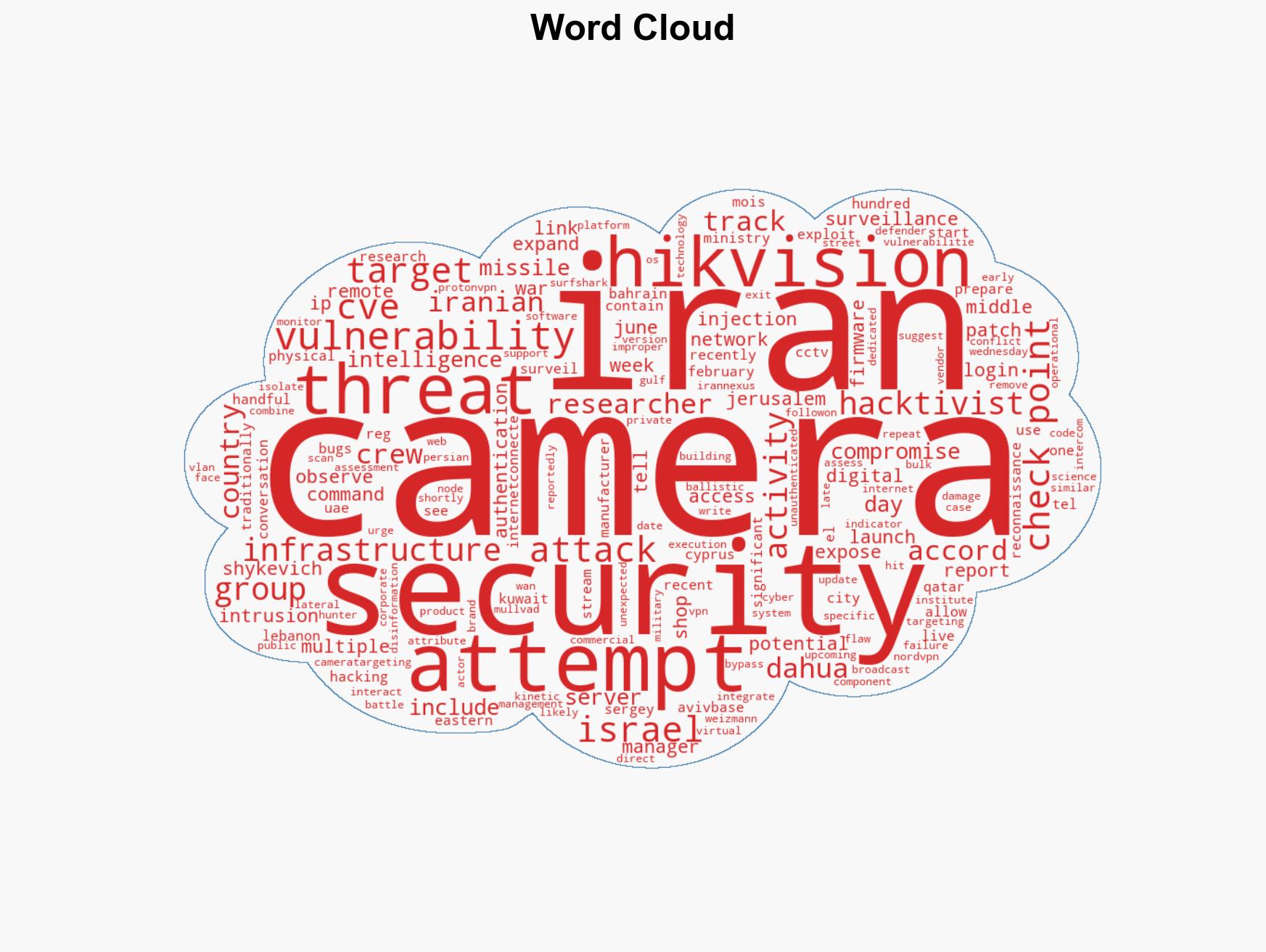
Iranian Hacking Groups Target Surveillance Cameras in Israel and Middle East Amid Escalating Conflict
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ‘Hundreds’ of Iranian hacking attempts have hit surveillance cameras since the missile strikes
1. BLUF (Bottom Line Up Front)
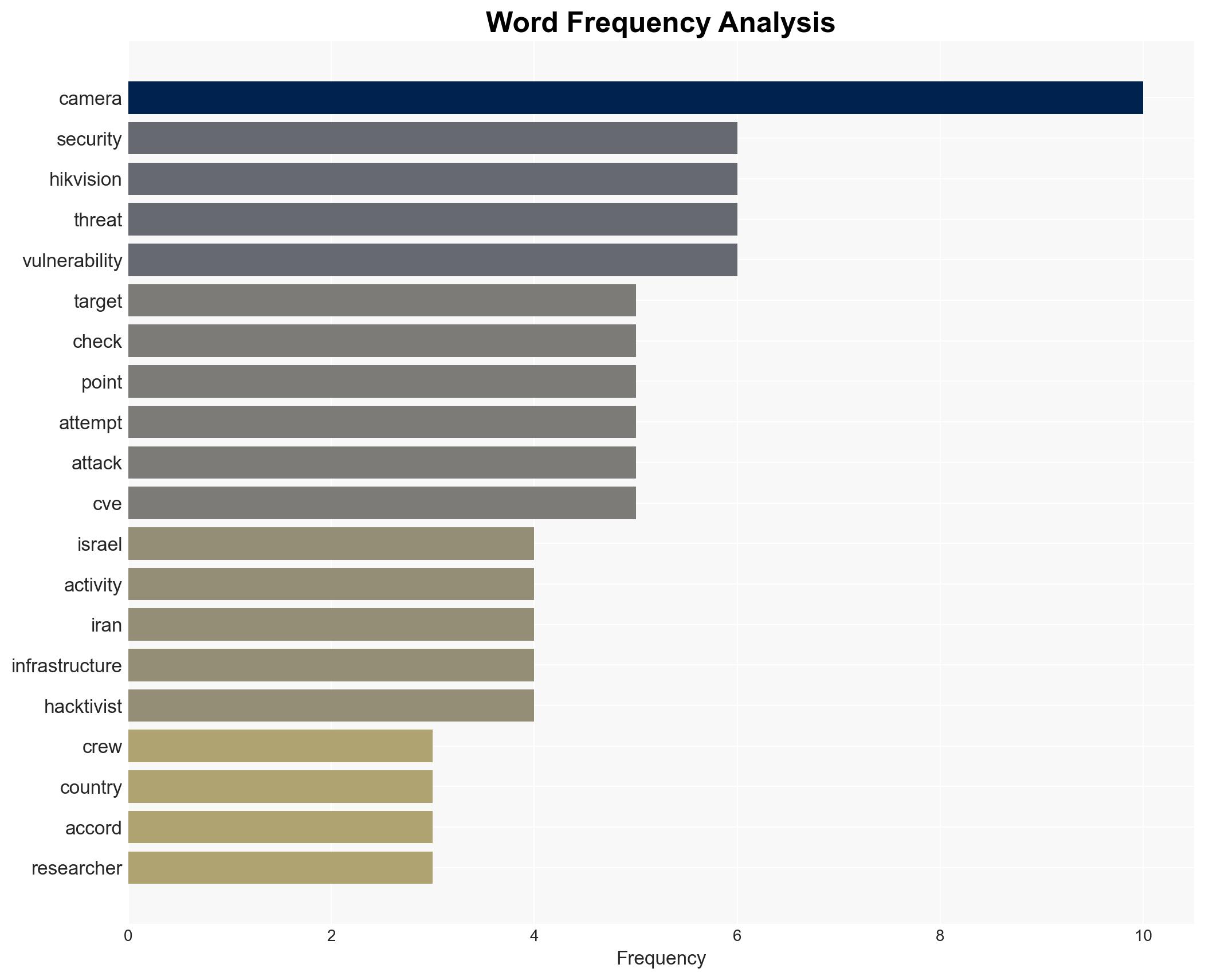
The recent surge in Iranian hacking attempts targeting surveillance cameras in Israel and other Middle Eastern countries likely serves as digital reconnaissance for potential kinetic actions. This activity, attributed to Iran-linked threat actors, suggests preparation for further military engagements. The affected countries include Israel, Qatar, Bahrain, Kuwait, the UAE, Cyprus, and Lebanon. Overall confidence in this assessment is moderate, given the historical pattern of similar Iranian tactics.
2. Competing Hypotheses
- Hypothesis A: The hacking attempts are part of a coordinated Iranian strategy to gather intelligence for future missile strikes. This is supported by historical precedents and the specific targeting of countries involved in recent missile activities. However, the lack of direct evidence linking specific attacks to these reconnaissance efforts remains a key uncertainty.
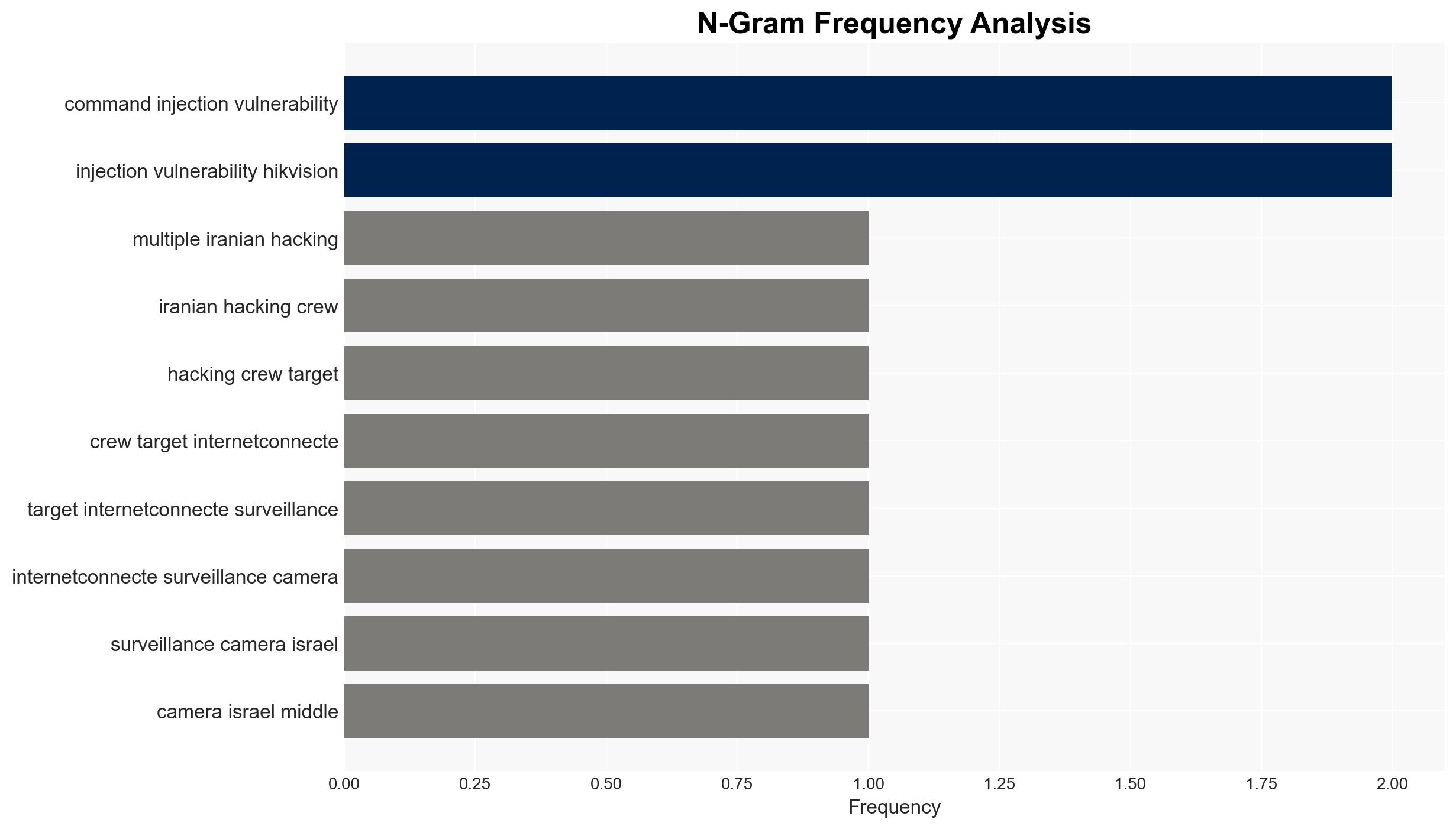
- Hypothesis B: The hacking attempts are primarily aimed at creating cyber disruption rather than preparing for kinetic actions. This could be supported by the use of vulnerabilities in widely used camera brands, suggesting a broader cyber campaign. Contradicting this is the historical use of such tactics by Iran for physical attack preparation.
- Assessment: Hypothesis A is currently better supported due to the alignment with Iran’s historical use of digital reconnaissance for kinetic operations. Indicators that could shift this judgment include evidence of cyber disruptions without subsequent physical attacks.
3. Key Assumptions and Red Flags
- Assumptions: Iran has the capability and intent to conduct both cyber and kinetic operations; the targeted countries are of strategic interest to Iran; the vulnerabilities in Hikvision and Dahua cameras are not fully mitigated.
- Information Gaps: Specific details on the success rate of the hacking attempts; direct evidence linking compromised cameras to subsequent physical attacks.
- Bias & Deception Risks: Potential bias in attributing all hacking attempts to Iran; reliance on a single source (Check Point) for threat intelligence; possible Iranian misinformation to obscure true intentions.
4. Implications and Strategic Risks
This development could lead to increased tensions and potential military escalations in the Middle East. The use of cyber means for reconnaissance may evolve into more sophisticated hybrid warfare tactics.
- Political / Geopolitical: Escalation of conflicts involving Iran and targeted countries, potentially drawing in international actors.
- Security / Counter-Terrorism: Heightened threat environment requiring increased vigilance and defensive measures against both cyber and physical attacks.
- Cyber / Information Space: Increased focus on cybersecurity measures for critical infrastructure, particularly surveillance systems.
- Economic / Social: Potential disruptions to regional stability and economic activities, particularly if physical attacks follow cyber reconnaissance.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently update firmware on vulnerable cameras, restrict internet access to surveillance systems, and enhance monitoring for suspicious activities.
- Medium-Term Posture (1–12 months): Develop resilience measures, increase regional cybersecurity collaboration, and invest in advanced threat detection capabilities.
- Scenario Outlook:
- Best: Successful mitigation of vulnerabilities prevents further reconnaissance and deters physical attacks.
- Worst: Unmitigated vulnerabilities lead to successful reconnaissance and subsequent military strikes.
- Most-Likely: Continued cyber reconnaissance with sporadic physical engagements, prompting ongoing regional tensions.
6. Key Individuals and Entities
- Iranian Ministry of Intelligence and Security (MOIS)
- Check Point Research
- Hikvision
- Dahua
- Sergey Shykevich, Threat Intelligence Group Manager at Check Point Research
7. Thematic Tags
cybersecurity, cyber-espionage, digital reconnaissance, Middle East security, Iranian cyber operations, surveillance vulnerabilities, kinetic warfare preparation, regional stability
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us