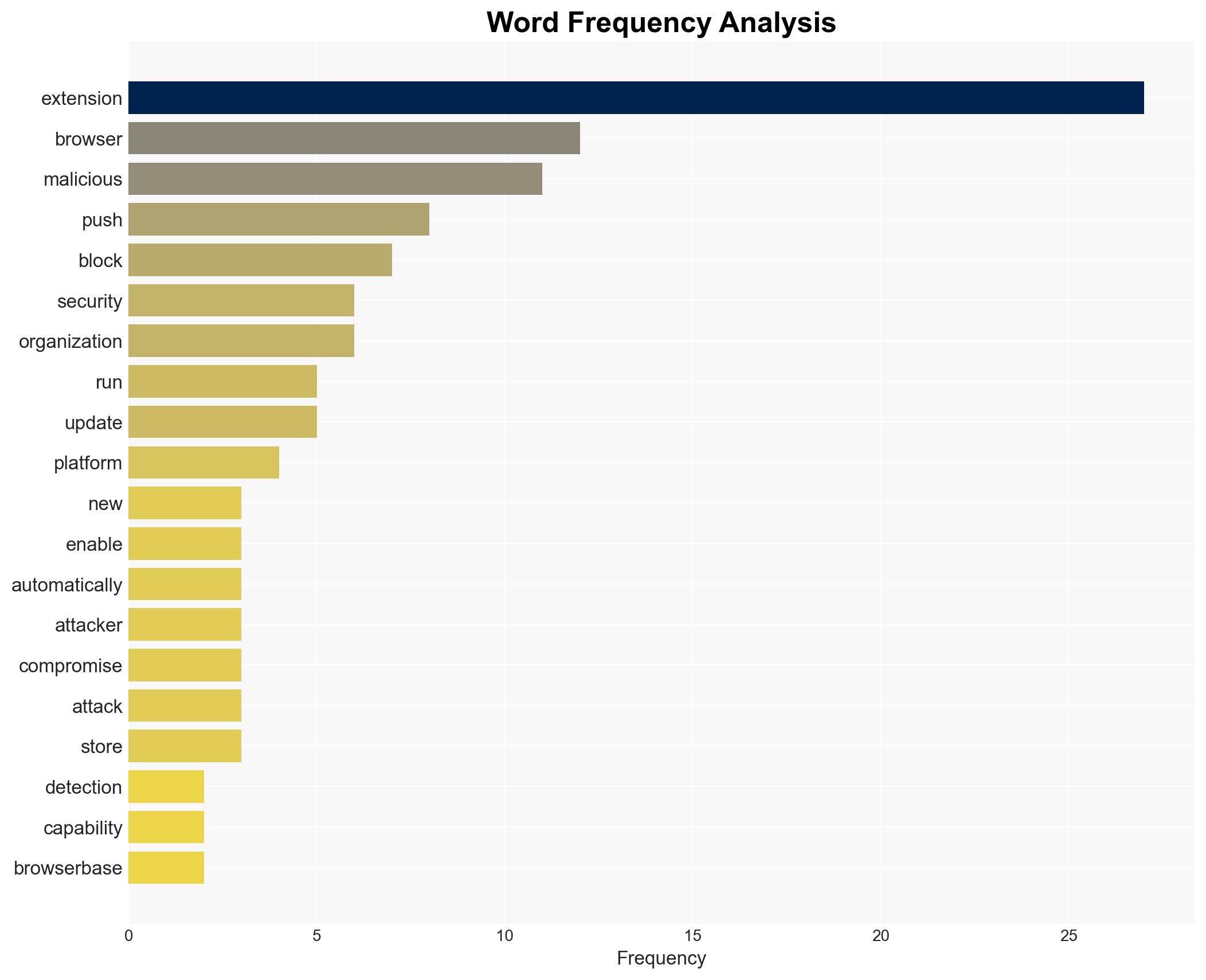
Push Security introduces detection and blocking for harmful browser extensions to enhance employee security.
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Push Security adds malicious browser extension detection to block threats in employee browsers
1. BLUF (Bottom Line Up Front)
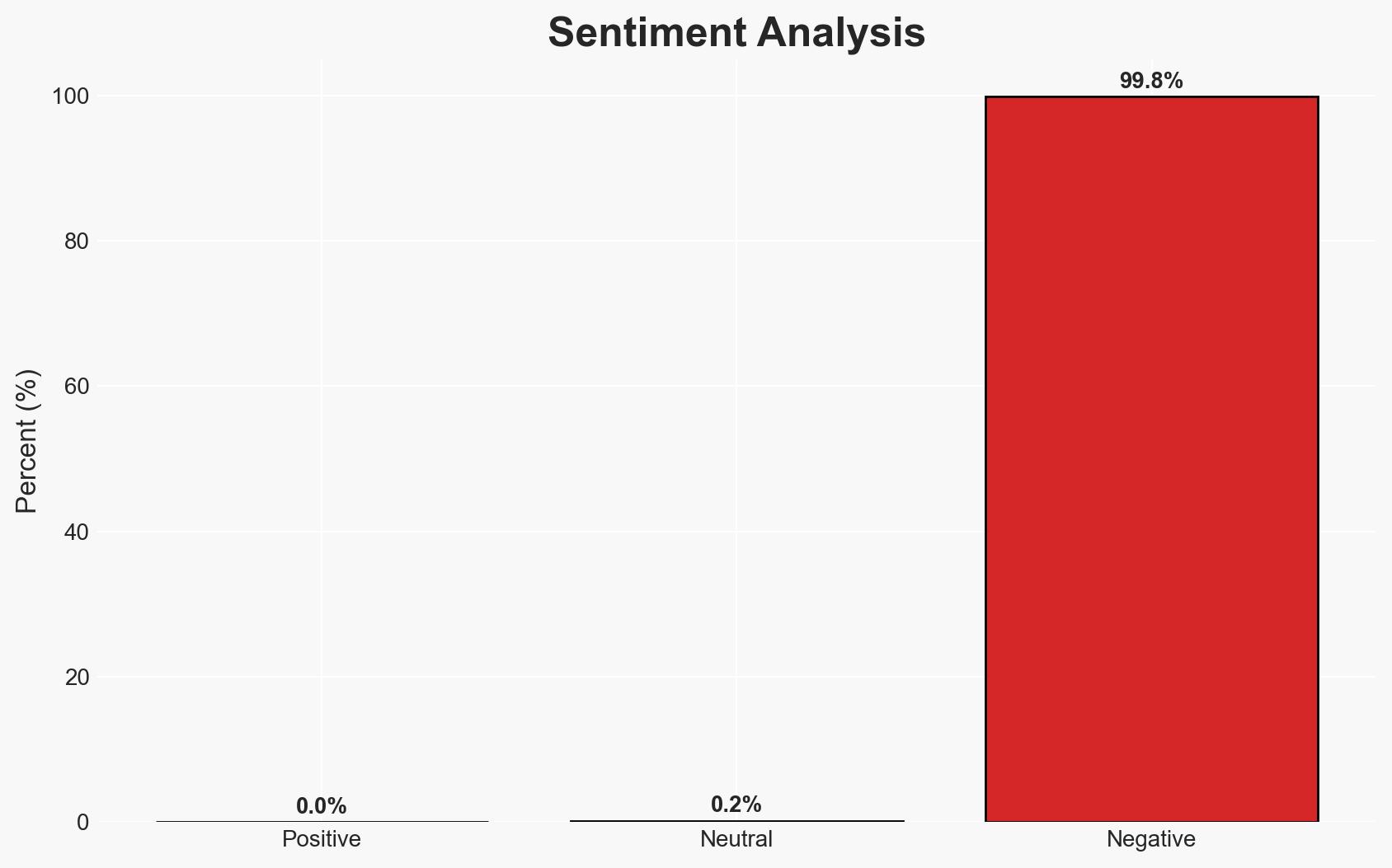
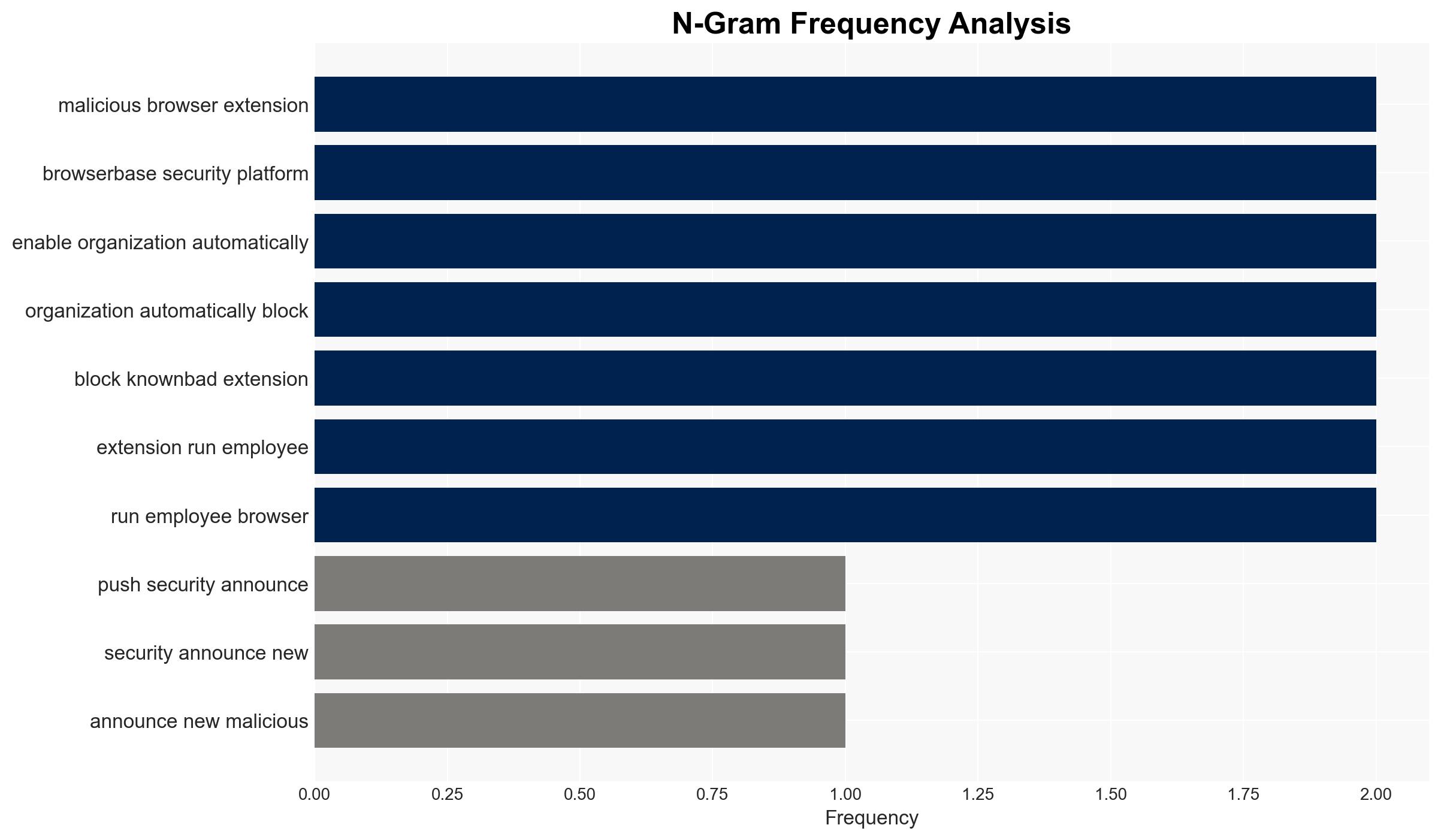
Push Security’s introduction of malicious browser extension detection and blocking capabilities addresses a significant and growing cybersecurity threat. This development is likely to enhance organizational security by mitigating risks associated with browser extensions, which are increasingly exploited by attackers. The most likely hypothesis is that this capability will improve security posture without significantly disrupting productivity. Overall confidence in this judgment is moderate, given existing information gaps and potential biases in threat reporting.
2. Competing Hypotheses
- Hypothesis A: Push Security’s new capability will significantly reduce the risk of compromise from malicious browser extensions. Supporting evidence includes the ability to automatically block known-bad extensions and provide real-time visibility. Contradicting evidence includes potential evasion tactics by attackers and incomplete coverage of all malicious extensions.
- Hypothesis B: The new capability will have limited impact due to sophisticated evasion techniques and the dynamic nature of extension threats. Supporting evidence includes the use of obfuscated and dynamically compiled code by attackers. Contradicting evidence includes the continuous update of Push’s intelligence database.
- Assessment: Hypothesis A is currently better supported due to the proactive blocking and visibility features, but key indicators such as the emergence of new evasion techniques could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will adopt and effectively implement the new capability; attackers will not rapidly develop new evasion techniques; Push Security’s intelligence database remains comprehensive and up-to-date.
- Information Gaps: Specific details on the detection algorithms used; the extent of Push Security’s intelligence database coverage; the rate of false positives and negatives.
- Bias & Deception Risks: Potential bias in threat reporting from Push Security; manipulation of extension approval processes by attackers; over-reliance on automated detection without human oversight.
4. Implications and Strategic Risks
This development could lead to a shift in attacker tactics, potentially increasing the sophistication of malicious extensions. It may also prompt other security vendors to enhance their offerings, thereby raising the overall security baseline.
- Political / Geopolitical: Limited direct implications, but increased cybersecurity resilience could indirectly affect geopolitical stability by reducing successful cyber intrusions.
- Security / Counter-Terrorism: Enhanced security posture may deter certain threat actors, reducing the frequency of successful breaches via browser extensions.
- Cyber / Information Space: Potential for increased attacker innovation in evasion techniques; may lead to a temporary spike in undetected threats.
- Economic / Social: Improved security could reduce financial losses from breaches, but initial implementation costs may be a barrier for smaller organizations.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a risk assessment to identify vulnerable areas; implement Push Security’s capability; monitor for emerging evasion techniques.
- Medium-Term Posture (1–12 months): Develop partnerships with other security vendors for intelligence sharing; invest in training for security teams to recognize and respond to extension-based threats.
- Scenario Outlook:
- Best: Significant reduction in extension-based compromises; increased adoption of similar technologies across the industry.
- Worst: Attackers develop new evasion methods, rendering current detection capabilities less effective.
- Most-Likely: Gradual improvement in security posture with periodic adjustments to counter new threats.
6. Key Individuals and Entities
- Jacques Louw, Chief Product Officer at Push Security
- Push Security
- Chrome Web Store
- Cyberhaven
- Trust Wallet
7. Thematic Tags
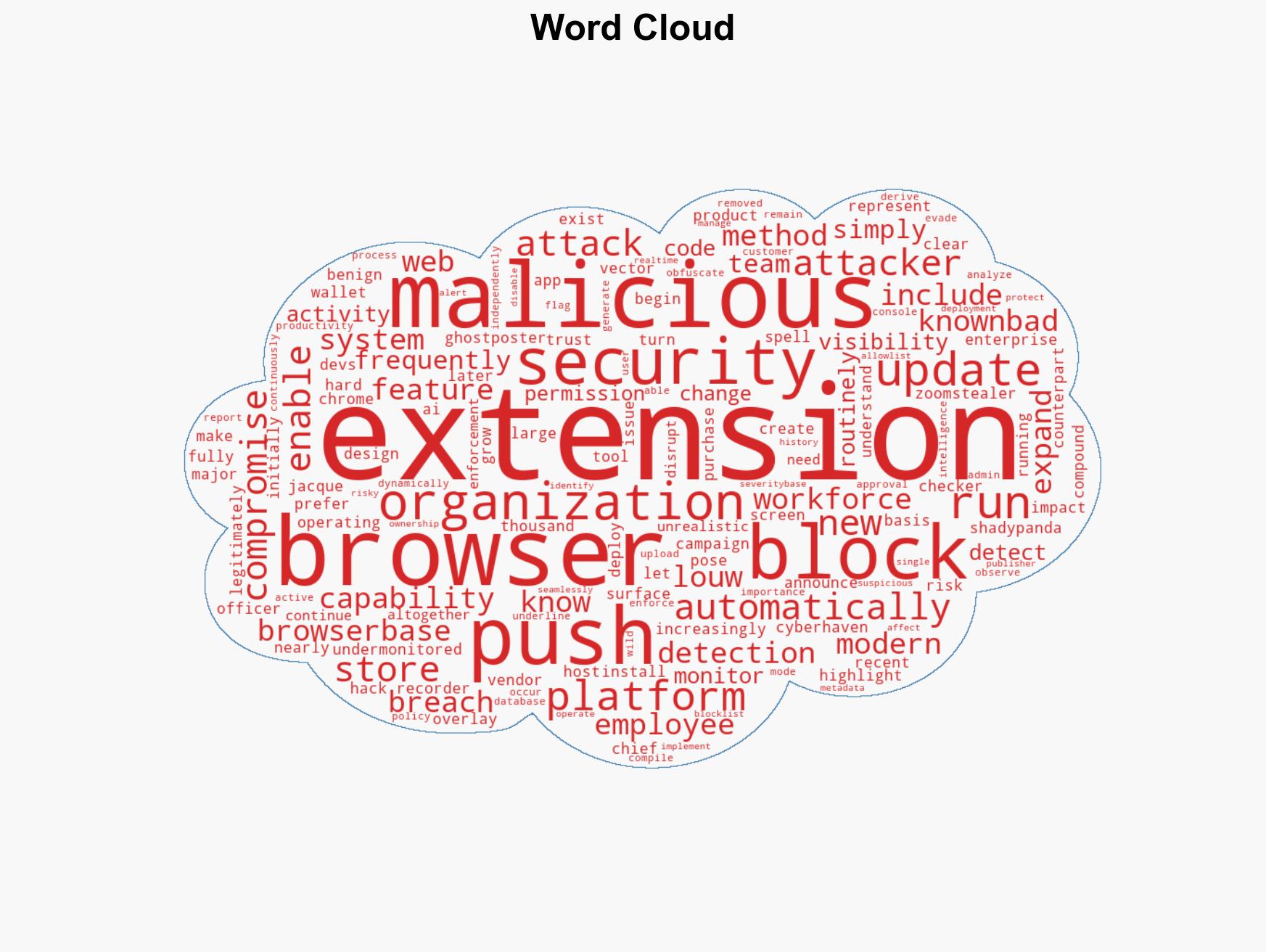
cybersecurity, browser extensions, threat detection, information security, cyber resilience, security innovation, threat mitigation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us