Transparent Tribe Leverages AI for High-Volume Malware Production in Targeted Campaign Against India
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Transparent Tribe Uses AI to Mass-Produce Malware Implants in Campaign Targeting India
1. BLUF (Bottom Line Up Front)
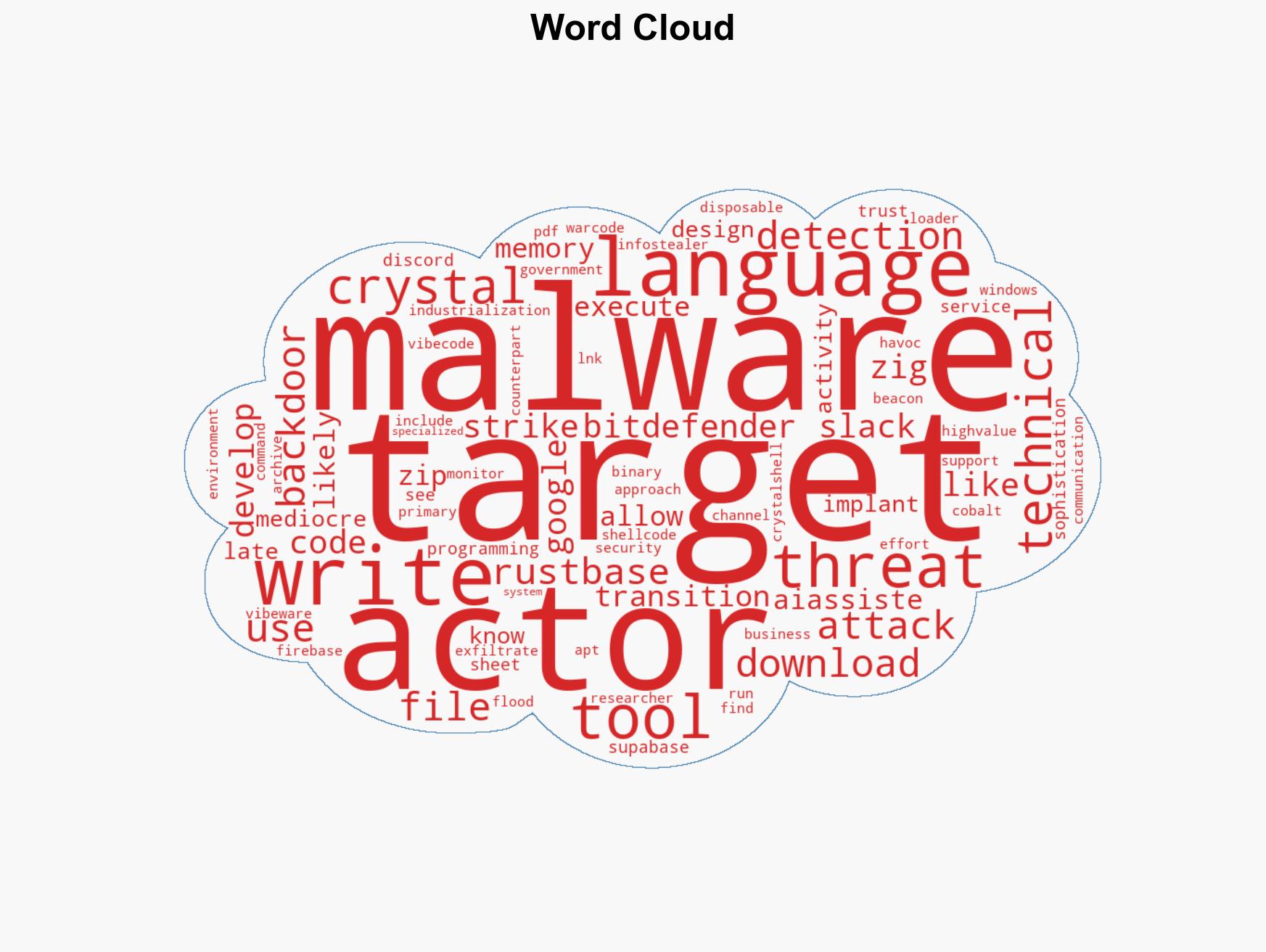
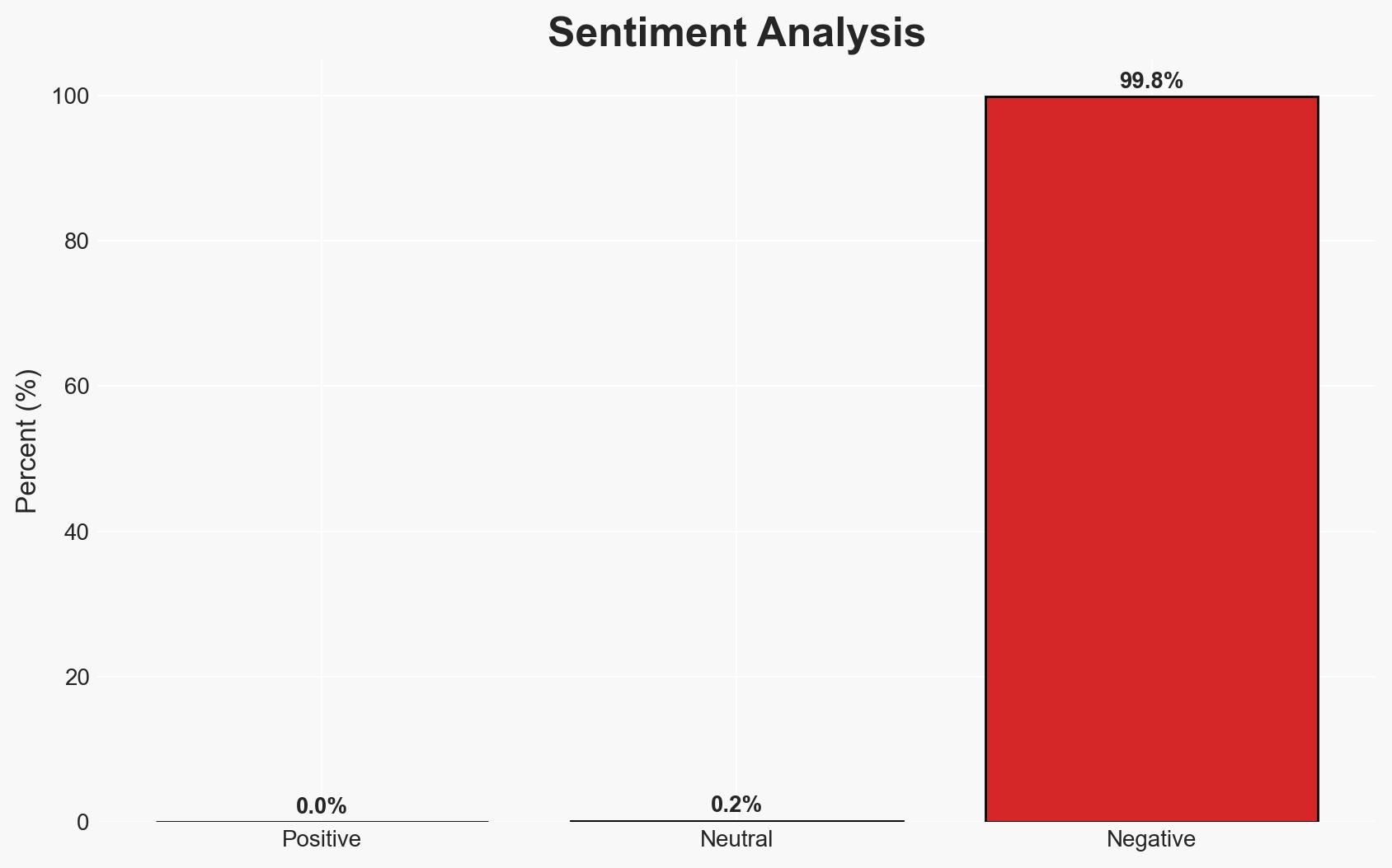
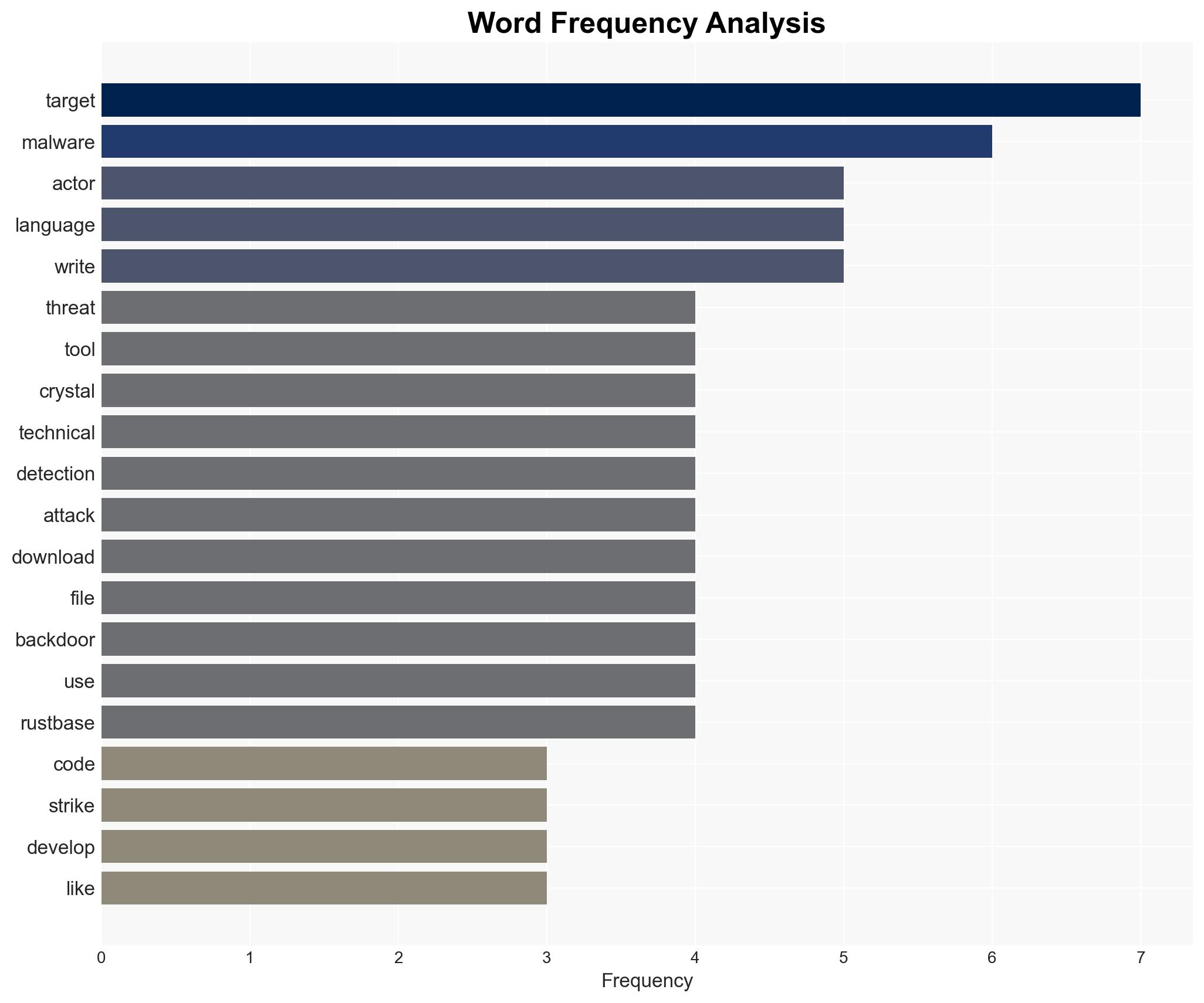
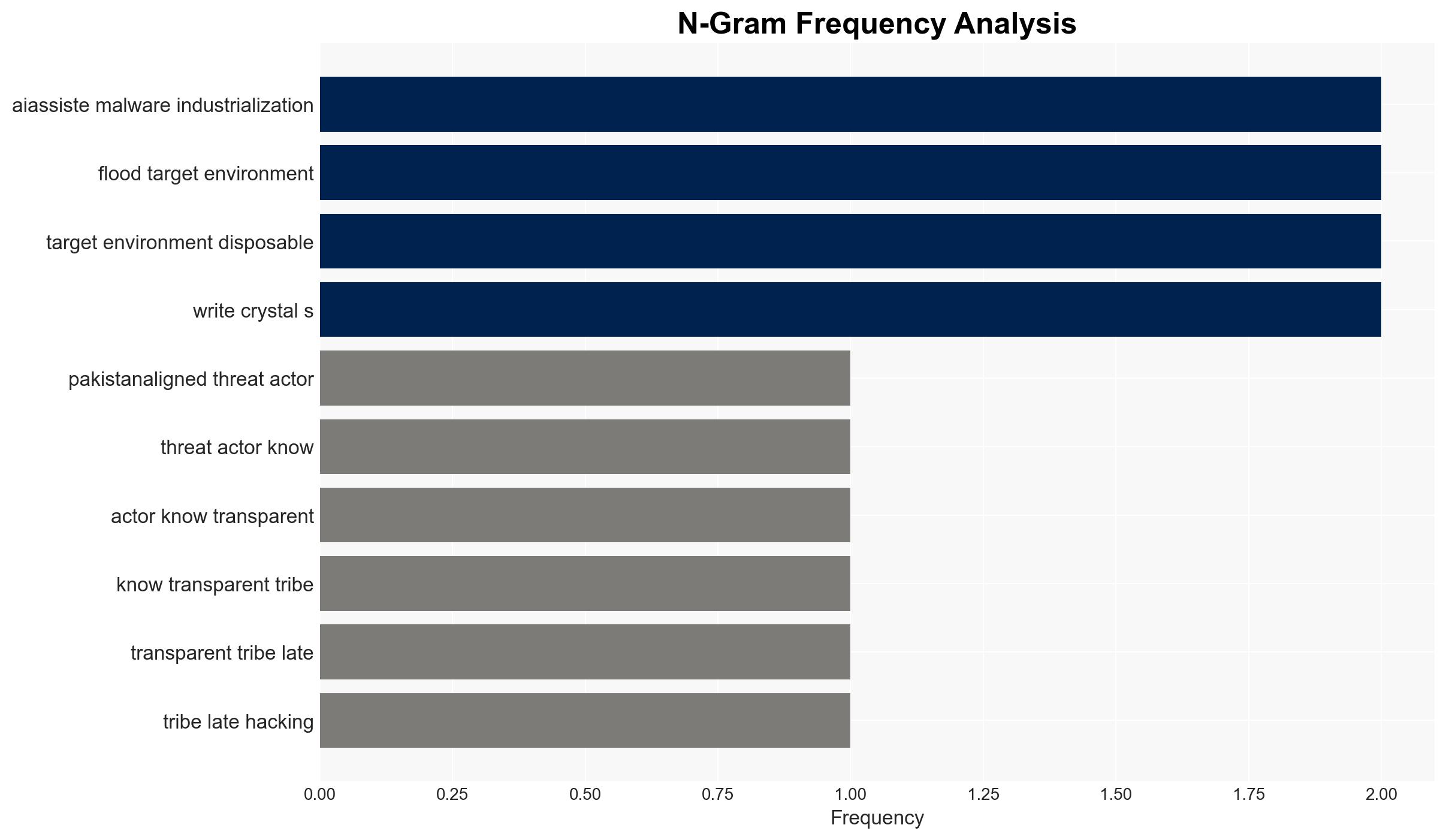
The Pakistan-aligned threat actor Transparent Tribe is leveraging AI-powered tools to mass-produce malware implants targeting the Indian government and its embassies, with moderate confidence in the assessment. This campaign signifies a shift towards AI-assisted malware industrialization, complicating detection efforts. The use of lesser-known programming languages and trusted services suggests a strategic adaptation in cyber operations.
2. Competing Hypotheses
- Hypothesis A: Transparent Tribe is using AI to mass-produce malware to overwhelm detection systems, focusing on volume over sophistication. This is supported by the use of polyglot binaries and trusted services to evade detection, but lacks detailed evidence on the effectiveness of this approach.
- Hypothesis B: The campaign represents an exploratory phase in AI-assisted cyber operations, with Transparent Tribe testing new tools and techniques rather than executing a fully operational strategy. This is supported by the use of experimental tools and the targeting of diverse entities, but is contradicted by the scale and coordination of the attacks.
- Assessment: Hypothesis A is currently better supported due to the observed scale and coordination of the attacks, indicating a deliberate strategy to flood target environments. Key indicators that could shift this judgment include evidence of significant operational impact or the discovery of more sophisticated malware components.
3. Key Assumptions and Red Flags
- Assumptions: Transparent Tribe has the capability to effectively utilize AI tools; the targeted entities have limited defenses against this type of attack; the campaign’s primary goal is to disrupt rather than exfiltrate sensitive information.
- Information Gaps: Detailed impact assessments of the malware on targeted systems; the extent of AI tool usage in the broader cyber threat landscape; confirmation of the campaign’s strategic objectives.
- Bias & Deception Risks: Potential bias from sources with vested interests in highlighting AI threats; risk of misattribution due to the use of common tools and services; possible exaggeration of AI capabilities by threat actors to enhance perceived threat.
4. Implications and Strategic Risks
This development could lead to increased adoption of AI tools by other threat actors, potentially altering the cyber threat landscape. The campaign may provoke a geopolitical response from India and its allies, impacting regional stability.
- Political / Geopolitical: Escalation of tensions between India and Pakistan; potential diplomatic fallout if attacks are linked to state actors.
- Security / Counter-Terrorism: Increased complexity in threat detection and response; potential for similar tactics to be adopted by other groups.
- Cyber / Information Space: Evolution of cyber tactics towards AI-assisted operations; potential erosion of trust in digital communication platforms.
- Economic / Social: Potential economic impact if critical infrastructure is targeted; public concern over cybersecurity threats may rise.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI-assisted malware trends; strengthen defenses against polyglot binaries; engage with cybersecurity partners for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop capabilities to detect and mitigate AI-generated threats; invest in AI research for defensive purposes; foster international cooperation on cyber norms.
- Scenario Outlook:
- Best: Effective countermeasures reduce the impact of AI-assisted attacks, leading to improved cybersecurity resilience.
- Worst: Widespread adoption of AI tools by threat actors overwhelms current defenses, causing significant disruptions.
- Most-Likely: Gradual increase in AI-assisted attacks prompts incremental improvements in detection and response capabilities.
6. Key Individuals and Entities
- Transparent Tribe (Pakistan-aligned threat actor)
- Bitdefender (Romanian cybersecurity vendor)
- APT36 (Linked to the campaign)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, AI in cyber operations, malware industrialization, geopolitical tensions, threat actor tactics
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us