California’s EV Charging Network Raises Concerns Over Potential Chinese Surveillance Ties
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
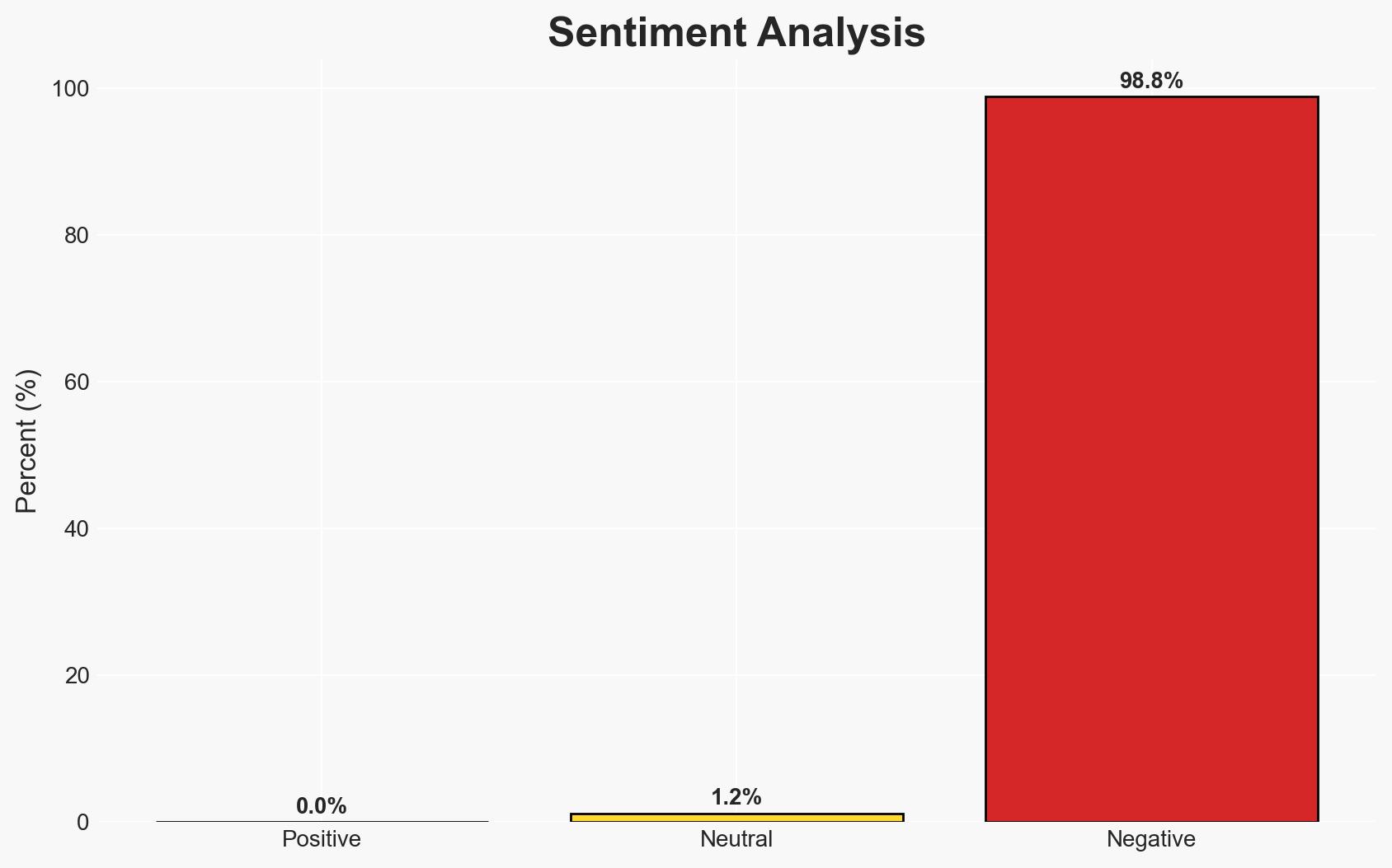
Intelligence Report: How Chinas EV charging tech could spy on Californians
1. BLUF (Bottom Line Up Front)
There is a moderate confidence that Chinese-linked EV charging infrastructure in California could be used for surveillance purposes, potentially compromising national security. This development primarily affects California residents and U.S. national security interests. The most likely hypothesis is that Chinese technology embedded in EV charging networks could collect sensitive data on U.S. citizens and military personnel.
2. Competing Hypotheses
- Hypothesis A: Chinese-linked EV charging networks in California are primarily intended for commercial purposes, with any surveillance capabilities being incidental. Supporting evidence includes the commercial nature of the partnerships and investments. However, the potential for data collection on sensitive movements remains a key uncertainty.
- Hypothesis B: The integration of Chinese technology in California’s EV charging infrastructure is a deliberate strategy by the Chinese government to conduct surveillance on U.S. citizens and military personnel. This is supported by historical precedents of data misuse and the strategic interest in monitoring U.S. military movements.
- Assessment: Hypothesis B is currently better supported due to the strategic implications of data collection and historical precedents of similar surveillance activities by state actors. Key indicators that could shift this judgment include evidence of data misuse or explicit policy directives from the Chinese government.
3. Key Assumptions and Red Flags
- Assumptions: The Chinese government has strategic interests in monitoring U.S. military and civilian movements; California’s infrastructure policies do not fully account for national security risks; U.S. domestic companies can meet EV infrastructure needs without foreign involvement.
- Information Gaps: Detailed technical specifications of the EV charging systems and their data handling capabilities; direct evidence of Chinese government directives regarding data collection from these networks.
- Bias & Deception Risks: Potential bias in sources advocating for domestic production; risk of underestimating commercial motivations behind Chinese investments; possibility of deceptive practices in data reporting by involved companies.
4. Implications and Strategic Risks
This development could lead to increased tensions between the U.S. and China, particularly if surveillance activities are confirmed. It may also prompt a reevaluation of foreign technology in critical infrastructure.
- Political / Geopolitical: Potential for diplomatic disputes and increased scrutiny of Chinese investments in U.S. infrastructure.
- Security / Counter-Terrorism: Increased risk of espionage and data exploitation targeting U.S. military and critical infrastructure.
- Cyber / Information Space: Potential for cyber vulnerabilities and data breaches within the EV charging network.
- Economic / Social: Possible disruptions in the EV market and public trust in infrastructure security; economic implications for companies reliant on Chinese technology.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a security audit of existing EV charging networks; increase monitoring of data flows and access points.
- Medium-Term Posture (1–12 months): Develop partnerships with domestic tech firms to enhance infrastructure security; implement stricter regulations on foreign technology in critical sectors.
- Scenario Outlook:
- Best: Strengthened domestic capabilities and secure infrastructure with minimal foreign influence.
- Worst: Confirmed surveillance leading to significant diplomatic fallout and compromised national security.
- Most-Likely: Gradual policy adjustments and increased scrutiny of foreign technology in critical sectors.
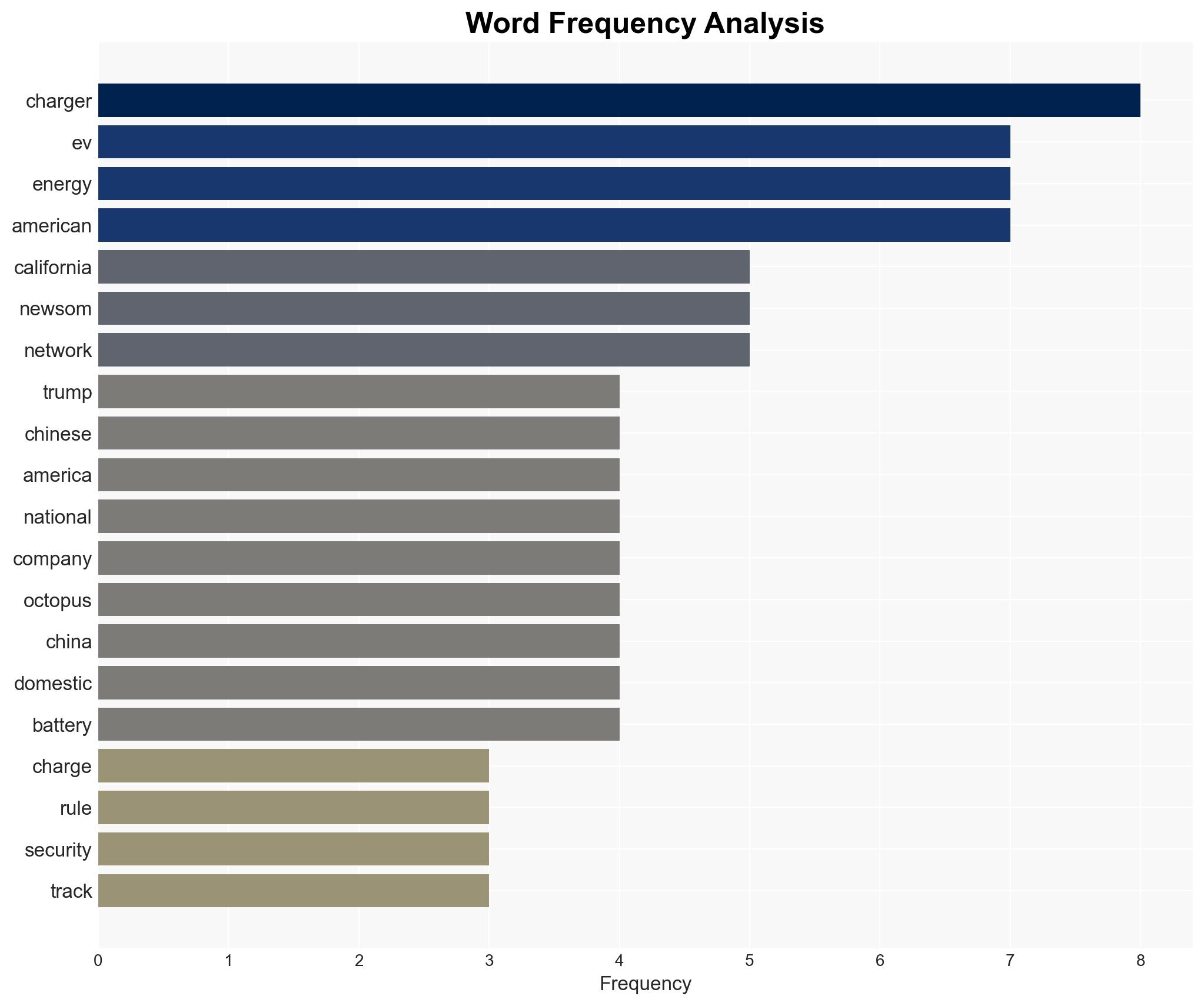
6. Key Individuals and Entities
- President Trump
- Governor Gavin Newsom
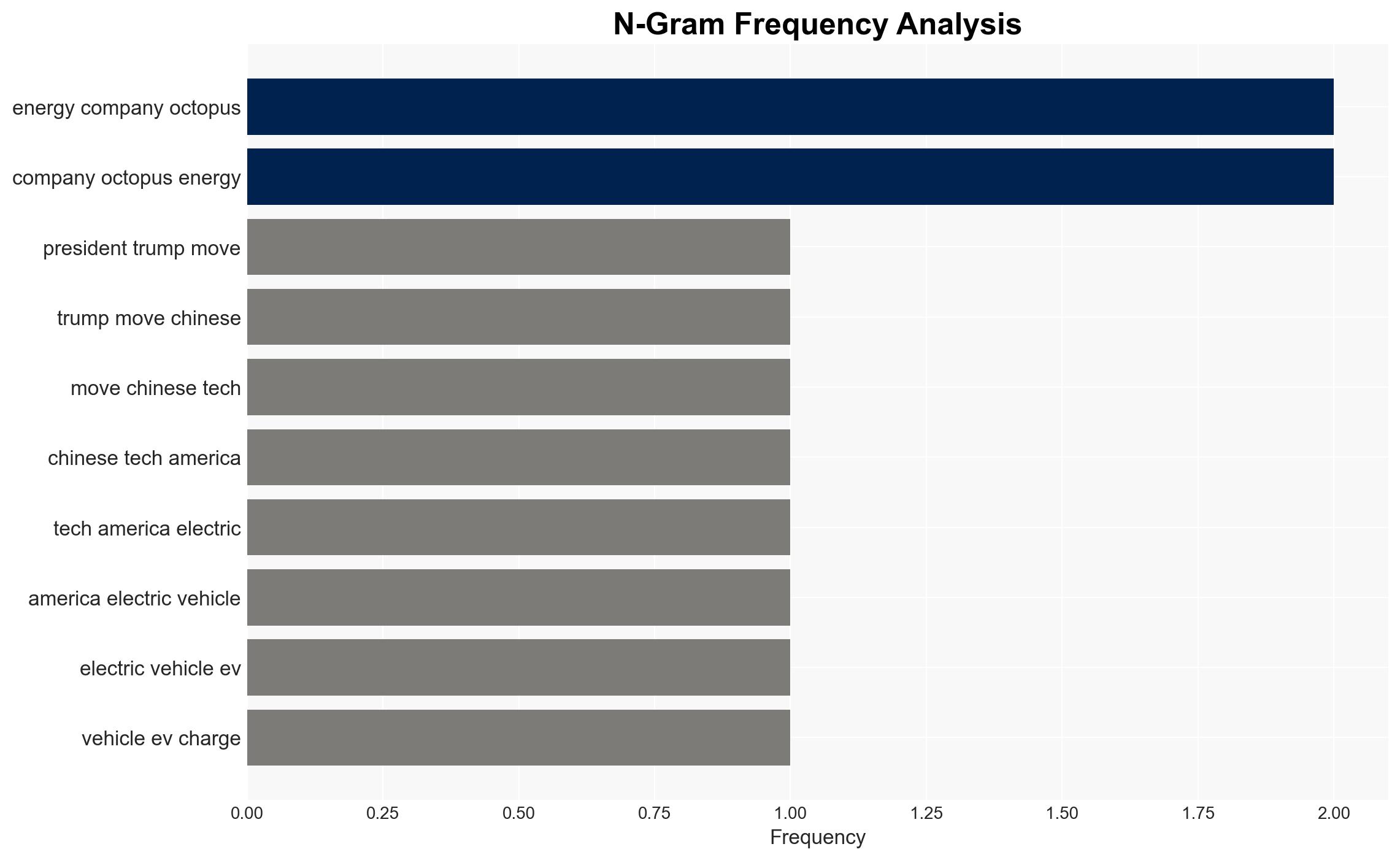
- Octopus Energy Generation
- PGC Power
- Sparkz
7. Thematic Tags
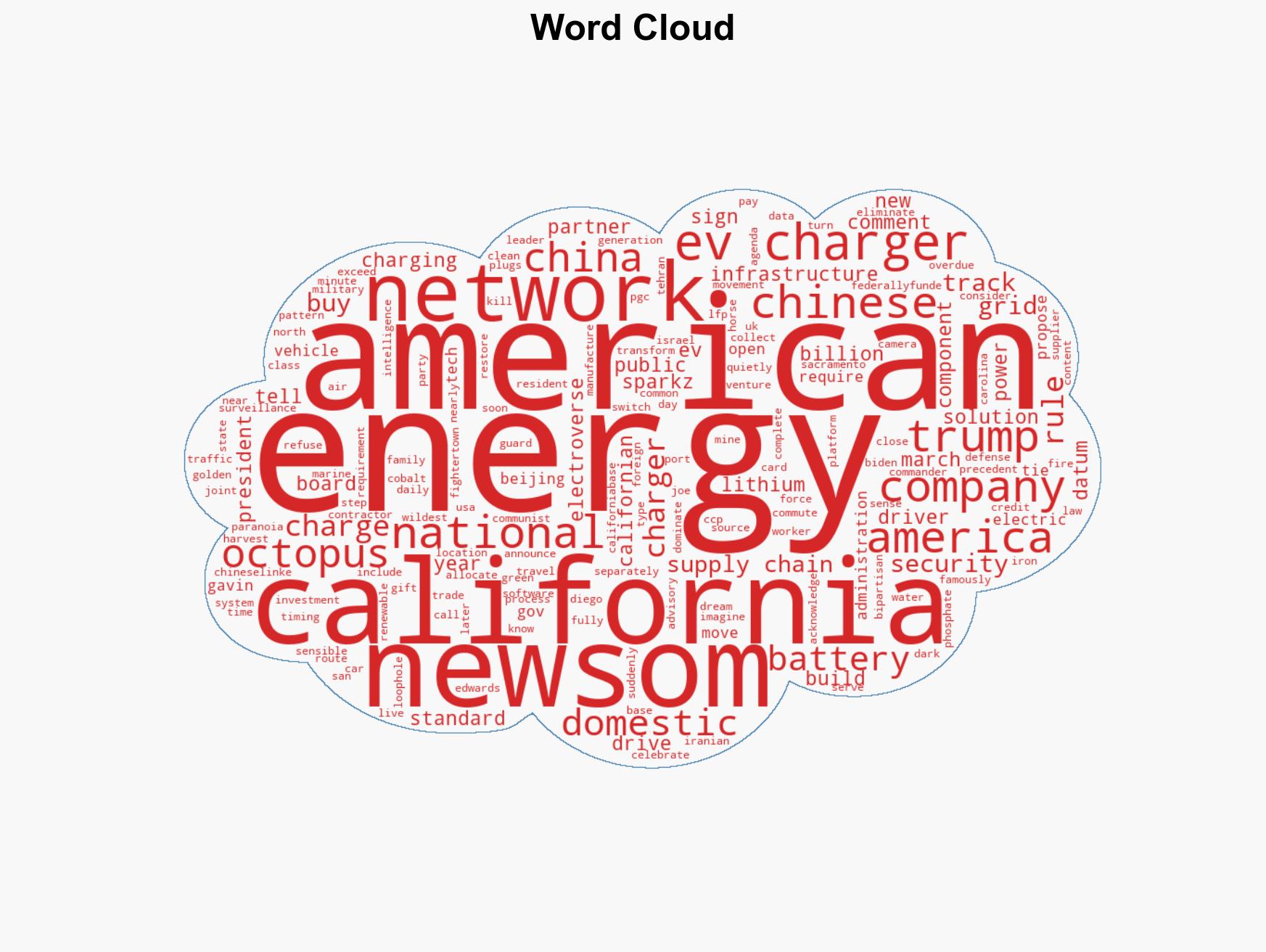
national security threats, national security, surveillance, EV infrastructure, China-U.S. relations, cyber-espionage, critical infrastructure, foreign investment
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us