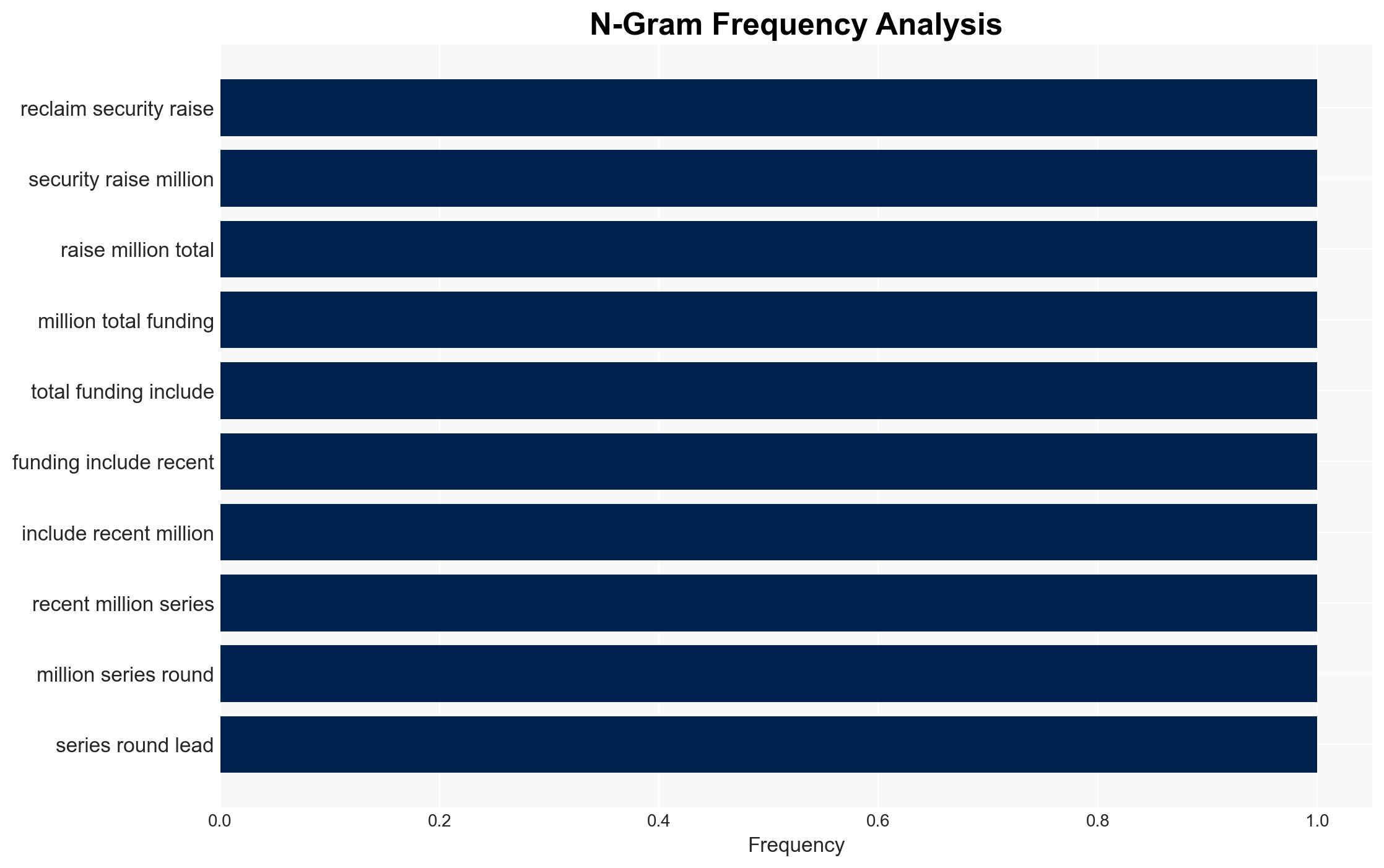
Reclaim Security raises $26 million to enhance automation in cybersecurity remediation efforts
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Reclaim Security secures 26 million to automate cybersecurity remediation
1. BLUF (Bottom Line Up Front)
Reclaim Security’s recent $26 million funding round aims to address the critical gap in cybersecurity remediation by automating the process, potentially reducing remediation times significantly. This development could impact enterprises by enhancing their cybersecurity posture and operational efficiency. The assessment is made with moderate confidence due to existing uncertainties in the technology’s real-world efficacy and adoption rates.
2. Competing Hypotheses
- Hypothesis A: Reclaim Security’s platform will significantly reduce remediation times and improve cybersecurity resilience by automating the remediation process. This is supported by the company’s focus on eliminating manual workflows and the introduction of the PIPE engine. However, the effectiveness of the AI-driven approach in diverse operational environments remains uncertain.
- Hypothesis B: The platform may not achieve the anticipated impact due to potential integration challenges and resistance from security teams accustomed to manual processes. While the technology promises improvements, the market’s readiness to adopt such a paradigm shift is questionable.
- Assessment: Hypothesis A is currently better supported due to the substantial investment and technological innovation backing Reclaim Security. Key indicators that could shift this judgment include evidence of successful deployment in varied environments and user feedback on operational impacts.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will prioritize automation in cybersecurity; AI-driven remediation will not introduce new vulnerabilities; PIPE engine’s simulations accurately predict operational impacts; the market will accept AI-driven solutions.
- Information Gaps: Lack of data on the platform’s performance in live environments; user adoption rates; potential unintended consequences of automation.
- Bias & Deception Risks: Potential over-reliance on vendor-provided performance metrics; cognitive bias towards technological optimism; risk of overstated capabilities by Reclaim Security.
4. Implications and Strategic Risks
This development could reshape cybersecurity strategies by emphasizing automation, potentially leading to faster threat mitigation but also raising concerns about AI reliability and trust.
- Political / Geopolitical: Increased cybersecurity resilience may reduce vulnerability to state-sponsored cyber-attacks, potentially affecting geopolitical dynamics.
- Security / Counter-Terrorism: Enhanced remediation capabilities could deter cyber-terrorism by reducing exploitable windows.
- Cyber / Information Space: The shift towards AI-driven solutions may accelerate the evolution of cyber threats, prompting adversaries to develop countermeasures.
- Economic / Social: Successful adoption could lead to economic benefits through reduced breach costs, but may also result in workforce displacement in cybersecurity roles.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor initial deployments of Reclaim Security’s platform; engage with industry stakeholders to assess real-world impacts.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to evaluate AI-driven remediation; invest in workforce training to adapt to automation.
- Scenario Outlook:
- Best: Widespread adoption leads to significant reductions in cyber incidents.
- Worst: Integration failures and new vulnerabilities undermine trust in AI solutions.
- Most-Likely: Gradual adoption with mixed results, prompting iterative improvements.
6. Key Individuals and Entities
- Barak Klinghofer, CEO of Reclaim Security
- Acrew Capital
- QP Ventures
- Ibex Investors
7. Thematic Tags
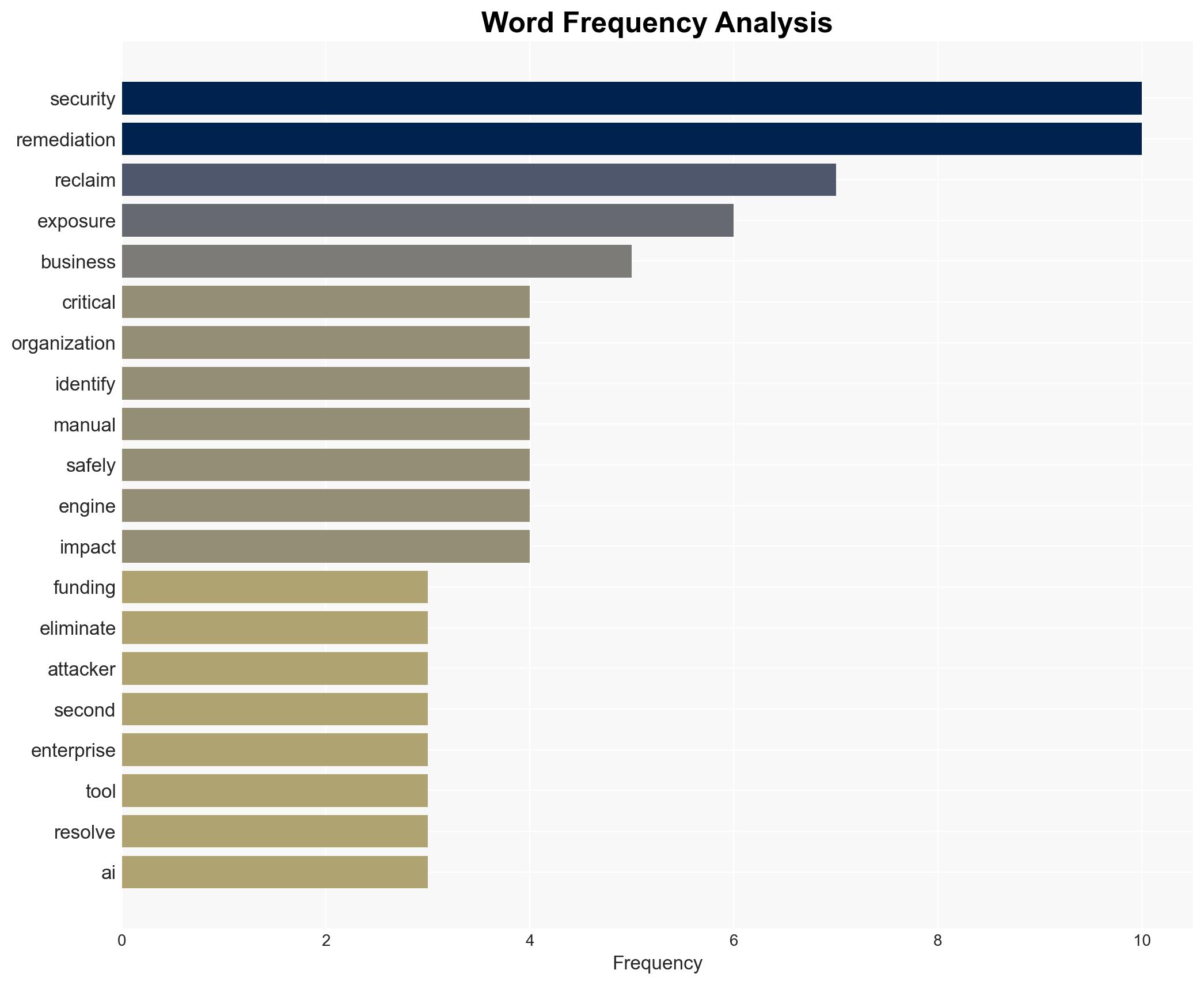
cybersecurity, automation, AI-driven remediation, venture capital, cybersecurity resilience, operational efficiency
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us