Ransomware gangs shift tactics to data theft as effective backup strategies mitigate impacts on businesses
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Backup strategies are working and ransomware gangs are responding with data theft
1. BLUF (Bottom Line Up Front)
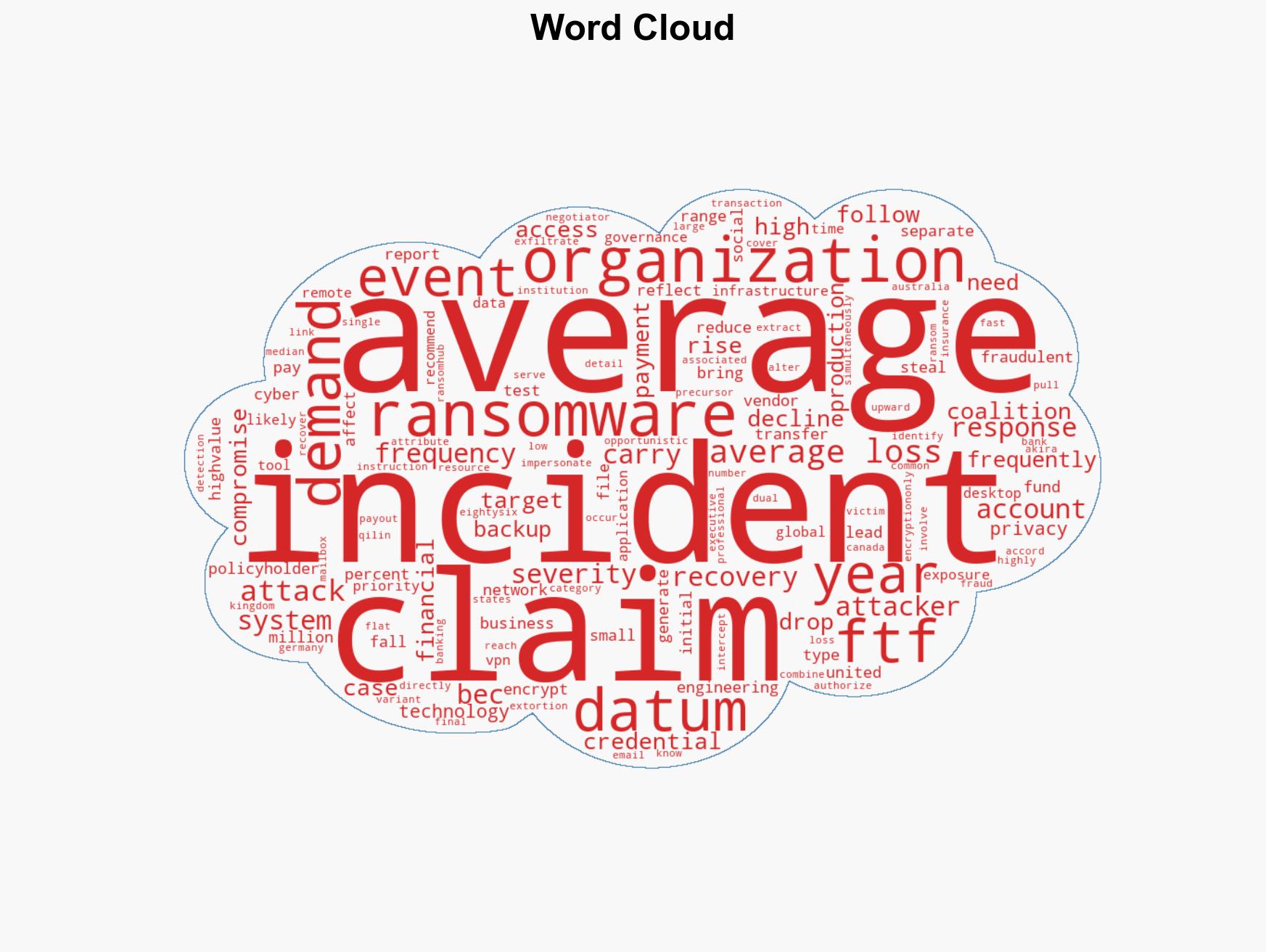
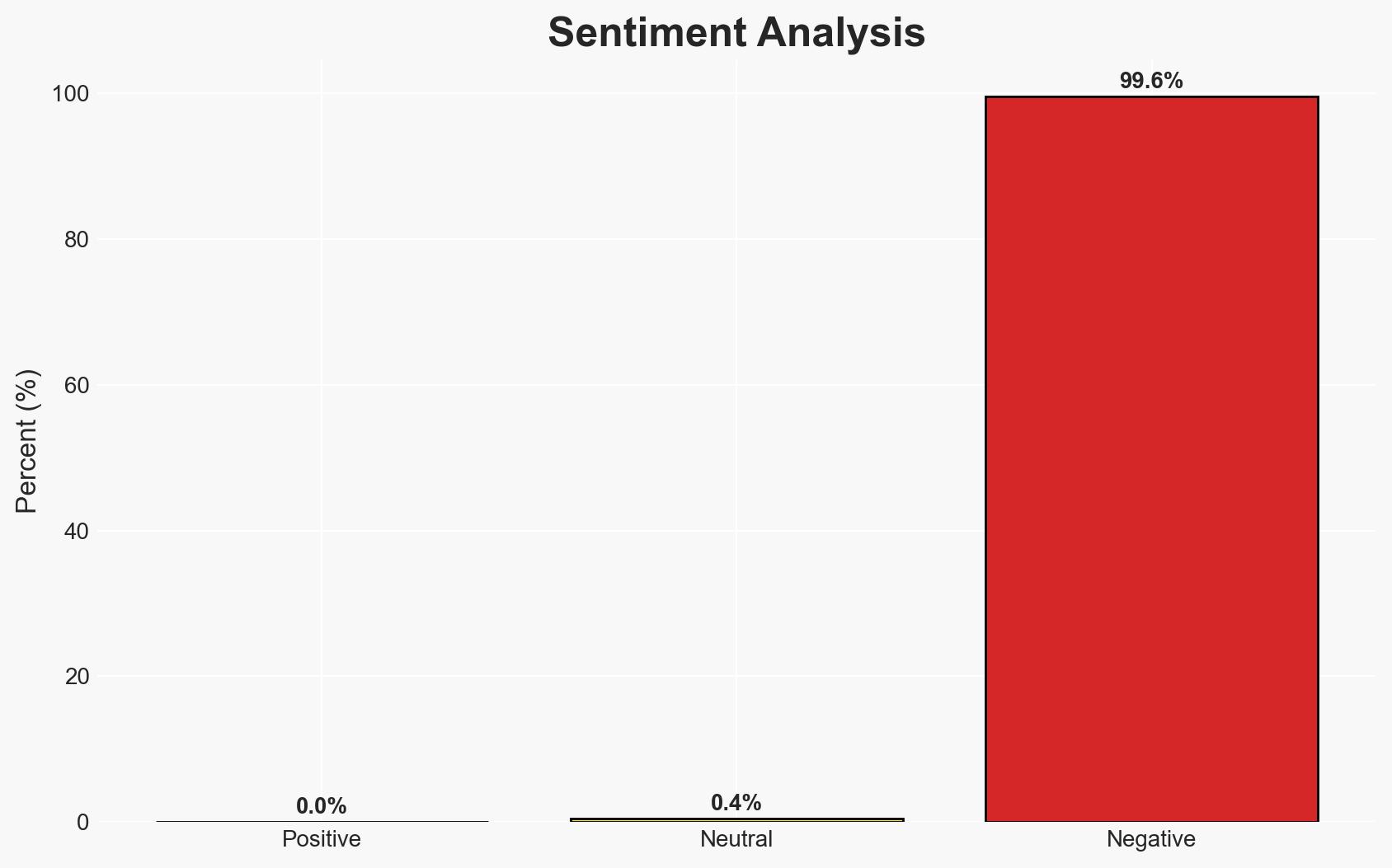
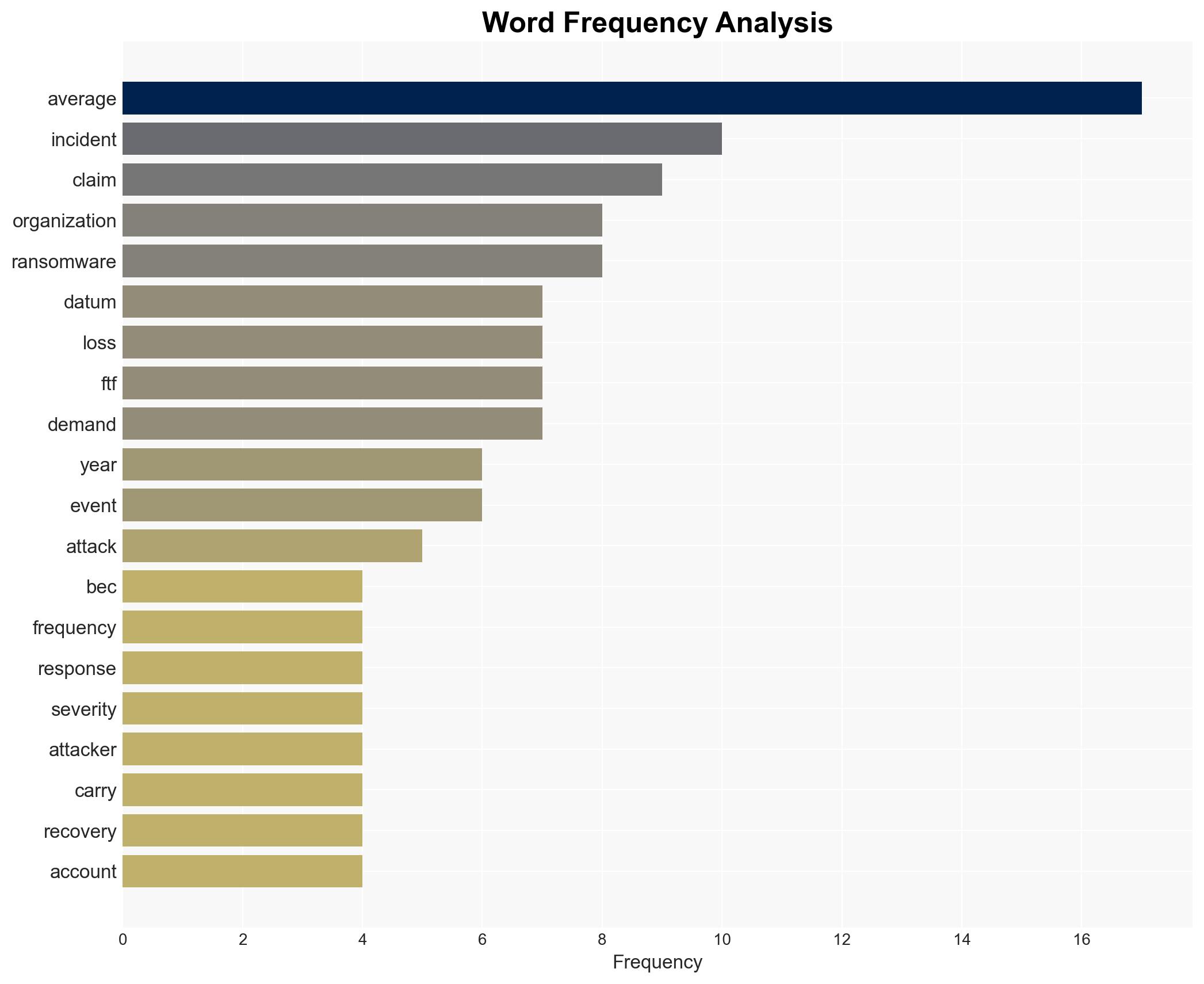
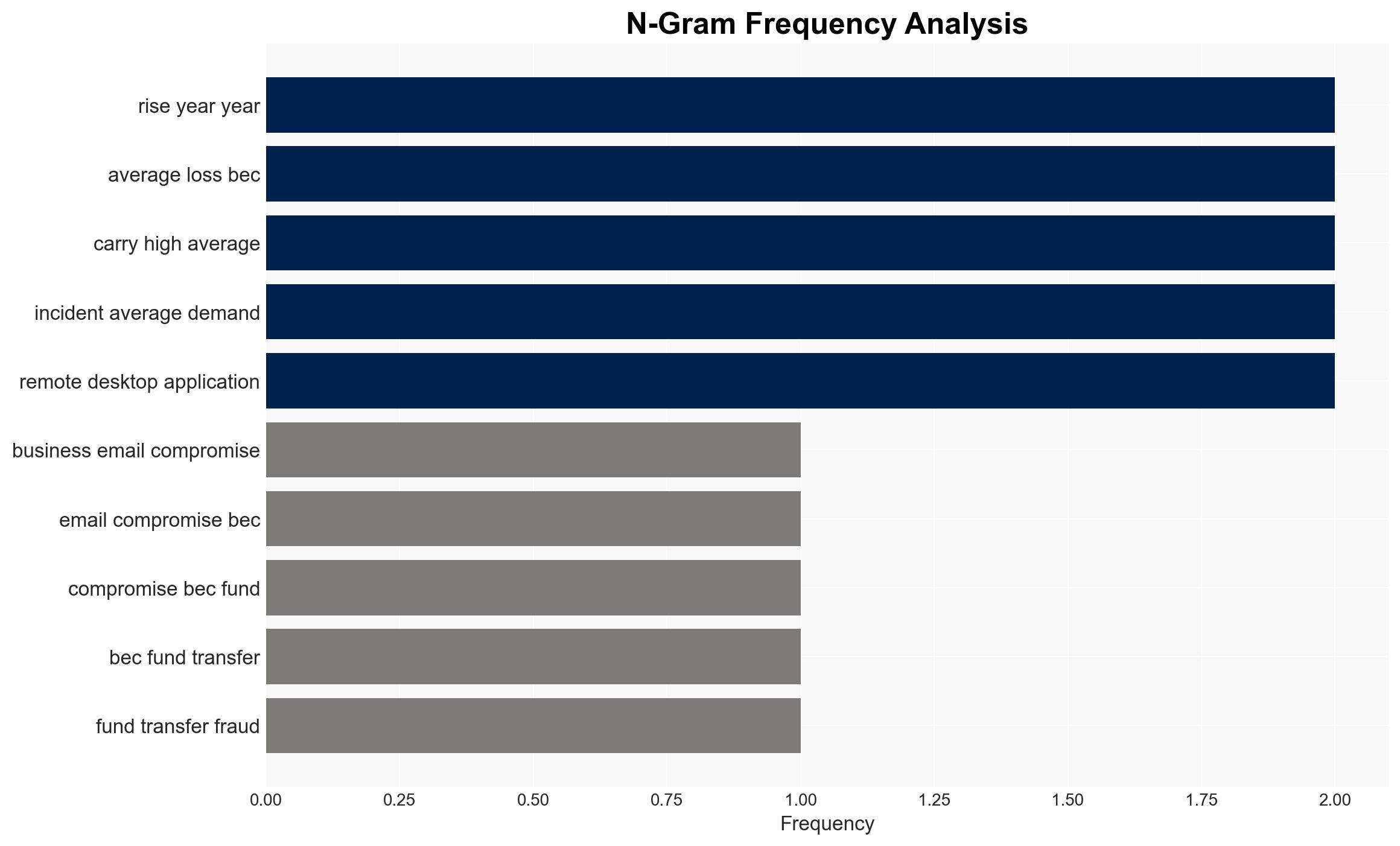
The decline in ransomware severity due to effective backup strategies has prompted ransomware gangs to increasingly employ data theft tactics. Business email compromise (BEC) and funds transfer fraud (FTF) remain prevalent, with social engineering as a significant component. The shift in tactics affects organizations globally, with moderate confidence in the assessment due to incomplete data on the full scope of ransomware adaptations.
2. Competing Hypotheses
- Hypothesis A: Ransomware gangs are increasingly using data theft as a response to effective backup strategies. Supported by the rise in dual extortion tactics and the decline in ransomware severity, but contradicted by the lack of comprehensive data on all ransomware group activities.
- Hypothesis B: The observed changes in ransomware tactics are primarily due to increased law enforcement actions and international cooperation. This is supported by the recovery of stolen funds and reduced average losses, though contradicted by the lack of direct evidence linking law enforcement actions to changes in ransomware strategies.
- Assessment: Hypothesis A is currently better supported due to the direct correlation between backup effectiveness and the shift to data theft. Indicators such as further increases in dual extortion cases or changes in ransom demands could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will continue to improve backup and recovery strategies; ransomware gangs will adapt tactics based on perceived vulnerabilities; social engineering will remain a key tactic in cyber fraud.
- Information Gaps: Detailed data on the full range of ransomware group activities and the effectiveness of international law enforcement efforts.
- Bias & Deception Risks: Potential bias in data reporting from insurance claims; possibility of underreporting due to reputational concerns; deception by ransomware groups in reported demands and tactics.
4. Implications and Strategic Risks
The evolution of ransomware tactics towards data theft could increase the complexity and impact of cyber incidents. This shift may influence organizational cybersecurity priorities and international cyber policy frameworks.
- Political / Geopolitical: Increased international pressure for cooperation on cybercrime could lead to new treaties or agreements.
- Security / Counter-Terrorism: Enhanced focus on cybersecurity defenses and incident response capabilities may be required.
- Cyber / Information Space: Potential increase in data privacy concerns and regulatory scrutiny as data theft becomes more prevalent.
- Economic / Social: Potential financial instability for smaller organizations unable to cope with data theft impacts; increased insurance premiums.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of ransomware group activities; promote awareness and training on social engineering tactics.
- Medium-Term Posture (1–12 months): Develop partnerships with international cybercrime units; invest in advanced threat detection and response capabilities.
- Scenario Outlook:
- Best: Effective international cooperation reduces ransomware incidents significantly.
- Worst: Ransomware gangs develop new, more sophisticated tactics, increasing incident severity.
- Most-Likely: Continued adaptation by ransomware gangs with moderate success in countermeasures.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, ransomware, data theft, social engineering, cyber insurance, international cooperation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us