Major Data Breach Exposes 15.8 Million Medical Records from French Health Ministry Software Vendor
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cyber Breach in France 158 Million Medical Records Stolen in Attack on Health Ministry Software Vendor – The420in
1. BLUF (Bottom Line Up Front)
The cyberattack on Cegedim Santé, a healthcare software vendor linked to France’s health ministry, resulted in the theft of approximately 15.8 million medical records. This incident highlights significant vulnerabilities in supply-chain security, affecting thousands of doctors and patients. The breach poses serious risks of identity theft and privacy violations. Overall confidence in this assessment is moderate due to incomplete information about the attackers and their motives.
2. Competing Hypotheses
- Hypothesis A: The breach was conducted by a financially motivated cybercriminal group aiming to exploit sensitive data for identity theft and phishing attacks. Supporting evidence includes the nature of the data stolen, which is highly valuable for such activities. Key uncertainties involve the identification of the group responsible and their specific methods.
- Hypothesis B: The attack was state-sponsored, intended to destabilize France’s healthcare system or gather intelligence. This is supported by the scale and sophistication of the breach, which may exceed typical criminal capabilities. However, there is a lack of direct evidence linking any state actor to the incident.
- Assessment: Hypothesis A is currently better supported due to the immediate financial incentives for cybercriminals and the lack of clear indicators of state involvement. Indicators such as attribution to a known state actor or discovery of geopolitical motives could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The breach was primarily financially motivated; the attackers had access to the vendor’s systems rather than direct government systems; the data will be used for malicious purposes.
- Information Gaps: Identity of the attackers; specific vulnerabilities exploited; full scope of data compromised.
- Bias & Deception Risks: Potential bias in attributing the attack to cybercriminals without considering state actors; deception risk from attackers using false flags to mislead investigators.
4. Implications and Strategic Risks
This breach could lead to increased scrutiny on supply-chain security and influence policy changes in data protection. It may also encourage similar attacks if perceived as successful.
- Political / Geopolitical: Potential diplomatic tensions if state involvement is suspected or confirmed.
- Security / Counter-Terrorism: Increased risk of exploitation of stolen data for criminal or terrorist activities.
- Cyber / Information Space: Heightened awareness and potential for improved cybersecurity measures across healthcare sectors.
- Economic / Social: Possible erosion of public trust in digital healthcare platforms, impacting adoption and use.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of affected systems, issue alerts to potential victims, and initiate a comprehensive forensic investigation.
- Medium-Term Posture (1–12 months): Strengthen supply-chain security protocols, develop partnerships for threat intelligence sharing, and conduct regular security audits.
- Scenario Outlook:
- Best: Rapid identification and neutralization of the threat actors, with minimal long-term impact.
- Worst: Data is widely exploited, leading to significant identity theft and loss of trust in digital healthcare systems.
- Most-Likely: Incremental improvements in cybersecurity with ongoing risks of similar attacks.
6. Key Individuals and Entities
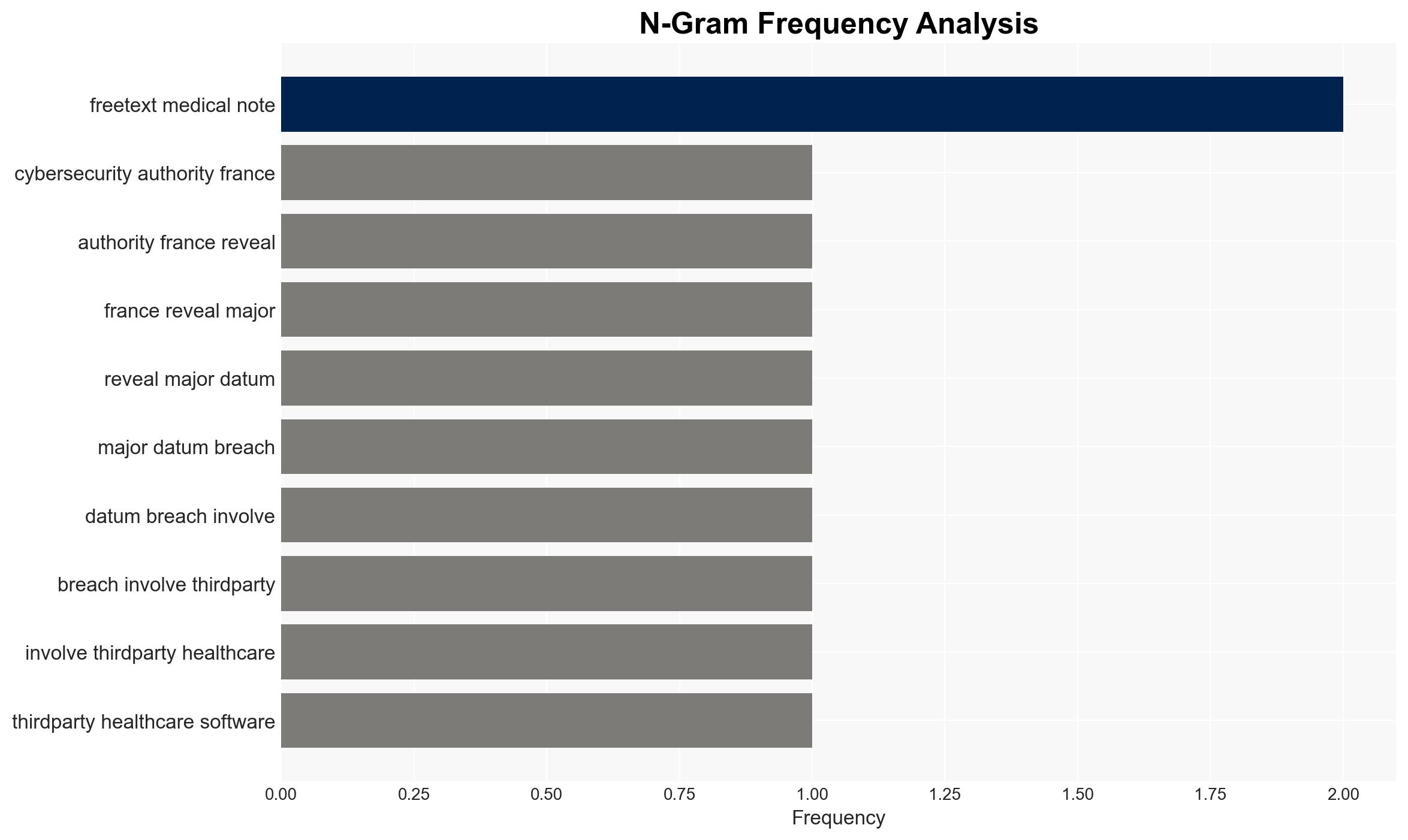
- Cegedim Santé – Healthcare software vendor
- MonLogicielMedical (MLM) – Digital healthcare platform
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
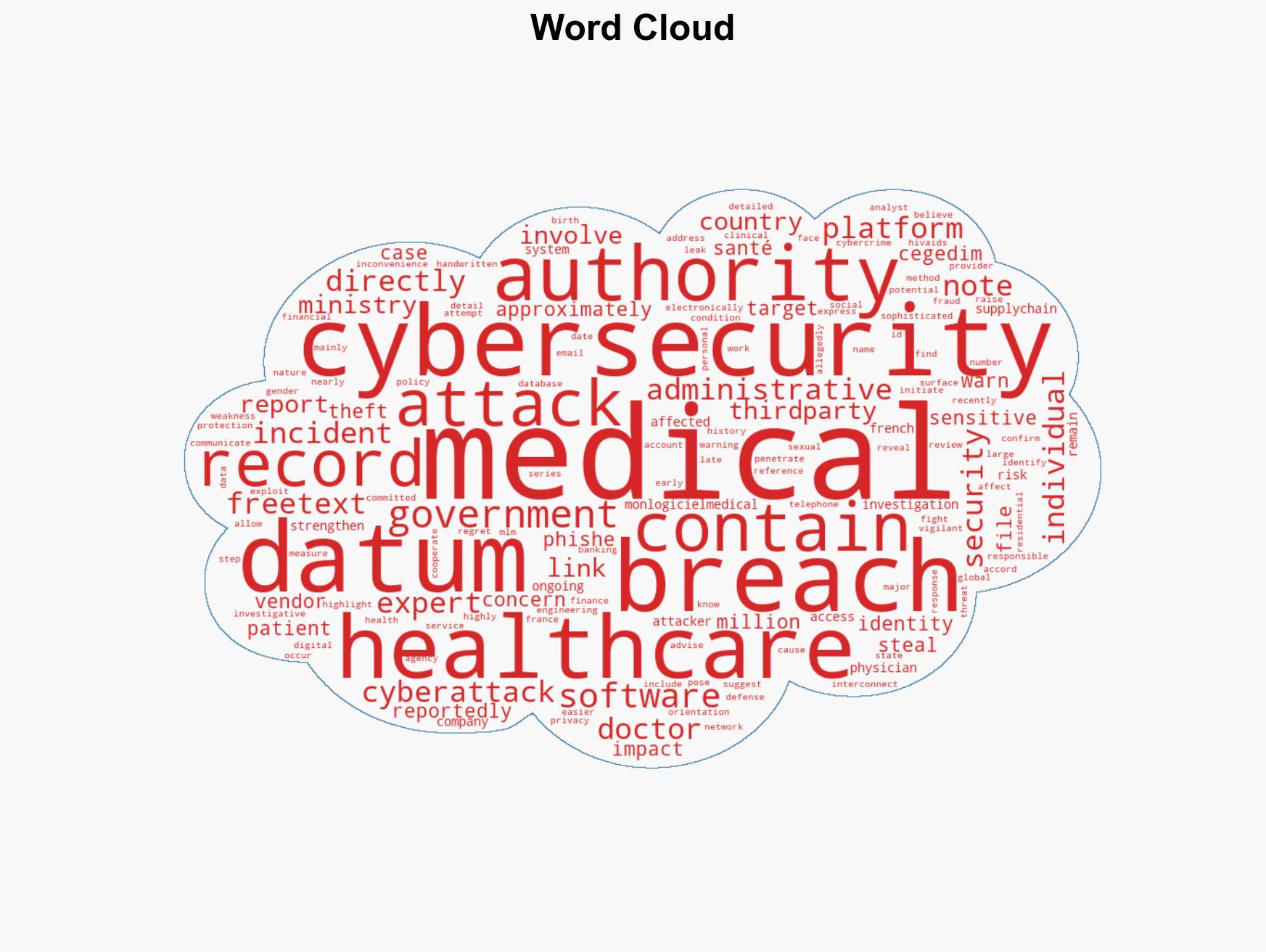
cybersecurity, data breach, healthcare, supply-chain security, identity theft, privacy risks, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us