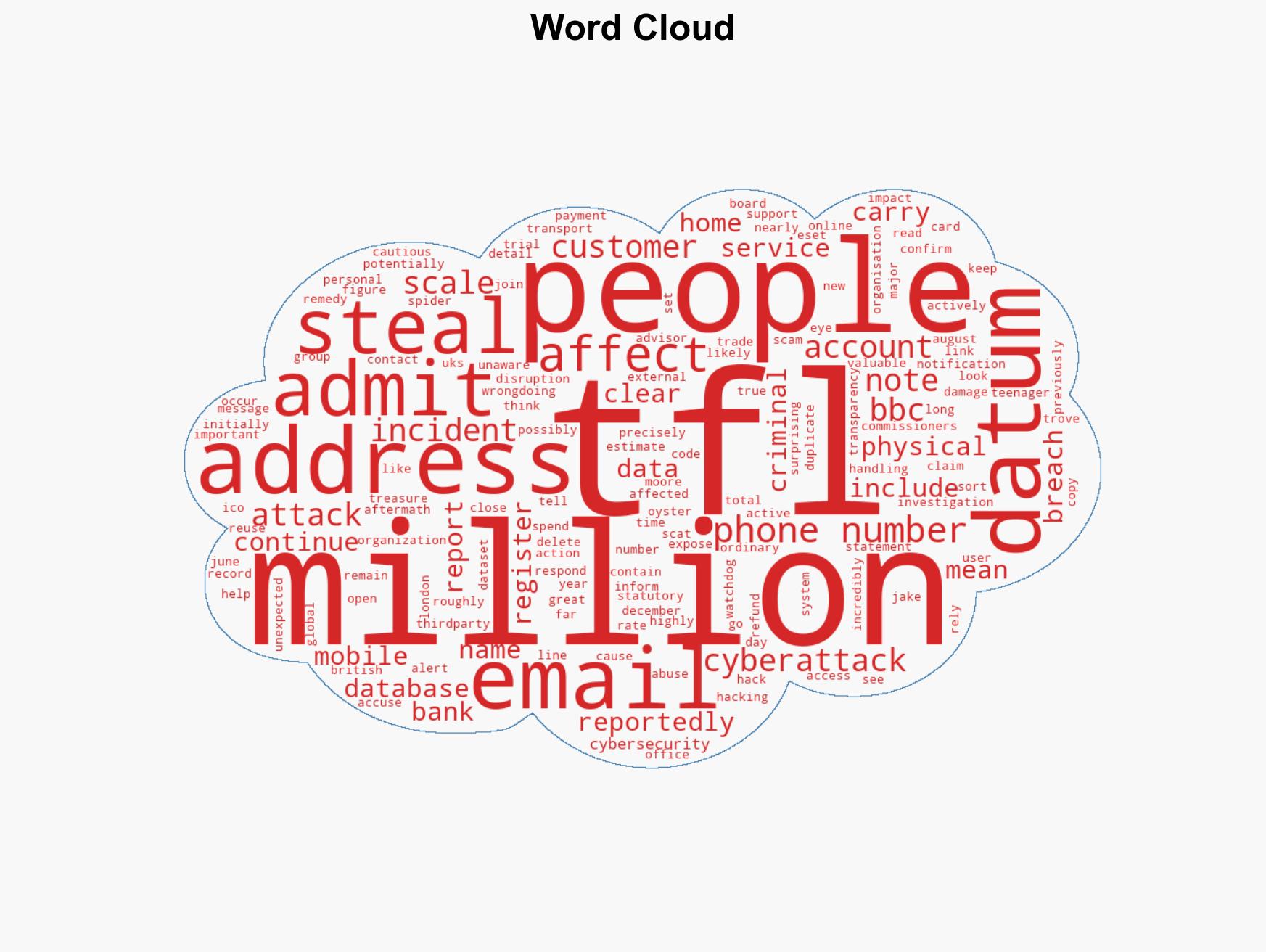
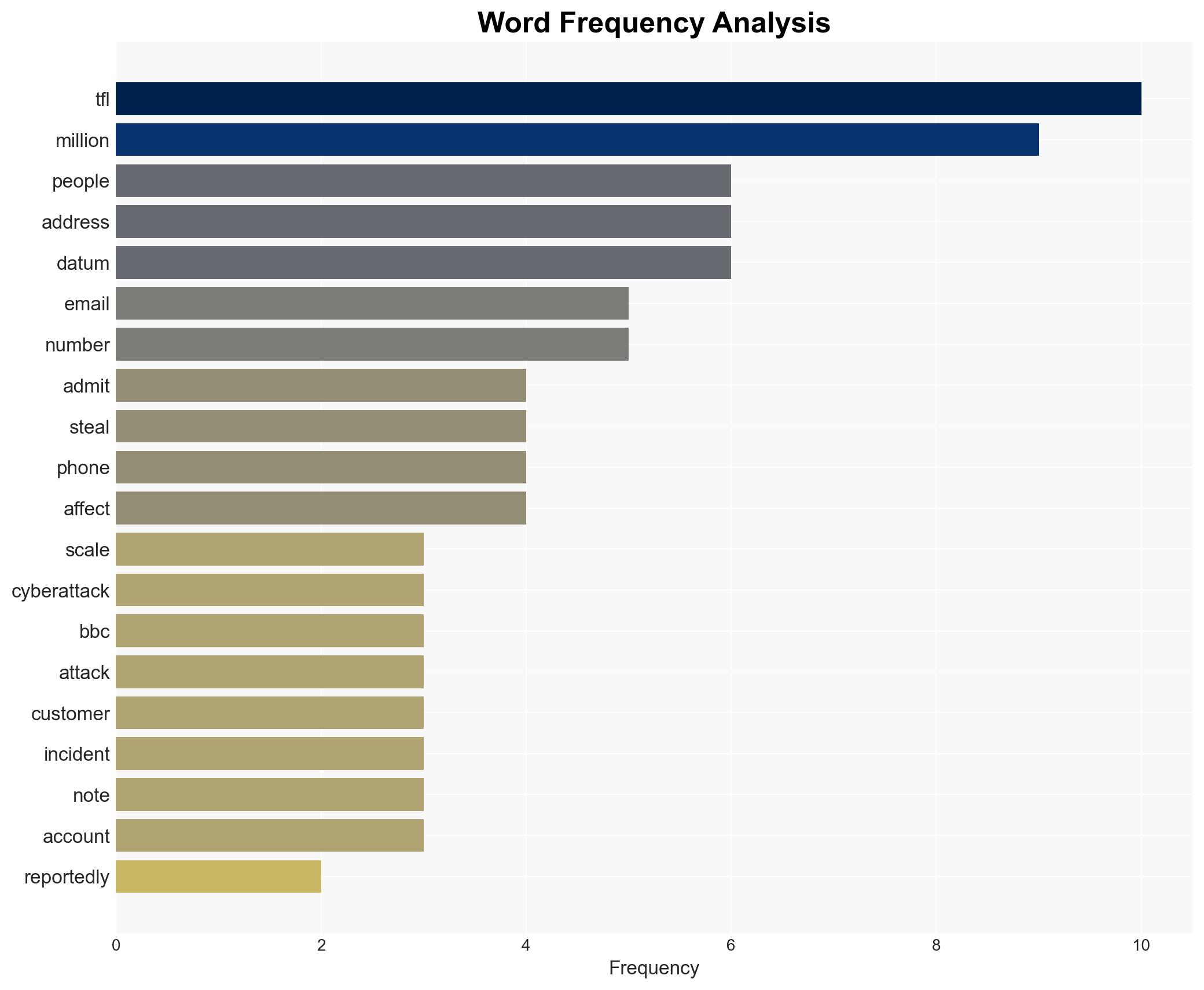
TfL acknowledges 2024 cyberattack compromised personal data of approximately 10 million customers
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: TfL admits 2024 cyberattack may have affected over 10 million people personal customer info stolen here’s what we know so far
1. BLUF (Bottom Line Up Front)
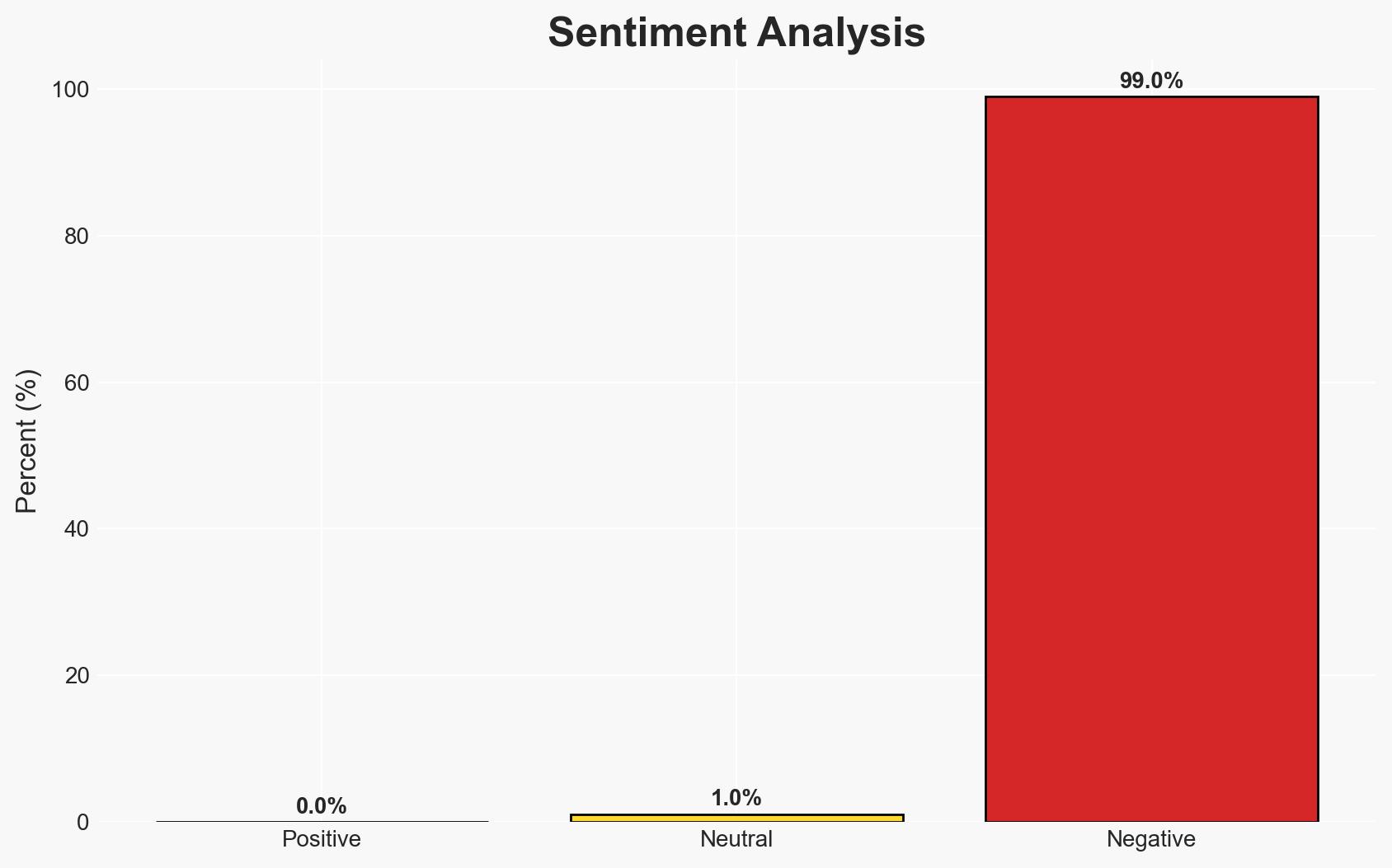
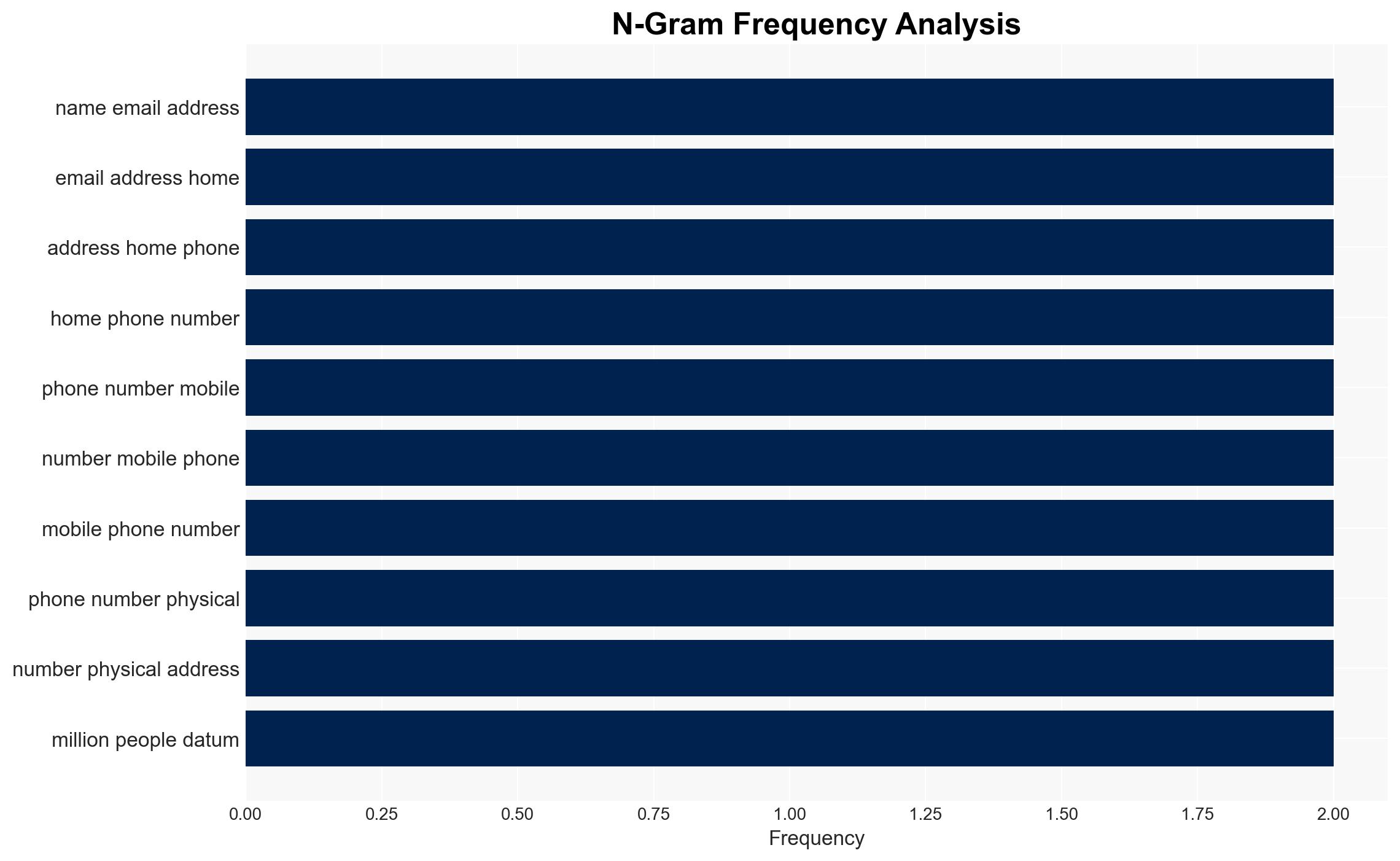
The 2024 cyberattack on Transport for London (TfL) has potentially compromised the personal data of over 10 million individuals, significantly more than initially reported. The breach, attributed to the hacking group Scatted Spider, underscores vulnerabilities in public infrastructure cybersecurity. This incident has broad implications for data privacy and public trust. Confidence in this assessment is moderate due to incomplete data on the full scope and impact of the breach.
2. Competing Hypotheses
- Hypothesis A: The cyberattack was primarily opportunistic, targeting TfL due to vulnerabilities in its systems. Supporting evidence includes the large volume of data stolen and the initial underestimation of the breach’s scale. Key uncertainties include the hackers’ motivations and whether they had specific targets within the dataset.
- Hypothesis B: The attack was part of a coordinated effort to gather data for broader criminal activities, possibly linked to other breaches. This is supported by the value of the dataset and its potential use in identity theft or fraud. Contradicting evidence includes the lack of immediate, widespread misuse of the data.
- Assessment: Hypothesis B is currently better supported due to the strategic value of the stolen data for criminal networks. Indicators such as the sale or use of the data in other criminal activities could further validate this hypothesis.
3. Key Assumptions and Red Flags
- Assumptions: TfL’s cybersecurity measures were insufficient; the attackers had no insider assistance; the breach was detected and reported accurately.
- Information Gaps: Details on the hackers’ identities and motivations; comprehensive data on the breach’s impact on individuals; full extent of data misuse.
- Bias & Deception Risks: Potential bias in TfL’s reporting to minimize reputational damage; possible deception in hackers’ claims or data manipulation.
4. Implications and Strategic Risks
This cyberattack could lead to increased scrutiny of public sector cybersecurity practices and influence future regulatory measures. The incident may also serve as a catalyst for more robust data protection policies.
- Political / Geopolitical: Potential for increased regulatory pressure on public infrastructure cybersecurity.
- Security / Counter-Terrorism: Heightened awareness of vulnerabilities in critical infrastructure could lead to improved security measures.
- Cyber / Information Space: The breach highlights the need for enhanced cybersecurity protocols and threat intelligence sharing.
- Economic / Social: Possible erosion of public trust in TfL and similar institutions, impacting service usage and public confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of data misuse, increase public awareness, and improve communication strategies.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity infrastructure, establish partnerships for threat intelligence sharing, and conduct regular security audits.
- Scenario Outlook:
- Best: Improved cybersecurity measures prevent future breaches.
- Worst: Data is widely misused, leading to significant financial and reputational damage.
- Most-Likely: Incremental improvements in cybersecurity with occasional data misuse incidents.
6. Key Individuals and Entities
- Transport for London (TfL)
- Scatted Spider (hacking group)
- Information Commissioner’s Office (ICO)
- Jake Moore, Global Cybersecurity Advisor at ESET
- Two British teenagers (accused hackers)
7. Thematic Tags
cybersecurity, data breach, public infrastructure, data privacy, regulatory compliance, threat intelligence, public trust
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us