APT36 Employs AI-Generated Malware to Overwhelm Indian Government Networks with Low-Quality Code
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Pakistan-Linked APT36 Floods Indian Govt Networks With AI-Made Vibeware
1. BLUF (Bottom Line Up Front)
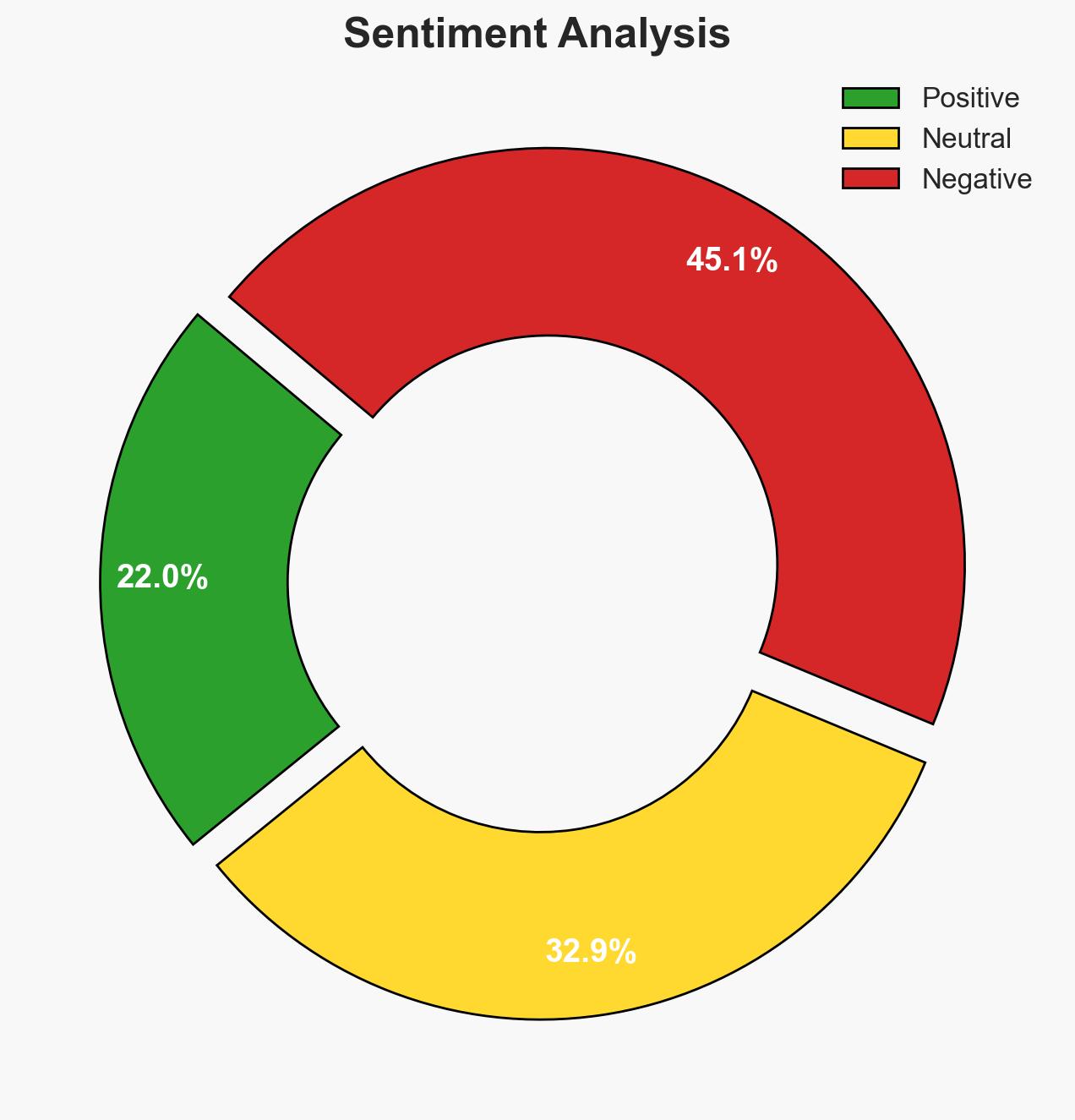
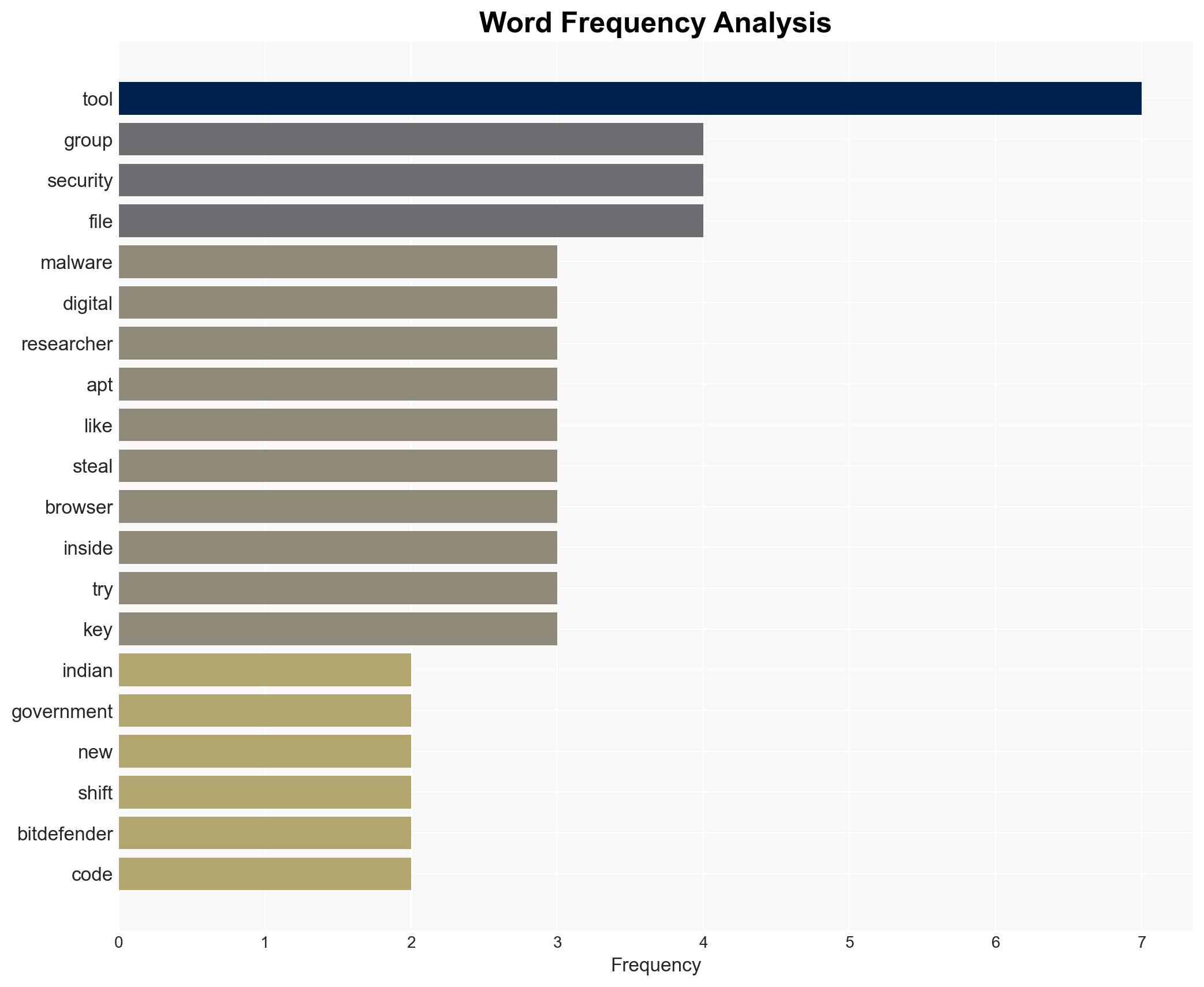
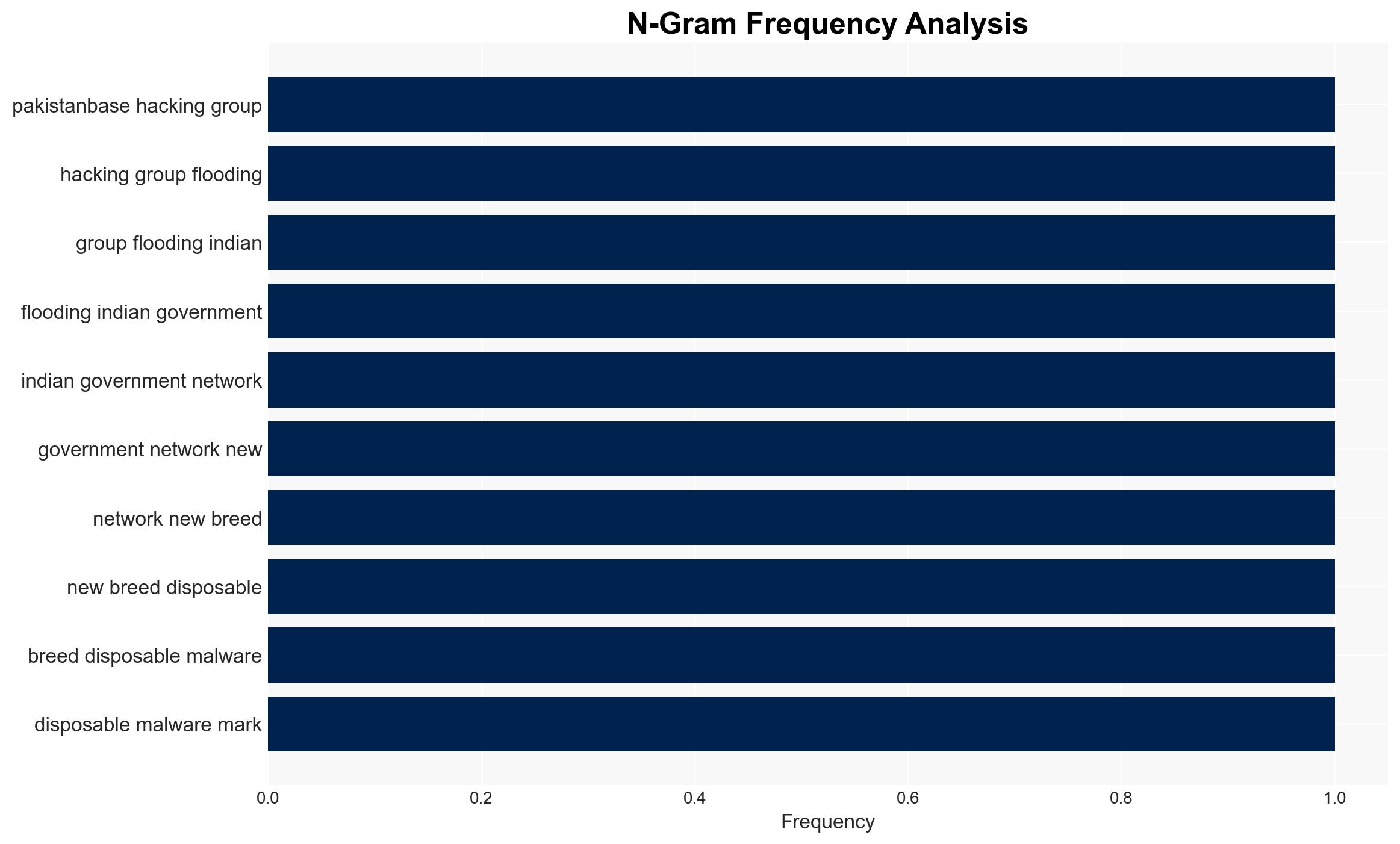
APT36, a Pakistan-based hacking group, is targeting Indian government networks with AI-generated malware, termed “Vibeware,” to overwhelm defenses through volume rather than sophistication. The operation includes psychological misdirection tactics and exploits trust in digital environments. This activity poses a moderate threat to Indian cybersecurity infrastructure with moderate confidence in the assessment.
2. Competing Hypotheses
- Hypothesis A: APT36 is using AI-generated Vibeware to exploit volume-based attacks, overwhelming Indian defenses with numerous low-quality malware. This is supported by the observed shift to niche programming languages and the use of psychological misdirection. Uncertainties include the actual impact of these attacks and the potential for more sophisticated tactics.
- Hypothesis B: The use of Vibeware is a diversionary tactic, and the real objective is to test new infiltration methods or gather intelligence on Indian cybersecurity responses. This is supported by the strategic use of common platforms like Google Sheets and Discord to mask activities. Contradicting evidence includes the low quality of the malware, suggesting a lack of sophistication.
- Assessment: Hypothesis A is currently better supported due to the volume and nature of the attacks, which align with the observed tactics and errors in execution. Indicators that could shift this judgment include the emergence of more sophisticated malware or evidence of deeper strategic objectives.
3. Key Assumptions and Red Flags
- Assumptions: APT36 has the capability to produce AI-generated malware rapidly; Indian cybersecurity defenses are primarily focused on quality rather than volume; psychological misdirection is a deliberate tactic.
- Information Gaps: The full extent of the damage caused by these attacks; the potential for more sophisticated malware being developed concurrently; the strategic objectives of APT36 beyond immediate disruption.
- Bias & Deception Risks: Confirmation bias in interpreting the low quality of malware as indicative of overall capability; potential deception in the use of cultural references to mislead investigators.
4. Implications and Strategic Risks
The development of AI-generated Vibeware by APT36 could lead to increased frequency of cyberattacks, straining Indian cybersecurity resources. This tactic may evolve into more sophisticated operations, impacting regional stability.
- Political / Geopolitical: Escalation of cyber tensions between India and Pakistan, potentially affecting diplomatic relations.
- Security / Counter-Terrorism: Increased vulnerability of Indian government networks, necessitating enhanced cybersecurity measures.
- Cyber / Information Space: Potential for broader adoption of AI-generated malware tactics by other actors, complicating cyber defense strategies.
- Economic / Social: Potential disruption of government services, impacting public trust and economic activities reliant on secure digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of government networks for AI-generated malware signatures; increase awareness and training for staff on phishing tactics.
- Medium-Term Posture (1–12 months): Develop partnerships for intelligence sharing on AI-generated threats; invest in AI-driven cybersecurity tools to counter volume-based attacks.
- Scenario Outlook:
- Best: Improved defenses lead to a reduction in successful attacks, with increased international cooperation on cybersecurity.
- Worst: Escalation of attacks overwhelms defenses, leading to significant data breaches and political fallout.
- Most-Likely: Continued low-level attacks with gradual improvements in defense capabilities, maintaining a status quo of cyber tension.
6. Key Individuals and Entities
- APT36 (Transparent Tribe) – Pakistan-based hacking group
- Indian Government Networks – Primary target
- Bitdefender – Cybersecurity firm providing analysis
7. Thematic Tags
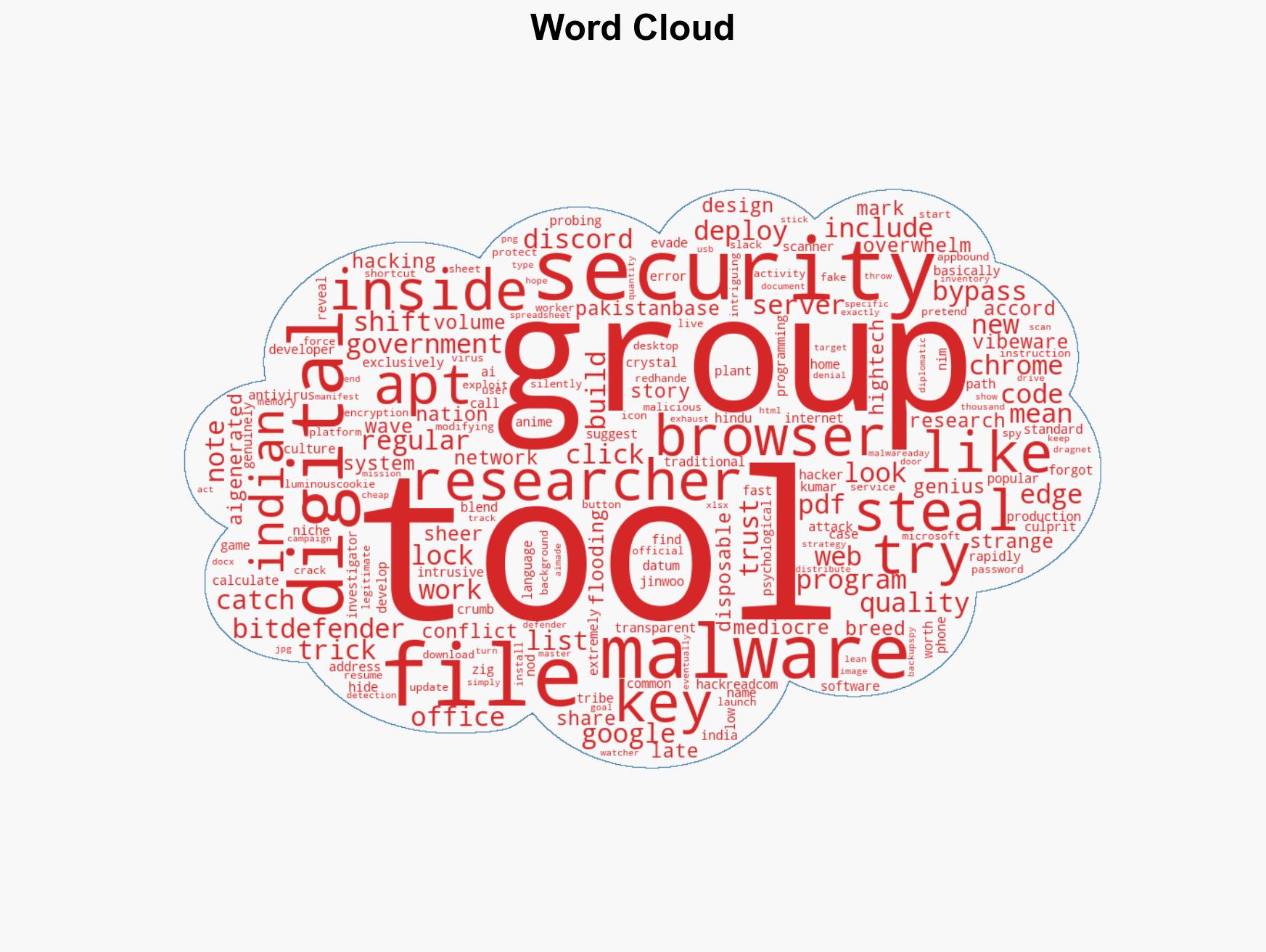
cybersecurity, cyber-espionage, AI-generated malware, India-Pakistan relations, Vibeware, psychological operations, digital trust exploitation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us