Iranian MuddyWater Hackers Infiltrate US Networks with New Dindoor Backdoor Following Military Strikes
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran-Linked MuddyWater Hackers Target US Networks With New Dindoor Backdoor
1. BLUF (Bottom Line Up Front)
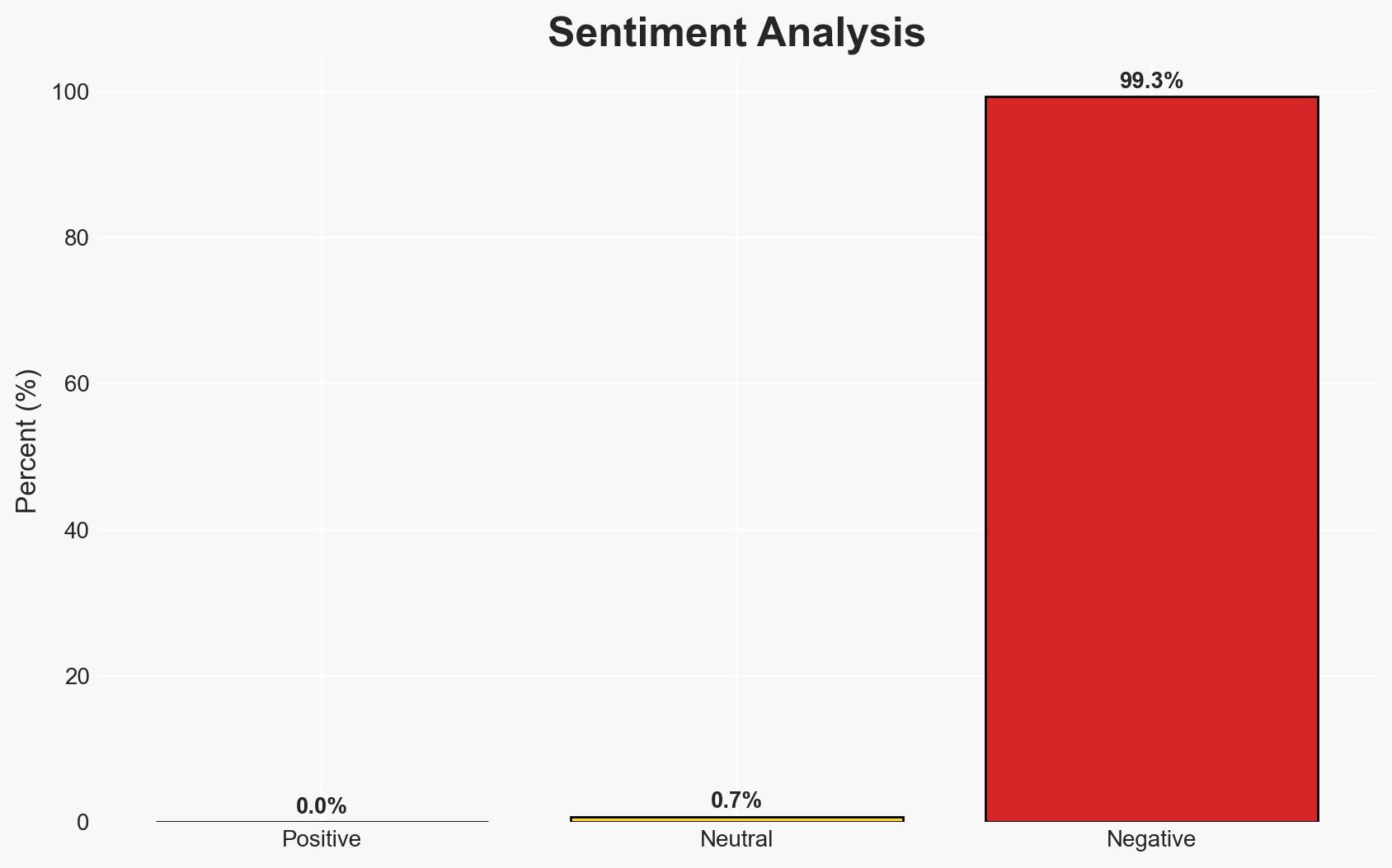
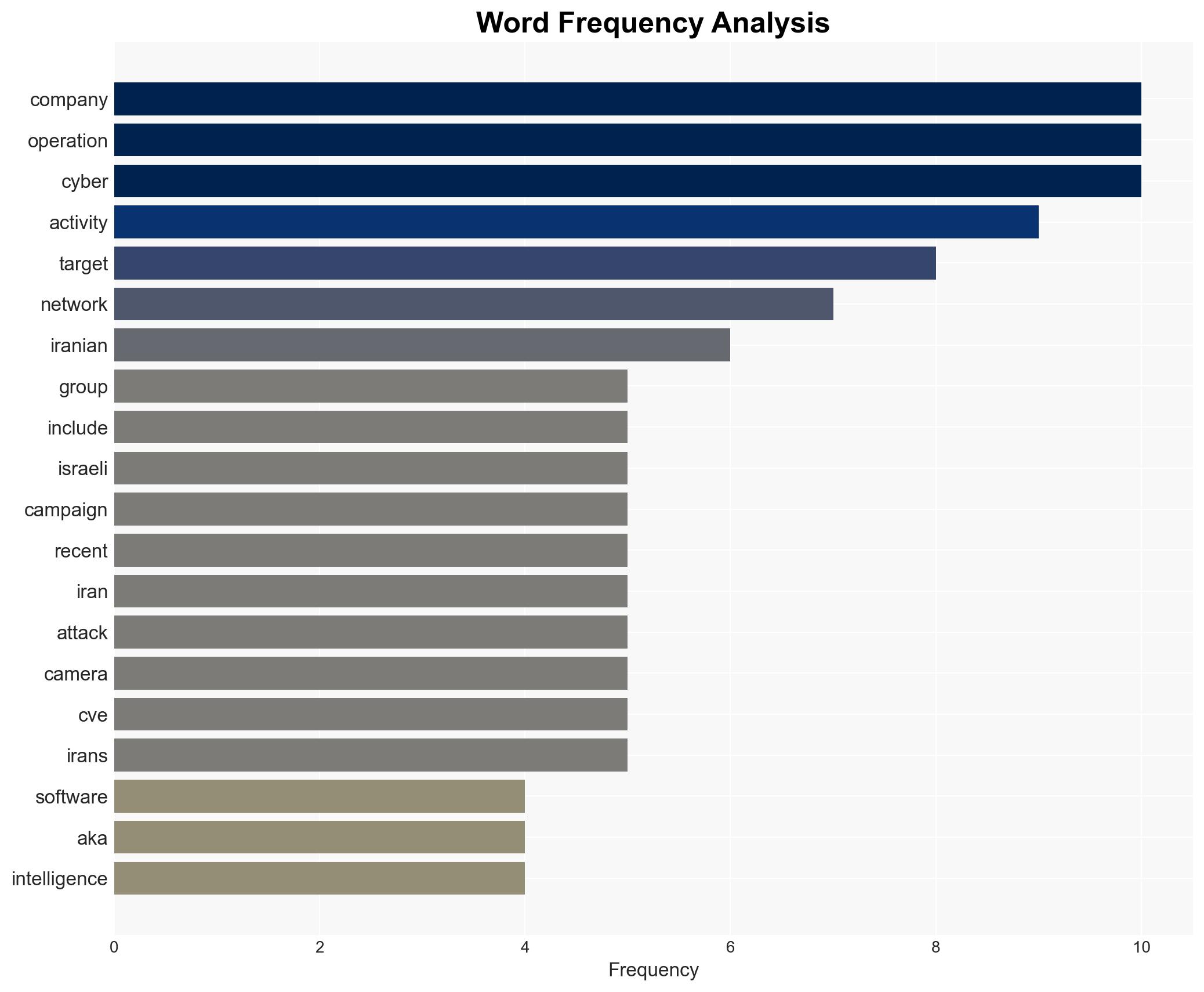
The Iranian state-sponsored hacking group MuddyWater is actively targeting U.S. networks, including banks, airports, and a software company linked to defense industries, using a new backdoor named Dindoor. This activity likely aims to gather intelligence and disrupt operations in response to recent military actions involving the U.S. and Israel. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: MuddyWater is conducting these cyber operations as a direct response to military actions by the U.S. and Israel, aiming to gather intelligence and possibly disrupt critical infrastructure. This is supported by the timing of the attacks and the targeting of defense-related entities. However, the full extent of data exfiltration success remains unknown.
- Hypothesis B: The cyber operations are part of a broader, ongoing campaign by Iran to enhance its cyber capabilities and assert influence, independent of recent military actions. This is supported by the group’s historical activities and the improvement in their cyber tools and techniques. Contradicting this is the specific timing and selection of targets.
- Assessment: Hypothesis A is currently better supported due to the correlation between the timing of the attacks and recent military events. Key indicators that could shift this judgment include evidence of long-term strategic planning unrelated to recent geopolitical events.
3. Key Assumptions and Red Flags
- Assumptions: MuddyWater is acting under the direction of the Iranian MOIS; the primary goal is intelligence gathering and disruption; the Dindoor backdoor is a newly developed tool for this campaign.
- Information Gaps: The extent of data exfiltration success; the full scope of MuddyWater’s operational capabilities; potential other targets not yet identified.
- Bias & Deception Risks: Potential over-reliance on attribution to MuddyWater; confirmation bias in linking all activities to recent military events; possible Iranian deception to mislead attribution efforts.
4. Implications and Strategic Risks
This development could lead to increased cyber tensions between Iran and Western nations, potentially escalating into broader geopolitical conflicts. The sophistication of the attacks suggests a growing cyber threat capability from Iran.
- Political / Geopolitical: Potential for increased sanctions or retaliatory cyber actions against Iran.
- Security / Counter-Terrorism: Heightened alert for critical infrastructure sectors; potential for physical security measures to be impacted by cyber disruptions.
- Cyber / Information Space: Increased vigilance required for network defenses; potential for misinformation campaigns linked to cyber activities.
- Economic / Social: Disruption to financial and transportation sectors could impact economic stability and public confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure networks; collaborate with international partners for intelligence sharing; conduct vulnerability assessments.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical sectors; invest in cybersecurity training and awareness; strengthen public-private partnerships.
- Scenario Outlook: Best: De-escalation and improved cyber defenses; Worst: Escalation into broader conflict with significant cyber and physical impacts; Most-Likely: Continued low-level cyber skirmishes with periodic escalations.
6. Key Individuals and Entities
- MuddyWater (Seedworm) – Iranian state-sponsored hacking group
- Iranian Ministry of Intelligence and Security (MOIS)
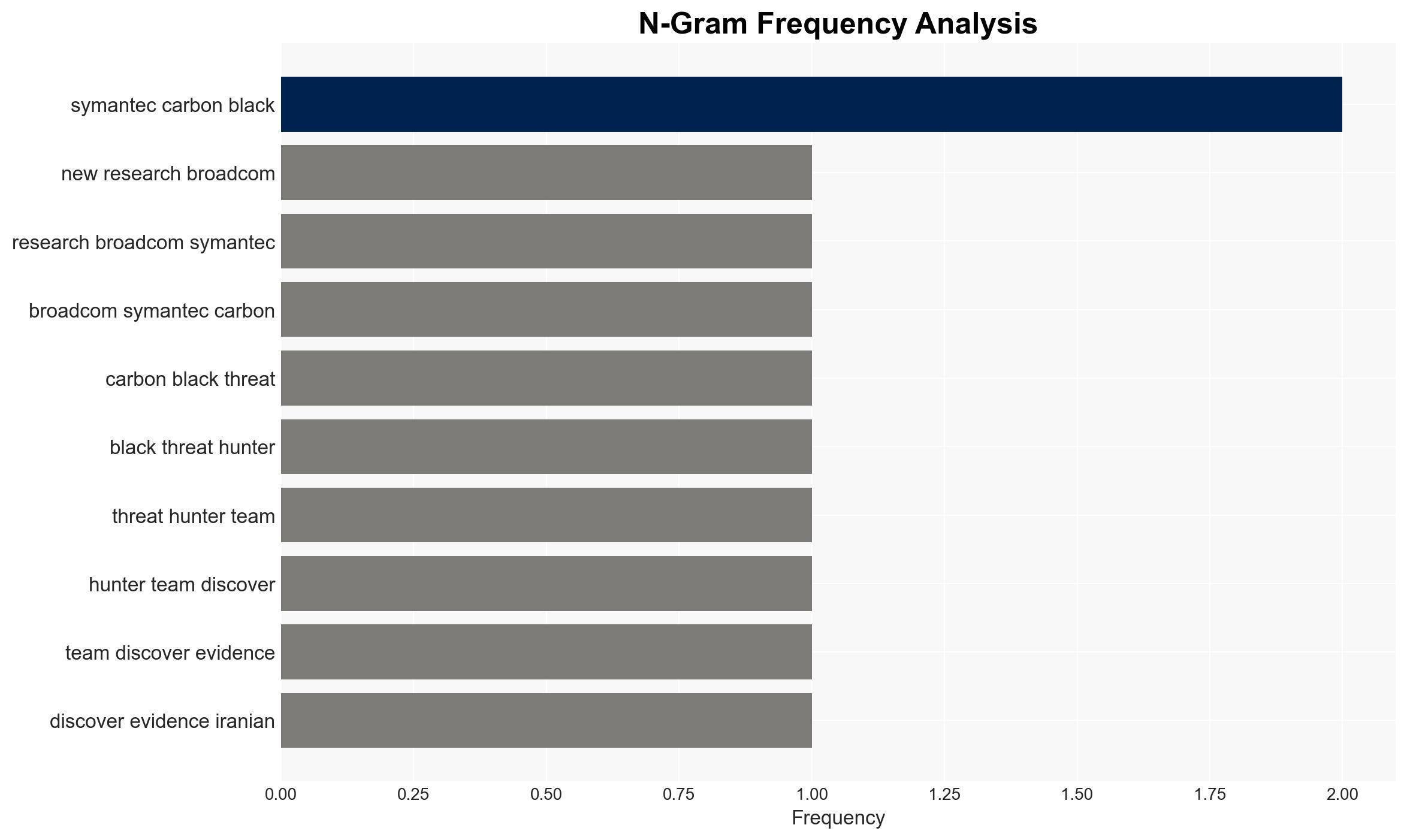
- Symantec and Carbon Black Threat Hunter Team
- U.S. banks, airports, and defense-related software companies
- Backblaze – American cloud storage company
7. Thematic Tags
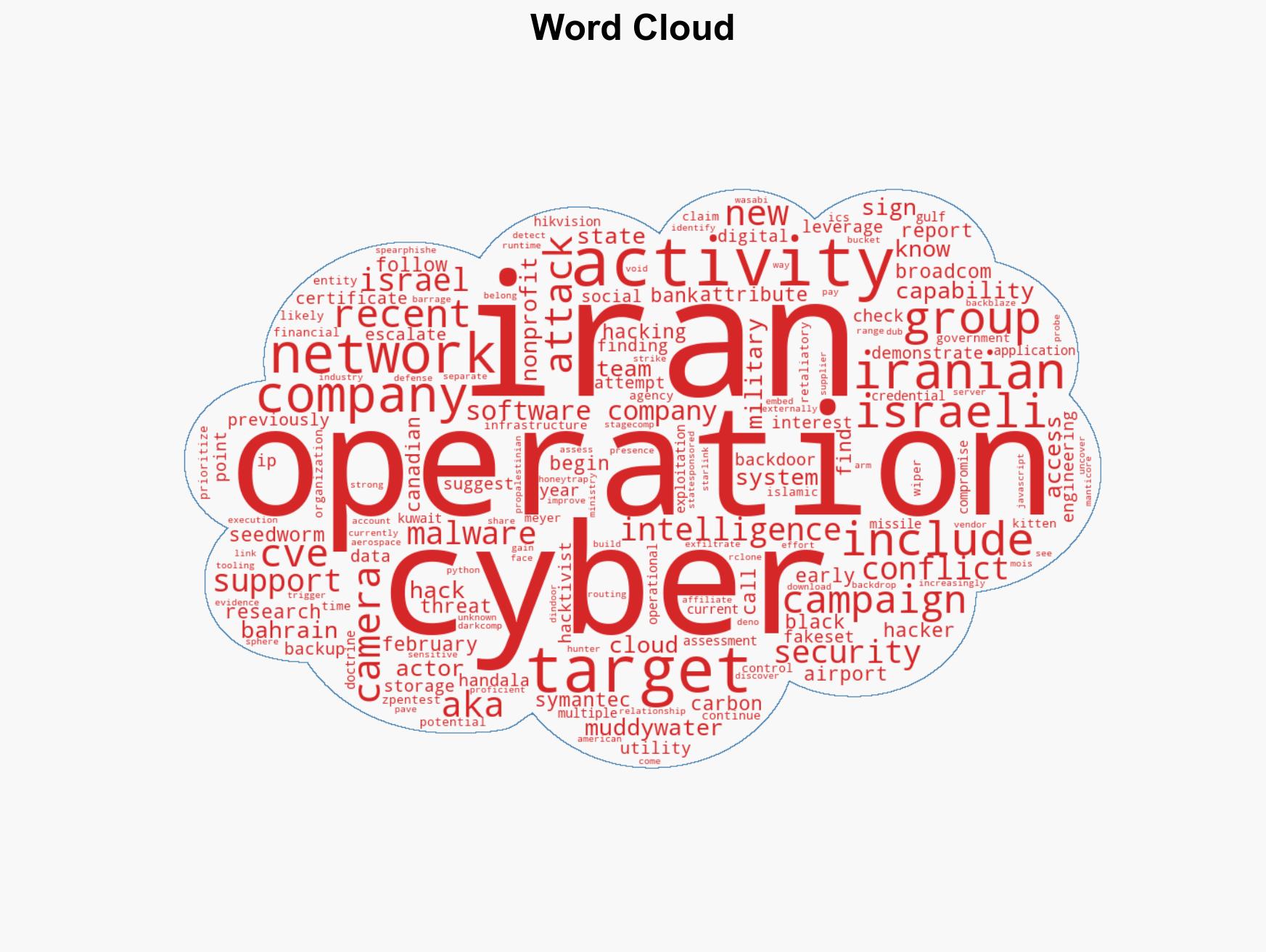
cybersecurity, cyber-espionage, Iran, MuddyWater, national security, critical infrastructure, cyber defense, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us