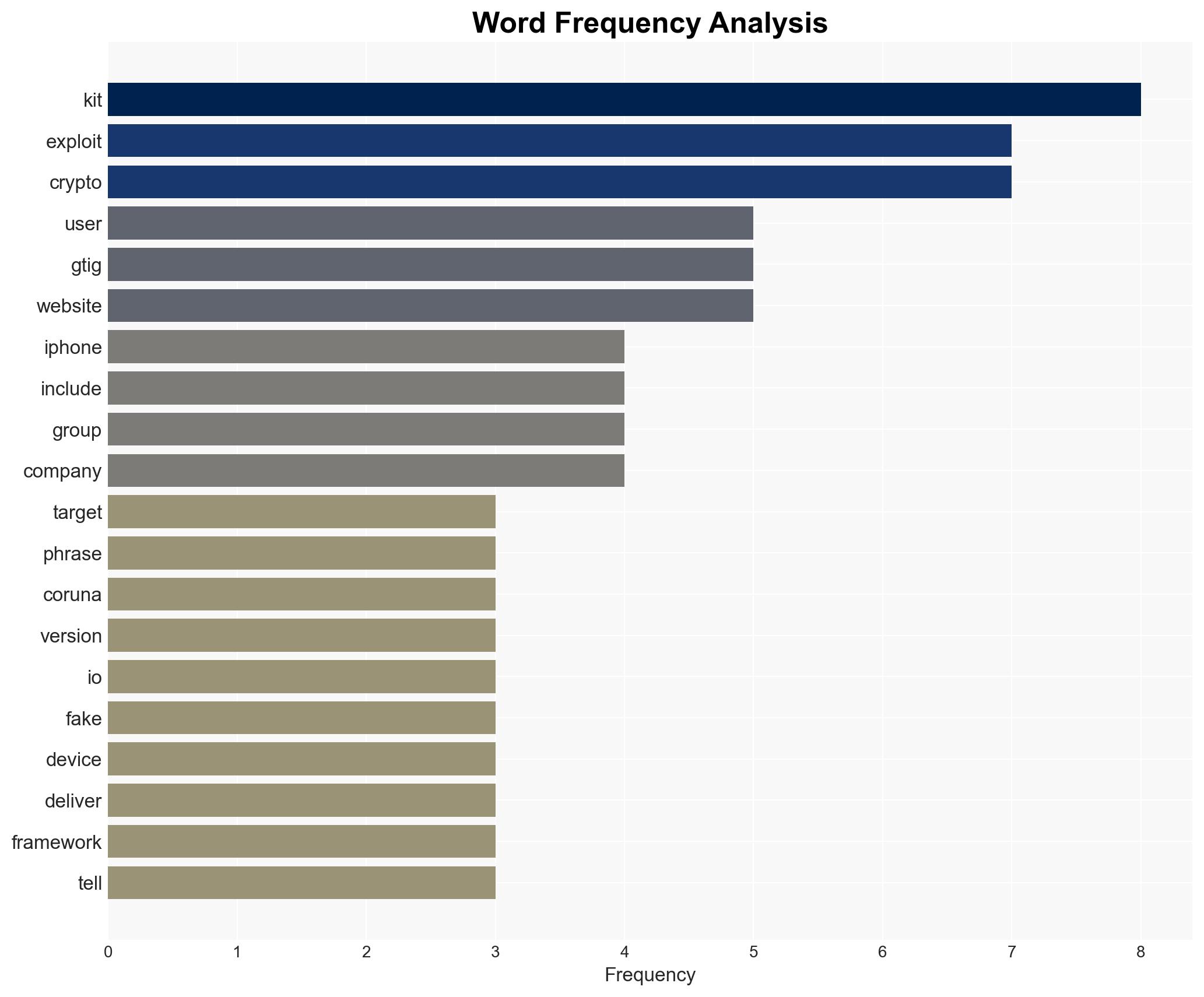
Google identifies new iPhone exploit kit targeting crypto wallets, warns users of potential scams.
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Google warns of crypto scams using new and powerful iPhone exploit kit
1. BLUF (Bottom Line Up Front)
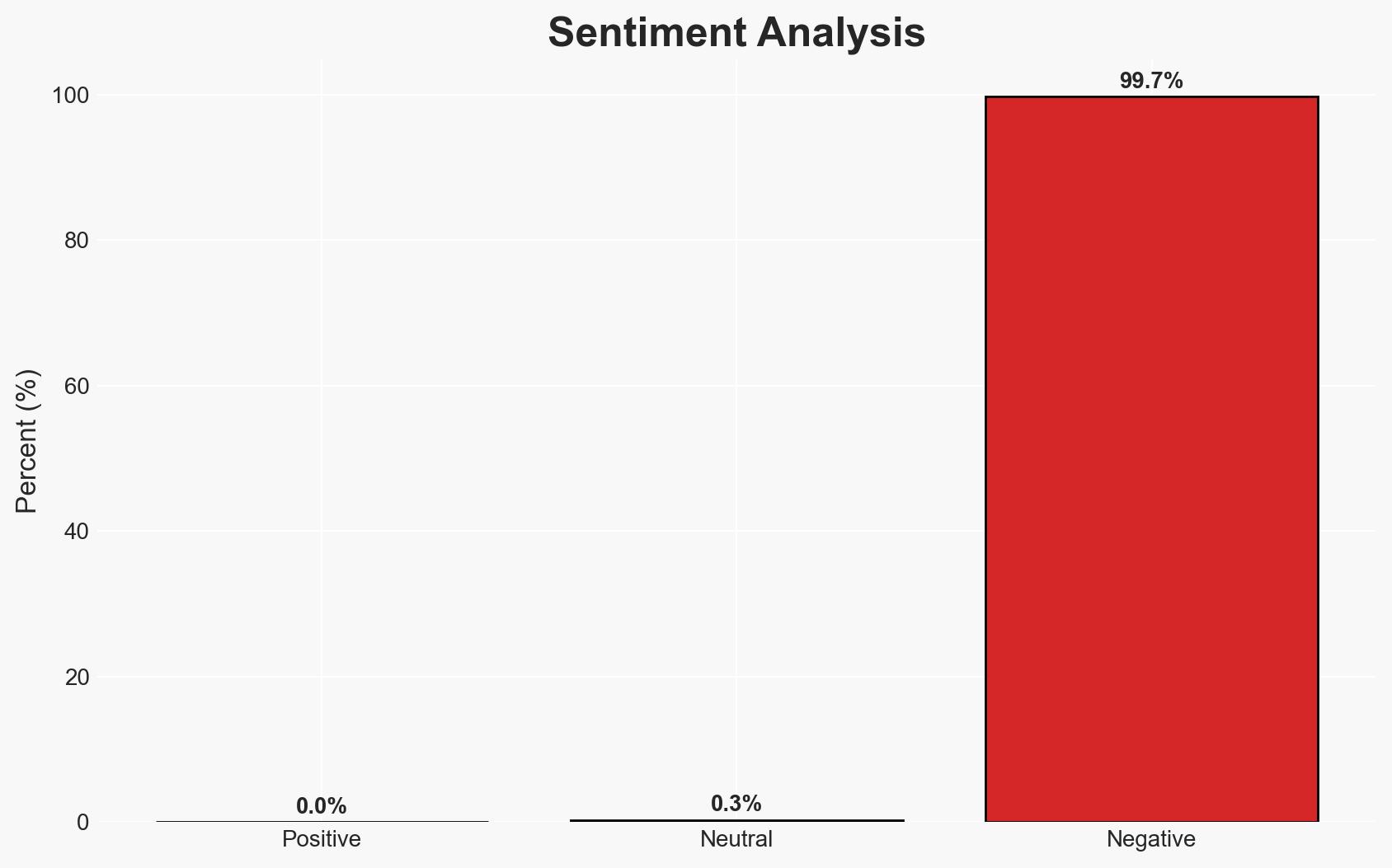
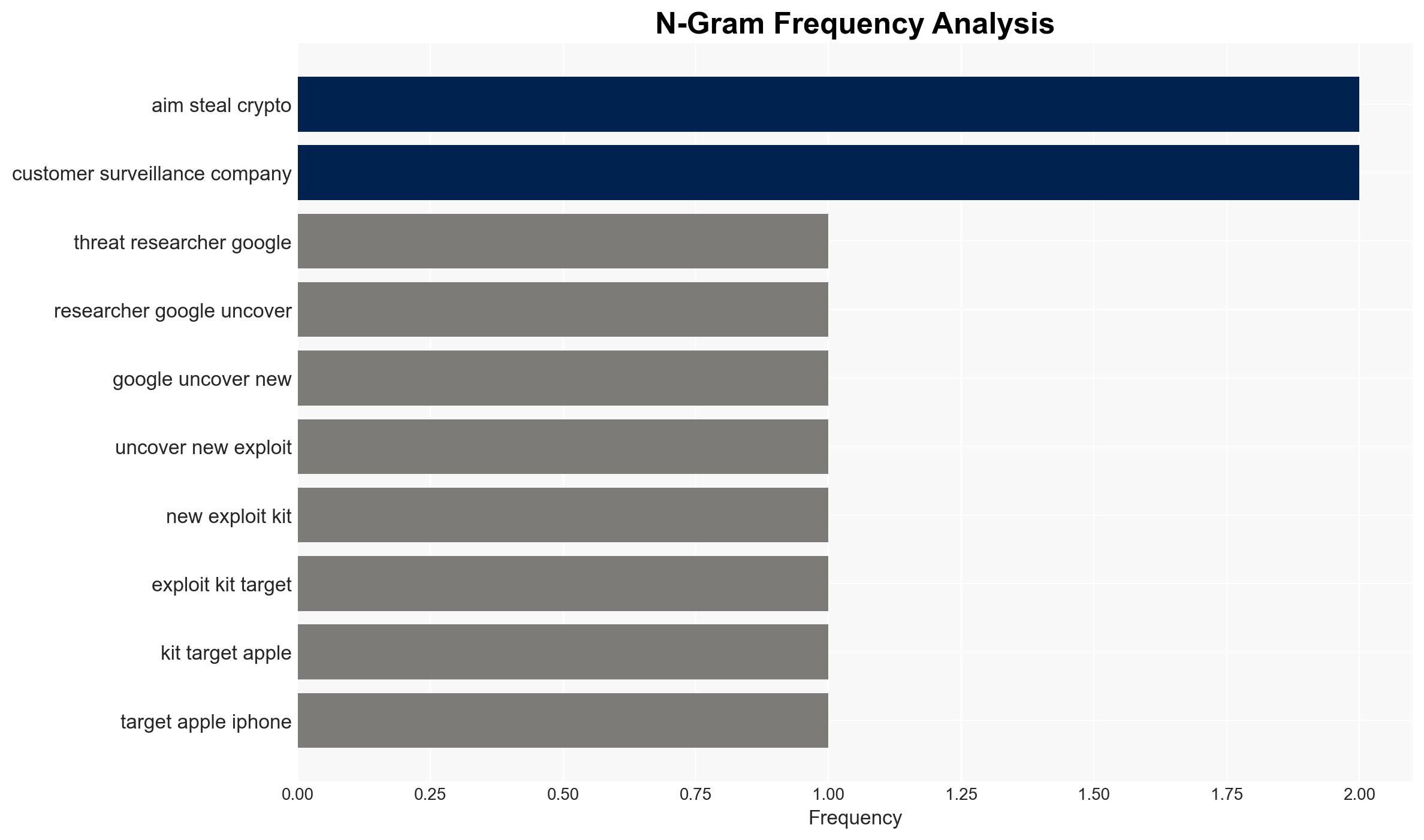
The Coruna exploit kit poses a significant threat to iPhone users, particularly those involved in cryptocurrency transactions, by targeting devices with outdated iOS versions. The kit is linked to a suspected Russian espionage group and has been used in fake Chinese crypto websites. The most likely hypothesis is that the kit originated from a surveillance company and has been repurposed by various actors. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The Coruna exploit kit was developed by a US government-affiliated entity and has been misappropriated by adversaries. This is supported by the sophistication and cost of development, as well as similarities to known US government tools. However, there is no direct evidence of code reuse.
- Hypothesis B: The kit was developed independently by a surveillance company and sold to multiple actors, including state and non-state entities. This is supported by the lack of direct evidence linking the code to US government tools and the commercial nature of surveillance software markets.
- Assessment: Hypothesis B is currently better supported due to the absence of direct evidence linking the exploit to US government code. Key indicators that could shift this judgment include new evidence of code reuse or direct attribution to a specific entity.
3. Key Assumptions and Red Flags
- Assumptions: The exploit kit’s sophistication implies state-level resources; the surveillance company operates in a market that sells to multiple actors; the kit’s use by Russian groups suggests geopolitical motivations.
- Information Gaps: The identity of the surveillance company customer; detailed technical analysis linking the kit to specific state actors; the full scope of the kit’s deployment and impact.
- Bias & Deception Risks: Potential bias in attributing sophisticated cyber tools to state actors; risk of deception in public reports to mislead attribution efforts.
4. Implications and Strategic Risks
The Coruna exploit kit could lead to increased geopolitical tensions, particularly between the US, Russia, and China, if attribution to state actors is confirmed. The use of such tools in cybercrime could undermine trust in digital financial systems.
- Political / Geopolitical: Potential escalation in cyber conflict between major powers; diplomatic strains if state sponsorship is confirmed.
- Security / Counter-Terrorism: Increased risk to individuals and organizations involved in cryptocurrency; potential for broader application in espionage.
- Cyber / Information Space: Highlighting vulnerabilities in iOS could lead to increased cyber operations targeting Apple devices; potential for misinformation campaigns.
- Economic / Social: Erosion of trust in cryptocurrency platforms; potential financial losses for individuals and businesses.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage iPhone users to update to the latest iOS version; enhance monitoring of cryptocurrency platforms for suspicious activity.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve threat intelligence sharing; invest in cybersecurity resilience and public awareness campaigns.
- Scenario Outlook:
- Best: Rapid patching and awareness campaigns mitigate threat impact.
- Worst: Exploit leads to significant financial and geopolitical fallout.
- Most-Likely: Continued use by diverse actors with moderate impact on targeted users.
6. Key Individuals and Entities
- Google Threat Intelligence Group (GTIG)
- iVerify (Rocky Cole)
- Kaspersky
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, espionage, cryptocurrency, iOS vulnerabilities, cybercrime, surveillance technology, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us